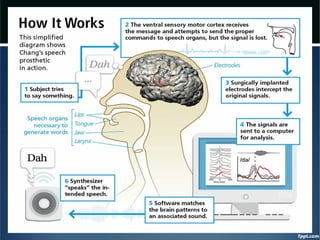
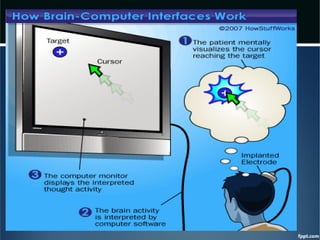
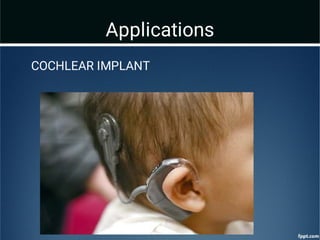
This document provides an overview of brain-computer interfaces (BCI). It discusses how a BCI allows a direct connection between the brain and a computer to control devices. It describes the different types of BCI as invasive, partially invasive, and non-invasive. The document outlines the basic components of a BCI system including signal acquisition, processing, and data manipulation. Finally, it discusses applications of BCI technology for assisting those with disabilities and conditions such as ALS, as well as uses in gaming, social interactions, and research.