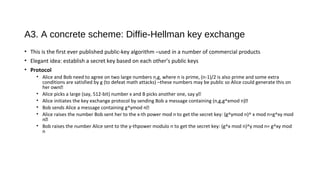
Authentication protocols allow communicating parties to verify each other's identities before exchanging confidential information. Digital signatures provide a way for senders to cryptographically sign messages in a way that cannot be forged or denied later. There are two main approaches: arbitrated signatures use a trusted third party to verify and time-stamp signatures, while direct signatures encrypt a hash of the message with the sender's private key for verification by the recipient. Key techniques like Diffie-Hellman key exchange, Kerberos, and public key infrastructures help enable secure authentication and signatures at scale.