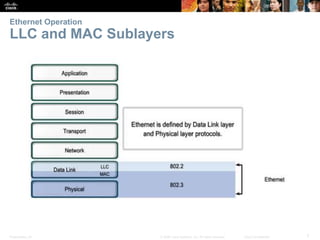
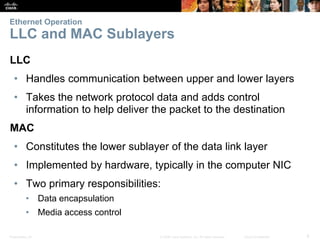
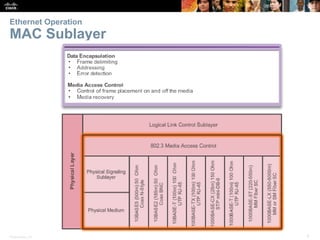
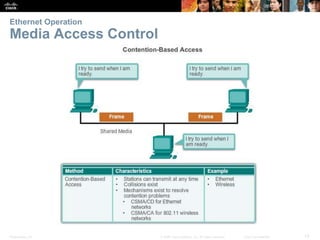
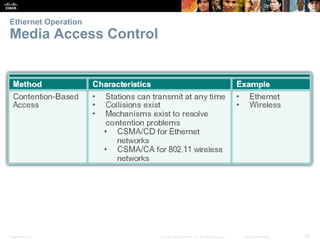
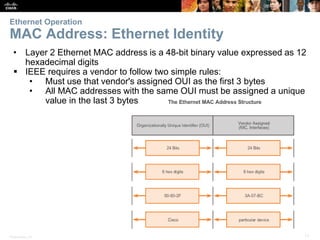
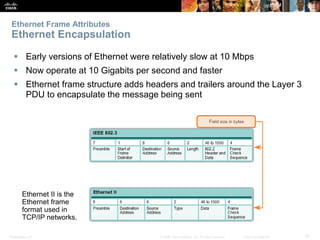
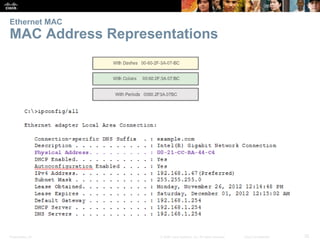
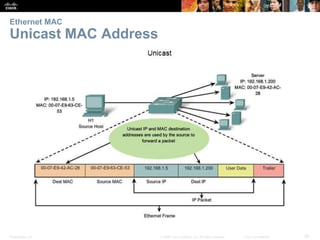
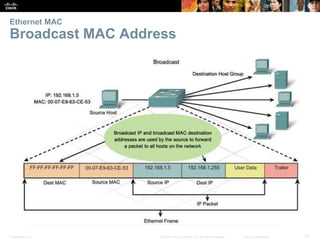
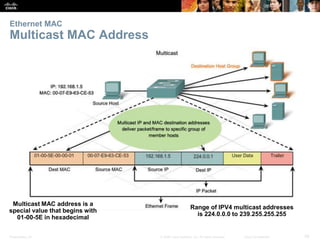
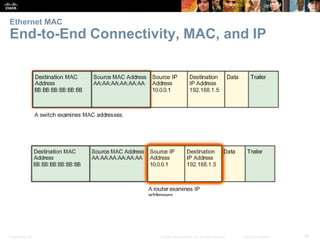
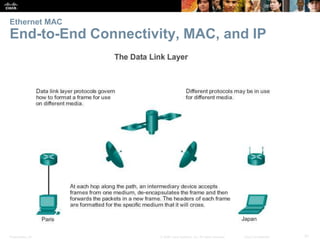
The document discusses Ethernet and its operation. It describes how Ethernet operates at the data link layer using two sublayers: the logical link control (LLC) sublayer and the media access control (MAC) sublayer. The MAC sublayer is responsible for framing data and media access control using carrier sense multiple access with collision detection (CSMA/CD) to prevent collisions on shared media. The MAC sublayer adds the source and destination MAC addresses to frames to allow for delivery to specific devices.