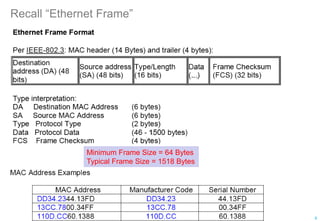
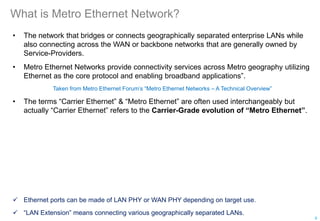
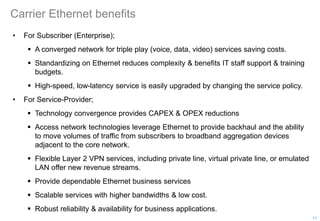
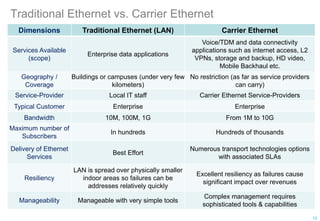
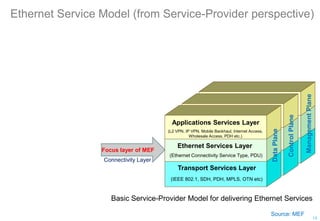
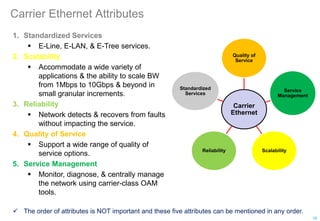
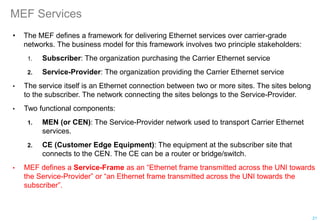
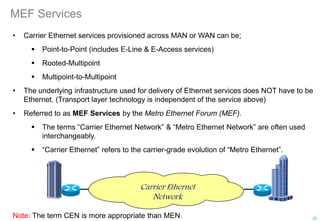
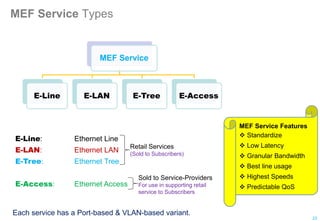
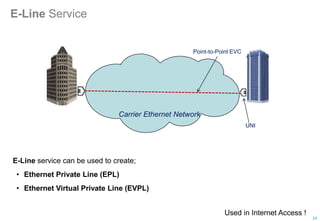
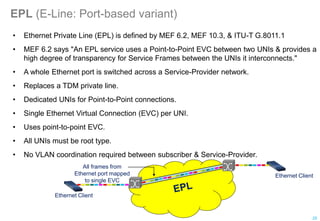
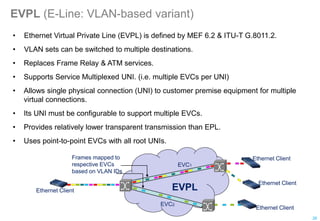
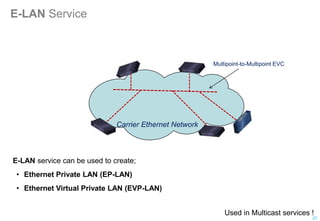
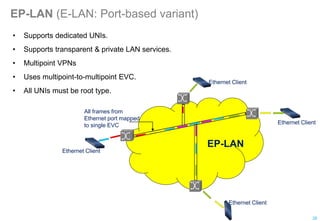
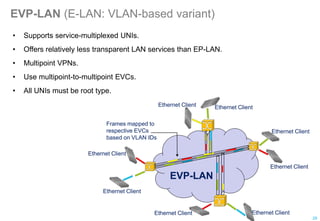
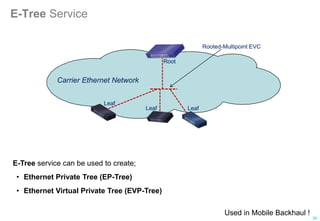
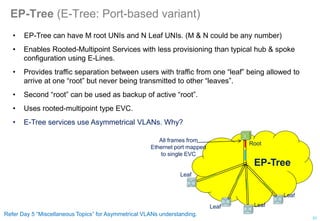
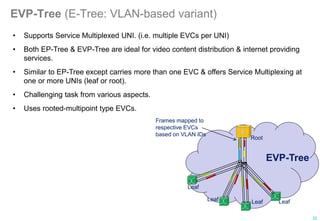
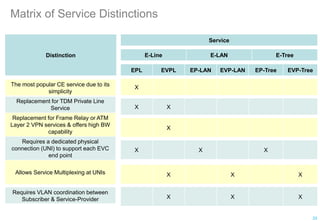
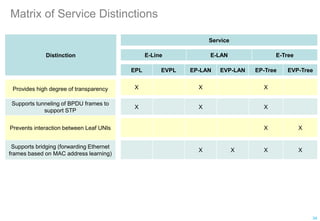
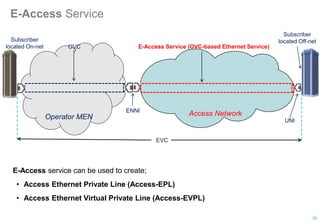
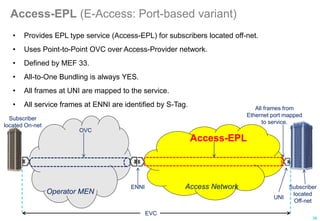
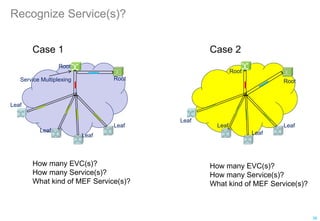
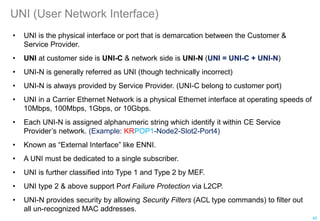
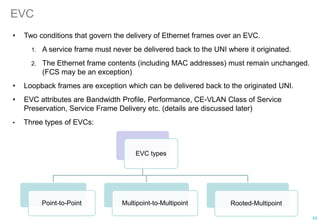
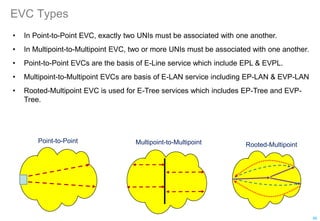
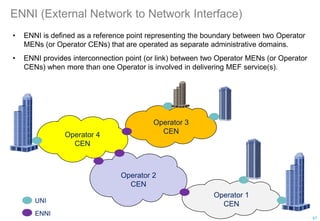
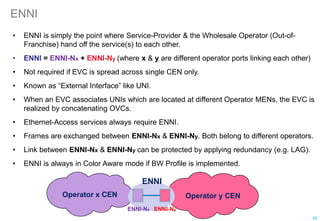
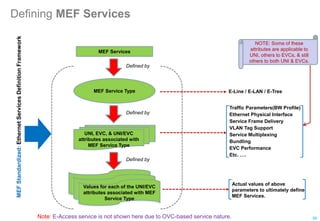
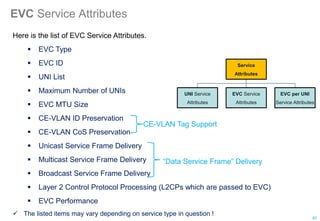
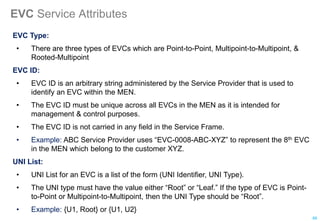
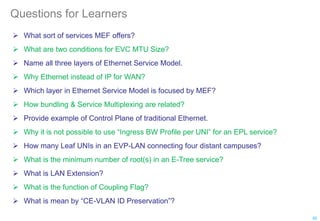
The 5-day course covers preparation for the MEF-CECP exam, focusing on carrier Ethernet concepts. Day 1 introduces carrier Ethernet and MEF services, including E-Line, E-LAN and E-Tree services. Participants learn about legacy Ethernet limitations addressed by carrier Ethernet, as well as the key attributes and components of carrier Ethernet networks.