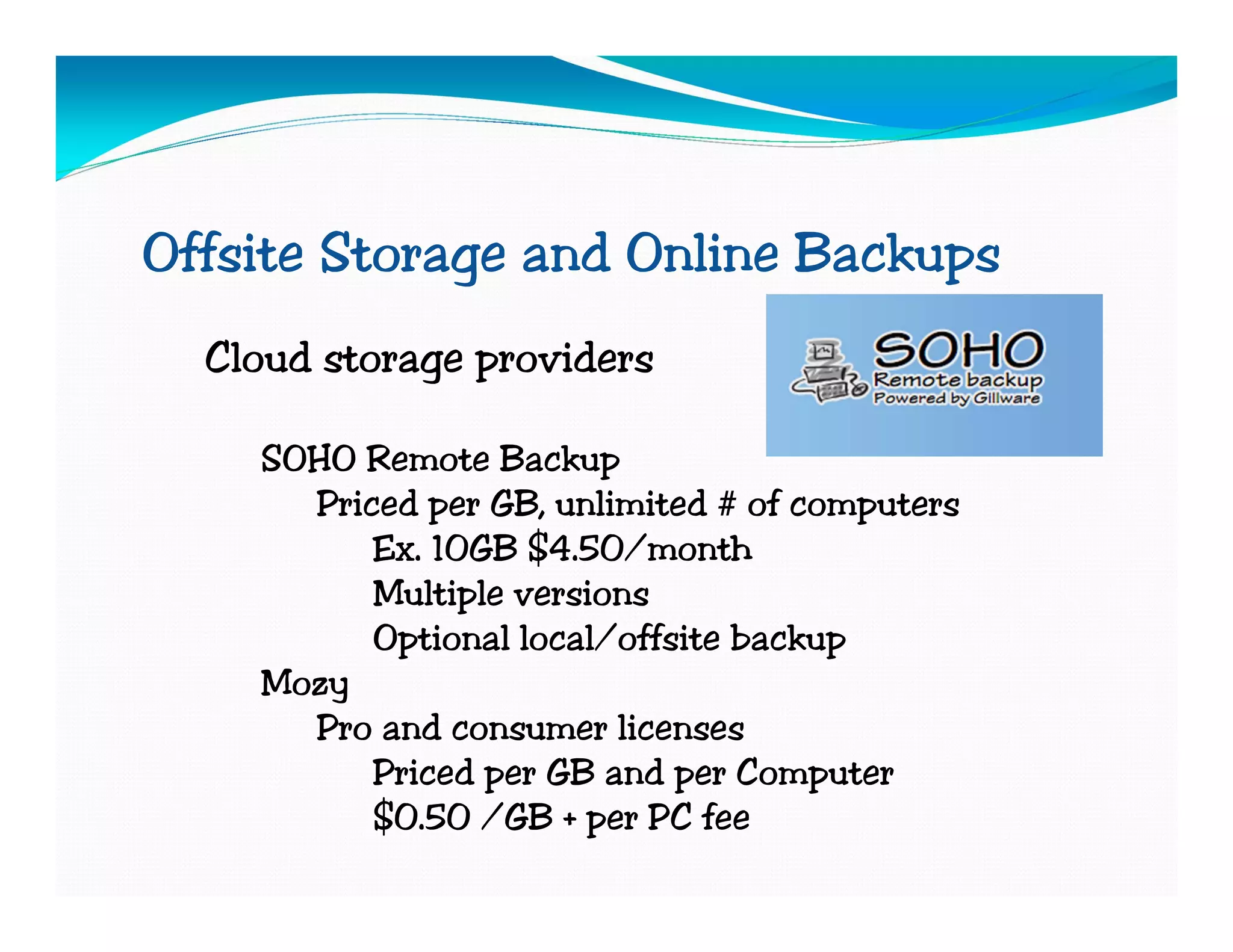
The document provides a comprehensive overview of PC maintenance and security, including disk cleanup, malware scanning, and backup strategies. It discusses the importance of regular updates, physical cleaning, and the use of antivirus software while recommending various tools and methods for effective maintenance and data protection. Additionally, it covers troubleshooting common issues and highlights the benefits of cloud storage for offsite backups.