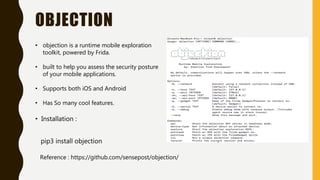
Frida is a dynamic instrumentation toolkit that allows injecting JavaScript into applications. Objection is a runtime mobile exploration toolkit powered by Frida that helps assess the security of mobile apps. It supports iOS and Android. Objection allows exploring apps by listing classes, methods, and injecting scripts to enable dynamic analysis like dumping keychain entries.



![FINDING CLASS AND METHODS
• ios hooking list classes
• ios hooking list class_methods Classname
• ios hooking search classes keywords
• ios hooking search methods classname
• ios hooking watch class classname --include-parents
• ios hooking set return_value "+[classname methodname]" false](https://image.slidesharecdn.com/objectiontoolusage-200705122053/85/Frida-Objection-Tool-Usage-9-320.jpg)