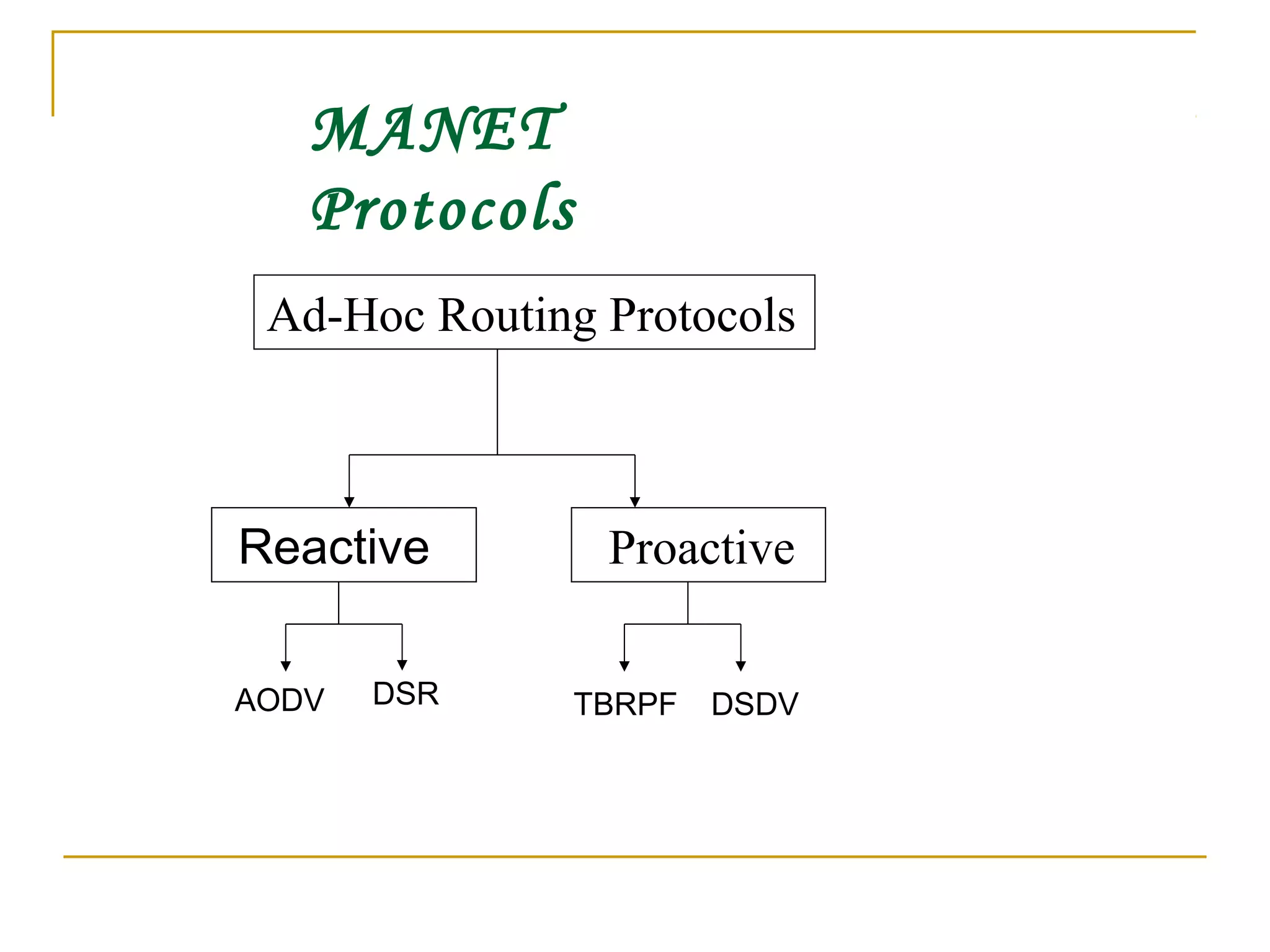
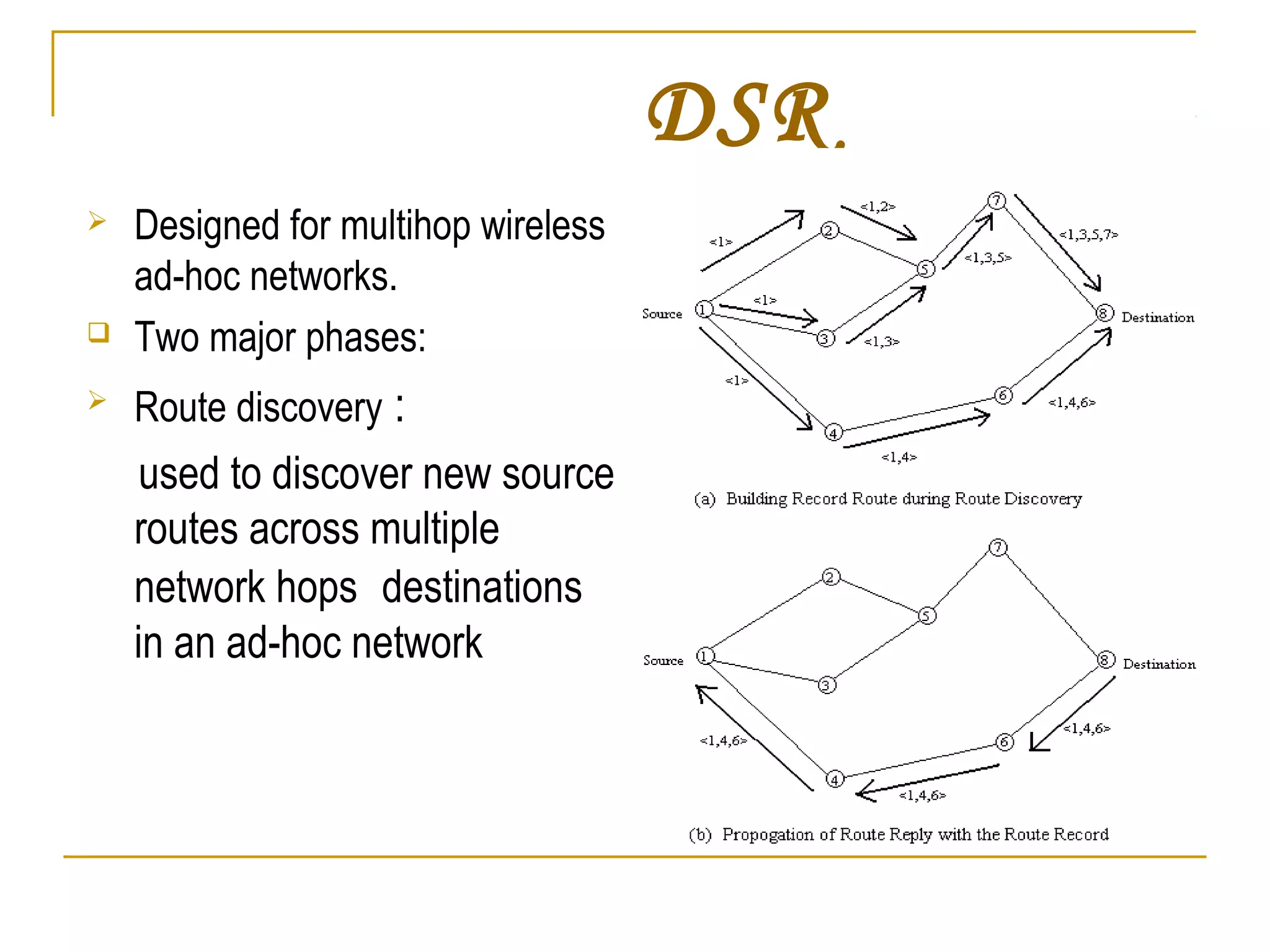
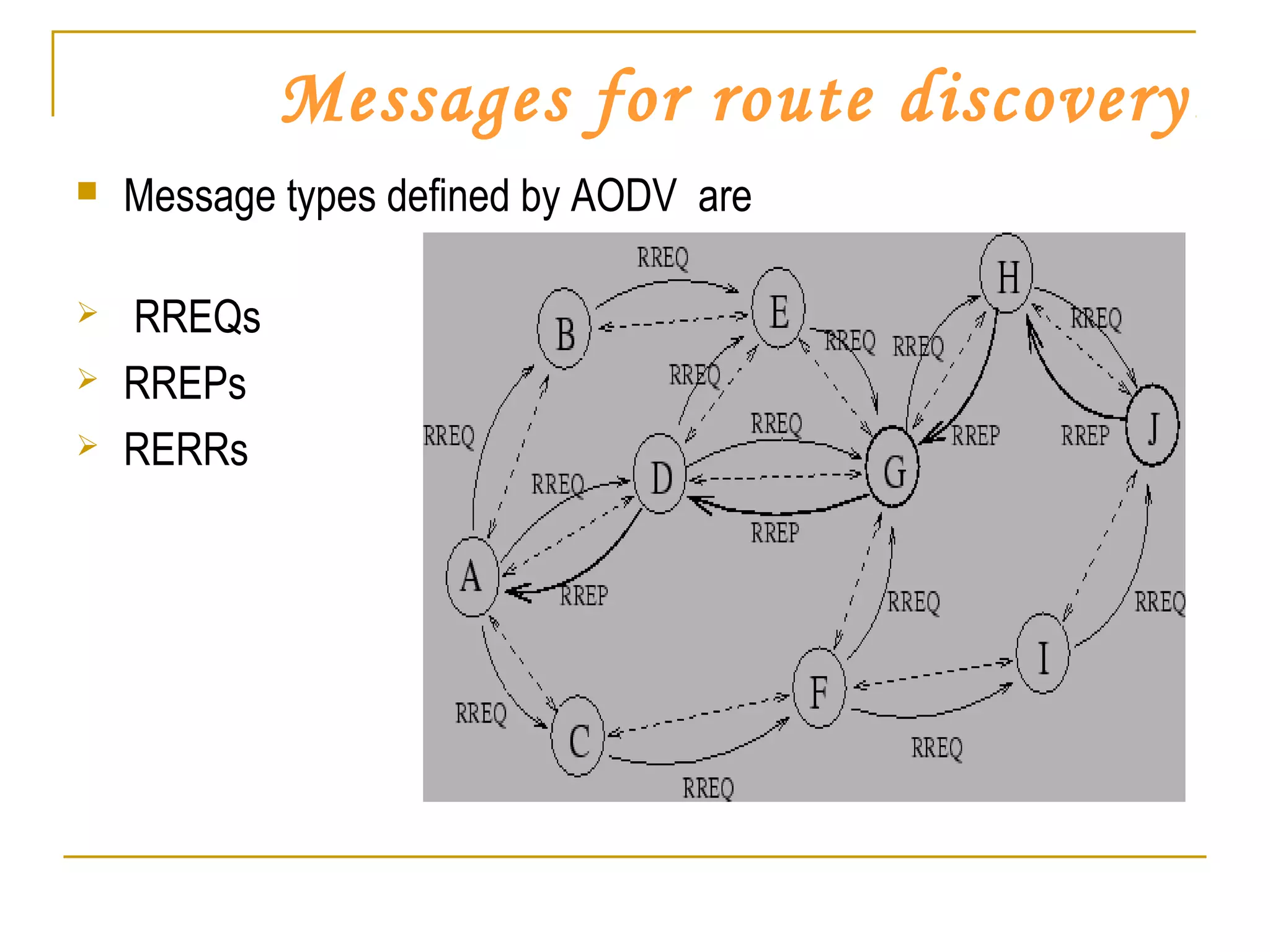
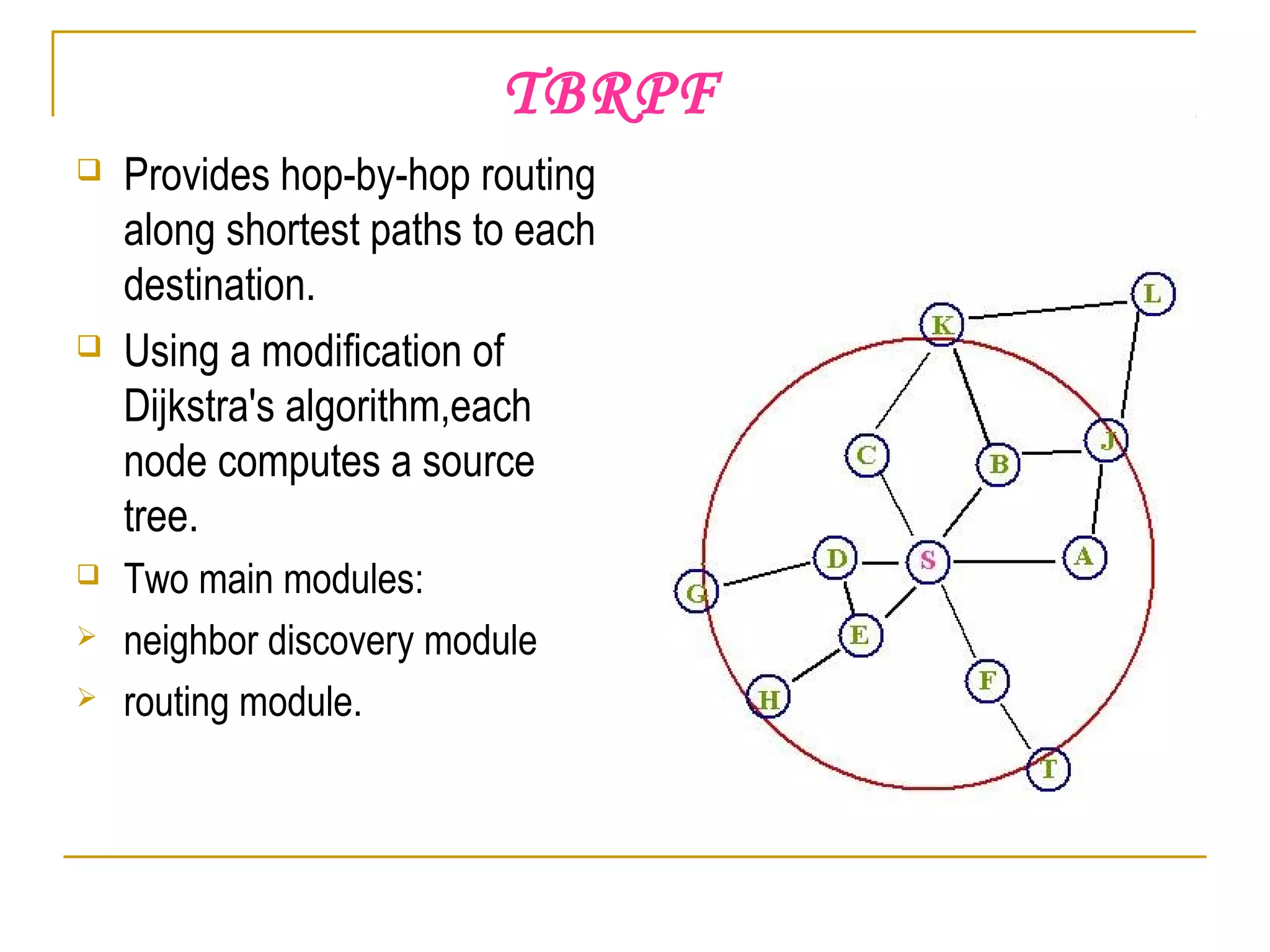
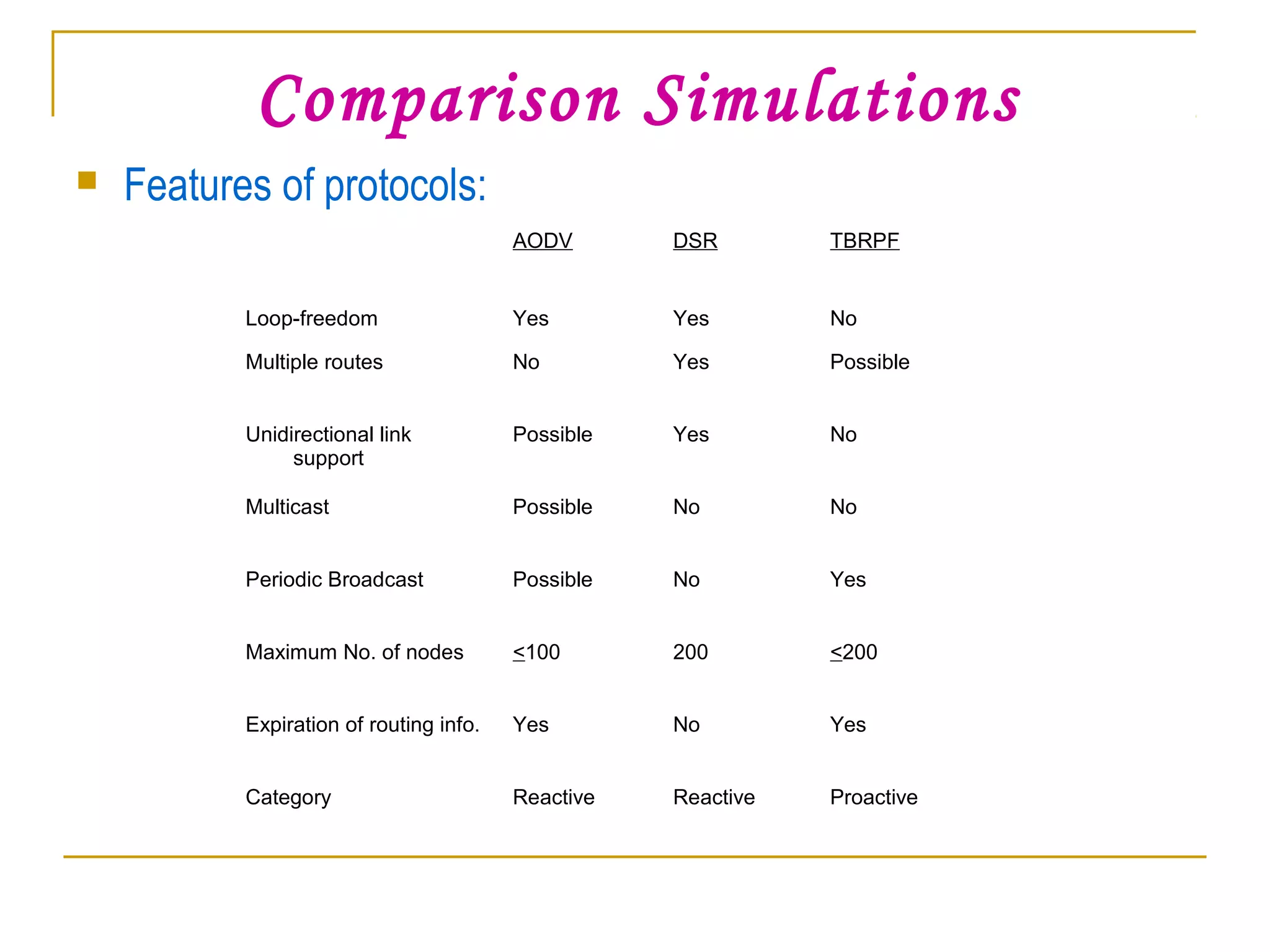
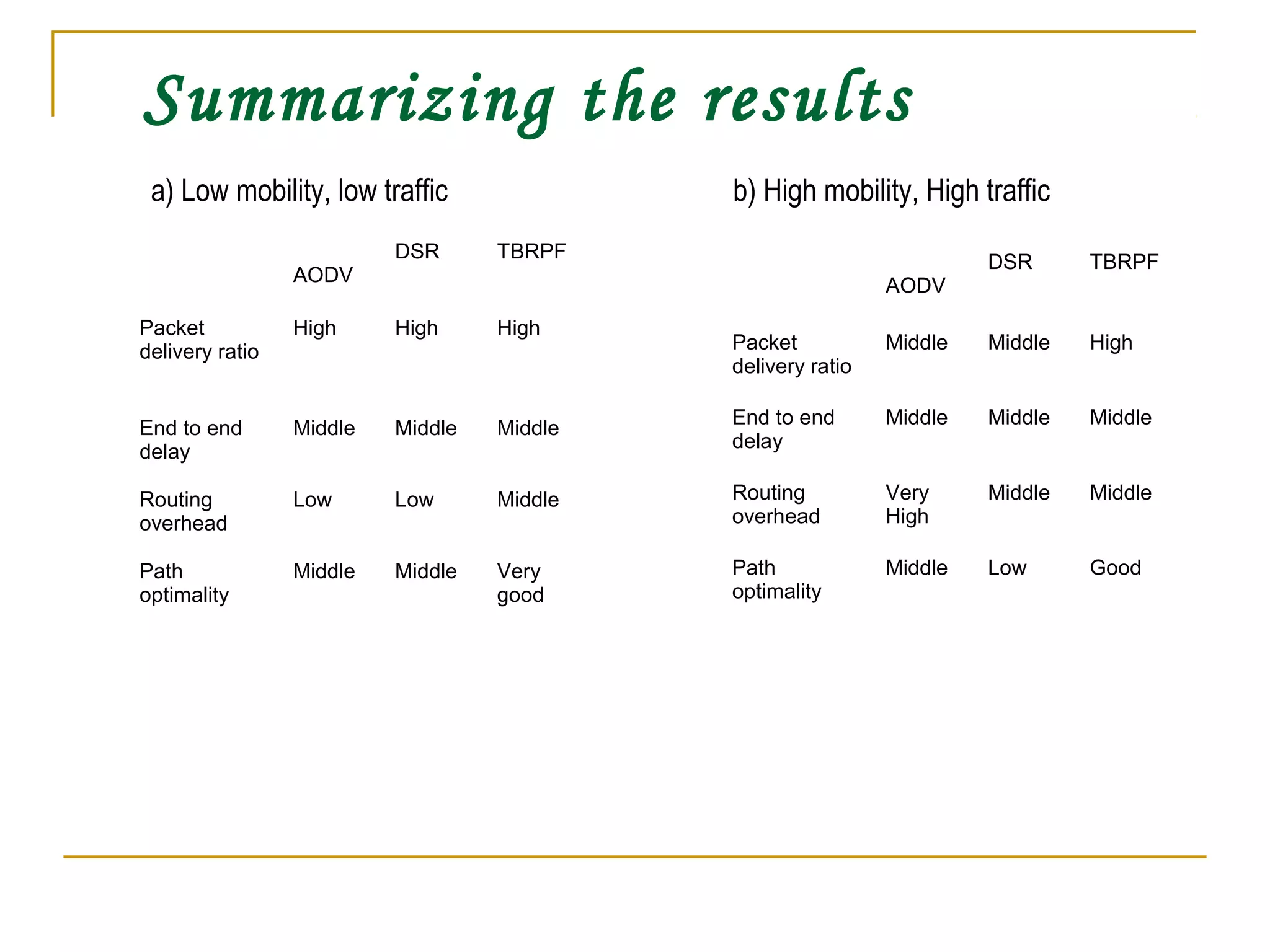
This document provides an overview of mobile ad hoc networks (MANETs) and several routing protocols used in MANETs. It defines MANETs and their characteristics. It then describes several representative routing protocols, including reactive (AODV, DSR), proactive (DSDV, TBRPF) protocols. It compares these protocols through simulations on metrics like packet delivery ratio, end-to-end delay, routing overhead under different traffic loads and node mobility. It finds that no single protocol performs best under all conditions and that fundamental open questions around scalability, energy efficiency and security remain.