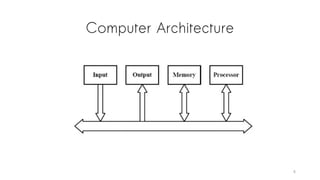
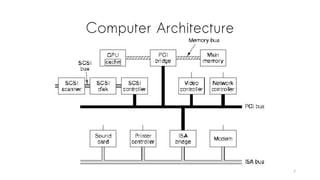
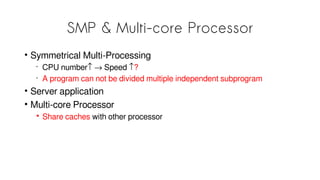
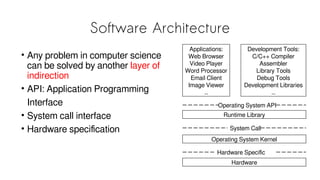
The document discusses how a "Hello World" program works behind the scenes. It covers topics like compilation, linking, executable file formats, loading programs into memory, and process creation. The key points are:
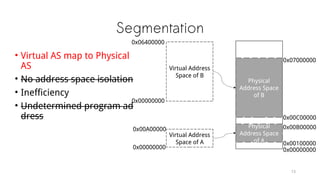
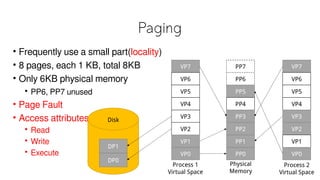
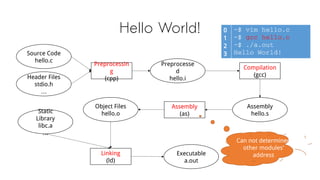
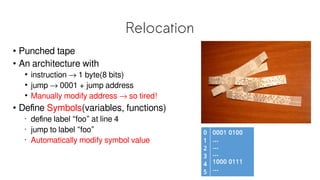
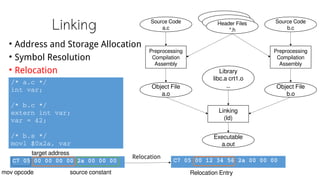
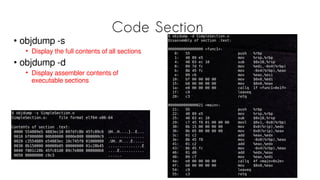
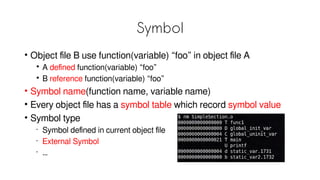
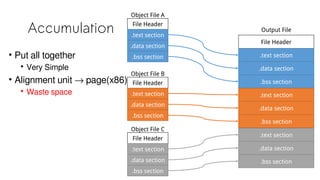
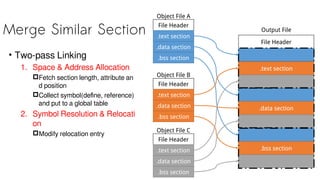
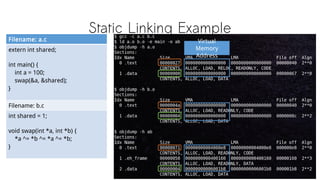
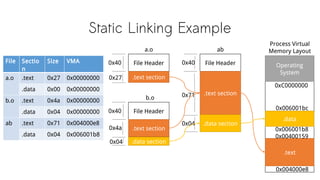
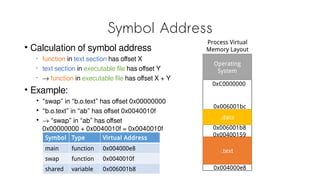
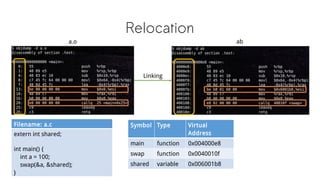
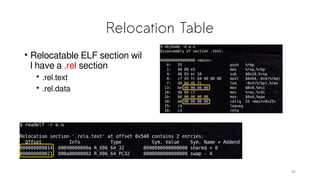
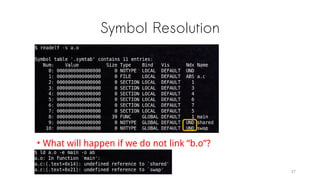
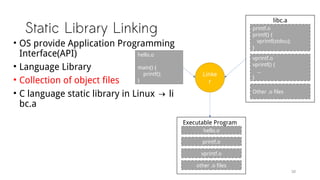
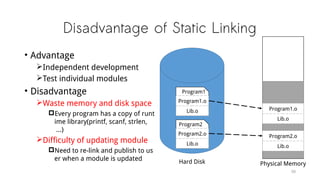
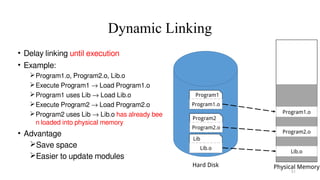
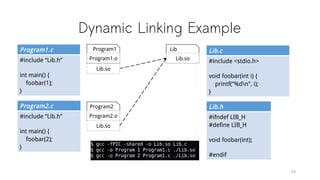
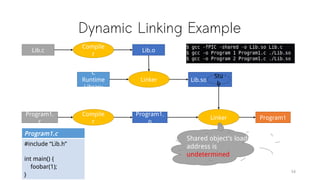
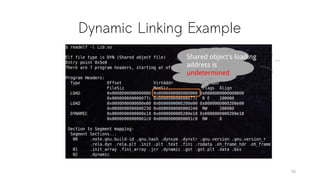
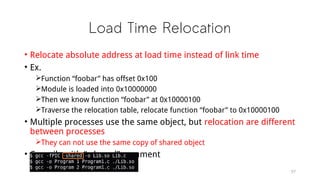
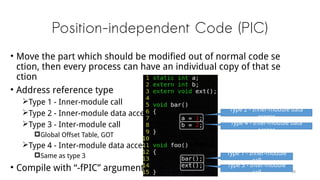
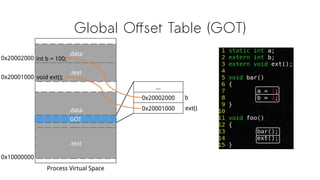
1) A C program is compiled into an object file, then linked with library files to create an executable. The linker resolves symbols and relocates addresses.
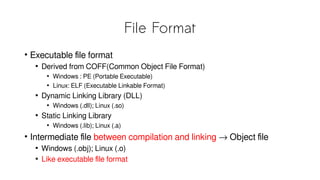
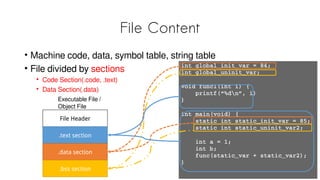
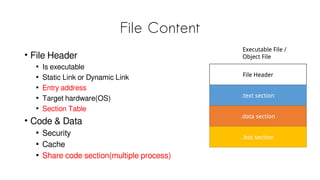
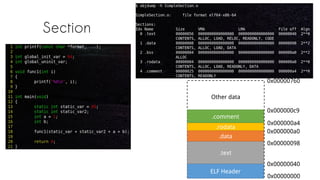
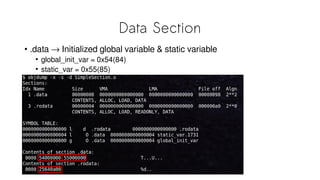
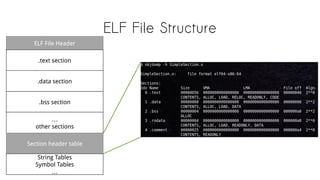
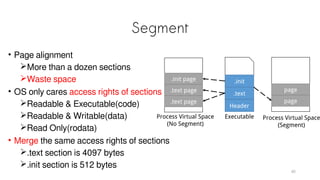
2) Executable files use formats like ELF that contain machine code, data, symbol tables, and sections. Object files have a similar format.
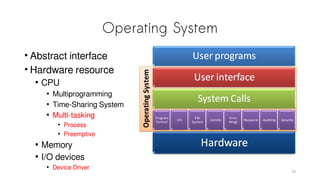
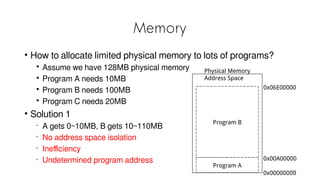
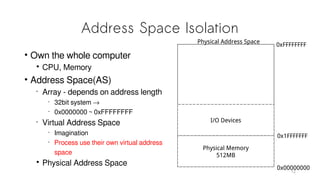
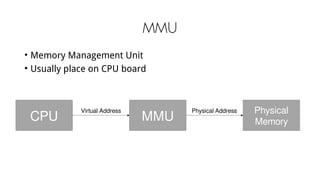
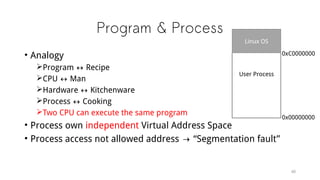
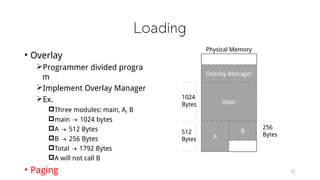
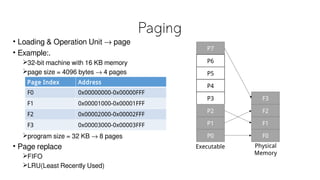
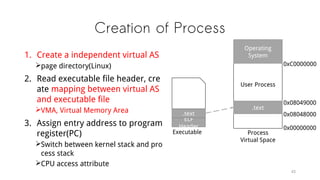
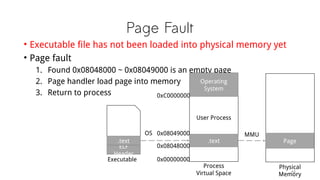
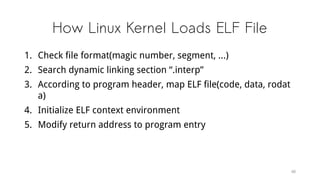
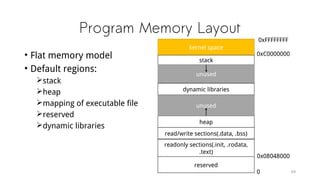
3) When a program runs, the OS loads pages of the executable into memory as needed and sets up the process with its own virtual address space.
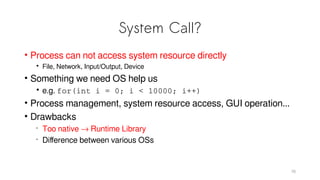
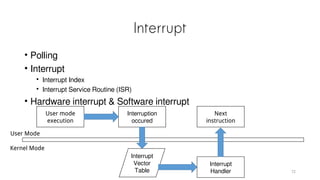
4) System calls
![Hello World!
0
1
2
3
~$ vim hello.c
~$ gcc hello.c
~$ ./a.out
Hello World!
Filename: hello.c
0
1
2
3
4
5
6
7
#include <stdio.h>
int main(int argc, char *argv[])
{
printf(“Hello World!n”);
return 0;
}
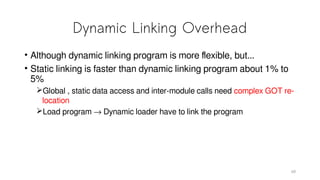
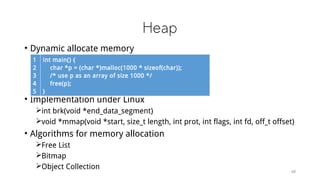
• Why we need to compile the program
• What is in an executable file
• What is the meaning of “#include<stdio.h>”
• Difference between
• Compiler(Microsoft C/C++ compiler, GCC)
• Hardware architecture(ARM, x86)
• How to execute a program
• What does OS do
• Before main function
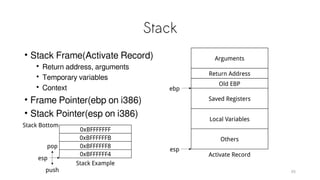
• Memory layout
• If we don’t have OS](https://image.slidesharecdn.com/helloworld-internals-150412232303-conversion-gate01/85/The-Internals-of-Hello-World-Program-4-320.jpg)


![Thinking
• Why do we need to compile the program
• What is in an executable file
• What is the meaning of “#include<stdio.h>”
• Difference between
Compiler(Microsoft VC, GCC)
Hardware architecture(ARM, x86)
• How to execute a program
What does OS do
Before main function
Memory layout
If we don’t have OS
0
1
2
3
~$ vim hello.c
~$ gcc hello.c
~$ ./a.out
Hello World!
Filename: hello.c
0
1
2
3
4
5
6
7
#include <stdio.h>
int main(int argc, char *argv[])
{
printf(“Hello World!n”);
return 0;
}
74](https://image.slidesharecdn.com/helloworld-internals-150412232303-conversion-gate01/85/The-Internals-of-Hello-World-Program-74-320.jpg)