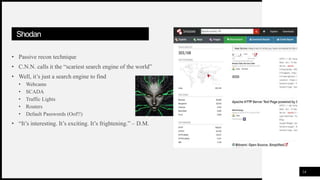
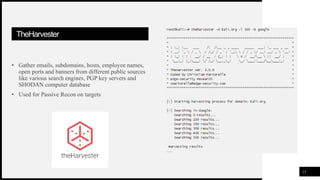
This document outlines an agenda for a presentation on open-source intelligence (OSINT) gathering techniques. The agenda includes an introduction to OSINT, different types of intelligence gathering, a scenario example, OSINT gathering tactics and tools like Shodan, TheHarvester and Google dorks, applications of OSINT, a demonstration, references for OSINT, and a conclusion. Key OSINT tools that will be demonstrated include Twitter, Shodan, TheHarvester and Google dorks for gathering information from public online sources.


![FIRSTUP
CONSULTANTS
TweetDeck
• A social media dashboard application for
management of Twitter accounts
• Customisable dashboard with unlimited
columns to monitor trends, follow hashtags,
and perform live searches
• Helps in observing events and incidents when
supplied with proper filters
• You just need a Twitter Account [Click Here]
• Using Boolean Operators AND and OR,
create filters
12
OSINT GATHERING TTPS](https://image.slidesharecdn.com/osintprimer1-200717162941/85/Osint-primer-12-320.jpg)


![OSINTOFOSINT
18
• Twitter: @s0md3v, @midnight_comms, @OsintCurious
• Github: https://github.com/jivoi/awesome-osint
• Tracelabs: https://www.tracelabs.org/
• OSINT Framework: https://osintframework.com/
• OSINT Curious Podcast: https://osintcurio.us/
• OSINT Stash: https://osint.best/
• 2nd Generation OSINT for the Defense Enterprise: [link]
• Seclists by Daniel Miessler [link]
• The Privacy Security & OSINT Show [link]](https://image.slidesharecdn.com/osintprimer1-200717162941/85/Osint-primer-18-320.jpg)