Embed presentation
Download as PDF, PPTX


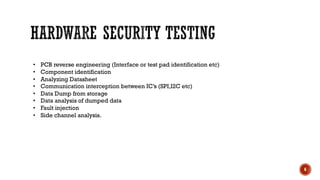


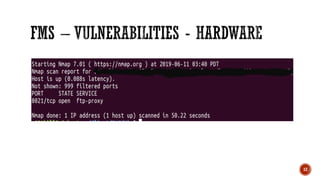
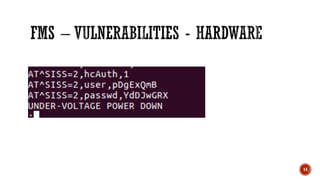

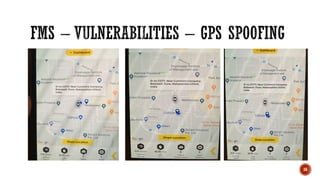


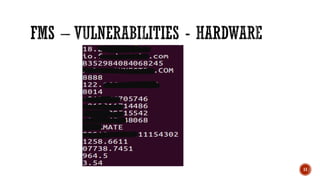
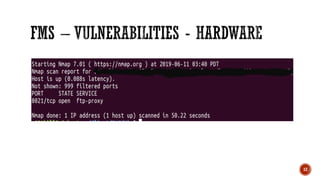
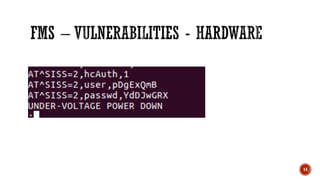
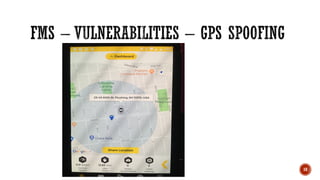
Arun Mane is the founder and director of AmynaSec Labs. He is a security speaker and trainer who has presented at many conferences including Defcon, Blackhat, Nullcon, and HITB. His areas of expertise include security testing of IoT devices, connected vehicles, medical devices, and industrial control systems. Some common issues he finds include devices being publicly accessible, having backdoors, hardcoded credentials, and crypto or web application management problems. His testing methodology involves assessing web and mobile applications, embedded device communications, hardware testing through reverse engineering, and analyzing communication protocols and stored data.