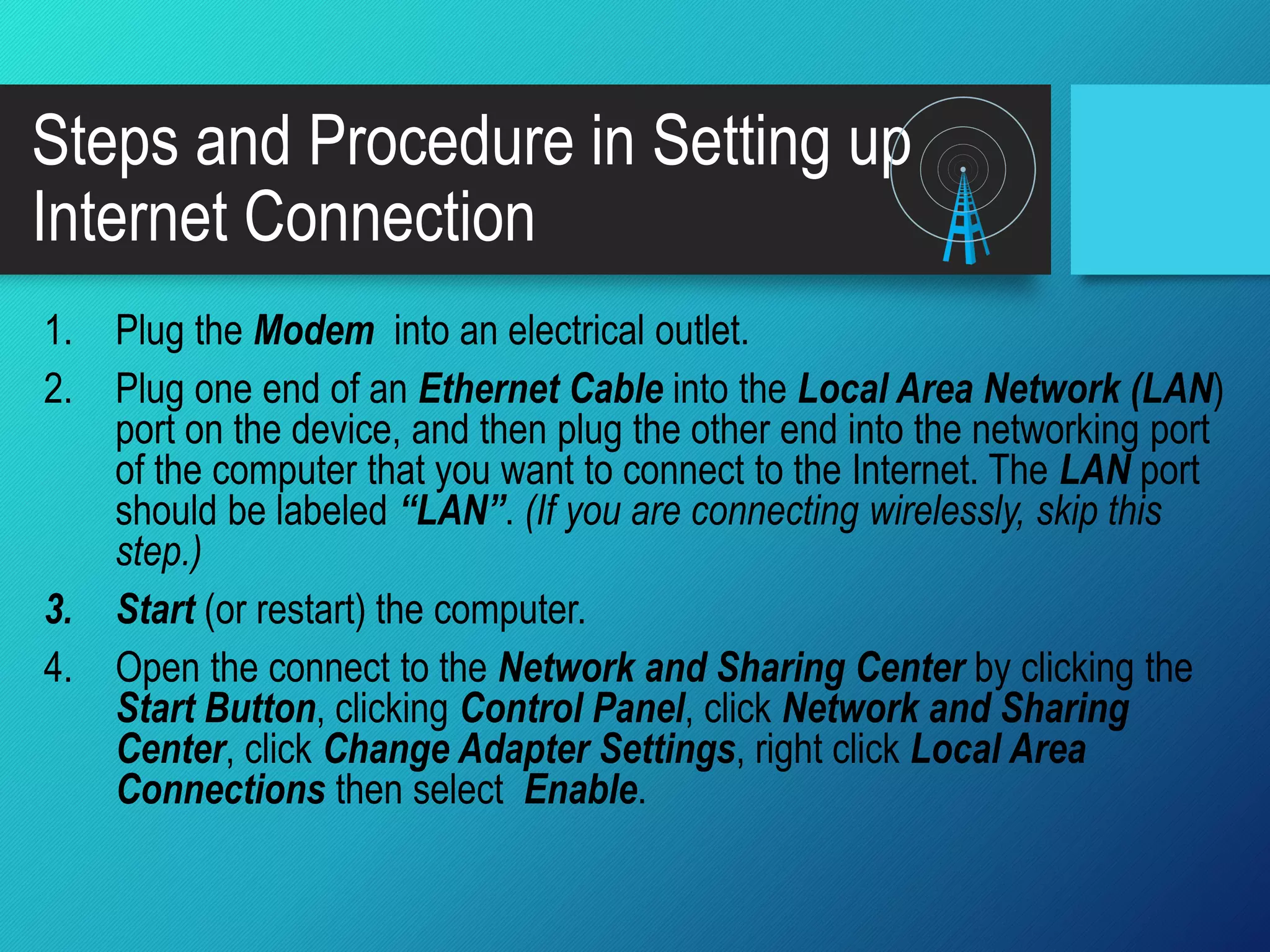
This document provides instructions for setting up an internet connection using either a wired or wireless modem. It discusses the purpose of the lesson, which is to familiarize students with the tools used to set up an internet connection. It also defines what an Internet Service Provider (ISP) is and lists some of the leading ISPs in the country. The document outlines the materials needed and steps to set up a wired or wireless internet connection, including plugging the modem into an outlet, connecting an Ethernet cable between the modem and computer, and enabling the network connection on the computer. It includes tasks for students to design a poster of a networked connected to the internet and to present their output through a PowerPoint presentation.