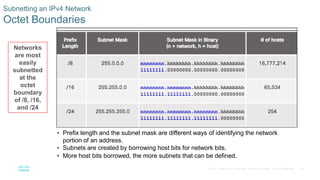
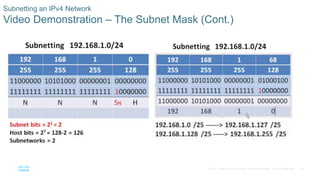
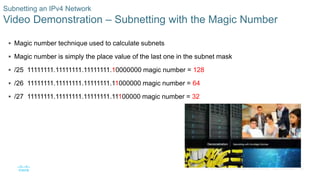
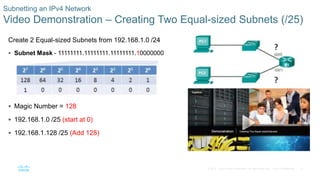
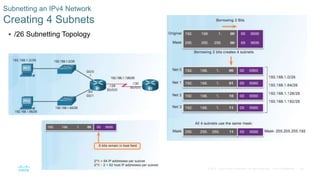
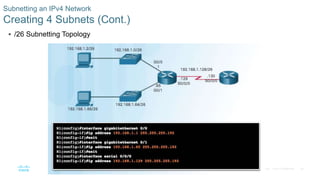
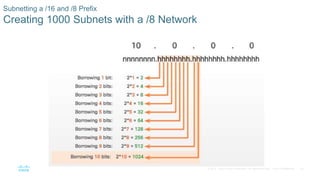
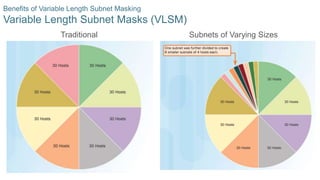
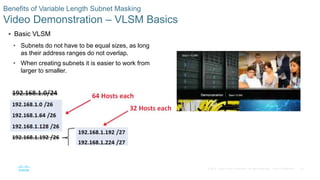
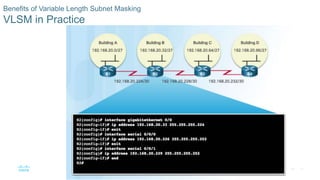
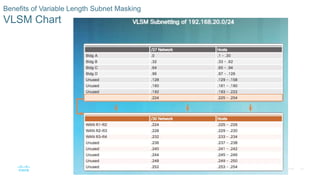
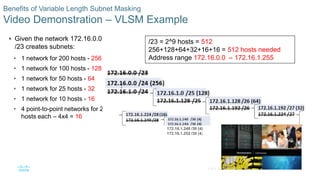
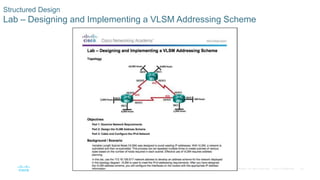
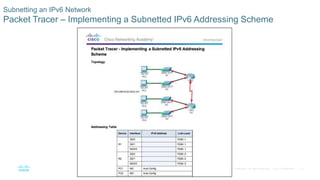
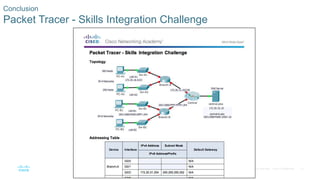
This document provides an overview of subnetting IP networks and addressing schemes. It covers subnetting IPv4 networks, including calculating subnets and hosts for various prefix lengths. It also discusses variable length subnet masking to better utilize address space. Finally, it touches on considerations for structured network design and address planning.