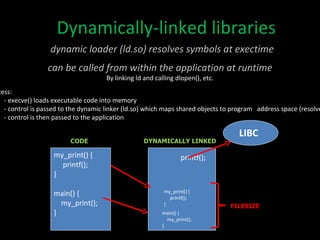
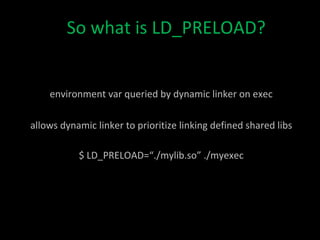
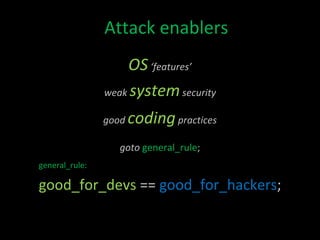
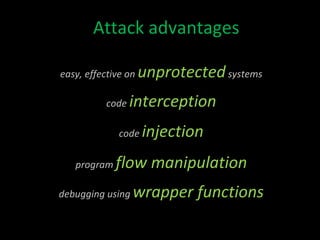
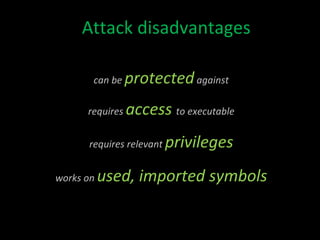
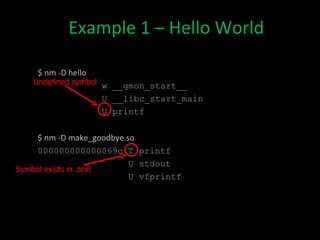
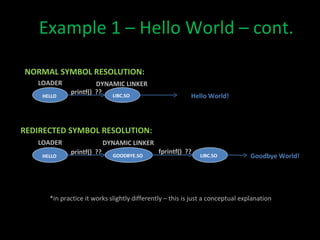
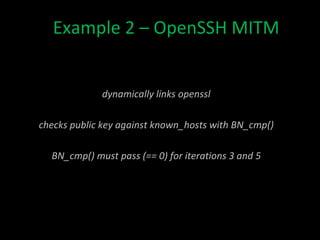
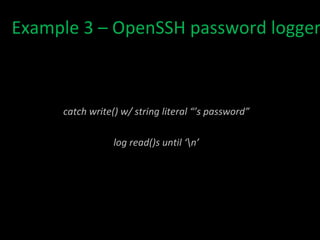
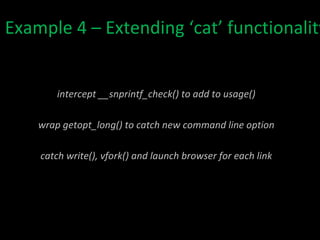
The document discusses how the Linux dynamic loader and LD_PRELOAD environment variable can be exploited to intercept and modify the behavior of shared library functions at runtime. It provides examples of how this technique could be used to implement a man-in-the-middle attack on OpenSSH authentication, log passwords, and extend the functionality of system programs like 'cat'. While powerful for debugging, this approach also has security disadvantages as it requires access to the executable and works only on exported symbols.
![Exploiting the Linux Dynamic Loader with LD_PRELOAD David Kaplan [email_address] DC9723 – June 2011](https://image.slidesharecdn.com/ldpreloadpresentationdc9723june11final-110625112630-phpapp01/75/LD_PRELOAD-Exploitation-DC9723-1-2048.jpg)