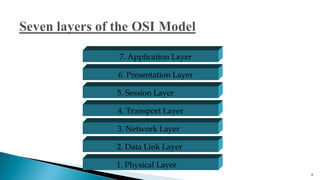
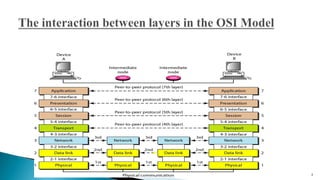
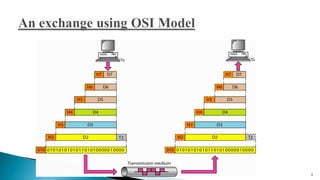
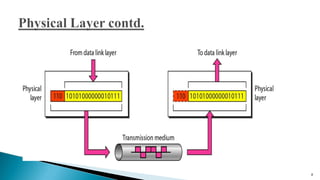
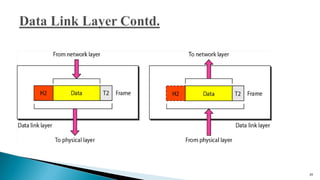
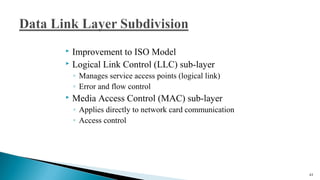
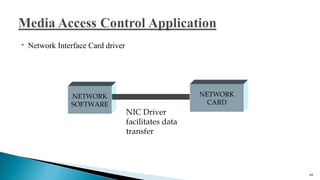
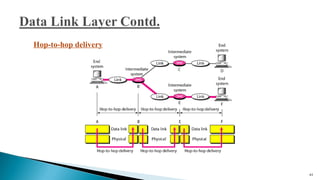
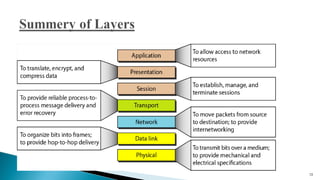
The document discusses the seven layers of the Open Systems Interconnection (OSI) model, with a focus on the physical and data link layers. It describes the key responsibilities of the physical layer, including representing bits, synchronizing data transmission, defining transmission media and topology. It also outlines the major duties of the data link layer, such as framing data, implementing addressing, and handling errors.