Embed presentation
Download as PDF, PPTX
















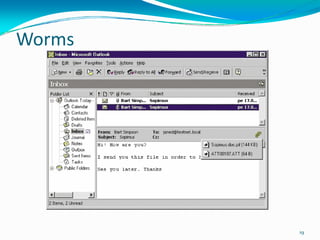

















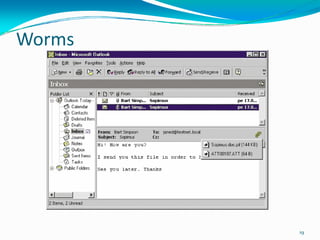
This chapter discusses maintaining a PC, including performing backups, protecting against viruses/malware, and troubleshooting. Topics covered include organizing the hard drive, creating backup plans and disks, using antivirus software, building a toolkit, and fundamental troubleshooting approaches like making backups before making changes and systematically isolating problems.