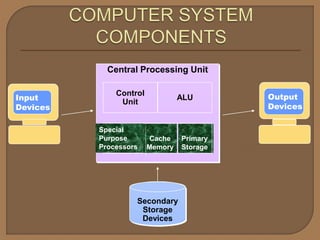
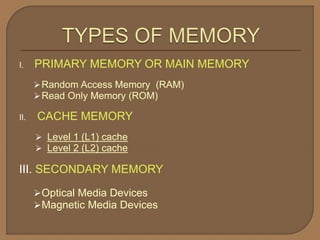
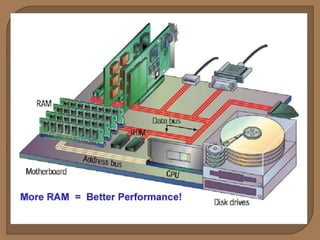
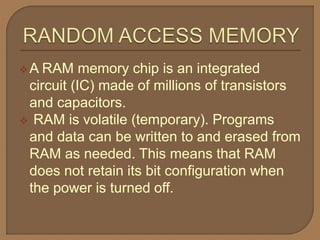
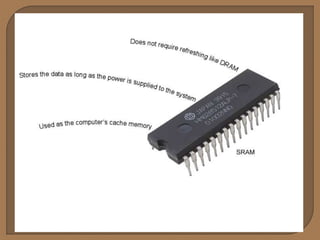
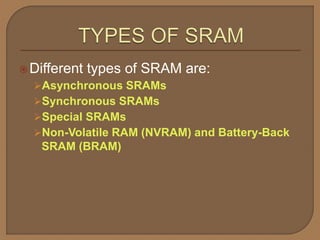
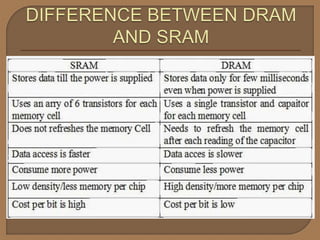
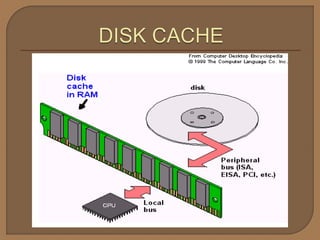
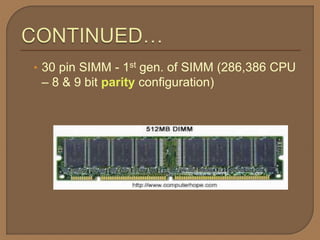
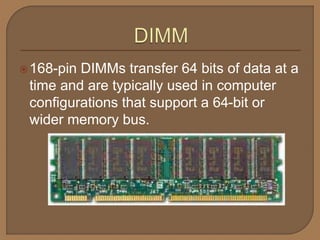
Memory is essential for computers and comes in primary and secondary forms. Primary memory, also called RAM, is volatile and directly used by the CPU. It includes DRAM and SRAM. Secondary memory is non-volatile storage like hard disks, SSDs, USB drives, and optical discs used for long-term storage. Common memory modules that plug into the motherboard include SIMMs, DIMMs, SO-DIMMs, and RIMMs which vary in size and pin count.