Embed presentation
Download as PDF, PPTX
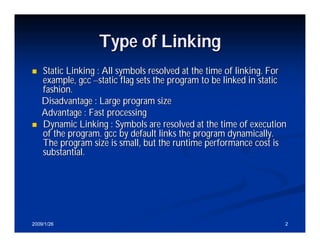

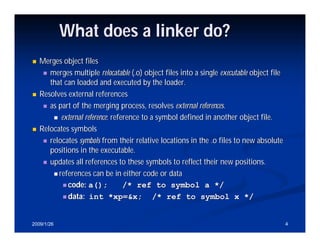
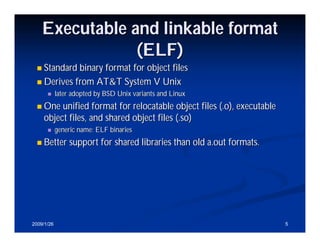
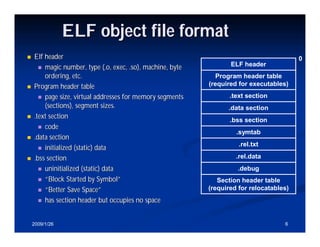
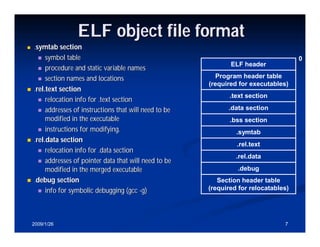
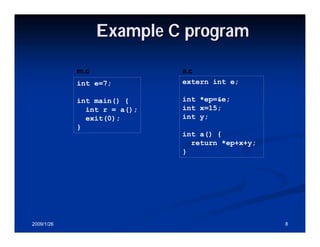
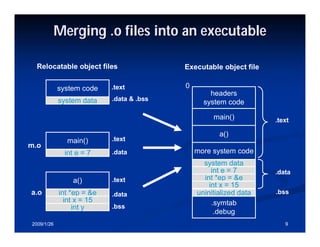
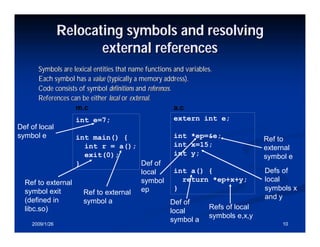
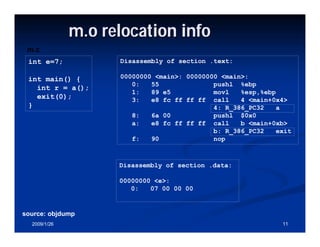
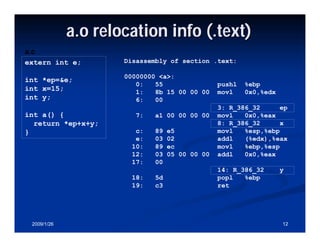
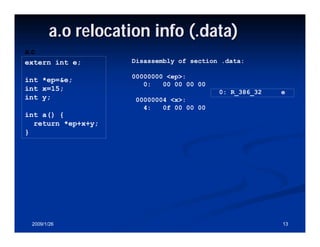
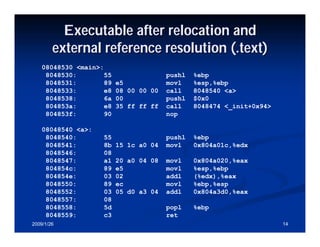
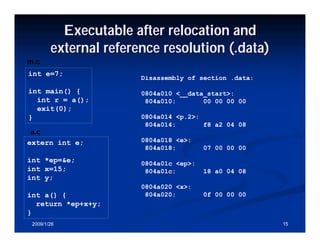
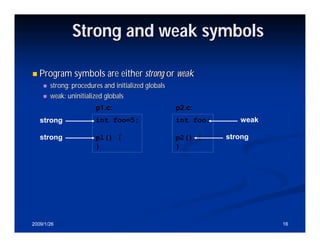
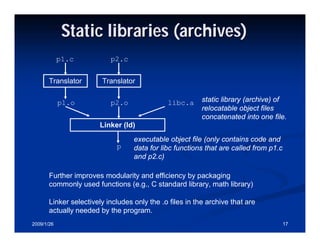
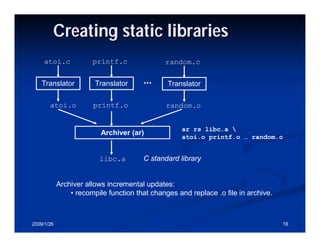
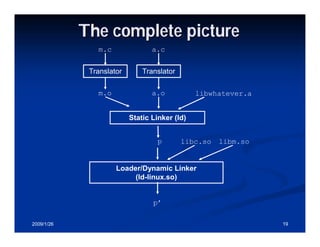
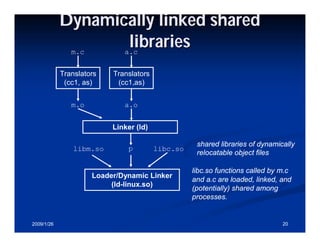
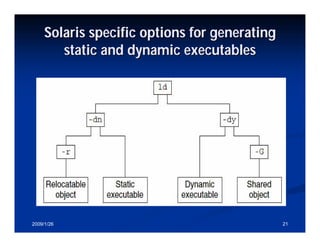
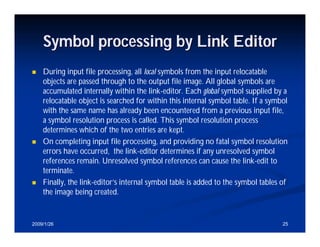
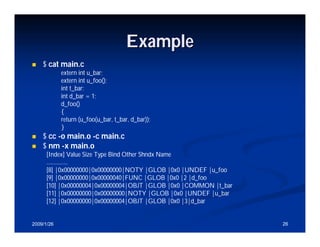
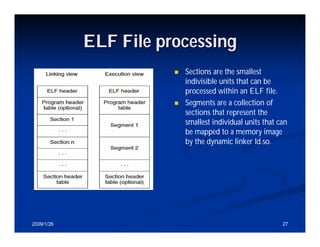
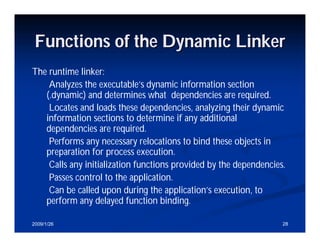
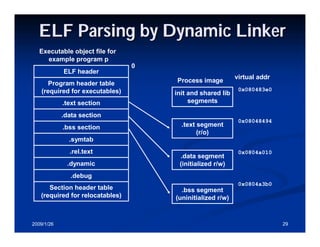
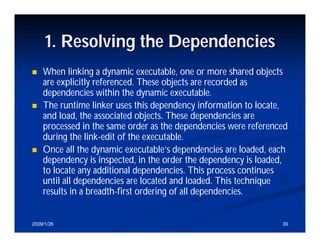
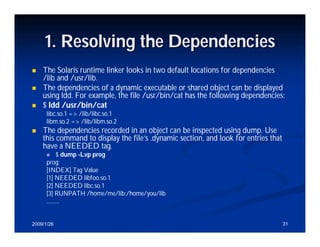
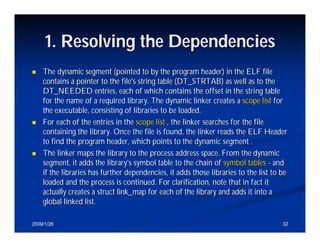
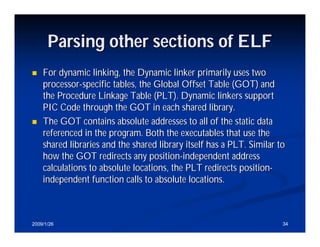
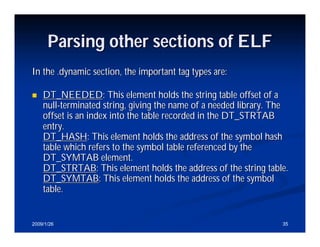
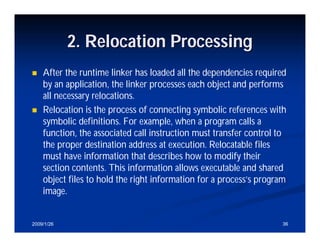
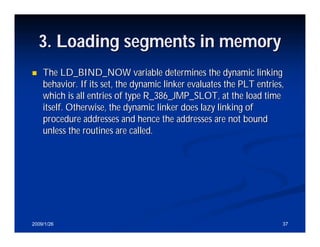
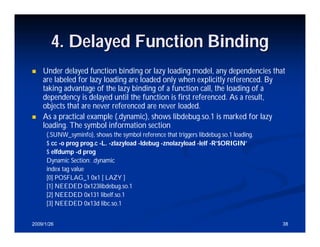
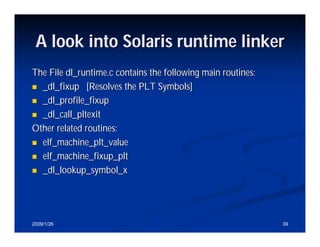
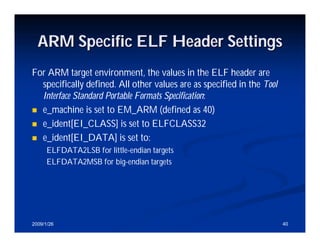
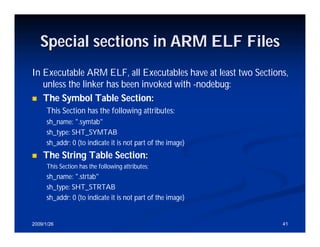
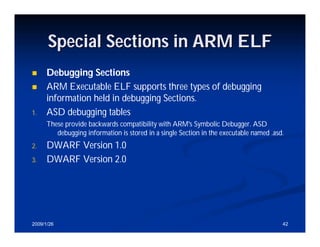


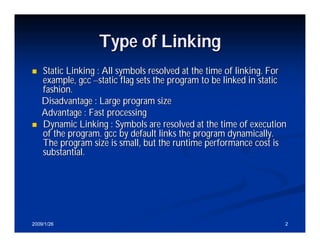
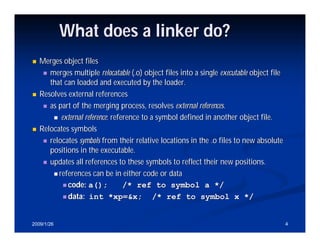
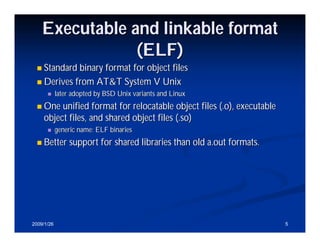
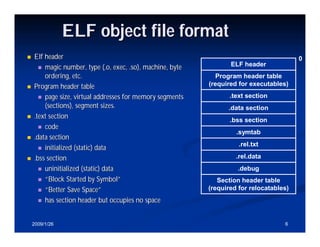
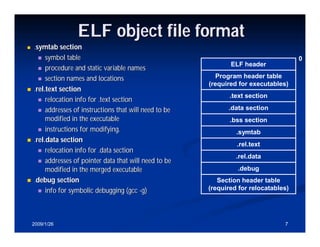
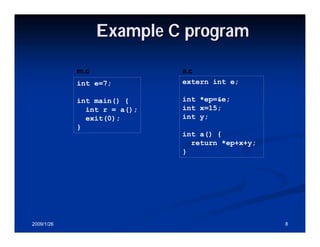
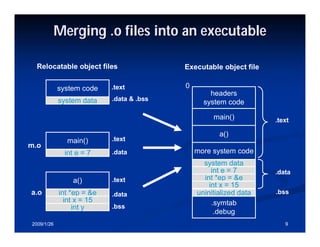
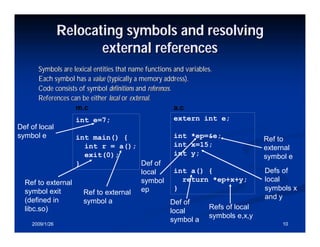
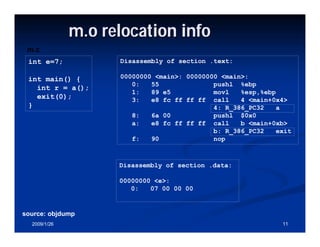
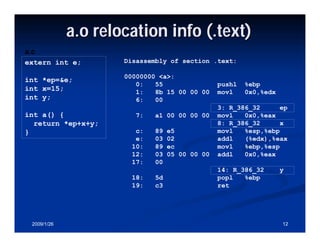
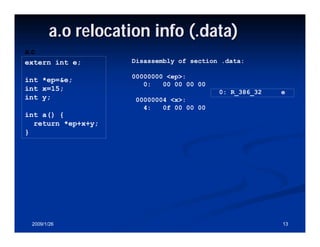
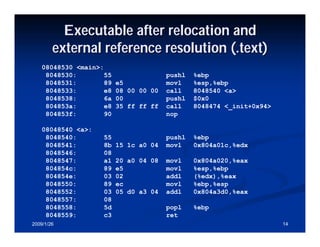
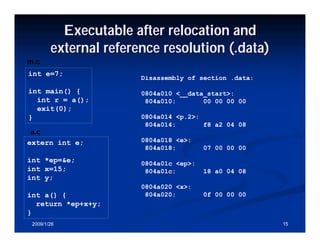
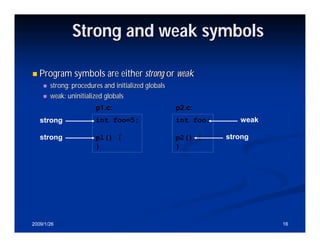
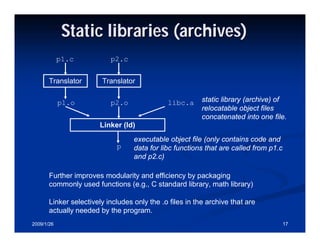
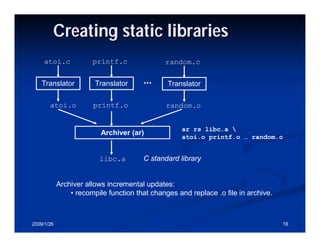
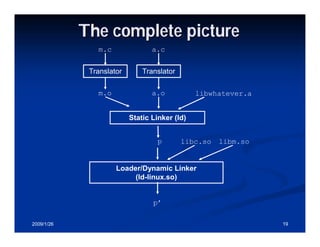
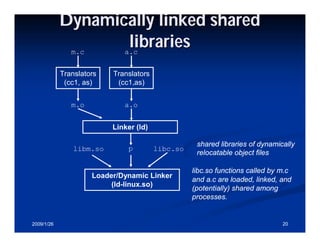
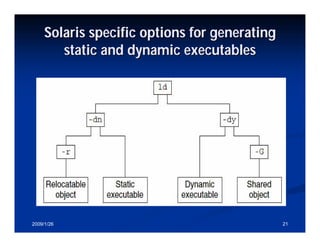
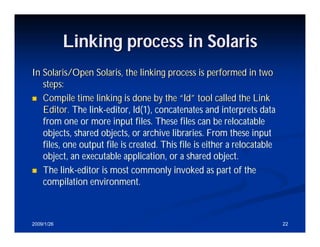
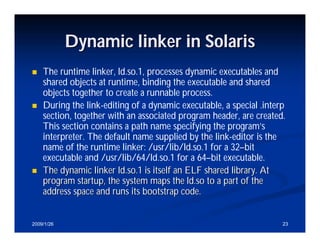
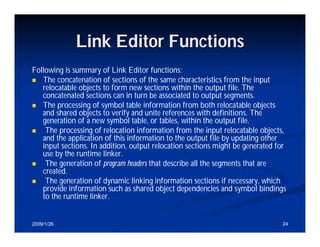
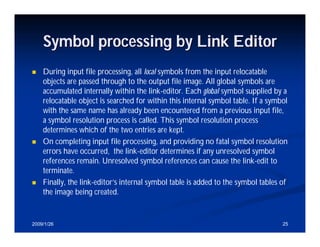
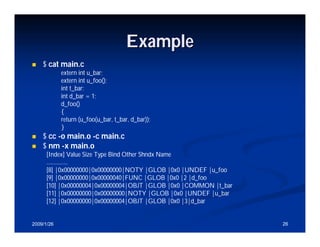
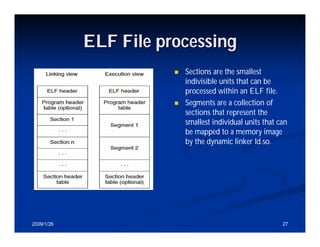
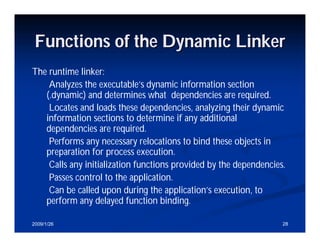
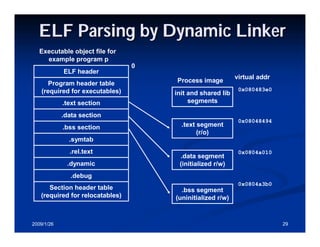
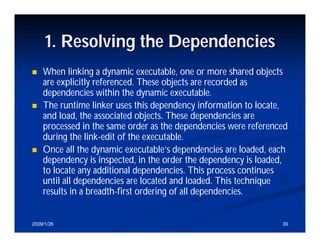
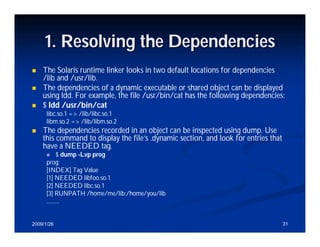
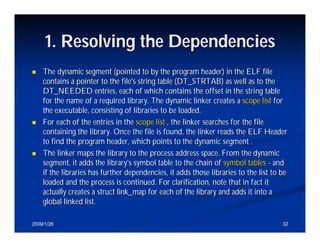
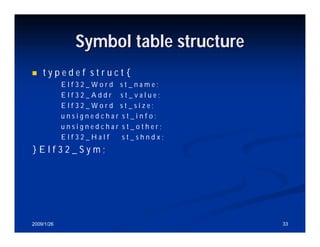
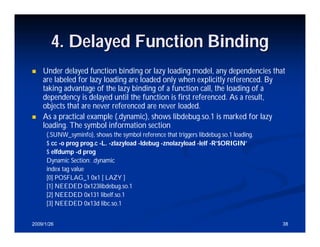
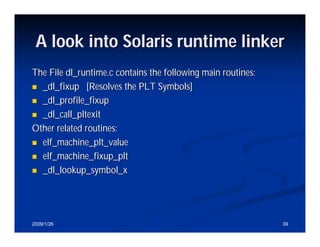
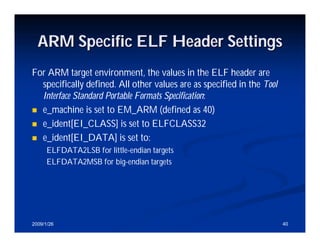
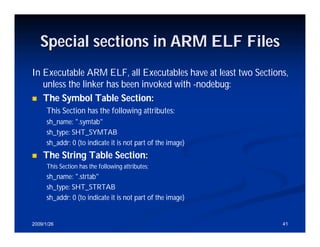
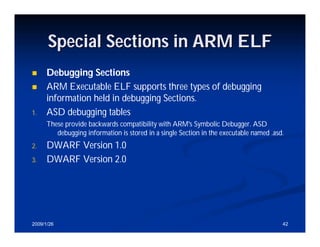
The document provides an overview of dynamic and static linking, explaining the differences in symbol resolution at linking time versus execution time. It details the linking process involving object files and the role of linkers in merging, relocating, and resolving symbols, as well as the ELF (Executable and Linkable Format) structure. Additionally, it covers the functions of static libraries and dynamic shared libraries, along with specifics related to Solaris linking processes.