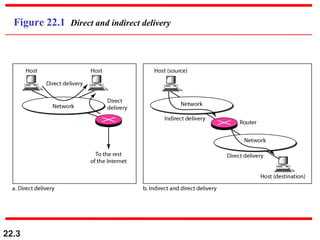
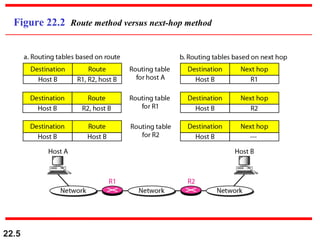
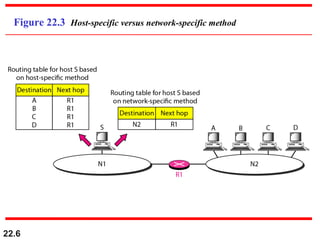
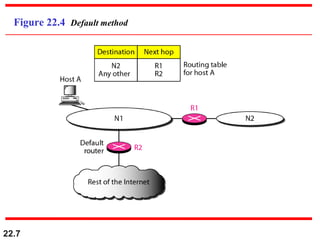
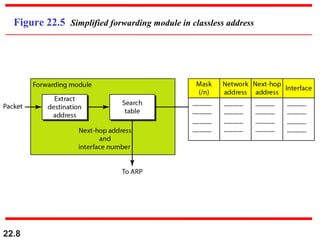
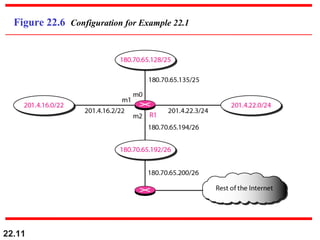
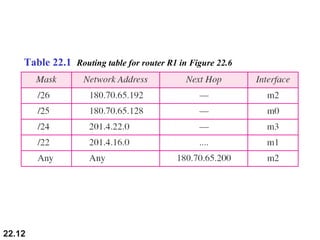
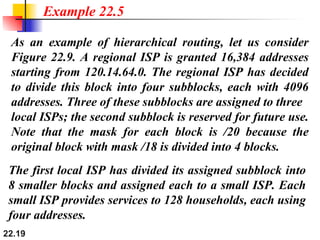
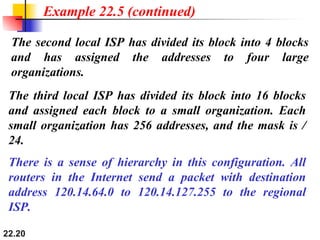
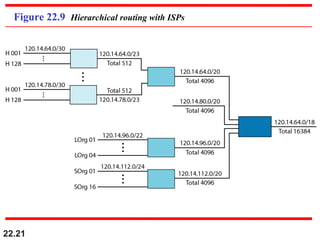
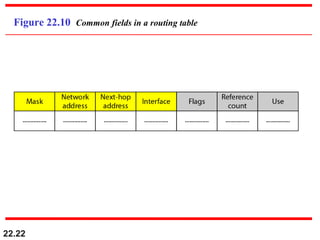
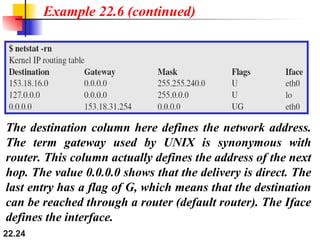
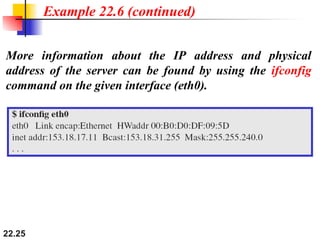
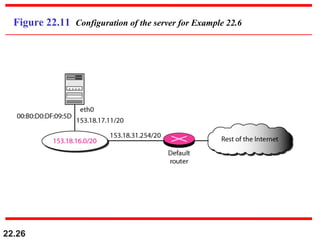
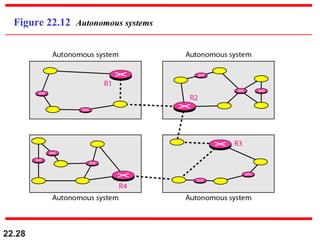
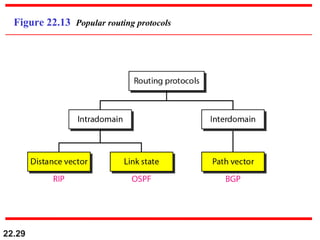
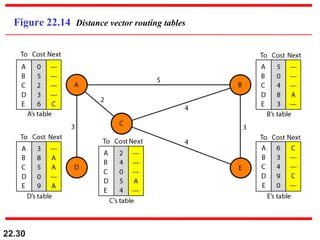
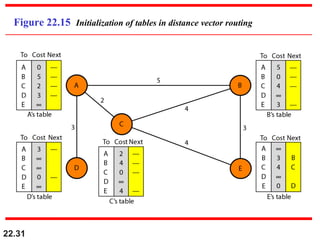
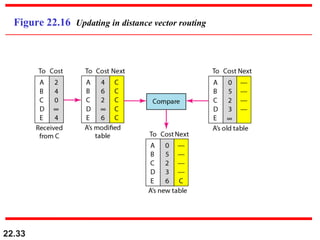
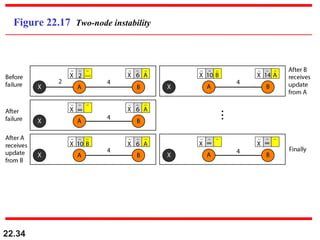
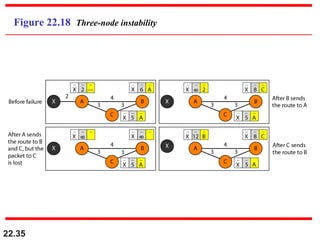
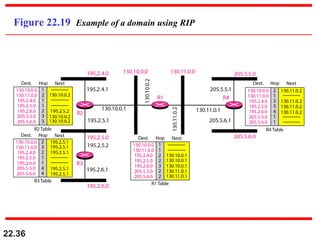
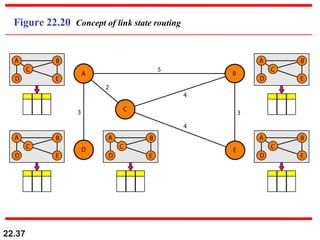
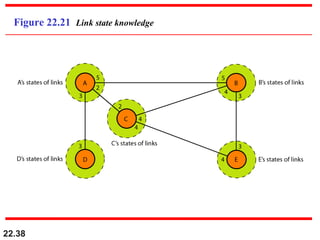
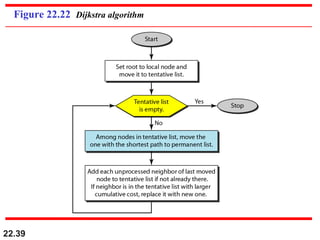
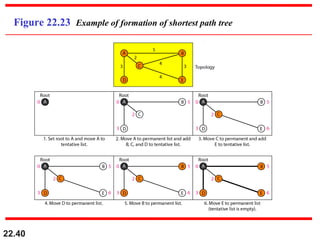
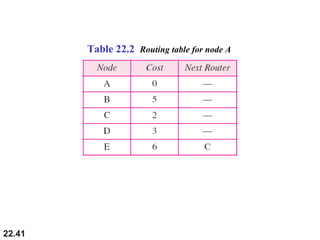
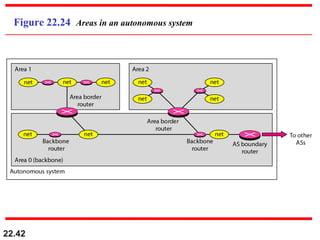
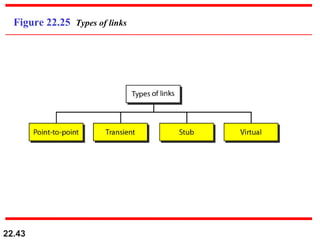
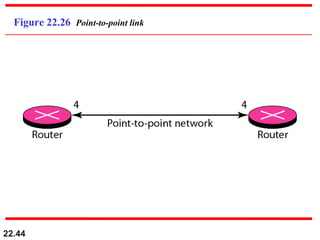
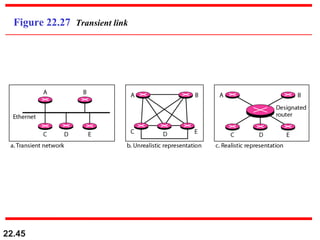
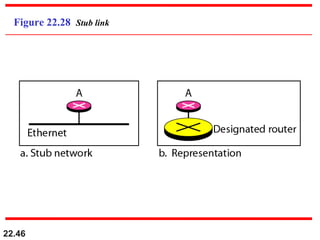
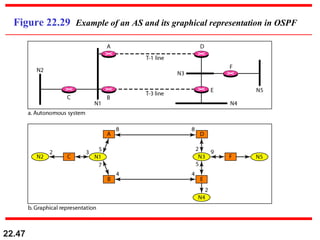
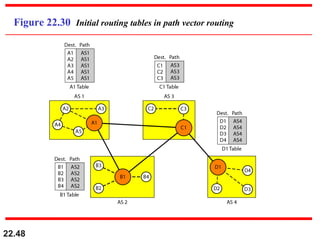
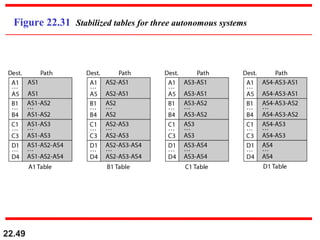
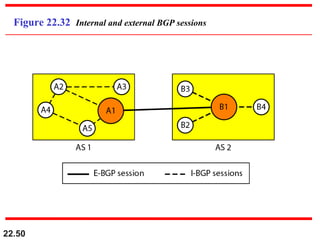
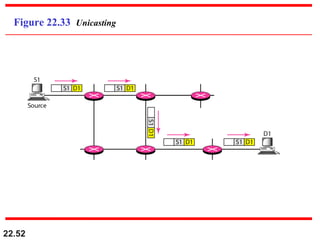
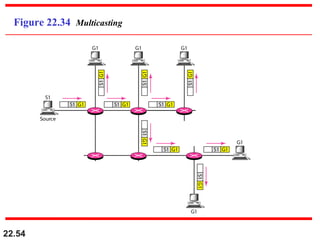
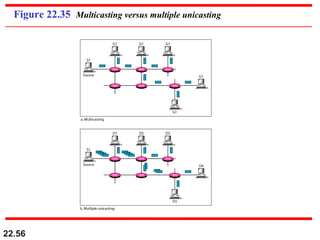
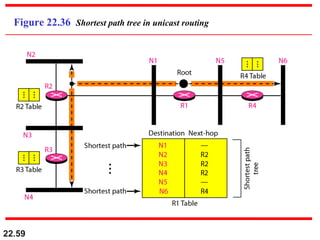
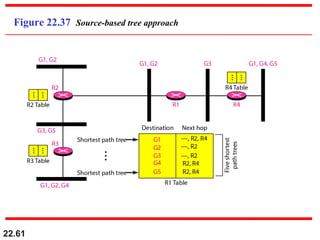
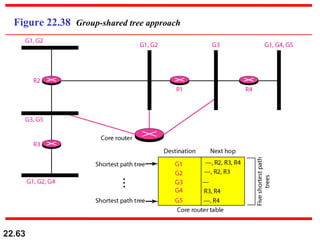
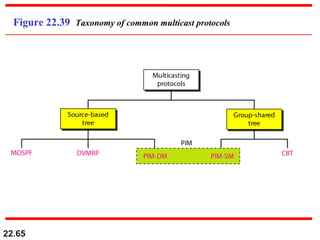
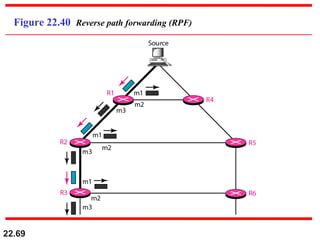
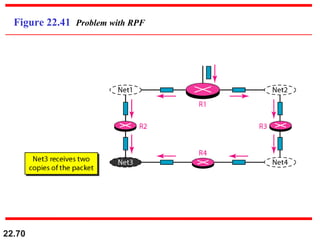
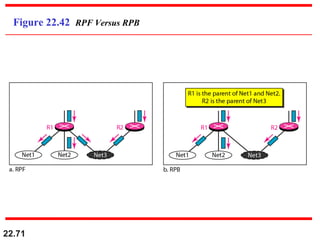
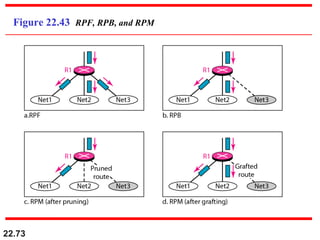
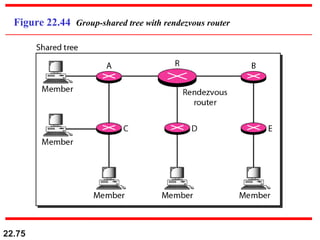
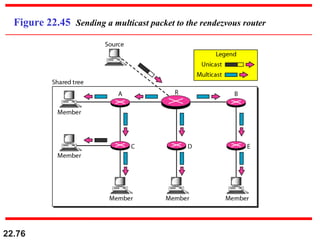
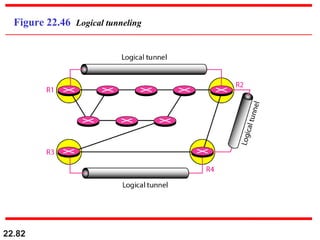
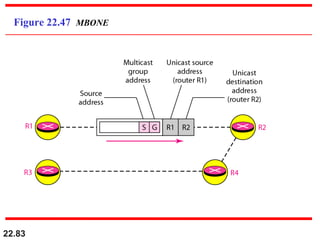
This document provides an overview of network layer concepts including delivery, forwarding, routing, and routing protocols. It discusses direct vs indirect delivery and how forwarding requires routers and hosts to have routing tables to determine the next hop for packet delivery. Distance vector and link state routing protocols are covered as well as intra- and inter-domain routing. Multicast routing is also introduced, covering applications, unicast vs multicast, and common multicast routing protocols. Numerous diagrams and examples are provided to illustrate key networking concepts.