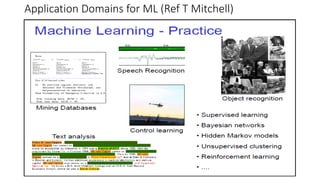
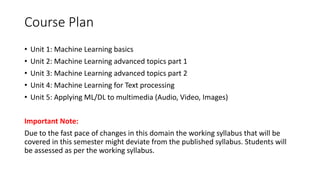
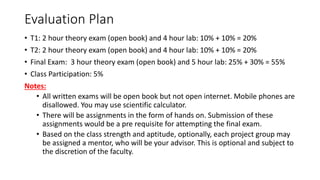
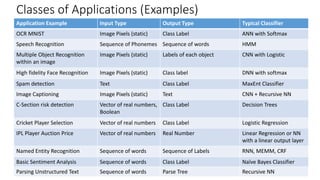
This document is an introduction to machine learning, outlining its applications, techniques, and course structure for a unit titled 'Applied Machine Learning.' It discusses the characteristics of suitable problems for machine learning, examples of its application, and the contemporary techniques that will be covered in the course, such as deep learning and natural language processing. It also includes information on evaluation methods and course requirements.