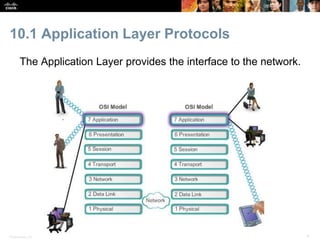
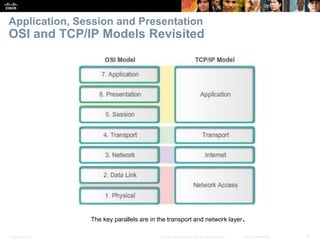
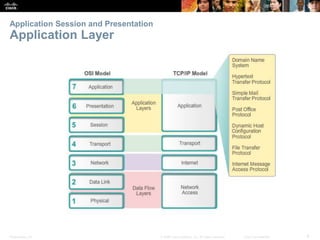
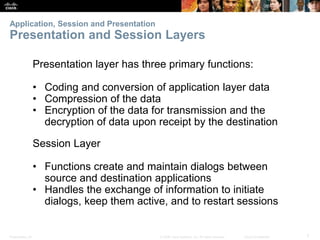
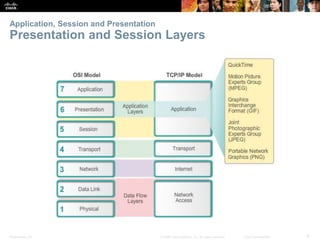
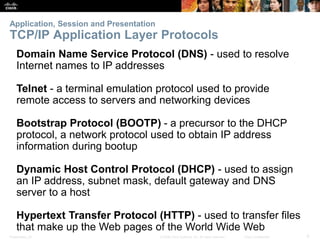
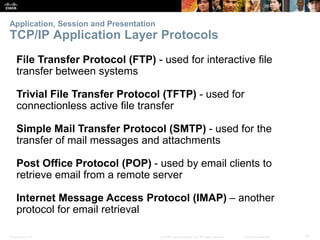
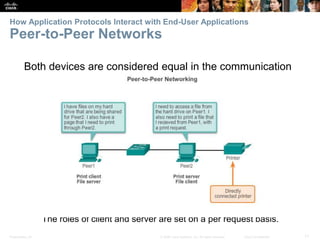
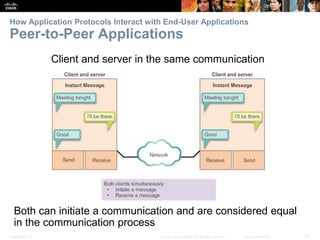
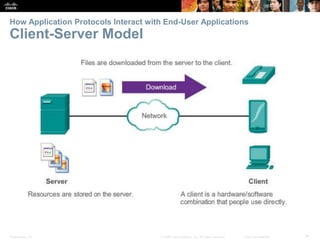
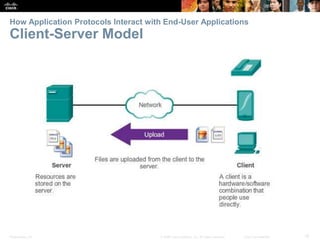
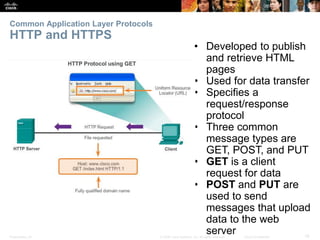
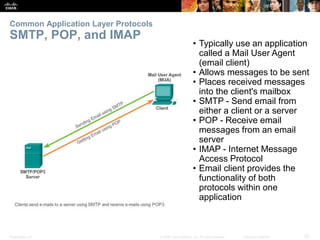
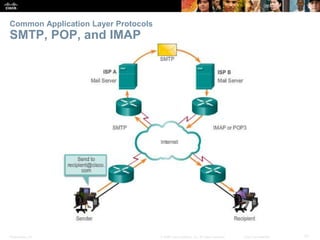
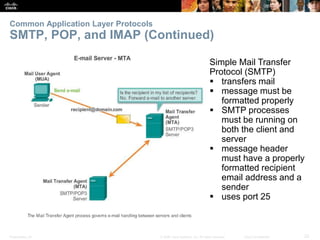
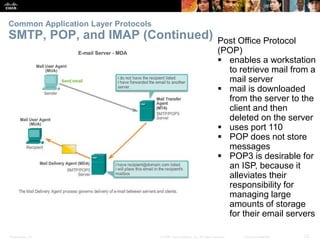
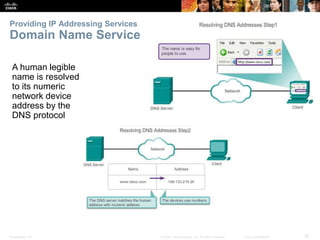
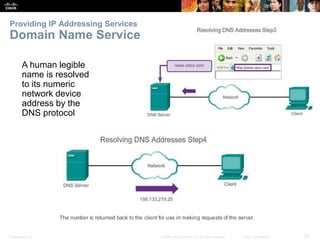
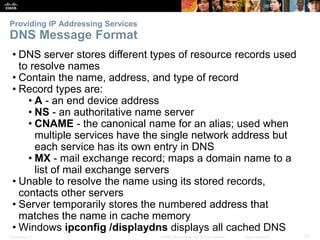
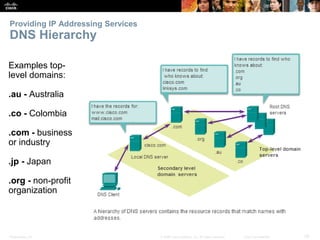
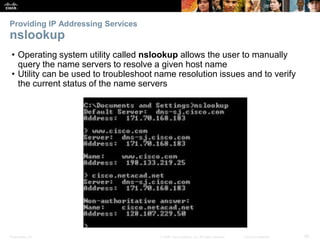
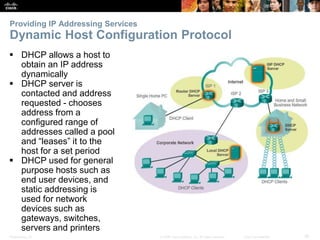
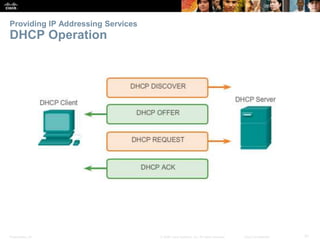
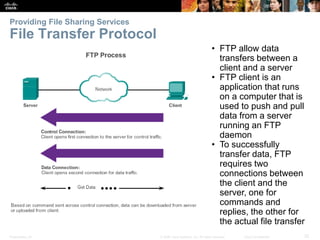
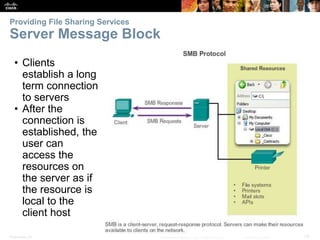
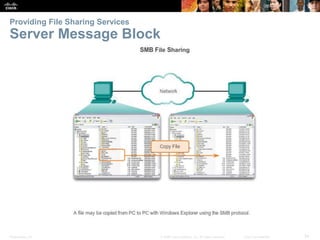
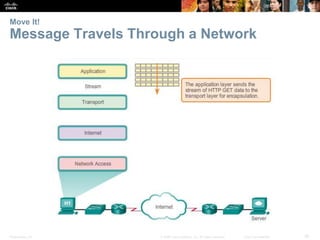
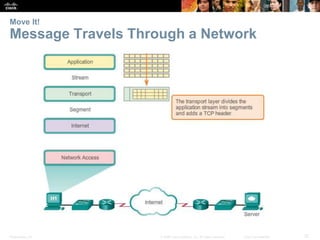
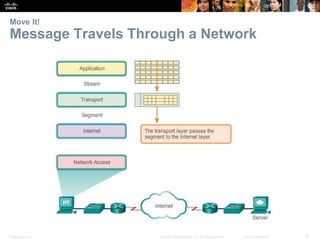
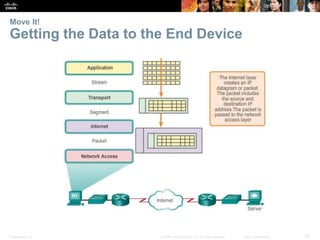
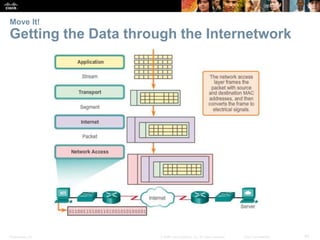
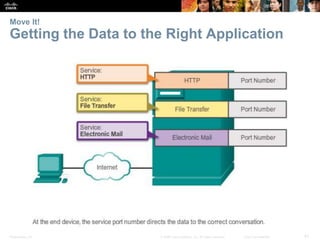
The document discusses application layer protocols and services. It describes how the application, session, and presentation layers work together to provide network services to end user applications. It provides examples of common application layer protocols like HTTP, SMTP, POP, and IMAP and how they enable services like web browsing and email. It also discusses protocols that provide IP addressing services like DNS and DHCP. The document outlines objectives for explaining application layer protocols, how they interact with applications, well-known examples, and how data moves across the network.