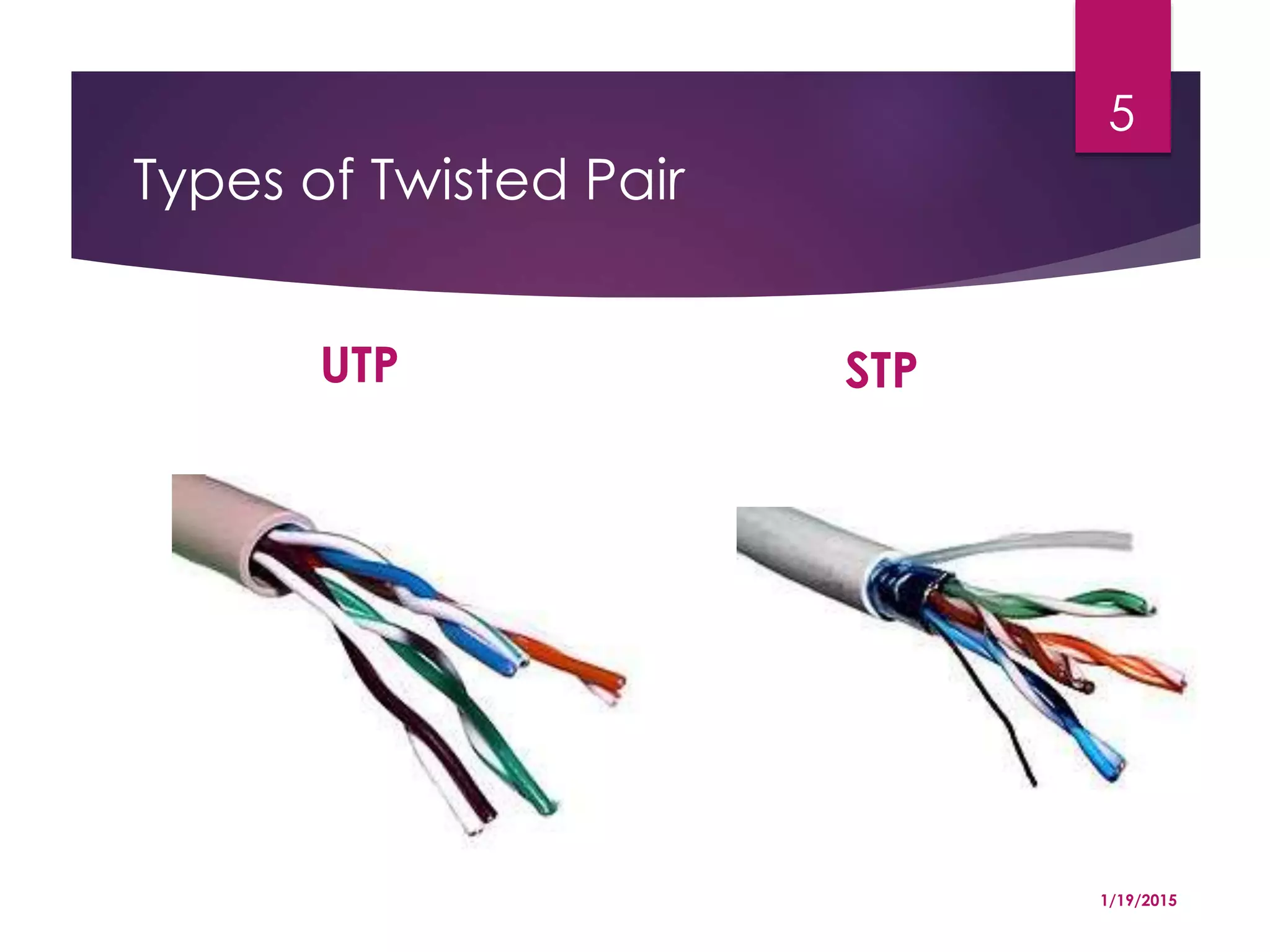
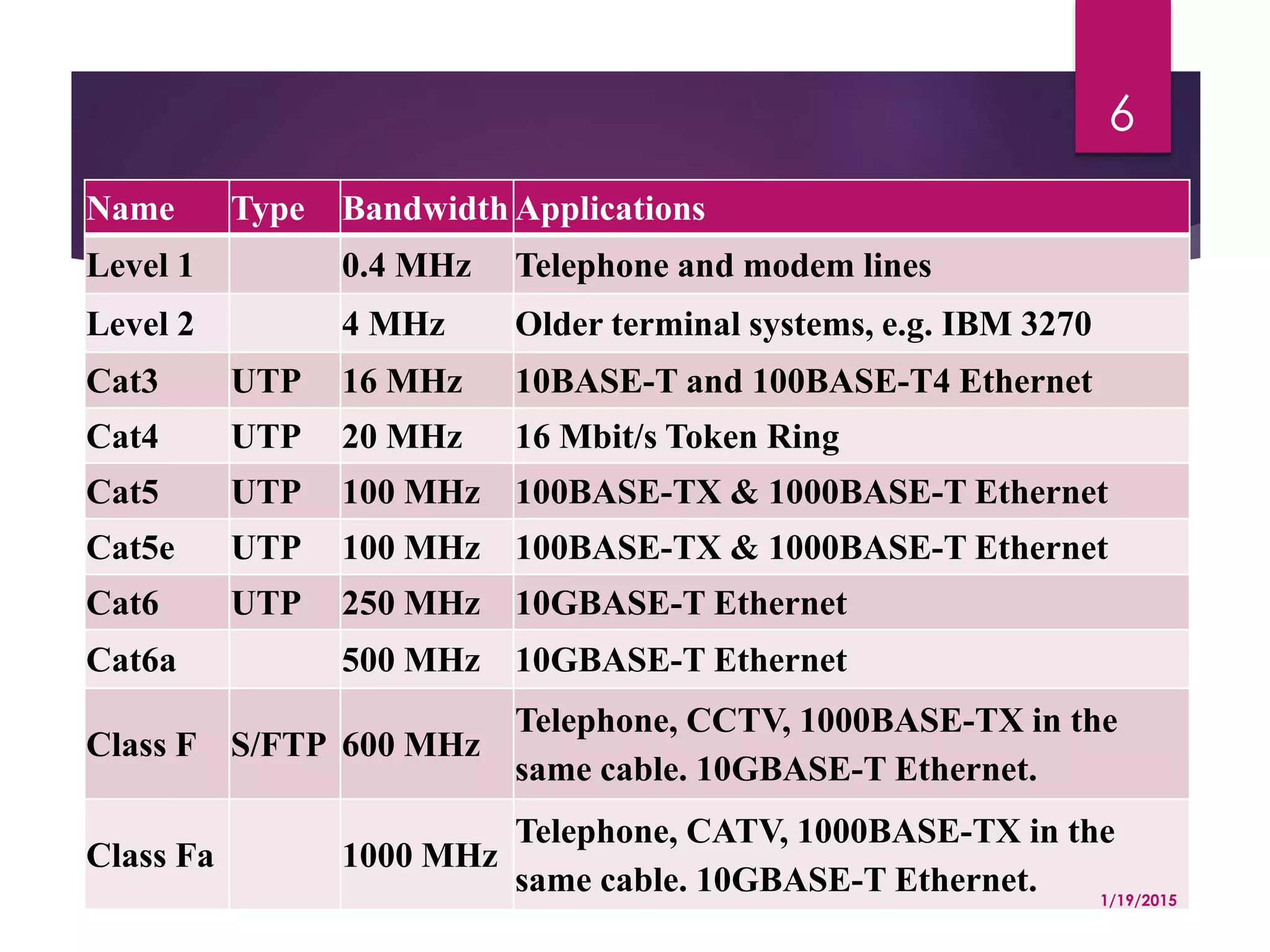
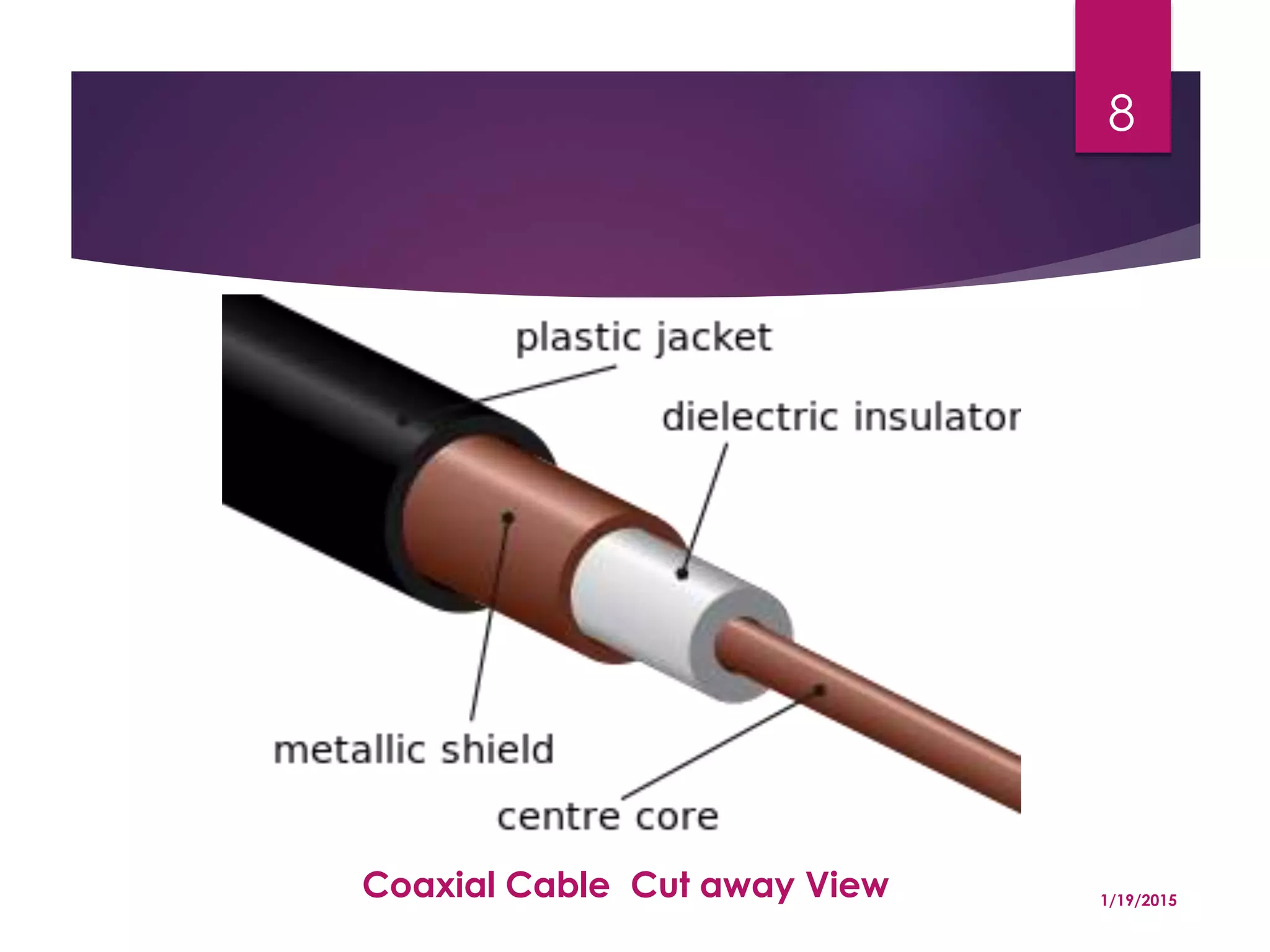
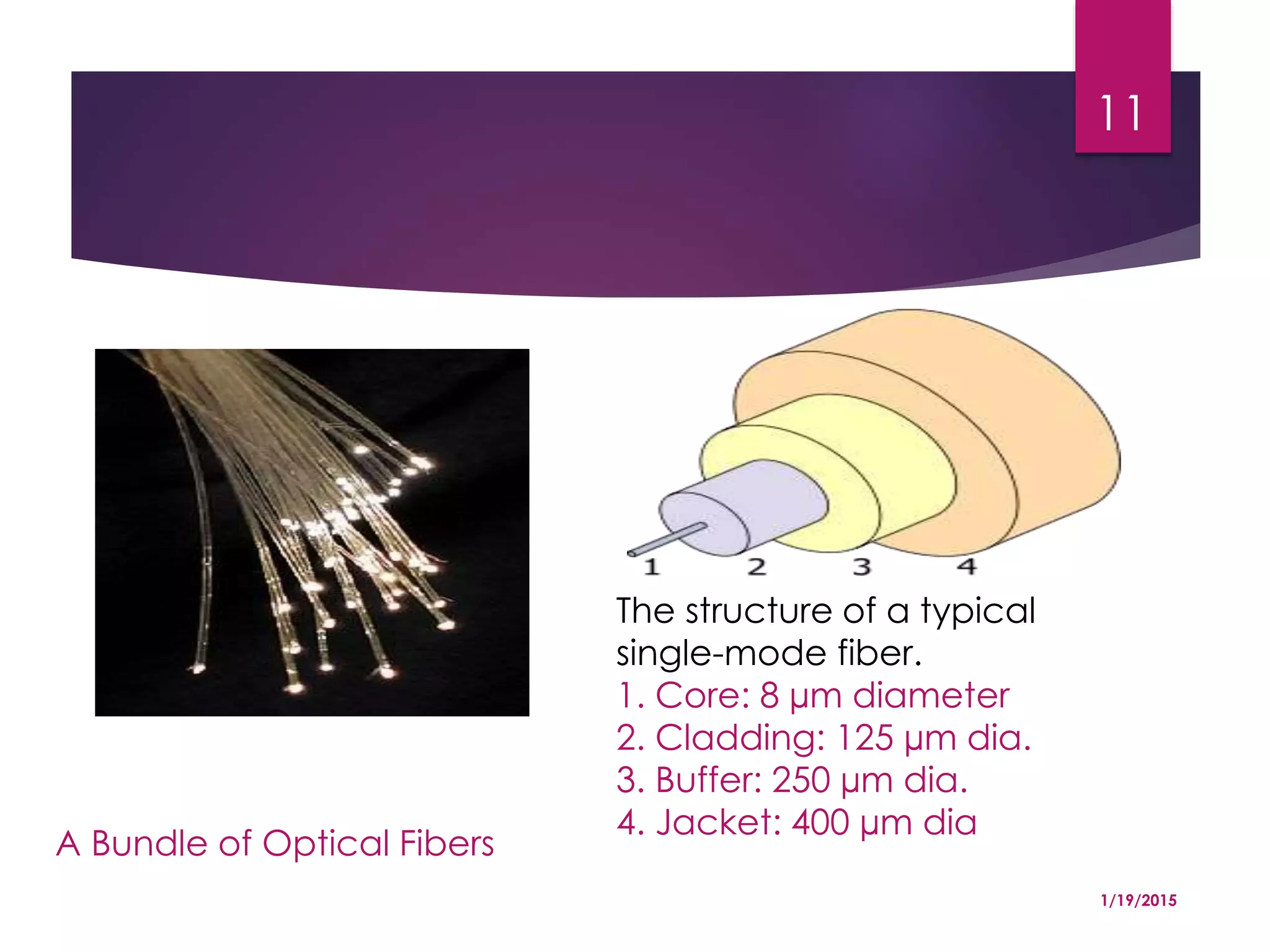
This document discusses different types of media used for data transmission and their characteristics. It describes guided media such as twisted pair cables, coaxial cables, and fiber optics, as well as unguided media like VSAT and satellites. It then explains several transmission characteristics including attenuation, noise, signal-to-noise ratio, and propagation delay.