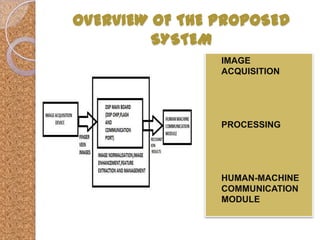
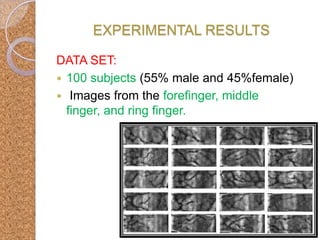
The document presents an embedded real-time finger-vein recognition system for mobile devices. The system uses finger vein patterns as a biometric for authentication through image acquisition of the finger veins, processing the images through segmentation, enhancement and feature extraction, and human-machine communication. It was found to have high security, low power consumption, small size, quick response time of 0.8 seconds, and high accuracy with a low equal error rate of 0.07%.