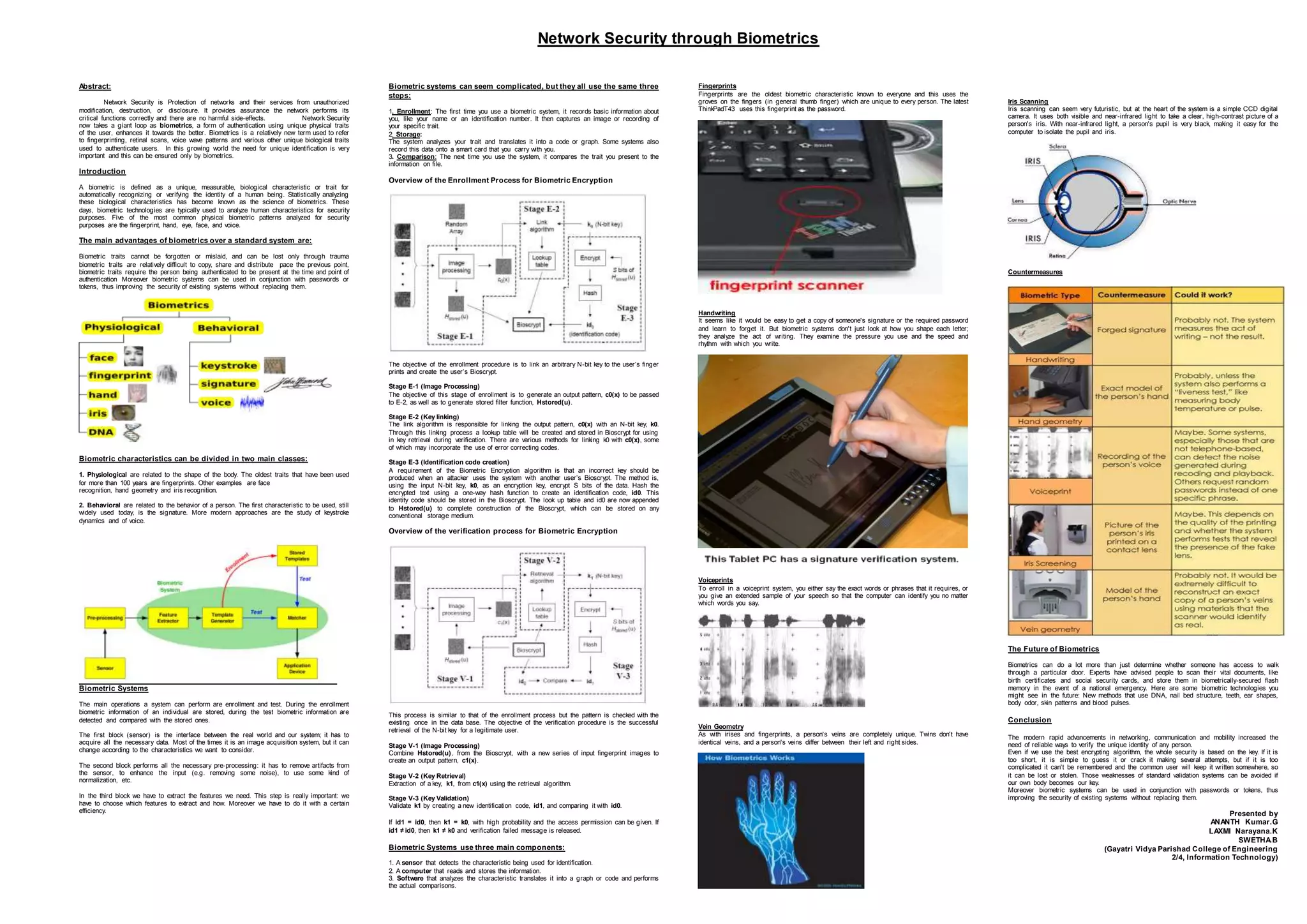
Network security is enhanced through biometrics authentication which uses unique physical traits to verify user identity. Biometrics is more secure than passwords since traits cannot be forgotten, stolen, or easily copied. The document discusses common biometric traits like fingerprints, iris scans, and voice recognition. It explains how biometric systems work by enrolling traits during initial use then comparing submitted traits to stored information for authentication. Biometrics provides stronger security for networks and systems by using the human body as a verification method.