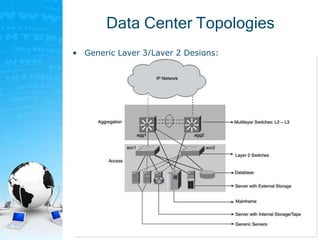
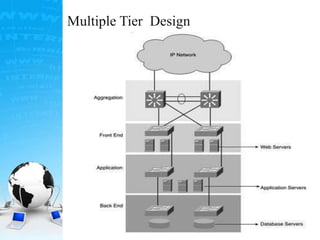
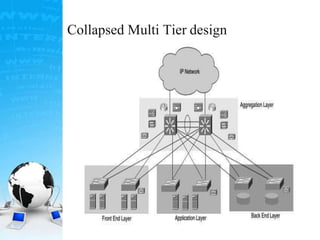
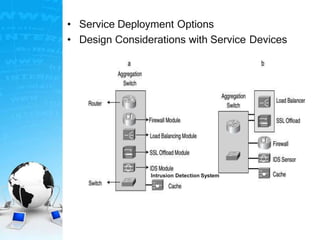
Here are the key points of a collapsed multitier design:
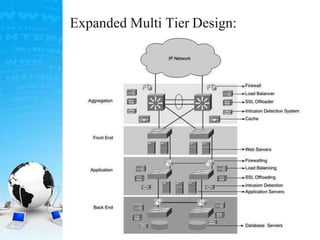
- All server farms are directly connected without physical separation between Layer 2 switches. This reduces hardware costs.
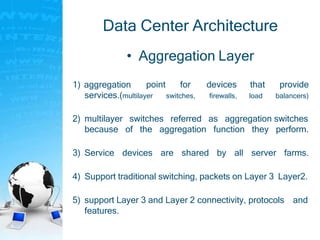
- Services like load balancing, firewalling, etc. are concentrated at the aggregation layer rather than being distributed between tiers.
- Less hardware is required compared to an expanded design as there is no need for separate switches and devices at each tier.
- However, it provides less control and scalability compared to an expanded design as tiers are not physically isolated. For example, if one tier needs to be scaled out, it affects the other tiers.
- Security may also be weaker as there is no firewall segmentation between tiers.