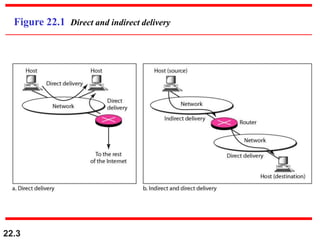
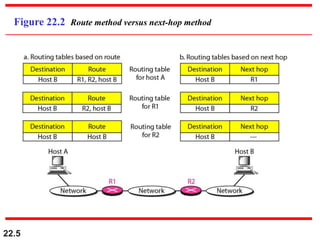
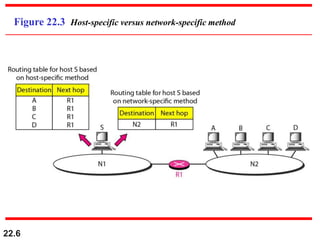
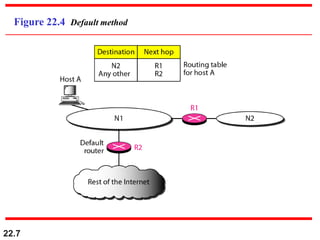
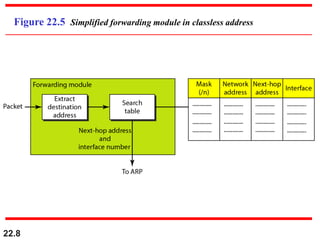
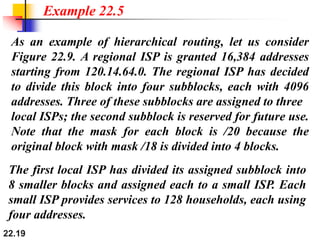
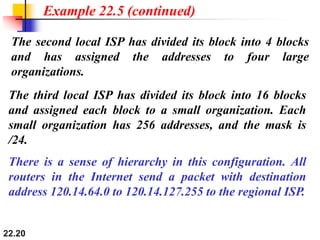
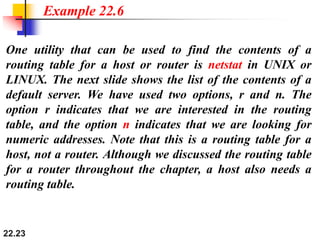
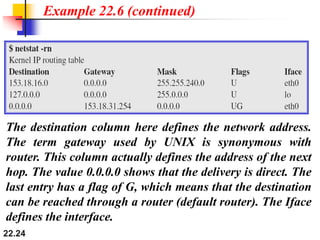
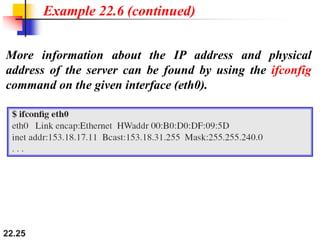
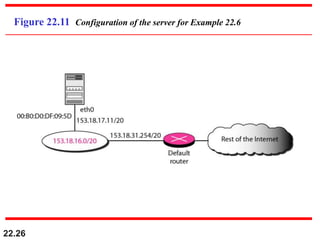
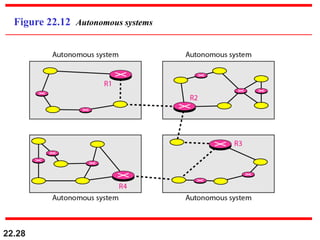
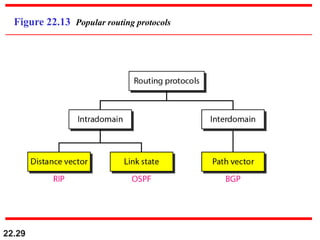
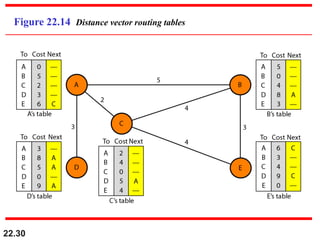
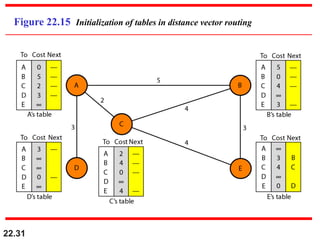
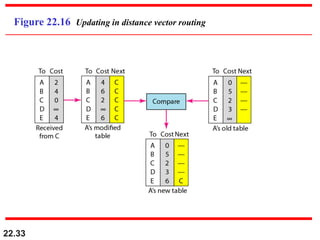
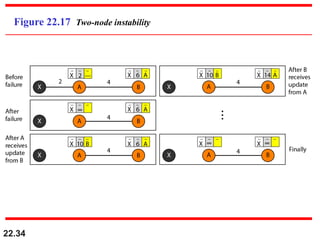
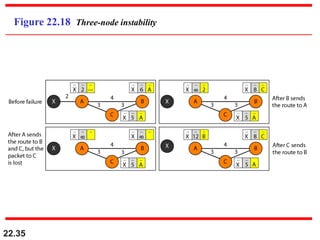
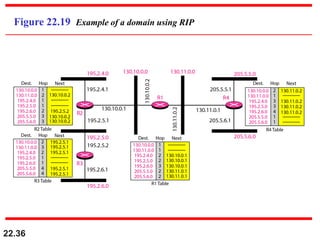
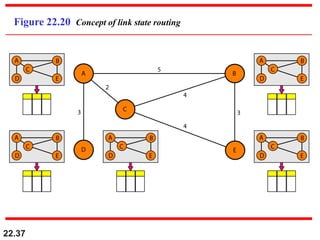
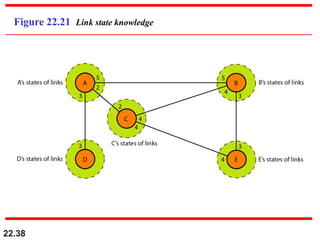
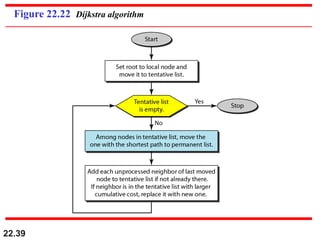
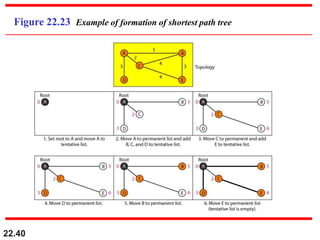
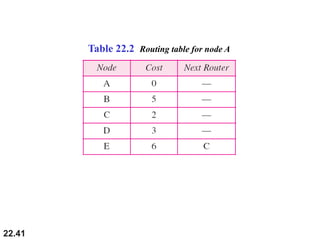
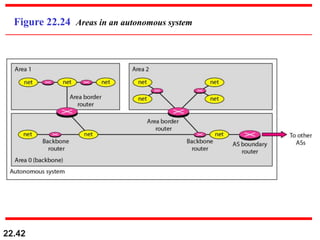
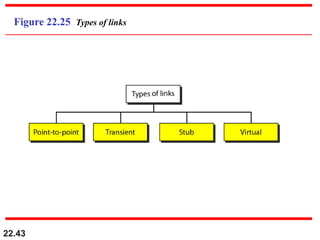
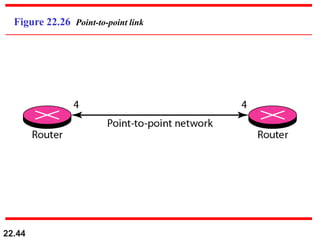
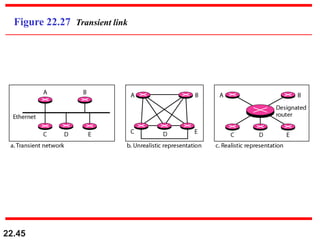
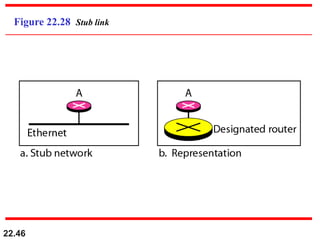
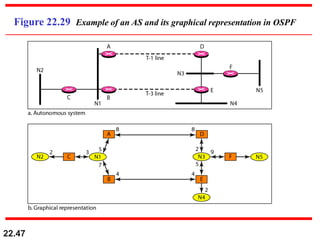
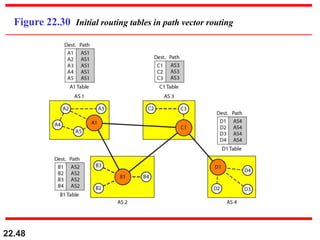
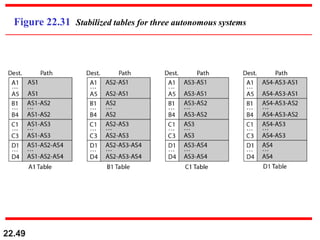
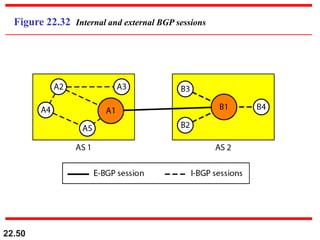
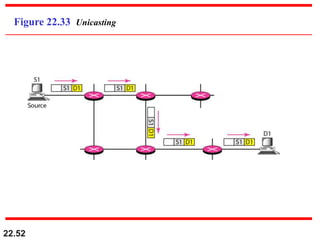
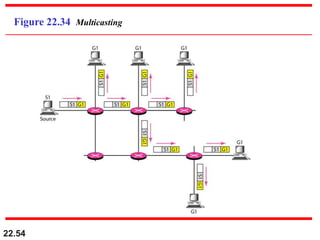
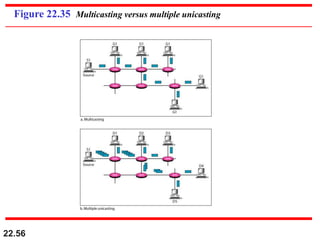
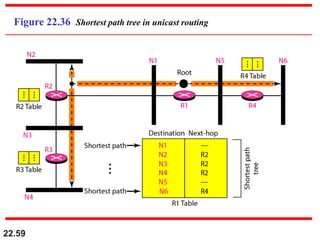
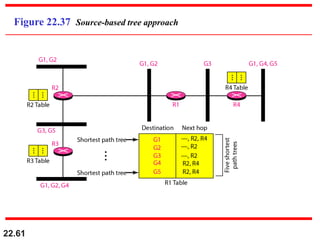
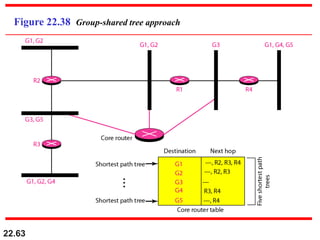
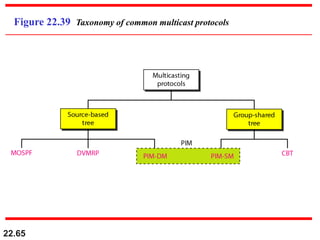
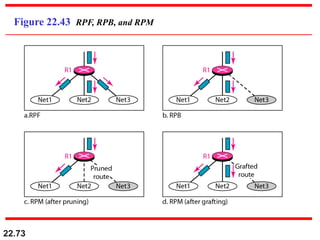
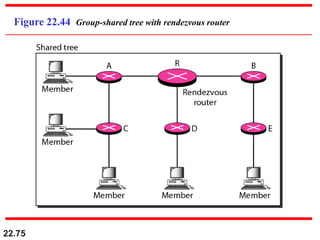
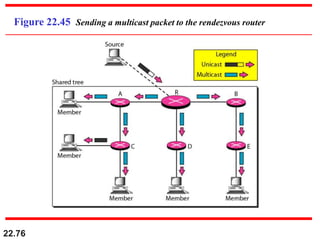
The document summarizes key concepts related to network layer delivery, forwarding, routing, and multicasting. It discusses direct versus indirect delivery and various forwarding techniques like route method versus next-hop method. It also covers unicast routing protocols like distance vector routing (RIP), link state routing (OSPF), and path vector routing (BGP). Finally, it discusses multicasting applications and routing protocols like DVMRP, MOSPF, PIM-SM, and CBT.