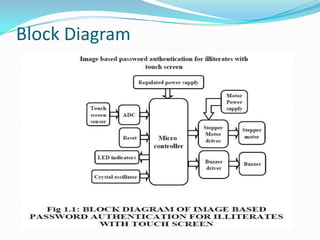
This document outlines a project aimed at developing a security system for illiterates using image-based passwords on touch screens. It includes sections on hardware components, advantages and disadvantages, and procedural steps for implementation. The conclusion emphasizes the security and memorability of image passwords compared to traditional text-based passwords.