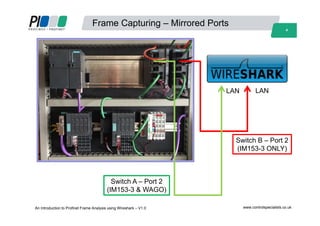
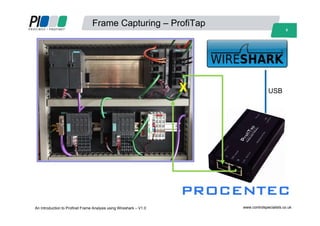
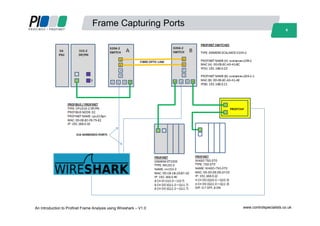
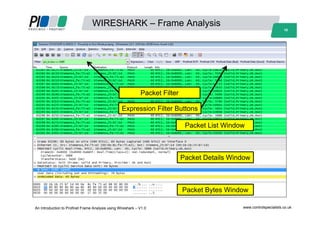
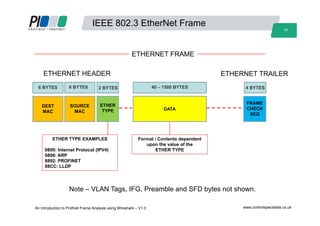
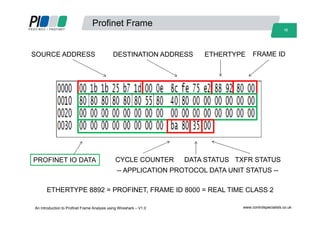
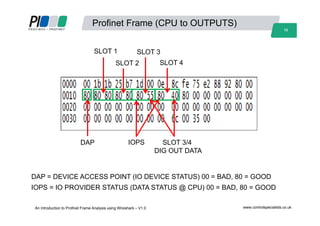
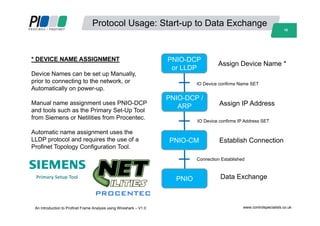
This document provides an introduction to Profinet frame analysis using Wireshark, focusing on the communication methods of Profinet devices over Ethernet. It outlines objectives such as capturing and analyzing Profinet frames, and includes details on equipment used in the workshop and the various protocols implemented. Additionally, operational steps for capturing frames during events like device start-up and data exchange are discussed.