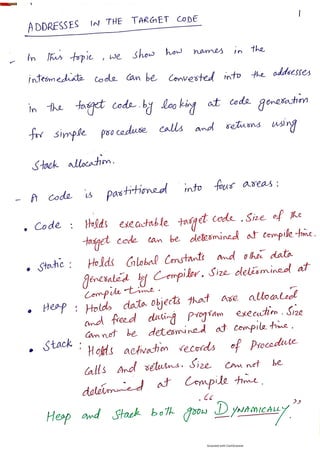
Address in the target code in Compiler Construction
•
0 likes•5,035 views
Address in the target code in compiler design Compiler Construction
Report
Share
Report
Share
Download to read offline
Recommended
Basic blocks and flow graph in Compiler Construction

Basic blocks and flow graph in compiler design
Compiler Construction
Peephole optimization techniques in compiler design

This document discusses various compiler optimization techniques, focusing on peephole optimization. It defines optimization as transforming code to run faster or use less memory without changing functionality. Optimization can be machine-independent, transforming code regardless of hardware, or machine-dependent, tailored to a specific architecture. Peephole optimization examines small blocks of code and replaces them with faster or smaller equivalents using techniques like constant folding, strength reduction, null sequence elimination, and algebraic laws. Common replacement rules aim to improve performance, reduce memory usage, and decrease code size.
Principal source of optimization in compiler design

Unit 5 Principal source of optimization in compiler design in SRM IST, Kattankulathur by Prof. R. Rajkumar AP | CSE | SRM IST
Computer Network notes (handwritten) UNIT 1

Introduction of computer network, layered architecture, topology, guided and unguided media, signals, multiplexing, OSI vs TCP/IP , IP address, TCP , UDP, DHCP, DNS, HTTP, etc.
Register allocation and assignment

This document discusses various strategies for register allocation and assignment in compiler design. It notes that assigning values to specific registers simplifies compiler design but can result in inefficient register usage. Global register allocation aims to assign frequently used values to registers for the duration of a single block. Usage counts provide an estimate of how many loads/stores could be saved by assigning a value to a register. Graph coloring is presented as a technique where an interference graph is constructed and coloring aims to assign registers efficiently despite interference between values.
Learning set of rules

The document discusses sequential covering algorithms for learning rule sets from data. It describes how sequential covering algorithms work by iteratively learning one rule at a time to cover examples, removing covered examples, and repeating until all examples are covered. It also discusses variations of this approach, including using a general-to-specific beam search to learn each rule and alternatives like the AQ algorithm that learn rules to cover specific target values. Finally, it describes how first-order logic can be used to learn more general rules than propositional logic by representing relationships between attributes.
Concept learning

The document discusses different approaches for concept learning from examples, including viewing it as a search problem to find the hypothesis that best fits the training examples. It also describes the general-to-specific learning approach, where the goal is to find the maximally specific hypothesis consistent with the positive training examples by starting with the most general hypothesis and replacing constraints to better fit the examples. The document also discusses the version space and candidate elimination algorithms for obtaining the version space of all hypotheses consistent with the training data.
Recommended
Basic blocks and flow graph in Compiler Construction

Basic blocks and flow graph in compiler design
Compiler Construction
Peephole optimization techniques in compiler design

This document discusses various compiler optimization techniques, focusing on peephole optimization. It defines optimization as transforming code to run faster or use less memory without changing functionality. Optimization can be machine-independent, transforming code regardless of hardware, or machine-dependent, tailored to a specific architecture. Peephole optimization examines small blocks of code and replaces them with faster or smaller equivalents using techniques like constant folding, strength reduction, null sequence elimination, and algebraic laws. Common replacement rules aim to improve performance, reduce memory usage, and decrease code size.
Principal source of optimization in compiler design

Unit 5 Principal source of optimization in compiler design in SRM IST, Kattankulathur by Prof. R. Rajkumar AP | CSE | SRM IST
Computer Network notes (handwritten) UNIT 1

Introduction of computer network, layered architecture, topology, guided and unguided media, signals, multiplexing, OSI vs TCP/IP , IP address, TCP , UDP, DHCP, DNS, HTTP, etc.
Register allocation and assignment

This document discusses various strategies for register allocation and assignment in compiler design. It notes that assigning values to specific registers simplifies compiler design but can result in inefficient register usage. Global register allocation aims to assign frequently used values to registers for the duration of a single block. Usage counts provide an estimate of how many loads/stores could be saved by assigning a value to a register. Graph coloring is presented as a technique where an interference graph is constructed and coloring aims to assign registers efficiently despite interference between values.
Learning set of rules

The document discusses sequential covering algorithms for learning rule sets from data. It describes how sequential covering algorithms work by iteratively learning one rule at a time to cover examples, removing covered examples, and repeating until all examples are covered. It also discusses variations of this approach, including using a general-to-specific beam search to learn each rule and alternatives like the AQ algorithm that learn rules to cover specific target values. Finally, it describes how first-order logic can be used to learn more general rules than propositional logic by representing relationships between attributes.
Concept learning

The document discusses different approaches for concept learning from examples, including viewing it as a search problem to find the hypothesis that best fits the training examples. It also describes the general-to-specific learning approach, where the goal is to find the maximally specific hypothesis consistent with the positive training examples by starting with the most general hypothesis and replacing constraints to better fit the examples. The document also discusses the version space and candidate elimination algorithms for obtaining the version space of all hypotheses consistent with the training data.
IOT Platform Design Methodology 

The document outlines the key steps in an IoT design methodology:
1. Define the purpose, requirements, and use cases of the system.
2. Specify the domain model, information model, services, and IoT level.
3. Develop functional and operational views describing the system components and how they will communicate and operate.
4. Integrate the physical devices and components and draw schematics.
5. Develop the IoT application to implement the designed system.
Unit 2,3,4 _ Internet of Things A Hands-On Approach (Arshdeep Bahga, Vijay Ma...

This document discusses the development of a new type of battery that could revolutionize energy storage. It describes how the battery uses a solid electrolyte material that conducts ions quickly and prevents short circuits. This new battery design could lead to batteries that charge faster, last longer, and are less flammable than current lithium-ion batteries. The document concludes by stating that further research is still needed but that this new battery technology shows significant potential.
Genetic algorithms vs Traditional algorithms

Genetic algorithms and traditional algorithms differ in their definitions, usages, and complexity. Genetic algorithms are based on genetics and natural selection, and help find optimal solutions to difficult problems. They are more advanced than traditional algorithms which provide step-by-step procedures. Genetic algorithms are used in fields like machine learning and artificial intelligence, while traditional algorithms are used in programming and mathematics.
COMPILER DESIGN Run-Time Environments

Run-Time Environments: Storage organization, Stack Allocation of Space, Access to Nonlocal Data on the Stack, Heap Management, Introduction to Garbage Collection, Introduction to Trace-Based Collection. Code Generation: Issues in the Design of a Code Generator, The Target Language, Addresses in the Target Code, Basic Blocks and Flow Graphs, Optimization of Basic Blocks, A Simple Code Generator, Peephole Optimization, Register Allocation and Assignment, Dynamic Programming Code-Generation
Region based segmentation

This document discusses region-based image segmentation techniques. Region-based segmentation groups pixels into regions based on common properties. Region growing is described as starting with seed points and grouping neighboring pixels with similar properties into larger regions. The advantages are it can correctly separate regions with the same defined properties and provide good segmentation in images with clear edges. The disadvantages include being computationally expensive and sensitive to noise. Region splitting and merging techniques are also discussed as alternatives to region growing.
Histogram Processing

Histogram Processing
Histogram Equalization
Histogram Matching
Local Histogram processing
Using histogram statistics for image enhancement
Uses for Histogram Processing
Histogram Equalization
Histogram Matching
Local Histogram Processing
Basics of Spatial Filtering
Symbol table in compiler Design

The document discusses symbol tables, which are data structures used by compilers to track semantic information about identifiers, variables, functions, classes, etc. It provides details on:
- How various compiler phases like lexical analysis, syntax analysis, semantic analysis, code generation utilize and update the symbol table.
- Common data structures used to implement symbol tables like linear lists, hash tables and how they work.
- The information typically stored for different symbols like name, type, scope, memory location etc.
- Organization of symbol tables for block-structured vs non-block structured languages, including using multiple nested tables vs a single global table.
Mobile Transport layer

This document discusses various approaches to improving TCP performance over mobile networks. It describes Indirect TCP, Snooping TCP, Mobile TCP, optimizations like fast retransmit/recovery and transmission freezing, and transaction-oriented TCP. Each approach is summarized in terms of its key mechanisms, advantages, and disadvantages. Overall, the document evaluates different ways TCP has been adapted to better support mobility and address challenges like frequent disconnections, packet losses during handovers, and high bit error rates over wireless links.
Intermediate code generation (Compiler Design) 

Compiler Design
Discuss Topics: Intermediate code generation
three address code generation
quadruple,triple,Indirect triple etc
Unit iv(simple code generator)

The document describes a simple code generator that generates target code for a sequence of three-address statements. It tracks register availability using register descriptors and variable locations using address descriptors. For each statement, it determines the locations of operands, copies them to a register if needed, performs the operation, updates the register and address descriptors, and stores values before procedure calls or basic block boundaries. It uses a getreg function to determine register allocation. Conditional statements are handled using compare and jump instructions and condition codes.
Kevin Knight, Elaine Rich, B. Nair - Artificial Intelligence (2010, Tata McGr...

This document discusses the history of chocolate production. It details how cocoa beans are harvested from cocoa trees and then fermented, dried, roasted, and ground into chocolate liquor. The liquor is then further processed through conching and tempering to produce chocolate in its familiar solid form.
State space search

This document discusses state space search in artificial intelligence. It defines state space search as consisting of a tree of symbolic states generated by iteratively applying operations to represent a problem. It discusses the initial, intermediate, and final states in state space search. As an example, it describes the water jug problem and its state representation. It also outlines different types of state space search algorithms, including heuristic search algorithms like A* and uninformed search algorithms like breadth-first search.
Digital Image Processing - Image Compression

Digital Image Processing - Image Compression (NOTES) Material or Tips for Engineering streams students
Measures of query cost

The document discusses measures of query cost in database management systems. It explains that query cost can be measured by factors like the number of disk accesses, size of the table, and time taken by the CPU. It further breaks down disk access time into components like seek time, rotational latency, and sequential vs. random I/O. The document then provides an example formula to calculate estimated query cost based on these components.
Learning by analogy

Analogical reasoning is a powerful learning tool that involves abstracting structural similarities between problems to apply solutions from known problems to new ones. The process involves developing mappings between instances and retrieving, reusing, revising, and retaining experiences. Transformational analogy transforms a previous solution by making substitutions for the new problem, while derivational analogy considers the detailed problem-solving histories to apply analogies.
Image compression models

This document discusses data compression techniques for digital images. It explains that compression reduces the amount of data needed to represent an image by removing redundant information. The compression process involves an encoder that transforms the input image, and a decoder that reconstructs the output image. The encoder uses three main stages: a mapper to reduce interpixel redundancy, a quantizer to reduce accuracy and psychovisual redundancy, and a symbol encoder to assign variable-length codes to the quantized values. The decoder performs the inverse operations of the encoder and mapper to reconstruct the original image, but does not perform the inverse of quantization which is a lossy process.
Agents in Artificial intelligence 

The document discusses different types of intelligent agents based on their architecture and programs. It describes five classes of agents: 1) Simple Reflex agents which react solely based on current percepts; 2) Model-based agents which use an internal model of the world; 3) Goal-based agents which take actions to reduce distance to a goal; 4) Utility-based agents which choose actions to maximize utility; and 5) Learning agents which are able to learn from experiences. The document also outlines different forms of learning like rote learning, learning from instruction, and reinforcement learning.
Decomposition technique In Software Engineering 

The document discusses different techniques for estimating software project costs and effort, including decomposition, sizing, and function point analysis. It provides an example of estimating the lines of code and function points for a mechanical CAD software project. Estimates are developed by decomposing the problem into smaller elements and tasks, and estimating the effort required for each. The accuracy of estimates depends on properly sizing the software and having reliable past project metrics.
And or graph

The document discusses AND/OR graphs, which are a type of graph or tree used to represent solutions to problems that can be decomposed into smaller subproblems. AND/OR graphs have nodes that represent goals or states, with successors labeled as either AND or OR branches. AND branches signify subgoals that must all be achieved to satisfy the parent goal, while OR branches indicate alternative subgoals that could achieve the parent goal. The graph helps model how decomposed subproblems relate and their solutions combine to solve the overall problem.
Heap management in Compiler Construction

Heap management in Compiler Construction
Compiler Construction
Compiler Design
Storage organization and stack allocation of space

Storage organization and stack allocation of space
Compiler Construction
Compiler Design
More Related Content
What's hot
IOT Platform Design Methodology 

The document outlines the key steps in an IoT design methodology:
1. Define the purpose, requirements, and use cases of the system.
2. Specify the domain model, information model, services, and IoT level.
3. Develop functional and operational views describing the system components and how they will communicate and operate.
4. Integrate the physical devices and components and draw schematics.
5. Develop the IoT application to implement the designed system.
Unit 2,3,4 _ Internet of Things A Hands-On Approach (Arshdeep Bahga, Vijay Ma...

This document discusses the development of a new type of battery that could revolutionize energy storage. It describes how the battery uses a solid electrolyte material that conducts ions quickly and prevents short circuits. This new battery design could lead to batteries that charge faster, last longer, and are less flammable than current lithium-ion batteries. The document concludes by stating that further research is still needed but that this new battery technology shows significant potential.
Genetic algorithms vs Traditional algorithms

Genetic algorithms and traditional algorithms differ in their definitions, usages, and complexity. Genetic algorithms are based on genetics and natural selection, and help find optimal solutions to difficult problems. They are more advanced than traditional algorithms which provide step-by-step procedures. Genetic algorithms are used in fields like machine learning and artificial intelligence, while traditional algorithms are used in programming and mathematics.
COMPILER DESIGN Run-Time Environments

Run-Time Environments: Storage organization, Stack Allocation of Space, Access to Nonlocal Data on the Stack, Heap Management, Introduction to Garbage Collection, Introduction to Trace-Based Collection. Code Generation: Issues in the Design of a Code Generator, The Target Language, Addresses in the Target Code, Basic Blocks and Flow Graphs, Optimization of Basic Blocks, A Simple Code Generator, Peephole Optimization, Register Allocation and Assignment, Dynamic Programming Code-Generation
Region based segmentation

This document discusses region-based image segmentation techniques. Region-based segmentation groups pixels into regions based on common properties. Region growing is described as starting with seed points and grouping neighboring pixels with similar properties into larger regions. The advantages are it can correctly separate regions with the same defined properties and provide good segmentation in images with clear edges. The disadvantages include being computationally expensive and sensitive to noise. Region splitting and merging techniques are also discussed as alternatives to region growing.
Histogram Processing

Histogram Processing
Histogram Equalization
Histogram Matching
Local Histogram processing
Using histogram statistics for image enhancement
Uses for Histogram Processing
Histogram Equalization
Histogram Matching
Local Histogram Processing
Basics of Spatial Filtering
Symbol table in compiler Design

The document discusses symbol tables, which are data structures used by compilers to track semantic information about identifiers, variables, functions, classes, etc. It provides details on:
- How various compiler phases like lexical analysis, syntax analysis, semantic analysis, code generation utilize and update the symbol table.
- Common data structures used to implement symbol tables like linear lists, hash tables and how they work.
- The information typically stored for different symbols like name, type, scope, memory location etc.
- Organization of symbol tables for block-structured vs non-block structured languages, including using multiple nested tables vs a single global table.
Mobile Transport layer

This document discusses various approaches to improving TCP performance over mobile networks. It describes Indirect TCP, Snooping TCP, Mobile TCP, optimizations like fast retransmit/recovery and transmission freezing, and transaction-oriented TCP. Each approach is summarized in terms of its key mechanisms, advantages, and disadvantages. Overall, the document evaluates different ways TCP has been adapted to better support mobility and address challenges like frequent disconnections, packet losses during handovers, and high bit error rates over wireless links.
Intermediate code generation (Compiler Design) 

Compiler Design
Discuss Topics: Intermediate code generation
three address code generation
quadruple,triple,Indirect triple etc
Unit iv(simple code generator)

The document describes a simple code generator that generates target code for a sequence of three-address statements. It tracks register availability using register descriptors and variable locations using address descriptors. For each statement, it determines the locations of operands, copies them to a register if needed, performs the operation, updates the register and address descriptors, and stores values before procedure calls or basic block boundaries. It uses a getreg function to determine register allocation. Conditional statements are handled using compare and jump instructions and condition codes.
Kevin Knight, Elaine Rich, B. Nair - Artificial Intelligence (2010, Tata McGr...

This document discusses the history of chocolate production. It details how cocoa beans are harvested from cocoa trees and then fermented, dried, roasted, and ground into chocolate liquor. The liquor is then further processed through conching and tempering to produce chocolate in its familiar solid form.
State space search

This document discusses state space search in artificial intelligence. It defines state space search as consisting of a tree of symbolic states generated by iteratively applying operations to represent a problem. It discusses the initial, intermediate, and final states in state space search. As an example, it describes the water jug problem and its state representation. It also outlines different types of state space search algorithms, including heuristic search algorithms like A* and uninformed search algorithms like breadth-first search.
Digital Image Processing - Image Compression

Digital Image Processing - Image Compression (NOTES) Material or Tips for Engineering streams students
Measures of query cost

The document discusses measures of query cost in database management systems. It explains that query cost can be measured by factors like the number of disk accesses, size of the table, and time taken by the CPU. It further breaks down disk access time into components like seek time, rotational latency, and sequential vs. random I/O. The document then provides an example formula to calculate estimated query cost based on these components.
Learning by analogy

Analogical reasoning is a powerful learning tool that involves abstracting structural similarities between problems to apply solutions from known problems to new ones. The process involves developing mappings between instances and retrieving, reusing, revising, and retaining experiences. Transformational analogy transforms a previous solution by making substitutions for the new problem, while derivational analogy considers the detailed problem-solving histories to apply analogies.
Image compression models

This document discusses data compression techniques for digital images. It explains that compression reduces the amount of data needed to represent an image by removing redundant information. The compression process involves an encoder that transforms the input image, and a decoder that reconstructs the output image. The encoder uses three main stages: a mapper to reduce interpixel redundancy, a quantizer to reduce accuracy and psychovisual redundancy, and a symbol encoder to assign variable-length codes to the quantized values. The decoder performs the inverse operations of the encoder and mapper to reconstruct the original image, but does not perform the inverse of quantization which is a lossy process.
Agents in Artificial intelligence 

The document discusses different types of intelligent agents based on their architecture and programs. It describes five classes of agents: 1) Simple Reflex agents which react solely based on current percepts; 2) Model-based agents which use an internal model of the world; 3) Goal-based agents which take actions to reduce distance to a goal; 4) Utility-based agents which choose actions to maximize utility; and 5) Learning agents which are able to learn from experiences. The document also outlines different forms of learning like rote learning, learning from instruction, and reinforcement learning.
Decomposition technique In Software Engineering 

The document discusses different techniques for estimating software project costs and effort, including decomposition, sizing, and function point analysis. It provides an example of estimating the lines of code and function points for a mechanical CAD software project. Estimates are developed by decomposing the problem into smaller elements and tasks, and estimating the effort required for each. The accuracy of estimates depends on properly sizing the software and having reliable past project metrics.
And or graph

The document discusses AND/OR graphs, which are a type of graph or tree used to represent solutions to problems that can be decomposed into smaller subproblems. AND/OR graphs have nodes that represent goals or states, with successors labeled as either AND or OR branches. AND branches signify subgoals that must all be achieved to satisfy the parent goal, while OR branches indicate alternative subgoals that could achieve the parent goal. The graph helps model how decomposed subproblems relate and their solutions combine to solve the overall problem.
Heap management in Compiler Construction

Heap management in Compiler Construction
Compiler Construction
Compiler Design
What's hot (20)
Unit 2,3,4 _ Internet of Things A Hands-On Approach (Arshdeep Bahga, Vijay Ma...

Unit 2,3,4 _ Internet of Things A Hands-On Approach (Arshdeep Bahga, Vijay Ma...
Kevin Knight, Elaine Rich, B. Nair - Artificial Intelligence (2010, Tata McGr...

Kevin Knight, Elaine Rich, B. Nair - Artificial Intelligence (2010, Tata McGr...
More from Muhammad Haroon
Storage organization and stack allocation of space

Storage organization and stack allocation of space
Compiler Construction
Compiler Design
Intermediate code and three address instructions

Intermediate code and three address instructions
Compiler Construction
LR(0) parser in Compiler Consturction

The document describes parsing the string "aabb" using an LR(0) parser for a context-free grammar (CFG) with the following production rules: S → X X, X → a X, X → b.
Powerful presentation components and skills

This document discusses the key components and skills for creating powerful presentations. It outlines the main steps as plan, prepare, practice, and present. When planning, presenters should consider their audience, goals, timing and location. Preparation involves structuring the presentation, developing visual aids and prompts, and considering voice, appearance and style. Presenters are advised to practice their presentation multiple times with visual aids and rehearse handling questions. The document provides tips for engaging the audience and overcoming flaws to give a successful presentation.
Terms of reference in Professional Practices

Terms of Reference (TOR) is a strategy-level document that defines the tasks, duties, background, objectives, planned activities, expected inputs and outputs, budget, schedules, and job descriptions required of a project contractor. The purpose of a TOR is to specify the amount and type of work to be accomplished by the project and establish the relationships between stakeholders. TORs are developed once a project has been identified, defined and planned to judge the performance of contractors and consultants.
Code of conduct .

The document discusses codes of conduct and professional practices. It defines a code of conduct as a management tool that outlines an organization's values, responsibilities, and ethical obligations to provide guidance for employees. It also discusses how codes of conduct are developed based on core values and can vary between organizations. Violations of the code can result in disciplinary action following steps of progressive discipline such as verbal warnings, written warnings, suspension, and termination. Human resources professionals are responsible for communicating the code of conduct, investigating violations, and ensuring compliance with employment law.
Misuse of computer

This document discusses various forms of computer misuse and abuse, including hacking, viruses, copyright infringement, identity theft, and cyberbullying. It provides examples of each type of misuse and outlines laws and steps that have been taken to address this issue, such as the Computer Misuse Act of 1990, the Data Protection Act, and copyright law. Enforcement has included closing abusive chat rooms, reducing email spamming, and punishing spammers with fines. Overall the document covers the definition, examples, legal aspects, and solutions regarding computer and internet misuse and abuse.
7 habits of highly effective people

The document discusses the seven habits of highly effective people according to Stephen Covey. It covers each of the seven habits: 1) Be proactive by controlling your environment rather than reacting to things outside your control. 2) Begin with the end in mind by envisioning your goals and planning backwards. 3) Put first things first by prioritizing important tasks over urgent ones. 4) Think win-win by finding solutions where all parties benefit. 5) Seek first to understand others before being understood through empathic listening. 6) Synergize by valuing differences and building on strengths. 7) Sharpen the saw through continuous self-improvement.
Soft skills in Profession

Soft skills refer to personal qualities like communication skills, interpersonal skills, creativity, leadership, and personal skills that make someone compatible to work with and help them succeed in the workplace. These skills are required not just for entering the workplace but also sustaining a career as they help with decision making, relationships, communication, professional development, and making a good impression. Important soft skills include communication, interpersonal abilities, creativity, leadership, and personal qualities.
Career and career path

This document discusses career and career paths. It defines a career as a person's course through life, usually involving special training and considered their life's work. A career path is defined as a smaller group of jobs within a career cluster that use similar skills, with the potential for vertical or lateral movement between jobs. The document provides examples of career paths in various fields like administration, customer service, education, and engineering. It also outlines the typical career path for a software engineer and lists requirements for navigating a career path, such as continuously learning new skills, networking, flexibility, and being open to lateral career moves.
Copy rights, intellectual copy rights and patents

Copyrights and patents provide legal protections for creative works and inventions. Copyright protects published works from unauthorized use by indicating the word "Copyright" or symbol © and applies to software to prevent copying without permission. Patents grant an exclusive right to products and processes that offer new technical solutions, allowing the inventor to exclude others from making or selling the invention for a period of time. Together, copyrights, trademarks, and patents fall under intellectual property rights which protect original creative works and innovations.
Open source software, commercial software, freeware software, shareware softw...

The document discusses different types of software including open source software, commercial software, freeware software, shareware software, and proprietary software. Open source software is available freely with publicly accessible source code. Commercial software requires payment of licensing fees and has proprietary source code. Freeware is free to use but retains copyright, while shareware is initially free but requires payment to continue use after a trial period. Proprietary software is owned and controlled by an individual or company.
More from Muhammad Haroon (20)
Storage organization and stack allocation of space

Storage organization and stack allocation of space
Open source software, commercial software, freeware software, shareware softw...

Open source software, commercial software, freeware software, shareware softw...
Recently uploaded
Walmart Business+ and Spark Good for Nonprofits.pdf

"Learn about all the ways Walmart supports nonprofit organizations.
You will hear from Liz Willett, the Head of Nonprofits, and hear about what Walmart is doing to help nonprofits, including Walmart Business and Spark Good. Walmart Business+ is a new offer for nonprofits that offers discounts and also streamlines nonprofits order and expense tracking, saving time and money.
The webinar may also give some examples on how nonprofits can best leverage Walmart Business+.
The event will cover the following::
Walmart Business + (https://business.walmart.com/plus) is a new shopping experience for nonprofits, schools, and local business customers that connects an exclusive online shopping experience to stores. Benefits include free delivery and shipping, a 'Spend Analytics” feature, special discounts, deals and tax-exempt shopping.
Special TechSoup offer for a free 180 days membership, and up to $150 in discounts on eligible orders.
Spark Good (walmart.com/sparkgood) is a charitable platform that enables nonprofits to receive donations directly from customers and associates.
Answers about how you can do more with Walmart!"
Andreas Schleicher presents PISA 2022 Volume III - Creative Thinking - 18 Jun...

Andreas Schleicher, Director of Education and Skills at the OECD presents at the launch of PISA 2022 Volume III - Creative Minds, Creative Schools on 18 June 2024.
How to Setup Warehouse & Location in Odoo 17 Inventory

In this slide, we'll explore how to set up warehouses and locations in Odoo 17 Inventory. This will help us manage our stock effectively, track inventory levels, and streamline warehouse operations.
Wound healing PPT

This document provides an overview of wound healing, its functions, stages, mechanisms, factors affecting it, and complications.
A wound is a break in the integrity of the skin or tissues, which may be associated with disruption of the structure and function.
Healing is the body’s response to injury in an attempt to restore normal structure and functions.
Healing can occur in two ways: Regeneration and Repair
There are 4 phases of wound healing: hemostasis, inflammation, proliferation, and remodeling. This document also describes the mechanism of wound healing. Factors that affect healing include infection, uncontrolled diabetes, poor nutrition, age, anemia, the presence of foreign bodies, etc.
Complications of wound healing like infection, hyperpigmentation of scar, contractures, and keloid formation.
How Barcodes Can Be Leveraged Within Odoo 17

In this presentation, we will explore how barcodes can be leveraged within Odoo 17 to streamline our manufacturing processes. We will cover the configuration steps, how to utilize barcodes in different manufacturing scenarios, and the overall benefits of implementing this technology.
Mule event processing models | MuleSoft Mysore Meetup #47

Mule event processing models | MuleSoft Mysore Meetup #47
Event Link:- https://meetups.mulesoft.com/events/details/mulesoft-mysore-presents-mule-event-processing-models/
Agenda
● What is event processing in MuleSoft?
● Types of event processing models in Mule 4
● Distinction between the reactive, parallel, blocking & non-blocking processing
For Upcoming Meetups Join Mysore Meetup Group - https://meetups.mulesoft.com/mysore/YouTube:- youtube.com/@mulesoftmysore
Mysore WhatsApp group:- https://chat.whatsapp.com/EhqtHtCC75vCAX7gaO842N
Speaker:-
Shivani Yasaswi - https://www.linkedin.com/in/shivaniyasaswi/
Organizers:-
Shubham Chaurasia - https://www.linkedin.com/in/shubhamchaurasia1/
Giridhar Meka - https://www.linkedin.com/in/giridharmeka
Priya Shaw - https://www.linkedin.com/in/priya-shaw
مصحف القراءات العشر أعد أحرف الخلاف سمير بسيوني.pdf

مصحف أحرف الخلاف للقراء العشرةأعد أحرف الخلاف بالتلوين وصلا سمير بسيوني غفر الله له
Chapter wise All Notes of First year Basic Civil Engineering.pptx

Chapter wise All Notes of First year Basic Civil Engineering
Syllabus
Chapter-1
Introduction to objective, scope and outcome the subject
Chapter 2
Introduction: Scope and Specialization of Civil Engineering, Role of civil Engineer in Society, Impact of infrastructural development on economy of country.
Chapter 3
Surveying: Object Principles & Types of Surveying; Site Plans, Plans & Maps; Scales & Unit of different Measurements.
Linear Measurements: Instruments used. Linear Measurement by Tape, Ranging out Survey Lines and overcoming Obstructions; Measurements on sloping ground; Tape corrections, conventional symbols. Angular Measurements: Instruments used; Introduction to Compass Surveying, Bearings and Longitude & Latitude of a Line, Introduction to total station.
Levelling: Instrument used Object of levelling, Methods of levelling in brief, and Contour maps.
Chapter 4
Buildings: Selection of site for Buildings, Layout of Building Plan, Types of buildings, Plinth area, carpet area, floor space index, Introduction to building byelaws, concept of sun light & ventilation. Components of Buildings & their functions, Basic concept of R.C.C., Introduction to types of foundation
Chapter 5
Transportation: Introduction to Transportation Engineering; Traffic and Road Safety: Types and Characteristics of Various Modes of Transportation; Various Road Traffic Signs, Causes of Accidents and Road Safety Measures.
Chapter 6
Environmental Engineering: Environmental Pollution, Environmental Acts and Regulations, Functional Concepts of Ecology, Basics of Species, Biodiversity, Ecosystem, Hydrological Cycle; Chemical Cycles: Carbon, Nitrogen & Phosphorus; Energy Flow in Ecosystems.
Water Pollution: Water Quality standards, Introduction to Treatment & Disposal of Waste Water. Reuse and Saving of Water, Rain Water Harvesting. Solid Waste Management: Classification of Solid Waste, Collection, Transportation and Disposal of Solid. Recycling of Solid Waste: Energy Recovery, Sanitary Landfill, On-Site Sanitation. Air & Noise Pollution: Primary and Secondary air pollutants, Harmful effects of Air Pollution, Control of Air Pollution. . Noise Pollution Harmful Effects of noise pollution, control of noise pollution, Global warming & Climate Change, Ozone depletion, Greenhouse effect
Text Books:
1. Palancharmy, Basic Civil Engineering, McGraw Hill publishers.
2. Satheesh Gopi, Basic Civil Engineering, Pearson Publishers.
3. Ketki Rangwala Dalal, Essentials of Civil Engineering, Charotar Publishing House.
4. BCP, Surveying volume 1
Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum

(𝐓𝐋𝐄 𝟏𝟎𝟎) (𝐋𝐞𝐬𝐬𝐨𝐧 𝟏)-𝐏𝐫𝐞𝐥𝐢𝐦𝐬
𝐃𝐢𝐬𝐜𝐮𝐬𝐬 𝐭𝐡𝐞 𝐄𝐏𝐏 𝐂𝐮𝐫𝐫𝐢𝐜𝐮𝐥𝐮𝐦 𝐢𝐧 𝐭𝐡𝐞 𝐏𝐡𝐢𝐥𝐢𝐩𝐩𝐢𝐧𝐞𝐬:
- Understand the goals and objectives of the Edukasyong Pantahanan at Pangkabuhayan (EPP) curriculum, recognizing its importance in fostering practical life skills and values among students. Students will also be able to identify the key components and subjects covered, such as agriculture, home economics, industrial arts, and information and communication technology.
𝐄𝐱𝐩𝐥𝐚𝐢𝐧 𝐭𝐡𝐞 𝐍𝐚𝐭𝐮𝐫𝐞 𝐚𝐧𝐝 𝐒𝐜𝐨𝐩𝐞 𝐨𝐟 𝐚𝐧 𝐄𝐧𝐭𝐫𝐞𝐩𝐫𝐞𝐧𝐞𝐮𝐫:
-Define entrepreneurship, distinguishing it from general business activities by emphasizing its focus on innovation, risk-taking, and value creation. Students will describe the characteristics and traits of successful entrepreneurs, including their roles and responsibilities, and discuss the broader economic and social impacts of entrepreneurial activities on both local and global scales.
Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...

Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh
RHEOLOGY Physical pharmaceutics-II notes for B.pharm 4th sem students

Physical pharmaceutics notes for B.pharm students
BIOLOGY NATIONAL EXAMINATION COUNCIL (NECO) 2024 PRACTICAL MANUAL.pptx

Practical manual for National Examination Council, Nigeria.
Contains guides on answering questions on the specimens provided
ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

Denis is a dynamic and results-driven Chief Information Officer (CIO) with a distinguished career spanning information systems analysis and technical project management. With a proven track record of spearheading the design and delivery of cutting-edge Information Management solutions, he has consistently elevated business operations, streamlined reporting functions, and maximized process efficiency.
Certified as an ISO/IEC 27001: Information Security Management Systems (ISMS) Lead Implementer, Data Protection Officer, and Cyber Risks Analyst, Denis brings a heightened focus on data security, privacy, and cyber resilience to every endeavor.
His expertise extends across a diverse spectrum of reporting, database, and web development applications, underpinned by an exceptional grasp of data storage and virtualization technologies. His proficiency in application testing, database administration, and data cleansing ensures seamless execution of complex projects.
What sets Denis apart is his comprehensive understanding of Business and Systems Analysis technologies, honed through involvement in all phases of the Software Development Lifecycle (SDLC). From meticulous requirements gathering to precise analysis, innovative design, rigorous development, thorough testing, and successful implementation, he has consistently delivered exceptional results.
Throughout his career, he has taken on multifaceted roles, from leading technical project management teams to owning solutions that drive operational excellence. His conscientious and proactive approach is unwavering, whether he is working independently or collaboratively within a team. His ability to connect with colleagues on a personal level underscores his commitment to fostering a harmonious and productive workplace environment.
Date: May 29, 2024
Tags: Information Security, ISO/IEC 27001, ISO/IEC 42001, Artificial Intelligence, GDPR
-------------------------------------------------------------------------------
Find out more about ISO training and certification services
Training: ISO/IEC 27001 Information Security Management System - EN | PECB
ISO/IEC 42001 Artificial Intelligence Management System - EN | PECB
General Data Protection Regulation (GDPR) - Training Courses - EN | PECB
Webinars: https://pecb.com/webinars
Article: https://pecb.com/article
-------------------------------------------------------------------------------
For more information about PECB:
Website: https://pecb.com/
LinkedIn: https://www.linkedin.com/company/pecb/
Facebook: https://www.facebook.com/PECBInternational/
Slideshare: http://www.slideshare.net/PECBCERTIFICATION
What is Digital Literacy? A guest blog from Andy McLaughlin, University of Ab...

What is Digital Literacy? A guest blog from Andy McLaughlin, University of Aberdeen
Recently uploaded (20)
spot a liar (Haiqa 146).pptx Technical writhing and presentation skills

spot a liar (Haiqa 146).pptx Technical writhing and presentation skills
Walmart Business+ and Spark Good for Nonprofits.pdf

Walmart Business+ and Spark Good for Nonprofits.pdf
Andreas Schleicher presents PISA 2022 Volume III - Creative Thinking - 18 Jun...

Andreas Schleicher presents PISA 2022 Volume III - Creative Thinking - 18 Jun...
How to Setup Warehouse & Location in Odoo 17 Inventory

How to Setup Warehouse & Location in Odoo 17 Inventory
Mule event processing models | MuleSoft Mysore Meetup #47

Mule event processing models | MuleSoft Mysore Meetup #47
مصحف القراءات العشر أعد أحرف الخلاف سمير بسيوني.pdf

مصحف القراءات العشر أعد أحرف الخلاف سمير بسيوني.pdf
Chapter wise All Notes of First year Basic Civil Engineering.pptx

Chapter wise All Notes of First year Basic Civil Engineering.pptx
Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum

Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum
Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...

Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...
RHEOLOGY Physical pharmaceutics-II notes for B.pharm 4th sem students

RHEOLOGY Physical pharmaceutics-II notes for B.pharm 4th sem students
BIOLOGY NATIONAL EXAMINATION COUNCIL (NECO) 2024 PRACTICAL MANUAL.pptx

BIOLOGY NATIONAL EXAMINATION COUNCIL (NECO) 2024 PRACTICAL MANUAL.pptx
ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...
What is Digital Literacy? A guest blog from Andy McLaughlin, University of Ab...

What is Digital Literacy? A guest blog from Andy McLaughlin, University of Ab...
