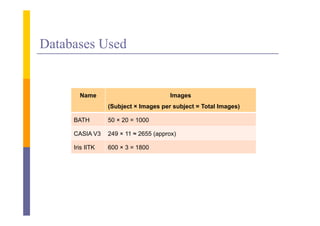
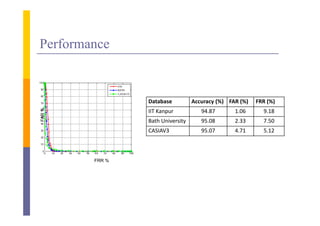
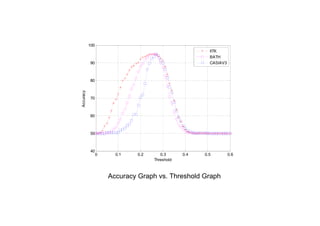
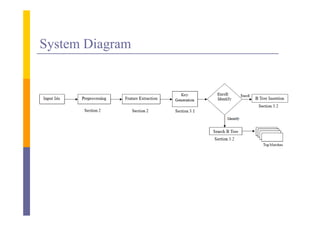
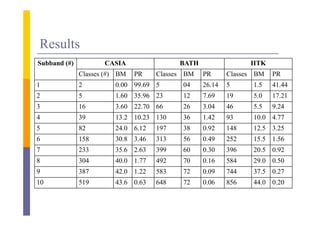
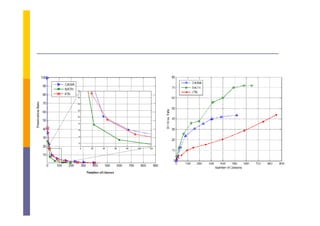
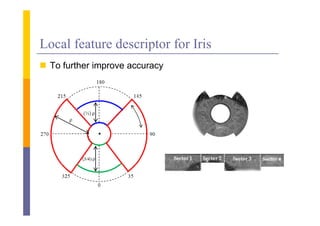
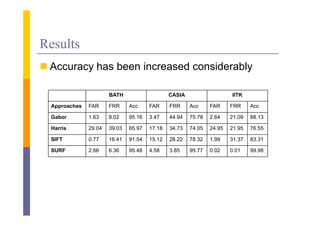
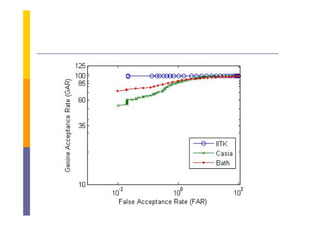
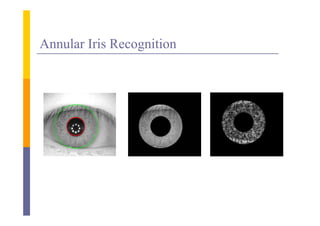
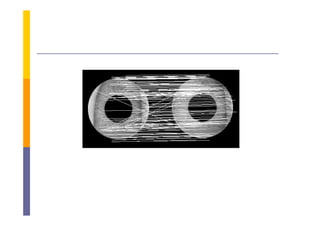
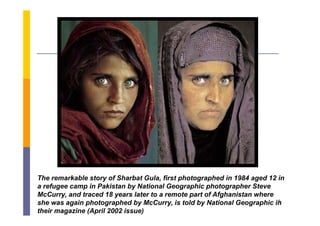
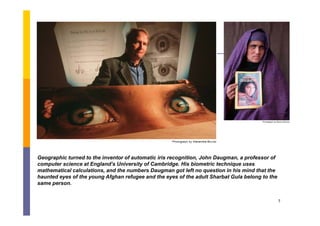
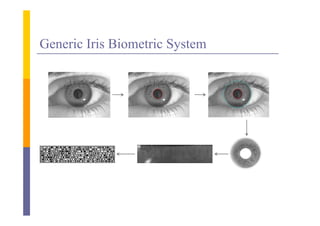
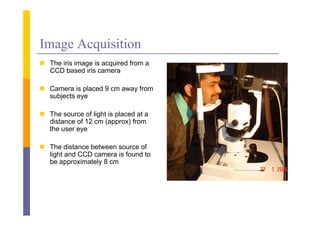
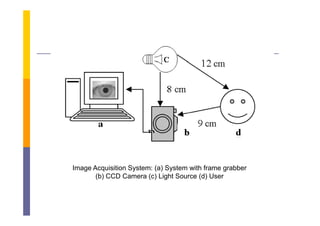
The document discusses iris biometrics and an iris recognition system. It provides details on iris anatomy, image acquisition, preprocessing, iris localization including pupil and iris detection, iris normalization, feature extraction using Haar wavelets, and matching. It evaluates the system on three databases achieving over 94% accuracy with low false acceptance and rejection rates. Further work is proposed on fusion, dual extraction approaches, indexing large databases, and using local descriptors.

![ F every edge pixel ( ) fi d the candidate center point using
For d i l (p) find h did i i
xt x p r cos( )
yt y p r sin( )
where xp and yp is the location of edge point p
r є [rmin rmax]
xt and yt is the determined circle center](https://image.slidesharecdn.com/irisrecognition-130128005204-phpapp02/85/Iris-Recognition-26-320.jpg)
![ F range of radius
For f di
The center point is computed
The Accumulator array is incremented by one for calculated center p
y y point
Accum[xt,yt,r]=Accum[xt,yt,r]+1
The point with maximum value in the accumulator is denoted as
circle center with radius r](https://image.slidesharecdn.com/irisrecognition-130128005204-phpapp02/85/Iris-Recognition-27-320.jpg)
![I ( x( , ), y ( , )) I ( , )
with
x p ( , ) x 0 ( ) rp * cos( )
y p ( , ) y 0 ( ) rp * sin( )
i (
xi ( , ) xi 0 ( ) ri * cos( )
yi ( , ) xi 0 ( ) ri * sin( )
where rp and ri are respectively the radius of pupil and the iris
while (xp(θ), yp(θ)) and (xi(θ), yi(θ)) are the coordinates of the
pupillary and li bi b
ill d limbic boundaries i th di ti θ Th value of θ
d i in the direction θ. The l f
belongs to [0;2], ρ belongs to [0;1]](https://image.slidesharecdn.com/irisrecognition-130128005204-phpapp02/85/Iris-Recognition-31-320.jpg)


![Feature Template
A l
At level 4 coefficient matrices are combined i
l ffi i i bi d into single f
i l feature
matrix or feature template FV= [CD4 CV4 CH4].
1 FV (i ) 0
Iris (i )
0 FV (i ) 0
where Iris is the binarized iris code](https://image.slidesharecdn.com/irisrecognition-130128005204-phpapp02/85/Iris-Recognition-38-320.jpg)