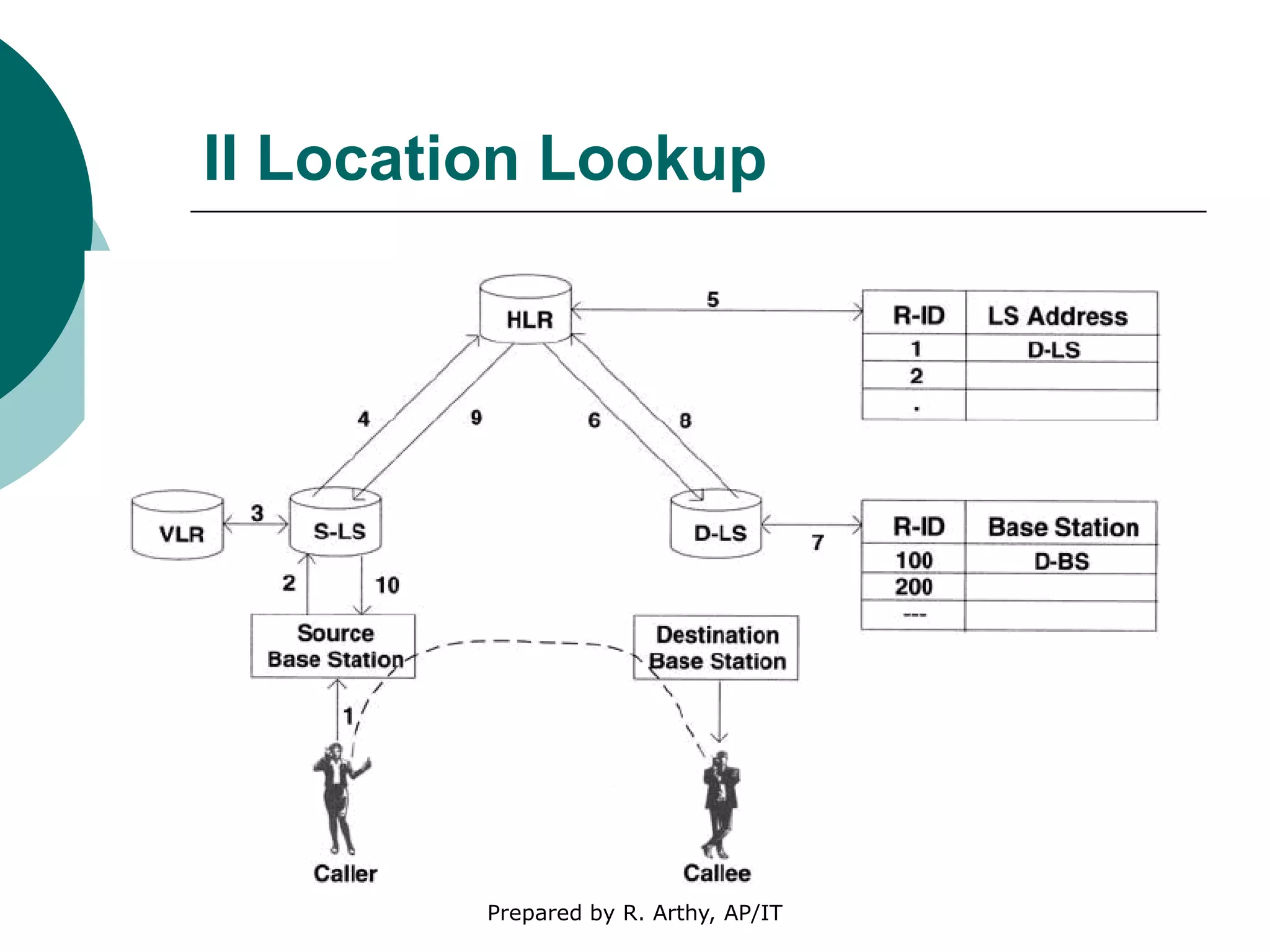
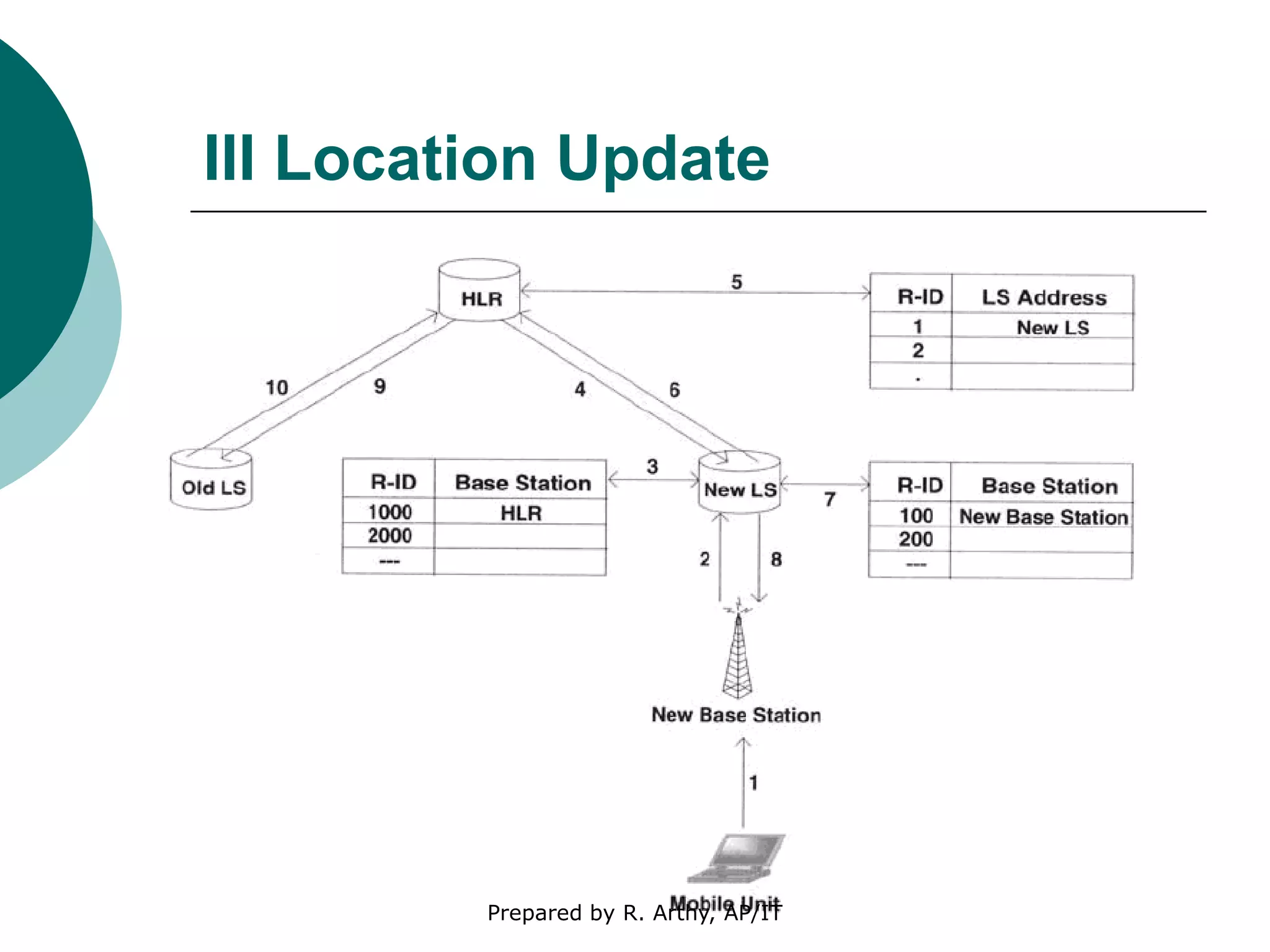
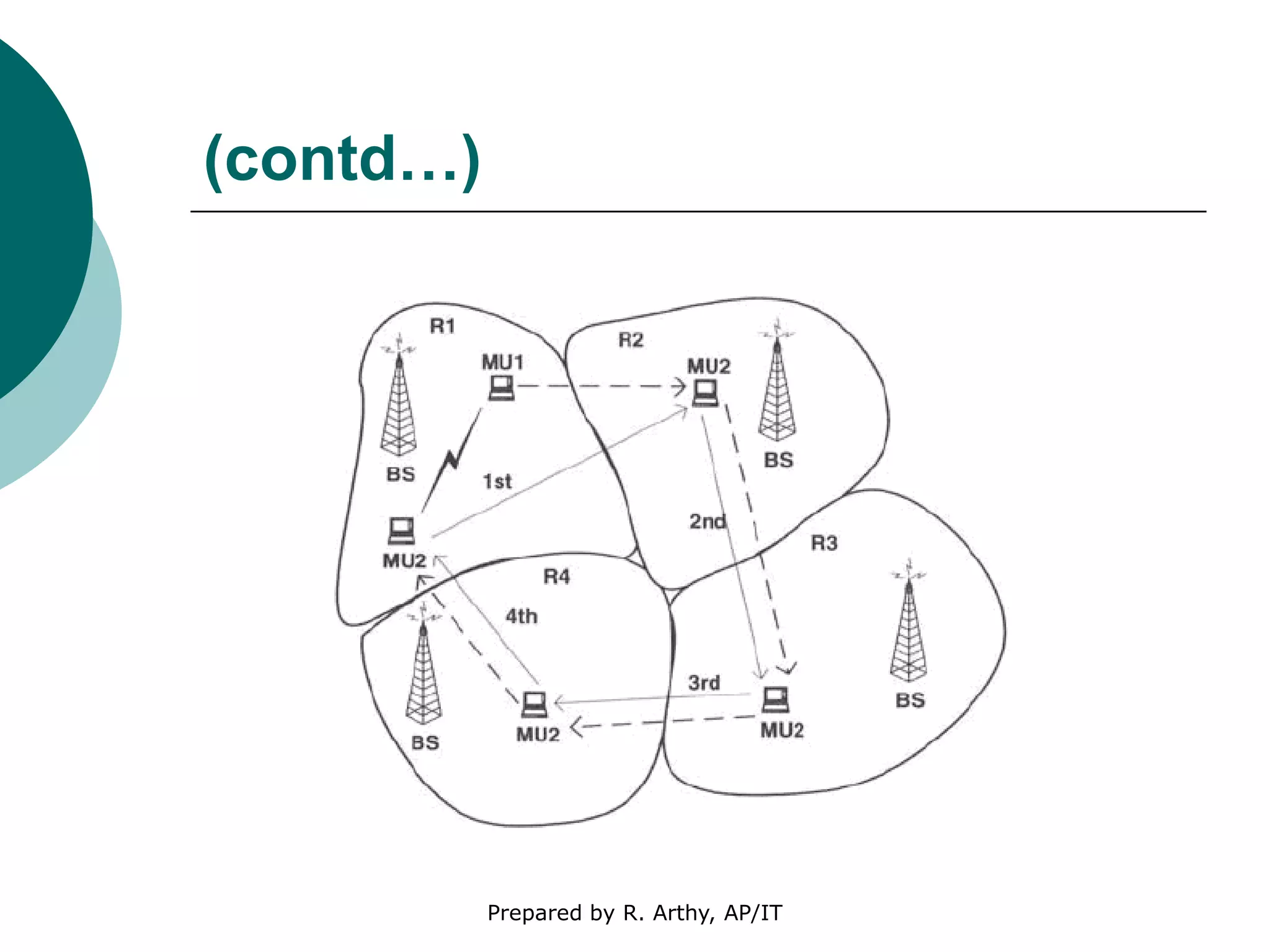
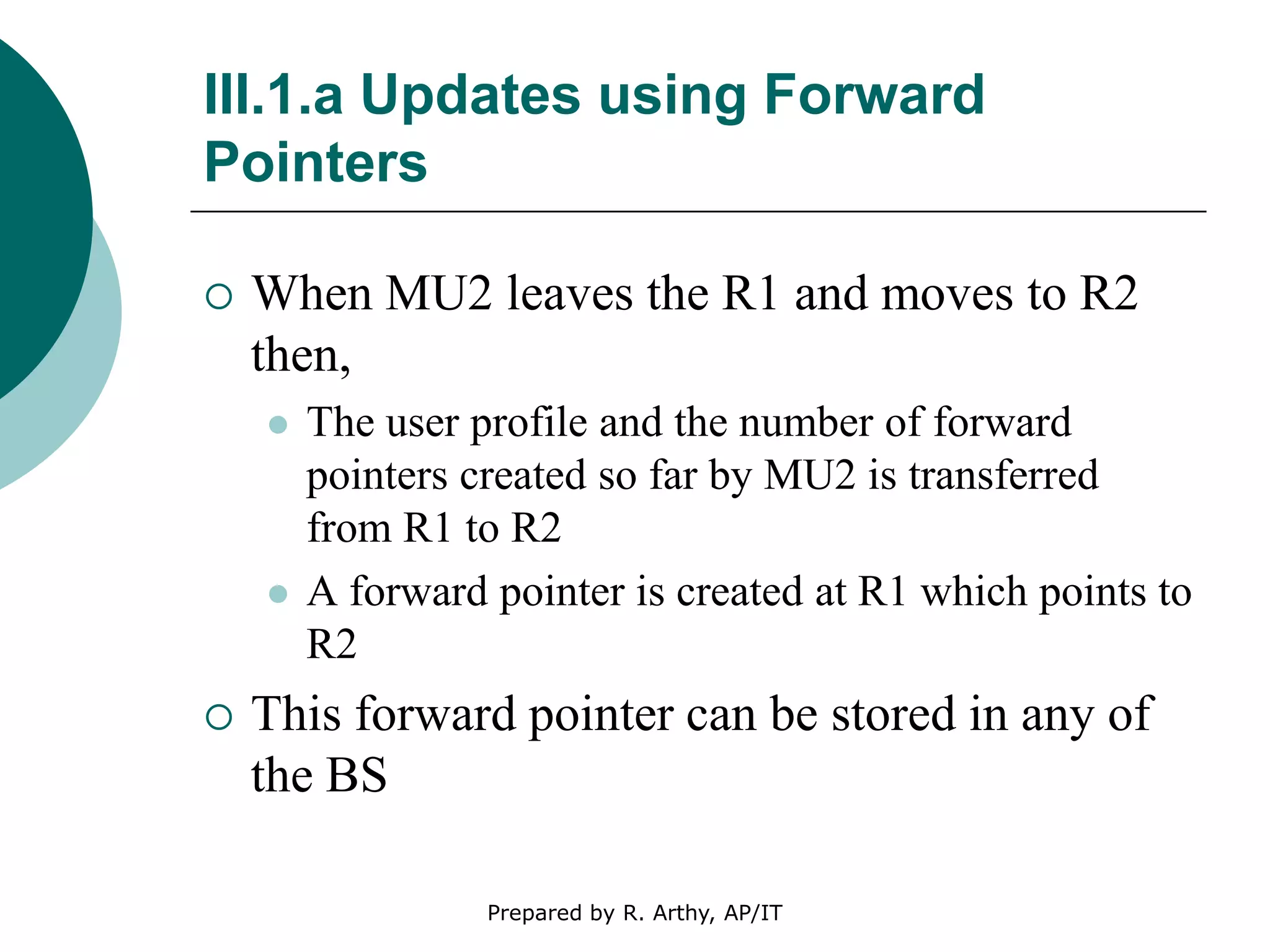
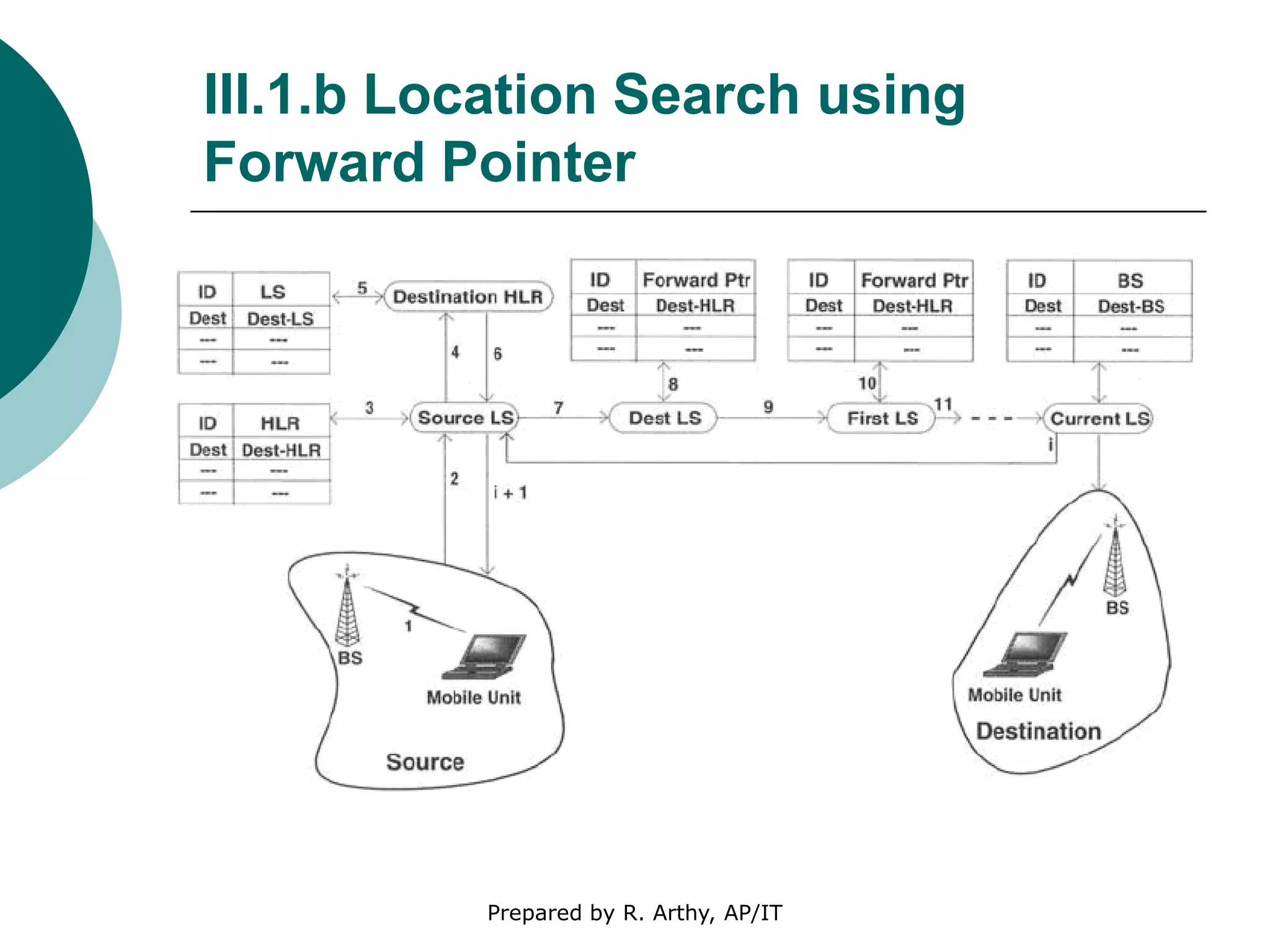
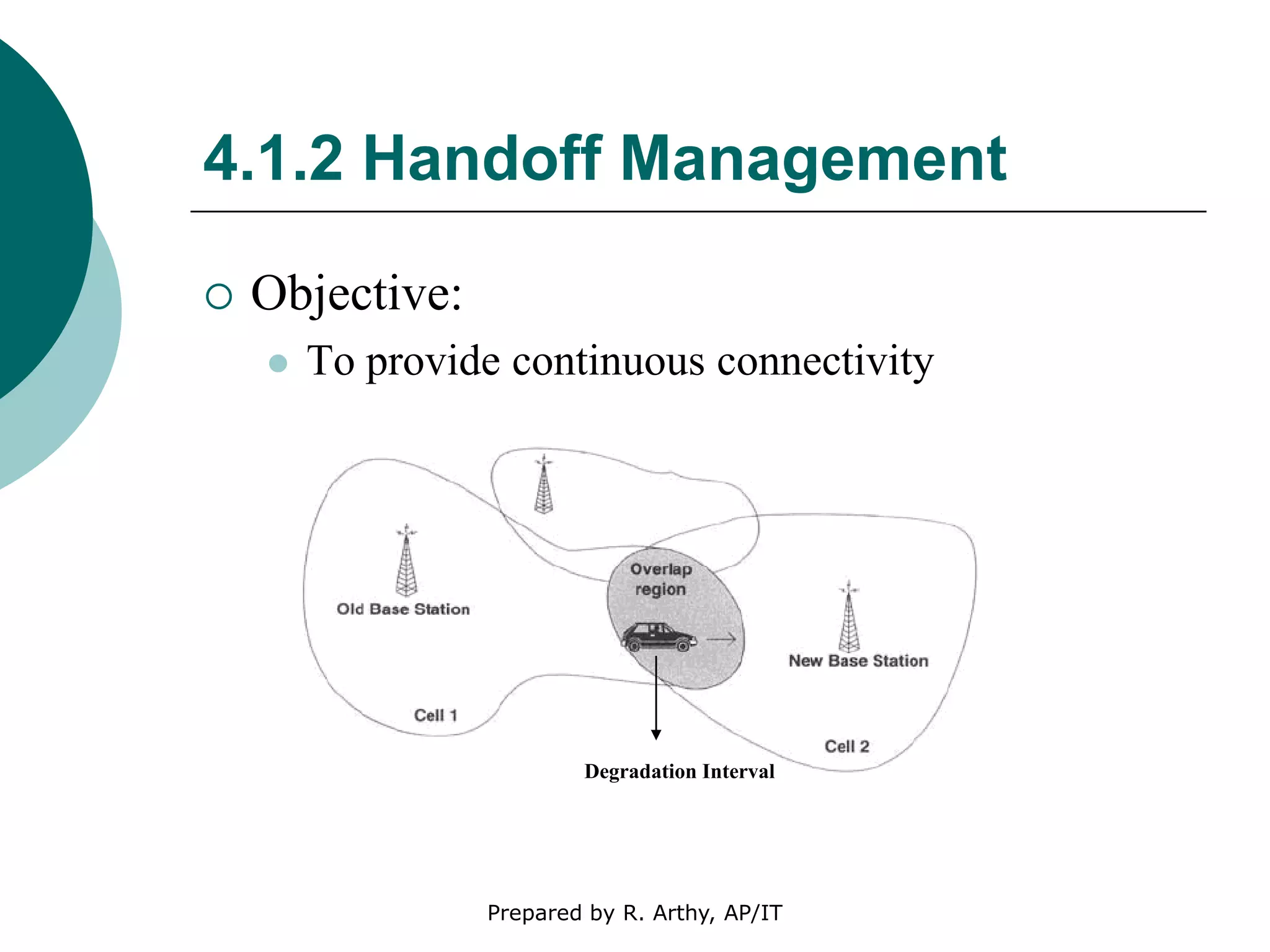
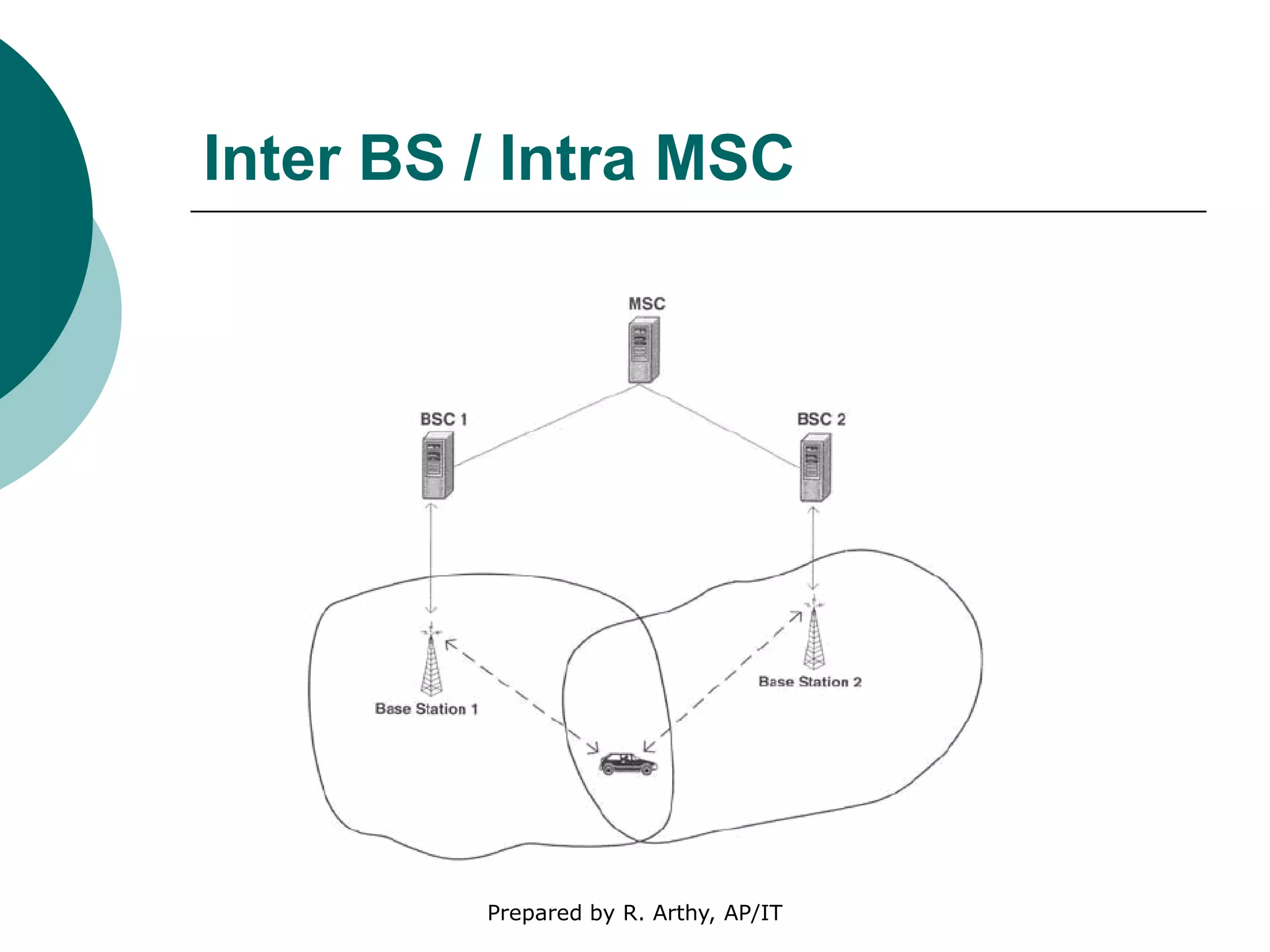
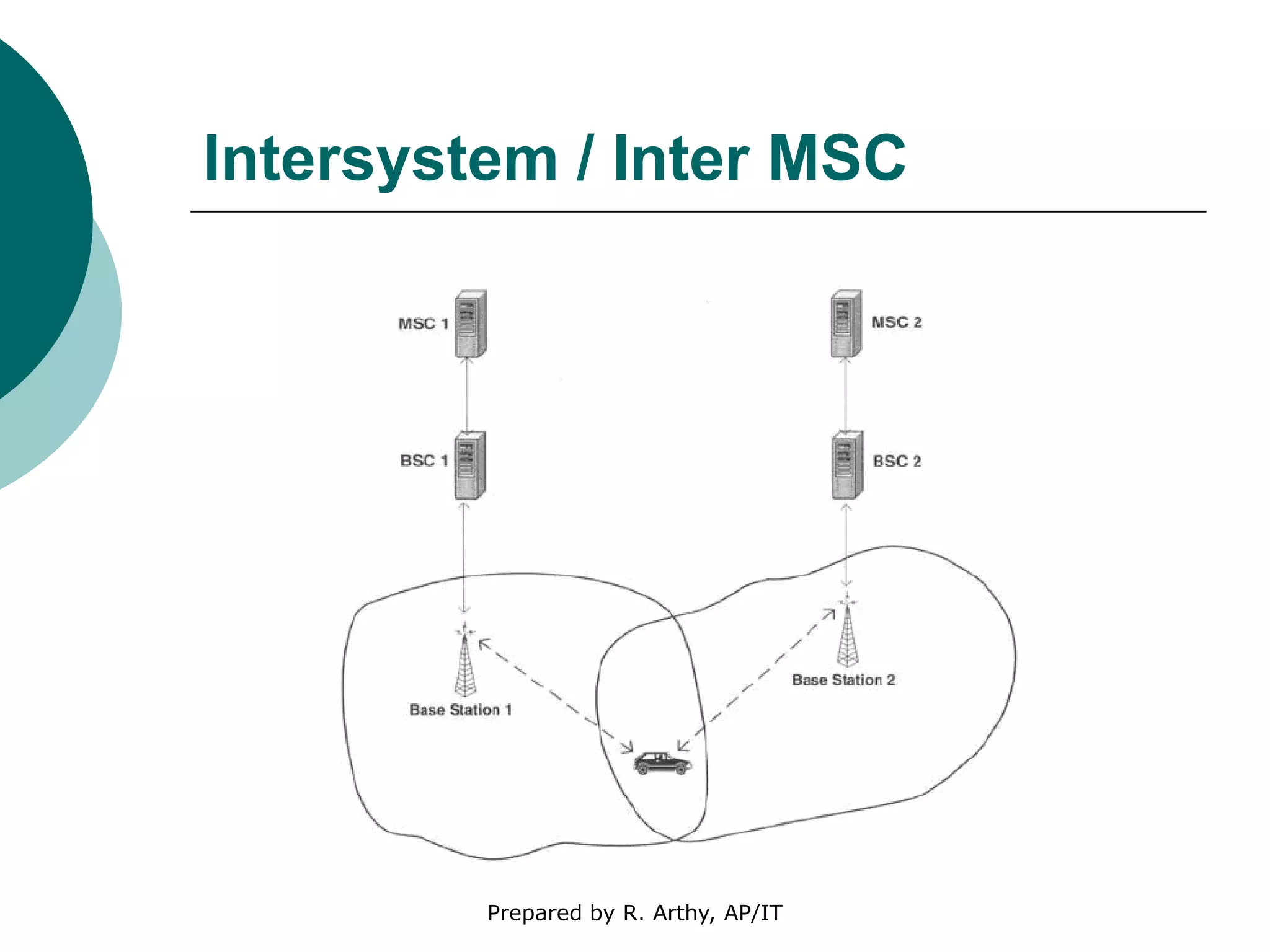
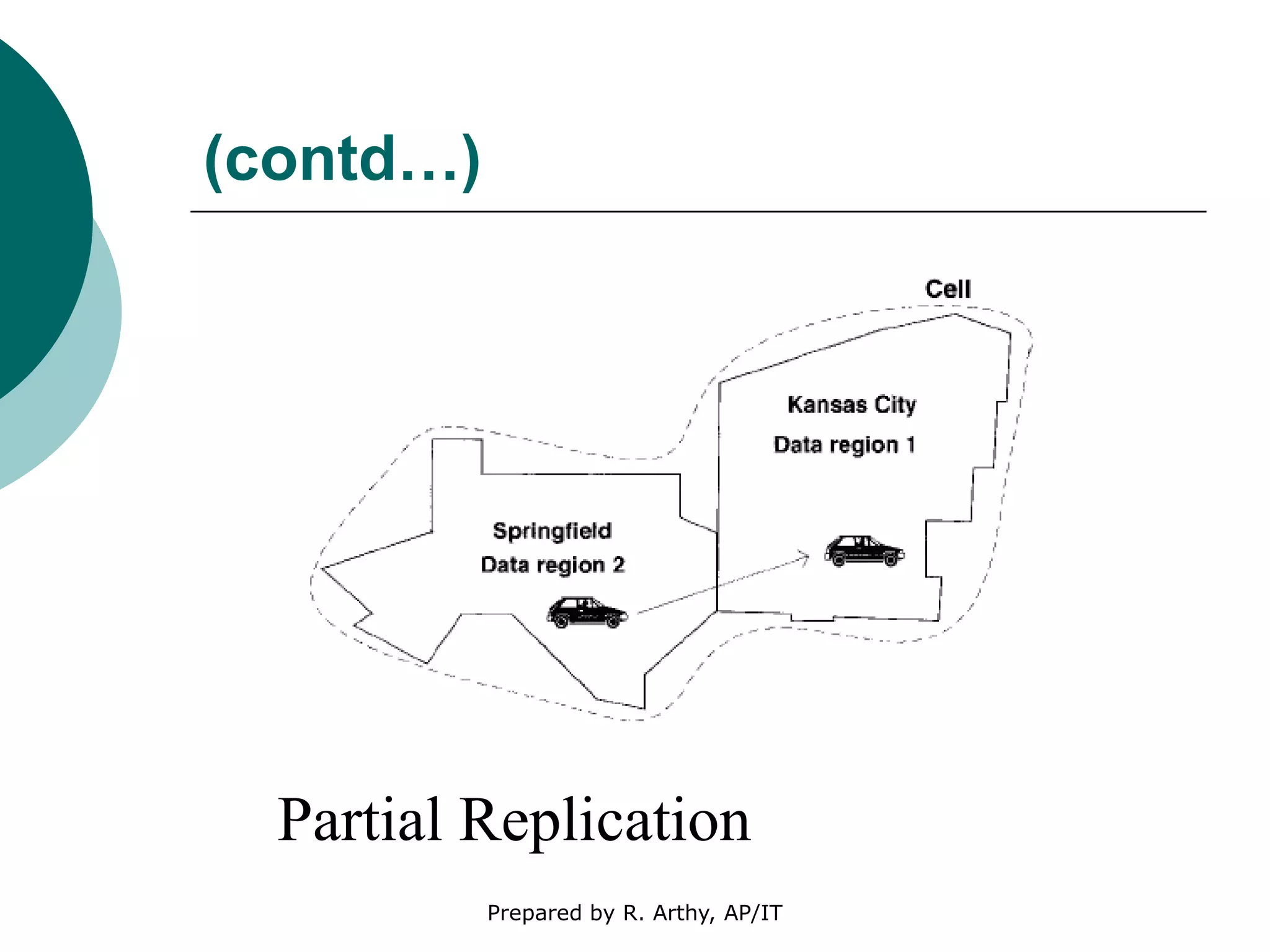
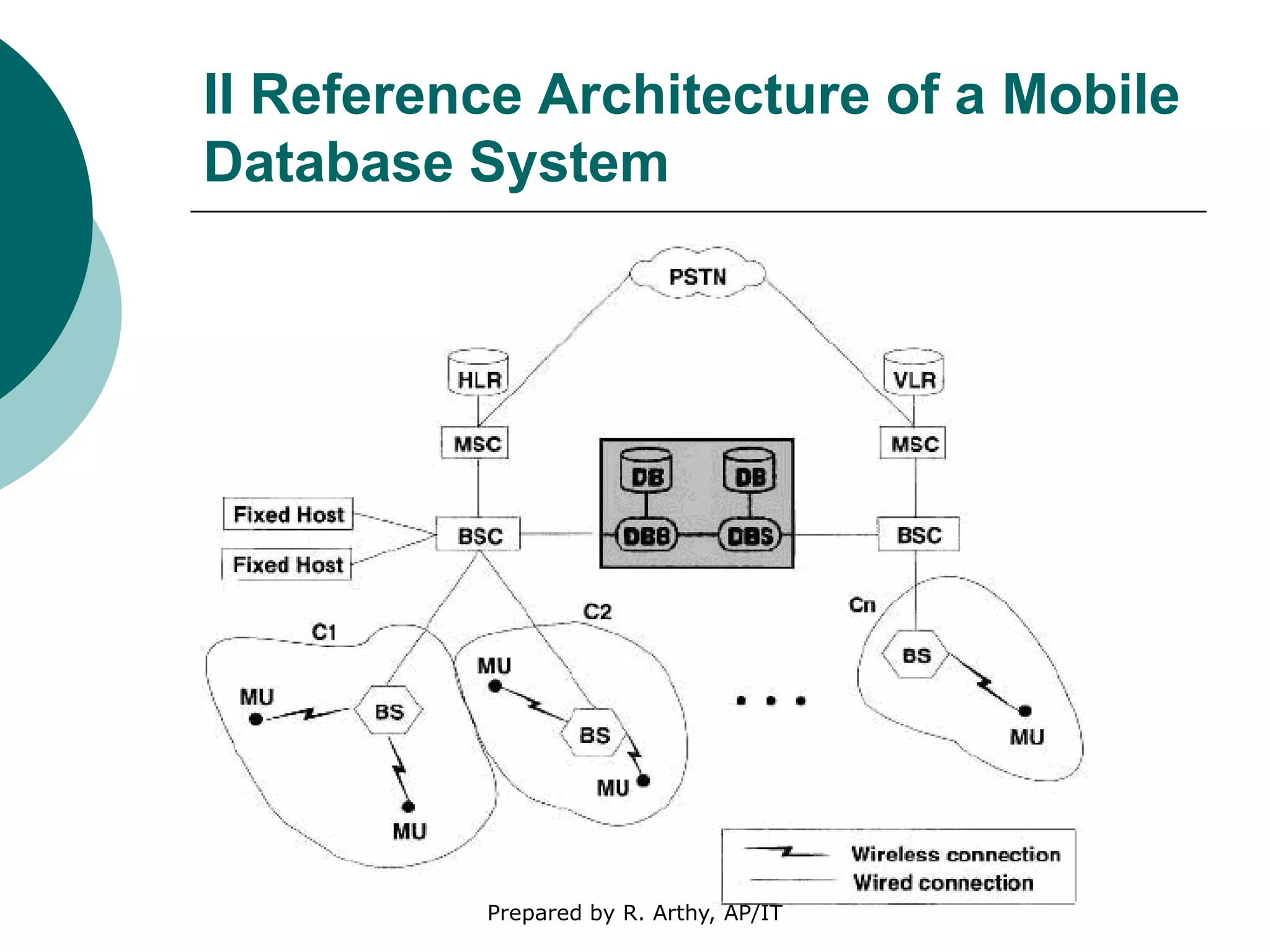
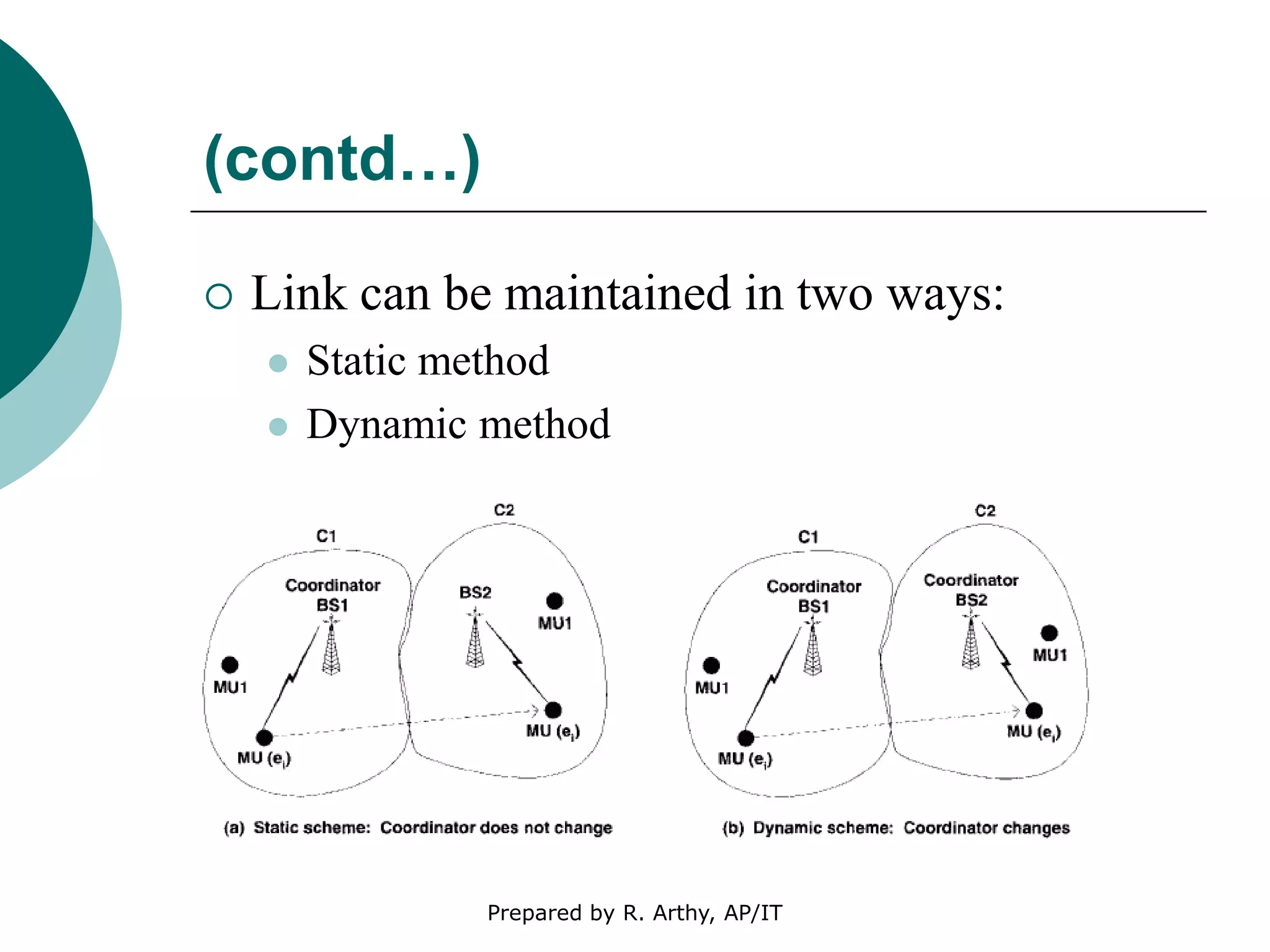
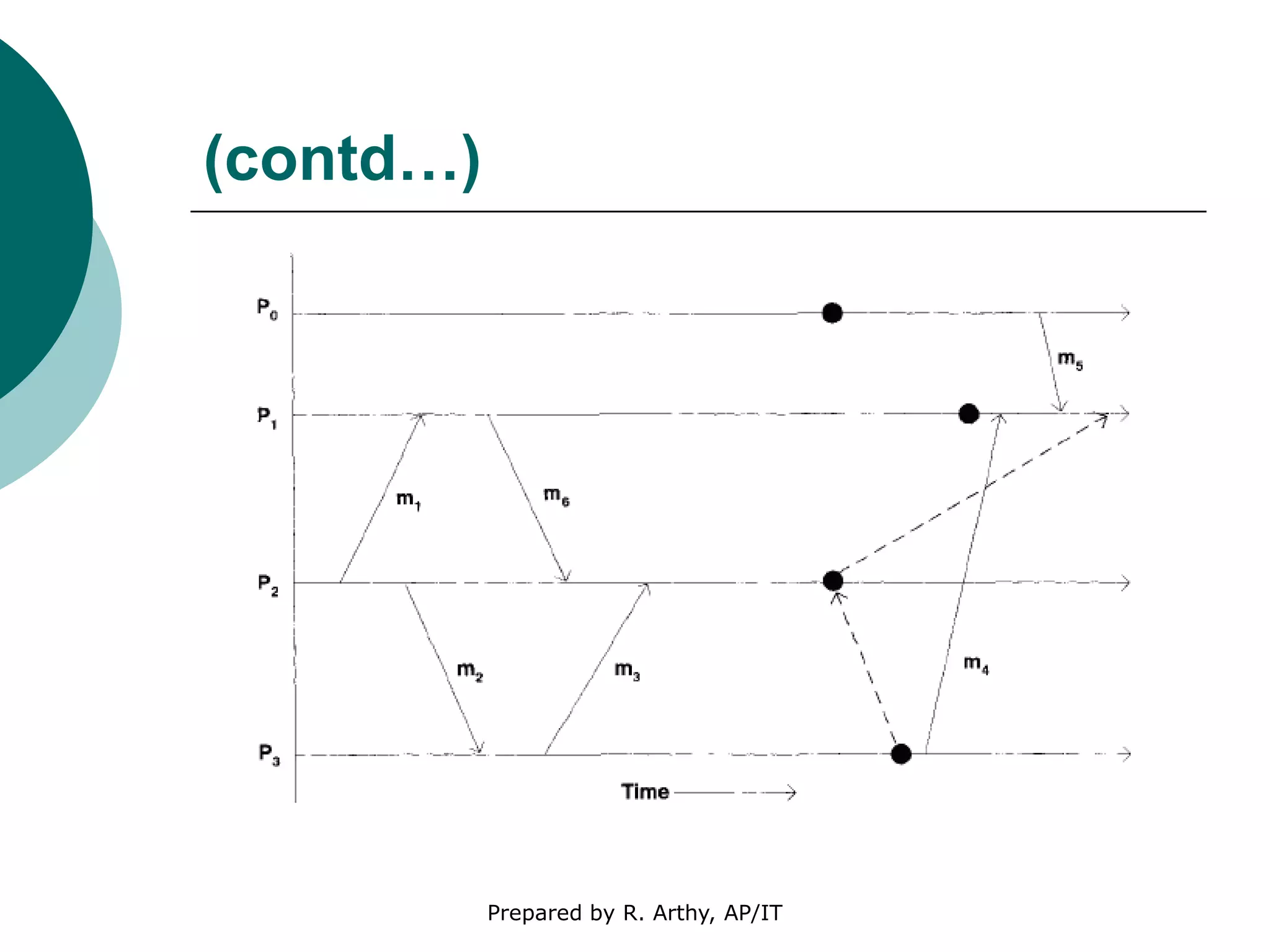
This document discusses location management and handoff management in mobile databases. It covers topics like location lookup, location update, location area, paging area, types of handoff (hard, soft), and challenges of mobility like ensuring atomicity, consistency, isolation and durability of transactions. It also summarizes different mobile transaction models like HiCoMo, Moflex, Kangaroo and Mobilaction that aim to process transactions reliably in a mobile environment with intermittent connectivity.