This document discusses number systems and data representation in computers. It covers topics like binary, decimal, hexadecimal, and ASCII number systems. Some key points covered include:
- Computers use the binary number system and positional notation to represent data precisely.
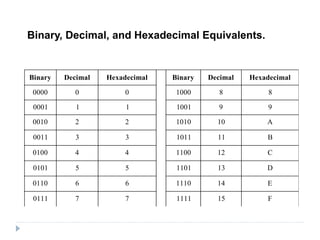
- Different number systems have different bases (like binary base-2, decimal base-10, hexadecimal base-16).
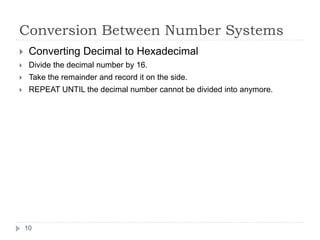
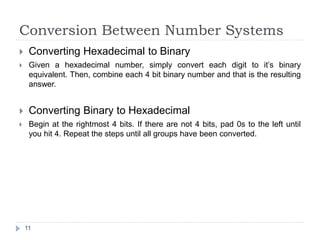
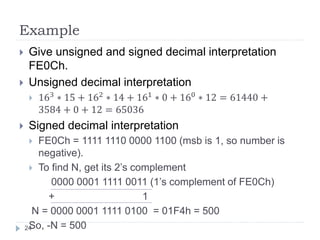
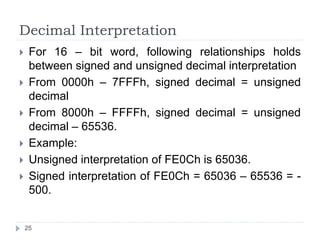
- Methods for converting between number systems like binary to decimal and hexadecimal to decimal.
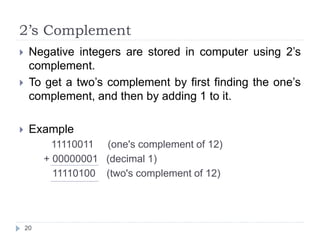
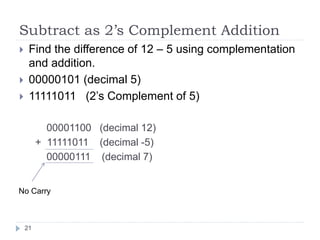
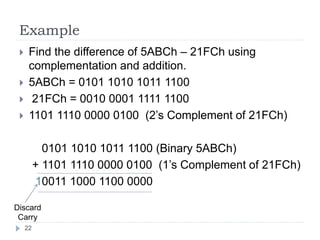
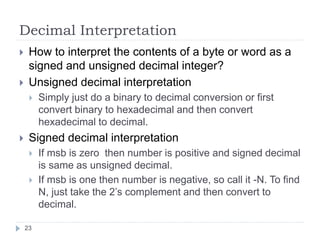
- Signed and unsigned integers, ones' complement, twos' complement representation of negative numbers.
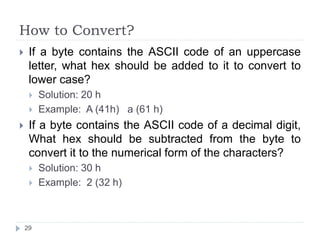
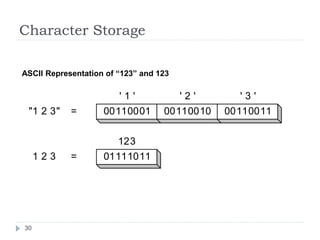
- ASCII encoding of characters and how to convert between character and numeric representations.


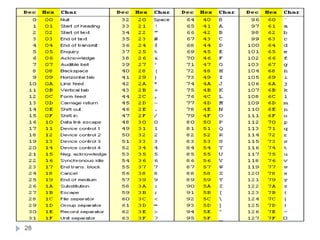
![Character Representation
All data, characters must be coded in binary to be
processed by the computer.
ASCII:
American Standard Code for Information Interchange
Most popular character encoding scheme.
Uses 7 bit to code each character.
27 = 128 ASCII codes.
Single character Code = One Byte [7 bits: char code, 8th
bit set to zero]
32 to 126 ASCII codes: printable
0 to 31 and 127 ASCII codes: Control characters
27](https://image.slidesharecdn.com/3-datarepresentation-140905055307-phpapp01/85/Data-Representation-27-320.jpg)