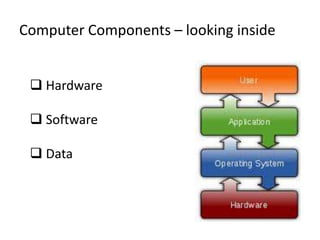
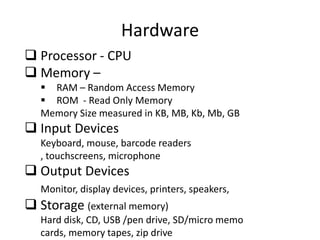
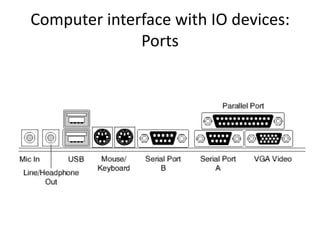
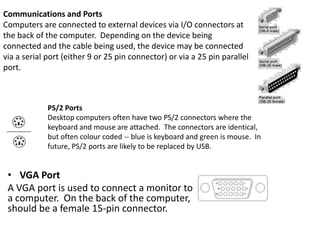
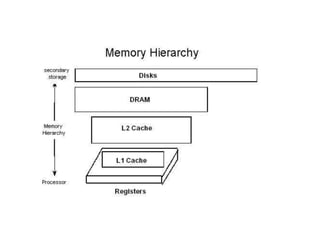
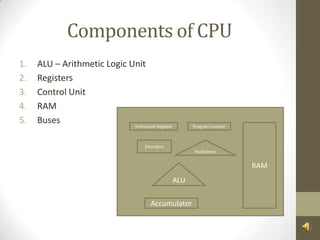
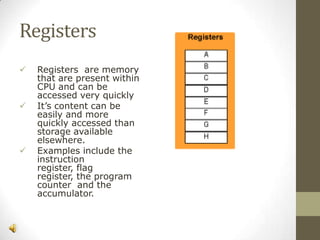
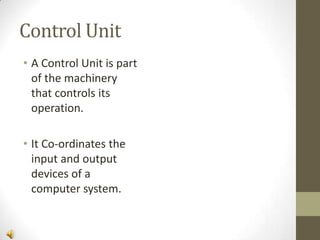
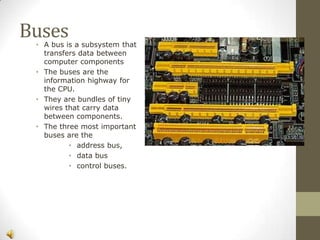
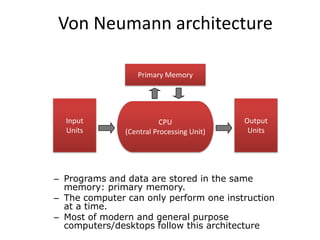
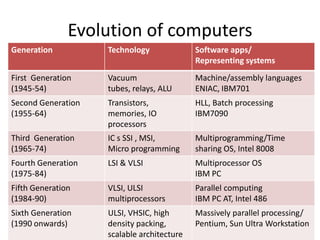
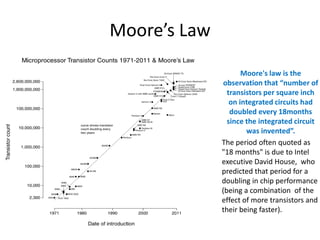
The document discusses the evolution of computer systems from the first generation to the sixth generation. It describes the key technologies that defined each generation as well as representative computer systems. It also covers Moore's Law and defines it as the observation that the number of transistors on integrated circuits doubles every 18 months. The document then provides an overview of computer components including the CPU, memory, storage, input/output ports and devices. It discusses the internal components of the CPU like the ALU, registers, control unit and buses. Finally, it briefly introduces the Von Neumann architecture.

![Super Computer
The Blue Gene/P supercomputer at Argonne National Lab runs over 250,000
processors using normal data center air conditioning, grouped in 72 racks/cabinets
connected by a high-speed optical network[1]](https://image.slidesharecdn.com/computersystemarchitecture-140206030940-phpapp01/85/Computer-system-architecture-10-320.jpg)