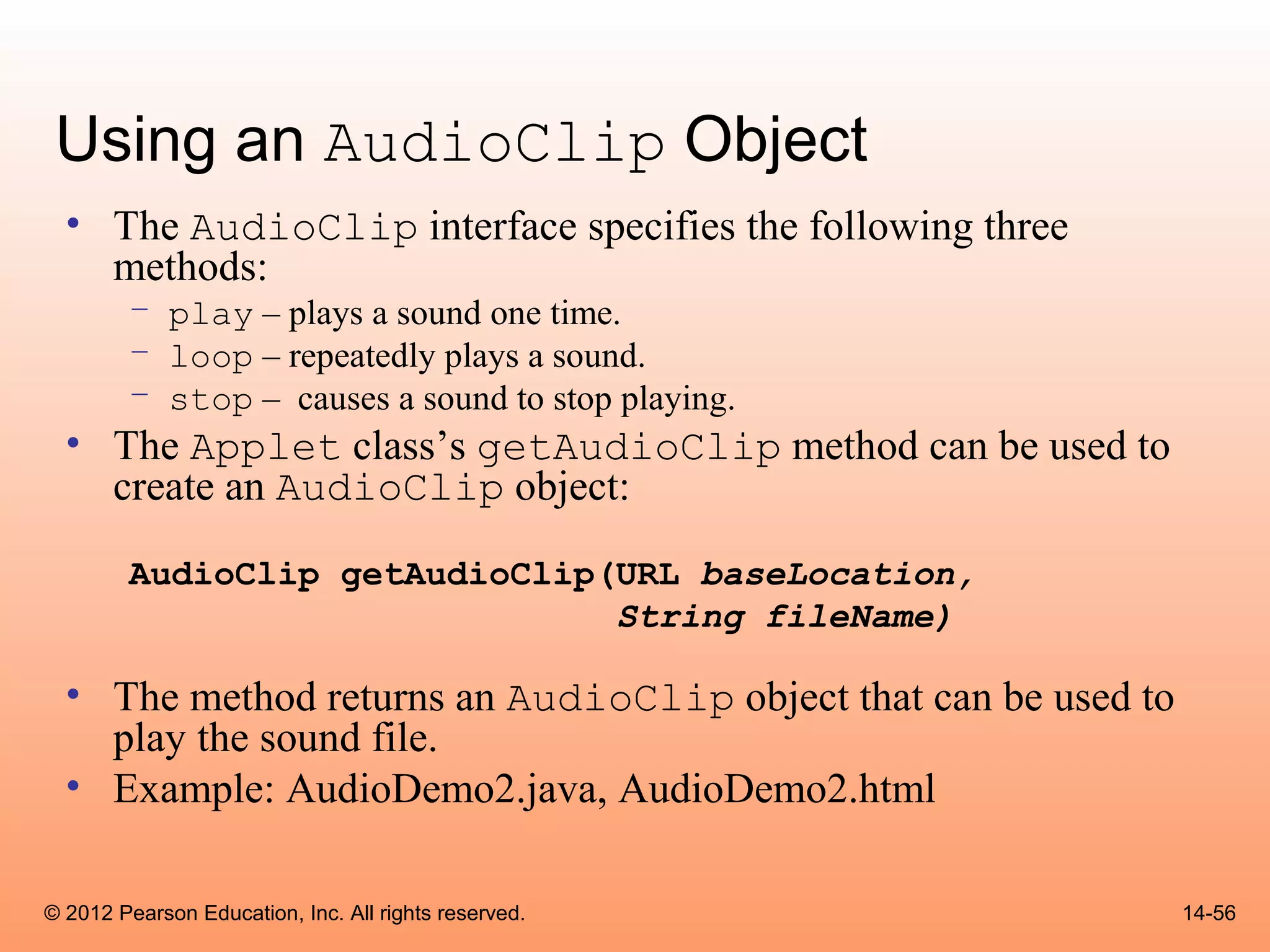
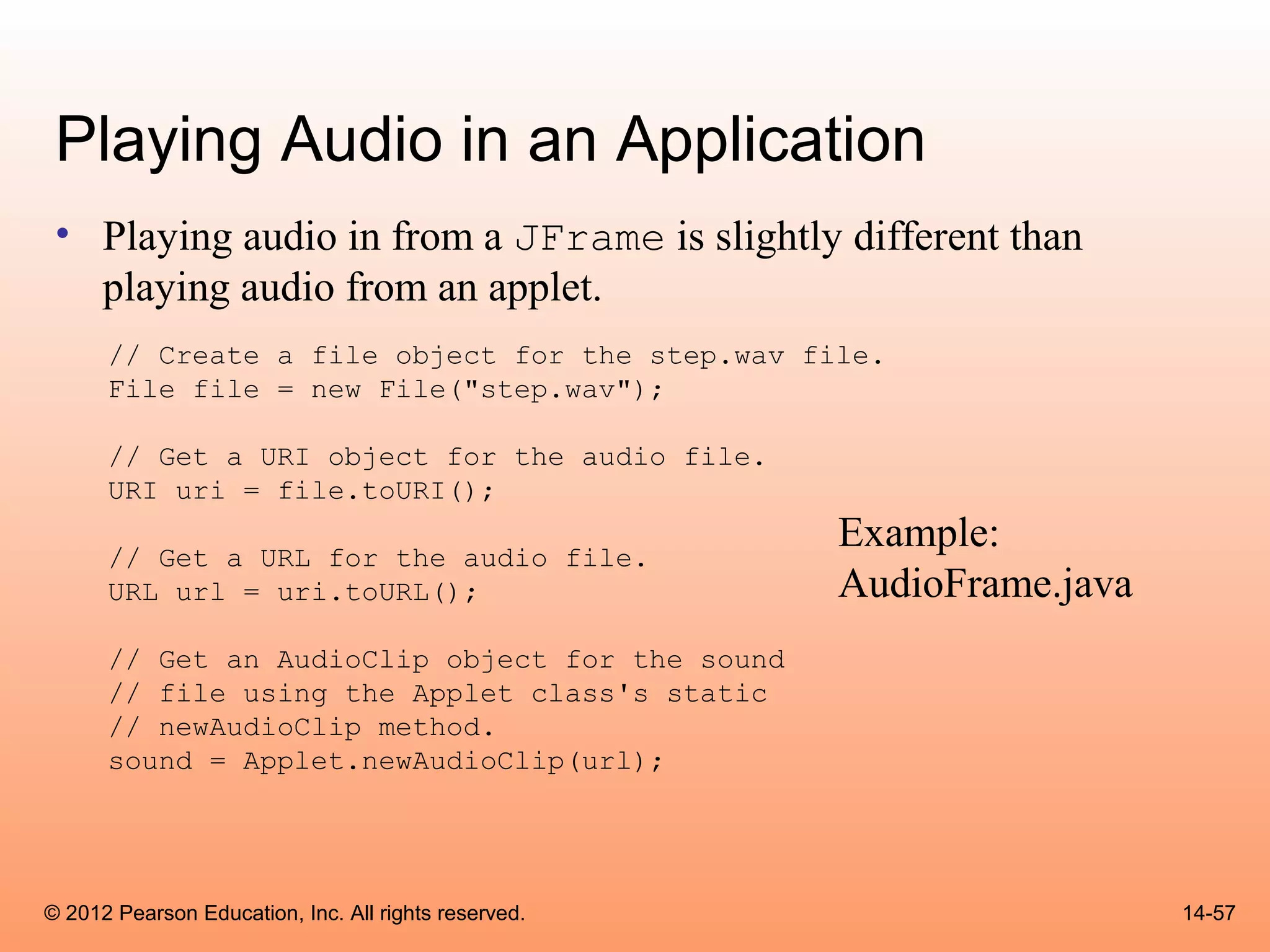
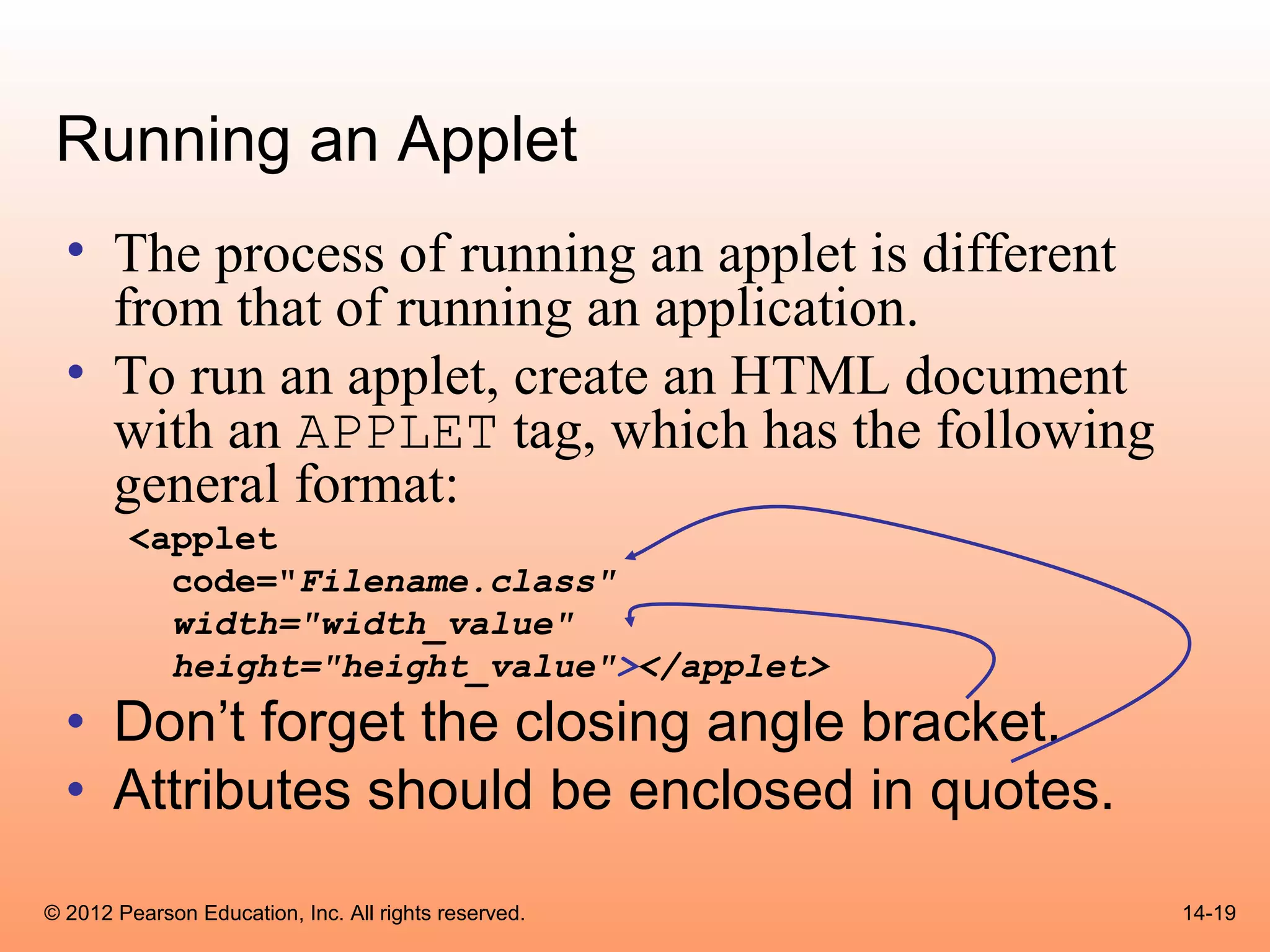
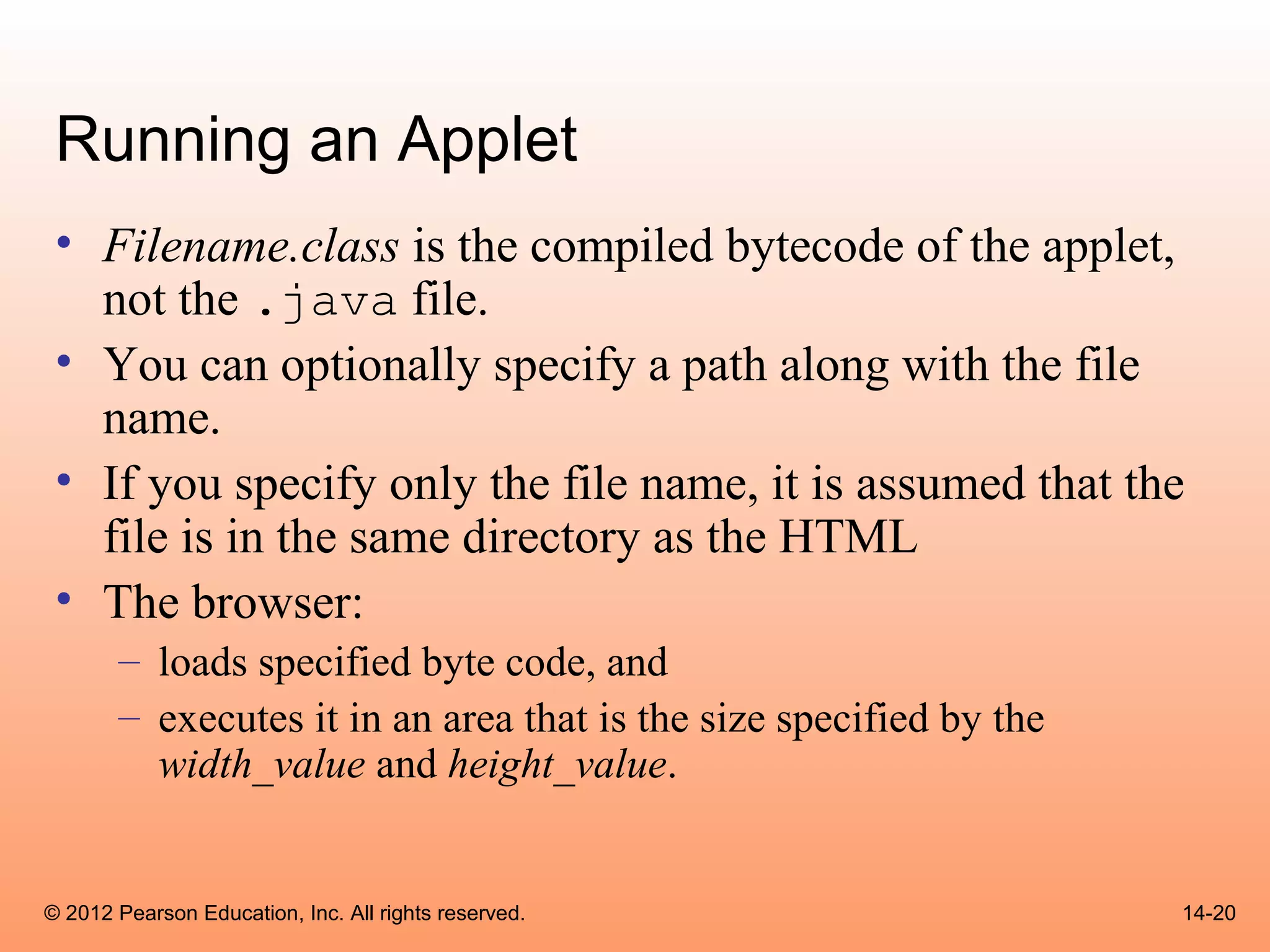
This chapter discusses applets and HTML. It covers creating applets using Swing and AWT, drawing shapes, handling mouse/key events, and playing audio. Applets are Java programs that run in web browsers, while applications are standalone. Applets are inserted into HTML using <applet> tags and run on the user's computer, having restrictions on file/network access for security.
![Polygons
• Polygons are drawn using arrays of integers representing x,
y coordinates
int[]xCoords={60,100,140,140,100,60,20,20};
int[]yCoords={20,20,60,100,140,140,100,60};
© 2012 Pearson Education, Inc. All rights reserved. 14-35](https://image.slidesharecdn.com/csogaddisjavachapter14-130411104015-phpapp01/75/Cso-gaddis-java_chapter14-35-2048.jpg)