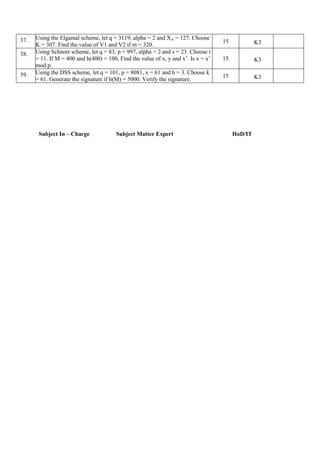
This document contains a question bank for the subject Cryptography and Network Security. It includes questions grouped under different units of the subject: Introduction and Number Theory, Block Ciphers and Public Key Cryptography, Hash Functions and Digital Signatures. For each question, it provides the question number, question, marks allotted, knowledge level and number of times the question may appear in the assessment. The document also provides details of the subject code, name, class, staff in-charge and course code.