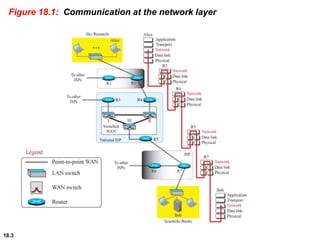
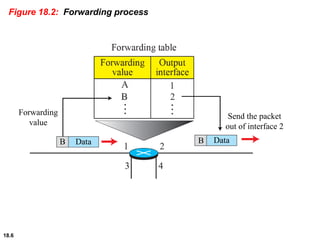
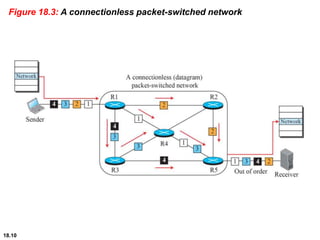
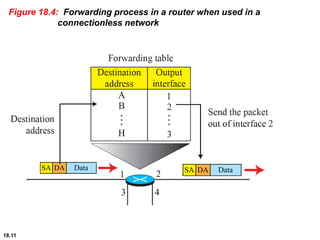
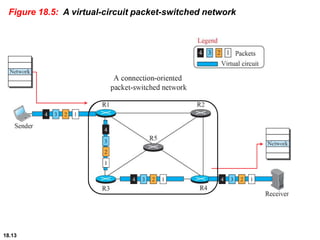
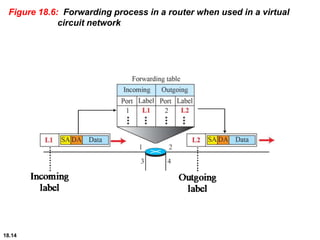
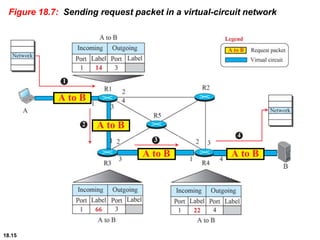
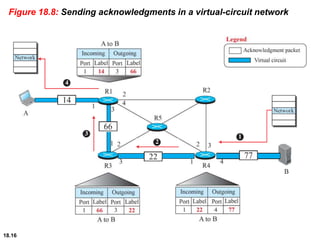
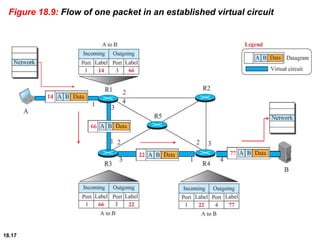
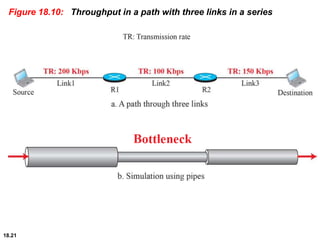
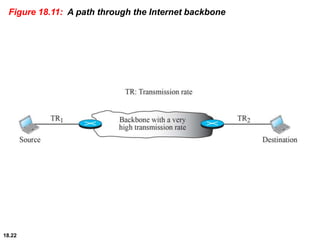
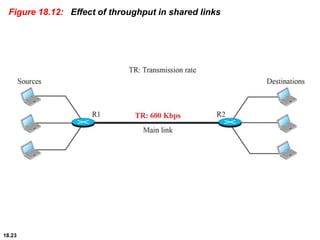
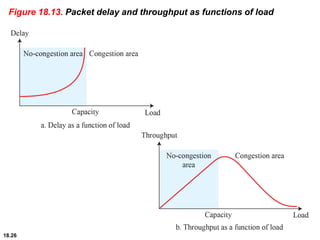
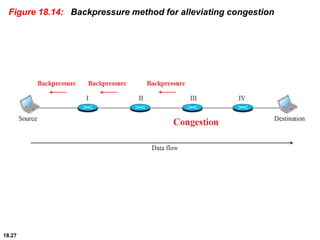
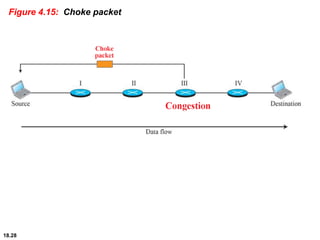
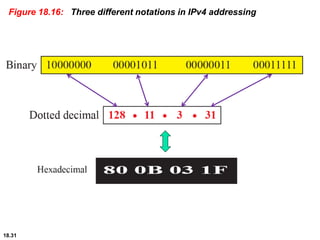
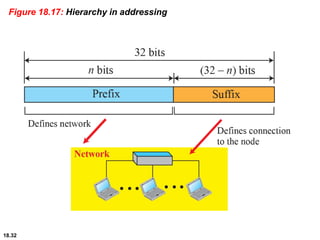
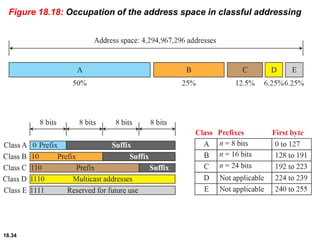
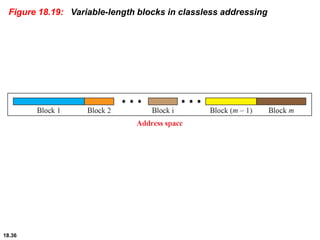
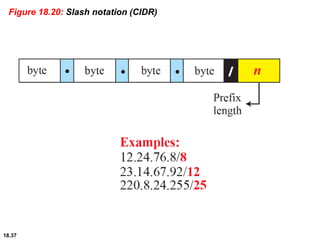
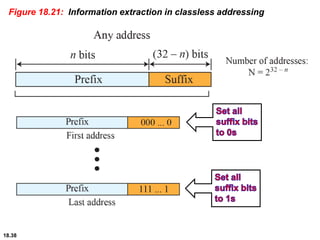
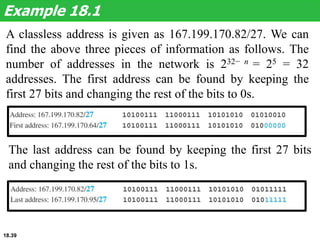
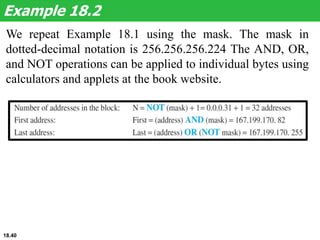
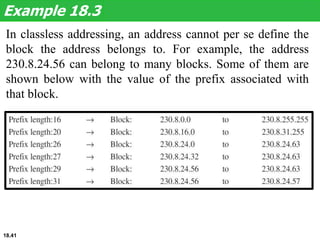
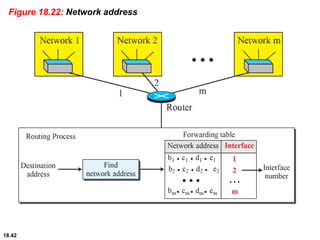
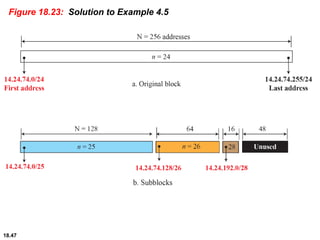
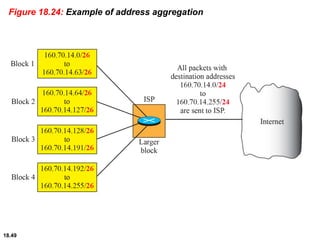
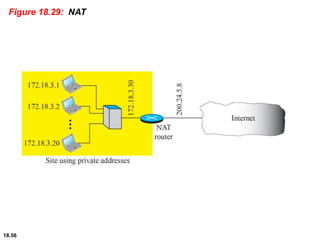
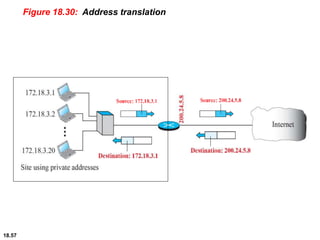
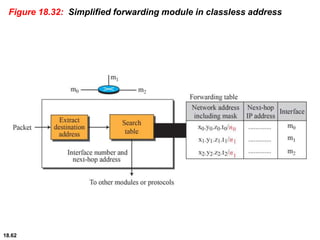
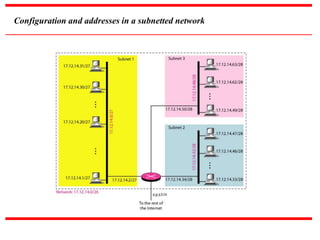
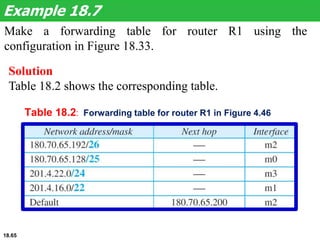
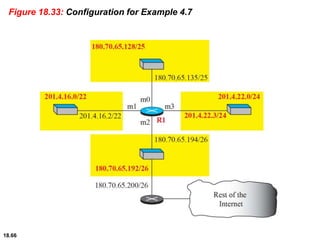
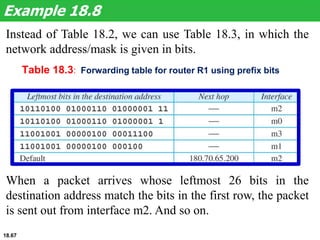
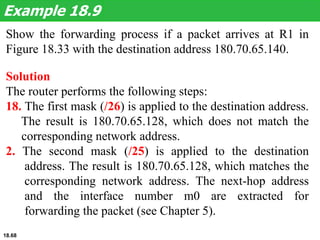
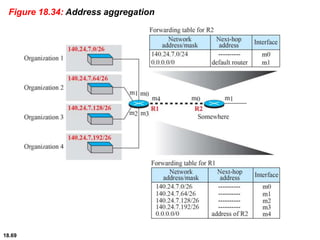
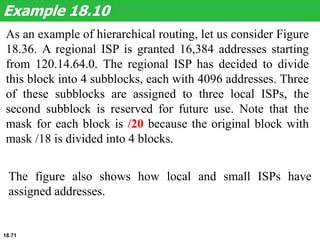
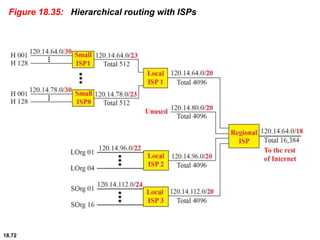
This document provides an overview of key concepts in network layer protocols and IP addressing. It discusses the services expected from the network layer, including packetizing, routing, forwarding and other functions. It describes two approaches to packet switching - connectionless (datagram) and connection-oriented (virtual circuit). It also covers network layer performance metrics like delay, throughput and packet loss. The document then focuses on IP addressing standards, including IPv4 address structure, classful vs. classless addressing, CIDR notation, and address space allocation.