1x ev do hard handoff
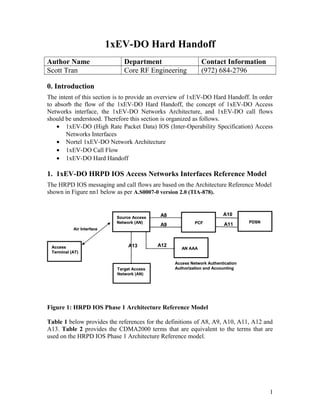
- 1. 1xEV-DO Hard Handoff Author Name Department Contact Information Scott Tran Core RF Engineering (972) 684-2796 0. Introduction The intent of this section is to provide an overview of 1xEV-DO Hard Handoff. In order to absorb the flow of the 1xEV-DO Hard Handoff, the concept of 1xEV-DO Access Networks interface, the 1xEV-DO Networks Architecture, and 1xEV-DO call flows should be understood. Therefore this section is organized as follows. • 1xEV-DO (High Rate Packet Data) IOS (Inter-Operability Specification) Access Networks Interfaces • Nortel 1xEV-DO Network Architecture • 1xEV-DO Call Flow • 1xEV-DO Hard Handoff 1. 1xEV-DO HRPD IOS Access Networks Interfaces Reference Model The HRPD IOS messaging and call flows are based on the Architecture Reference Model shown in Figure nn1 below as per A.S0007-0 version 2.0 (TIA-878). Figure 1: HRPD IOS Phase 1 Architecture Reference Model Table 1 below provides the references for the definitions of A8, A9, A10, A11, A12 and A13. Table 2 provides the CDMA2000 terms that are equivalent to the terms that are used on the HRPD IOS Phase 1 Architecture Reference model. 1 Source Access Network (AN) Target Access Network (AN) Access Terminal (AT) PCF PDSN AN AAA Air Interface A13 A8 A9 A10 A11 A12 Access Network Authentication Authorization and Accounting Source Access Network (AN) Target Access Network (AN) Access Terminal (AT) Access Terminal (AT) PCFPCF PDSNPDSN AN AAAAN AAA Air Interface A13 A8 A9 A10 A11 A12 Access Network Authentication Authorization and Accounting
- 2. Table 1: Definitions for the HRPF IOS interface. Interface Description A8 – A9 (AN – PCF) Interface TIA/EIA-2001-A delta text (Annex B) A10 – A11 (PCF – PDSN) Interface TIA/EIA-2001-A delta text (Annex C) A12 (AN – AN AAA) Interface New HRDP IOS defined text (Section 2.3) A13 (AN – AN) Interface New HRDP IOS defined text (Section 2.4) Table 2: CDMA2000 Term equivalent to HRPD Term CDMA2000 Term HRPD Term BS AN Base Station Access Network BSC AN Base Station Controller Access Network MS Access Network Mobile Station Access Network 2. Nortel 1xEV-DO Network Architecture A 1xEV-DO carrier provides only data service. The network required for 1xE-DO technology is an end-to-end IP data network. An access terminal talks to a basestation or an access point (AP) over the air. The basestation is connected to a radio node controller (RNC) or an access network controller (ANC). A RNC is responsible for radio resource management as well as mobility management. A RNC/ANC in a 1xEV-DO network has similar functionality as a basestation controller (BSC) in a 1xRTT network. However, a RNC does not interact with a Mobile Switch Center (MSC) as a BSC does in a 1xRTT network. A PDSN is a gateway to public data networks in a 1xEV-DO network. A network reference diagram for 1xEV-DO network is shown in Figure 2 2
- 3. BSC PDSN MSC PDN PSTN Carrier IP Internet 1xRTT Backhaul Metrocell BTS & 1xEV-DO AP 1xEV-DO Module (DOM) DO-EMSDO-RNC AN-AAA PDSN - AAA BSC PDSN MSC PDNPDN PSTNPSTN Carrier IP Internet Carrier IP Internet 1xRTT Backhaul Metrocell BTS & 1xEV-DO AP 1xEV-DO Module (DOM) DO-EMSDO-RNC AN-AAA PDSN - AAA Figure 2: Nortel Network 1xEV-DO Network Architecture 3. 1xEV-DO Call Flow When a 1xEV-DO access terminal is turned on for the first time, it requests a Unicast Access Terminal Identifier (UATI) from the access network. A RNC assigns a unique UATI to each mobile in its serving area. Every RNC/ANC assign it owns UATI to mobiles in its serving. After UATI assignment, a 1xEV-DO session is established between the mobile and the RNC. The session parameters are negotiated during the session establishment process. If A12 interface is deployed, the access terminal authentication is performed. A 1xEV-DO session establishment between a mobile and a RNC/ANC is equivalent to a registration in cellular networks. The RNC/ANC sends a R-P session registration request to the PDSN for the mobile. Once R-P session is established, the next step is a PPP session establishment between the mobile and the PDSN. The mobile is authenticated at the PDSN, and is assigned an IP address during this process. Once PPP session is established, the mobile is ready to transmit and receive IP data packets. Figure 3 shows the message flow for 1xEV-DO session establishment. 3
- 4. Figure 3: 1xEV-DO Call Flow 4. Handoffs in 1xEV-DO networks There are three levels of hierarchic in a 1xEV-DO network for mobility management. The first level of mobility is between basestations of same RNCs/ANCs. The second level of mobility is across the boundary of RNCs/ANCs served by the same PDSN. The third level of mobility is across PDSNs as shown in Figure 4. BTS BTS BTS BTS BTS BTS RNC RNCRNC PDSN PDSN Home Agent Mobility between PDSNs (Mobile IP) Mobility between RNCs (R-P Session Handoff) Mobility between BTS’ BTS BTS BTS BTS BTS BTSBTS BTS BTS BTS BTS BTS RNC RNCRNCRNC RNCRNC PDSN PDSNPDSN PDSN Home Agent Mobility between PDSNs (Mobile IP) Mobility between RNCs (R-P Session Handoff) Mobility between BTS’ Figure 4 Reference Mobility Model 4 PDSNAT AN ANAAA UATI-Request UATI- Assignment UATI-Complete Session Establishment PPP&LCPNegotiation CHAPChallenge- Response A12Access - Request A12Access- Accept CHAP– AuthenticationSuccess A11– RegistrationRequest A11- Registration Reply Establish PPPconnection TransmittingPacket Data PDSNAT AN ANAAA UATI-Request UATI- Assignment UATI-Complete Session Establishment PPP&LCPNegotiation CHAPChallenge- Response A12Access - Request A12Access- Accept CHAP– AuthenticationSuccess A11– RegistrationRequest A11- Registration Reply Establish PPPconnection TransmittingPacket Data
- 5. There are following different types of handoff in a 1xEV-DO network and a 1xEV-DO – 1xRTT hybrid network. • Intra RNC/ANC Inter AN/AP Handoff (this type of handoff is already explained in the above section) • Inter RNC/ANC and Intra PDSN Handoff • Inter RNC/ANC and Inter PDSN Handoff • 1xEV-DO to 1xRTT Handoff • 1xRTT to 1xEV-DO Handoff 5. Inter RNC/ANC and Intra PDSN Handoff As the signal strength of a target cell exceeds a handoff trigger threshold, an active mobile may request a handoff. If the target cell is not in the area of the serving RNC, the request is ignored. There is no inter RNC soft handoff in a 1xEV-DO network. As the mobile continues to move towards the target cell, the RF connection may be dropped. The mobile camps on the target cell, and it starts a new 1xEV-DO session on the target RNC. The target RNC can request the session information from the source RNC if A13 interface is deployed between the source and the target RNCs. If A13 is not deployed, the target RNC goes through 1xEV-DO session establishment process with the access terminal. The target RNC requests a new R-P session for the mobile from the PDSN. The R-P sessions are anchored on IMSI. When the PDSN receives the request for a new R-P session, it realizes that a R-P session exists for the mobile. It clears the old R-P session, and establishes a new R-P session. The PPP session between the PDSN and the mobile is not changed during this R-P session handoff. The mobile continues to use the same IP address. 6. Inter RNC and Inter PDSN handoff If the target RNC is not hosted by the source PDSN, a new PPP session has to be established between the mobile and the new PDSN. If mobile IP is deployed and the PDSN acts a foreign agent, the mobile will get register a new care-of-address of its new foreign agent/PDSN. With mobile IP, the mobile can continue to use the same IP address as it moves across the PDSNs. The change in PDSNs is transparent to the end application. However, the process of mobile IP handoff is much longer than the process of R-P session handoff in an intra PDSN handoff. If mobile IP is not deployed, the mobile will get a new IP address during inter PDSN handoffs. The mobile will have to restart it active IP applications. 7. 1xEV-DO to 1xRTT Handoff As long as a 1xEV-DO carrier is available, a hybrid terminal will continue to camp on the 1xEV-DO carrier for the data service. 1xEV-DO to 1xRTT handoff takes place when a mobile moves out of 1xEV-DO coverage. This handoff takes placed in only dormant mode. There is no active or soft handoff between 1xEV-DO and 1xRTT carriers. 5
- 6. When a hybrid terminal moves out of 1xEV-DO coverage area and 1xRTT is available, it registers with the 1xRTT network for data service. The BSC sends a request to a PDSN to establish a new R-P session for the mobile. If the R-P session request is sent to the same PDSN where the mobile had its PPP session for 1xEV-DO, and its IMSI is the same as its IMSI in 1xEV-DO network, the PDSN will continue to use the same PPP session with the hybrid terminal. Otherwise, a new PPP session is established between the PDSN and the mobile. The mobile will get a new IP address if mobile IP is not deployed. If mobile IP is deployed, it will perform mobile IP registration and continue to use the same IP address. Hybrid terminal monitor 1xRTT forward link paging/control channel for voice pages both in dormant and active states. They are able to monitor two control channels in the dormant mode because the control channels are in slotted mode operation for both 1xEV- DO and 1xRTT networks. In 1xEV-DO active state hybrid terminal can monitor 1xRTT paging channel because the forward link in the active mode is time division multiplexed. If there is a page for voice call on 1xRTT paging channel for a hybrid terminal, the hybrid terminal will clear 1xEV-DO connection and establish a voice call connection on 1xRTT. A hybrid terminal can not monitor 1xEV-DO control channel during a 1xRTT call. It searches for 1xEV-DO control channel after it terminates 1xRTT call. 8. 1xRTT to 1xEV-DO Handoff A hybrid terminal can monitor 1xEV-DO control channel while it is not in 1xRTT active call. A hybrid terminal searches for the 1xEV-DO carrier every 3 minutes in a deep sleep mode. If the access terminal finds a 1xEV-DO carrier, it will camp on 1xEV-DO carrier for data services. The access terminal will establish a new 1xEV-DO session with 1xEV- DO network. If the access terminal already has a 1xEV-DO session, it will send an unsolicited location update notification to 1xEV-DO network. This notification has a message tells 1xEV-DO network that the access terminal has moved into its coverage area. If the source BSC and the target RNC are served by the same PDSN, there can be a R-P session handoff and the mobile can continue to use the same PPP session. Otherwise, the access terminal either will have to rely on mobile IP to continue to use the same IP address or establish a new PPP session with the target PDSN. 9. HHO Trigger Method For the phase I commercial 1xEV-DO, all the hard handoff scenarios mentioned above is performed by dormant trigger method with “Packet Zone ID” changed. Therefore there is a case that if the AT is moving from source cell to target cell and the data transferring still active, then the RF connection is dropped due to “out of coverage” from source. The data transferring session is delay for duration until the AT detects the target cell signal. Then the AT will be on traffic channel and the data transferring session will continue. For the connection drop case, the end user may experience some delay at application level just like in the case of network congestion. Therefore, the end user does not notice RF connection drops directly. 6
- 7. When a hybrid terminal moves out of 1xEV-DO coverage area and 1xRTT is available, it registers with the 1xRTT network for data service. The BSC sends a request to a PDSN to establish a new R-P session for the mobile. If the R-P session request is sent to the same PDSN where the mobile had its PPP session for 1xEV-DO, and its IMSI is the same as its IMSI in 1xEV-DO network, the PDSN will continue to use the same PPP session with the hybrid terminal. Otherwise, a new PPP session is established between the PDSN and the mobile. The mobile will get a new IP address if mobile IP is not deployed. If mobile IP is deployed, it will perform mobile IP registration and continue to use the same IP address. Hybrid terminal monitor 1xRTT forward link paging/control channel for voice pages both in dormant and active states. They are able to monitor two control channels in the dormant mode because the control channels are in slotted mode operation for both 1xEV- DO and 1xRTT networks. In 1xEV-DO active state hybrid terminal can monitor 1xRTT paging channel because the forward link in the active mode is time division multiplexed. If there is a page for voice call on 1xRTT paging channel for a hybrid terminal, the hybrid terminal will clear 1xEV-DO connection and establish a voice call connection on 1xRTT. A hybrid terminal can not monitor 1xEV-DO control channel during a 1xRTT call. It searches for 1xEV-DO control channel after it terminates 1xRTT call. 8. 1xRTT to 1xEV-DO Handoff A hybrid terminal can monitor 1xEV-DO control channel while it is not in 1xRTT active call. A hybrid terminal searches for the 1xEV-DO carrier every 3 minutes in a deep sleep mode. If the access terminal finds a 1xEV-DO carrier, it will camp on 1xEV-DO carrier for data services. The access terminal will establish a new 1xEV-DO session with 1xEV- DO network. If the access terminal already has a 1xEV-DO session, it will send an unsolicited location update notification to 1xEV-DO network. This notification has a message tells 1xEV-DO network that the access terminal has moved into its coverage area. If the source BSC and the target RNC are served by the same PDSN, there can be a R-P session handoff and the mobile can continue to use the same PPP session. Otherwise, the access terminal either will have to rely on mobile IP to continue to use the same IP address or establish a new PPP session with the target PDSN. 9. HHO Trigger Method For the phase I commercial 1xEV-DO, all the hard handoff scenarios mentioned above is performed by dormant trigger method with “Packet Zone ID” changed. Therefore there is a case that if the AT is moving from source cell to target cell and the data transferring still active, then the RF connection is dropped due to “out of coverage” from source. The data transferring session is delay for duration until the AT detects the target cell signal. Then the AT will be on traffic channel and the data transferring session will continue. For the connection drop case, the end user may experience some delay at application level just like in the case of network congestion. Therefore, the end user does not notice RF connection drops directly. 6