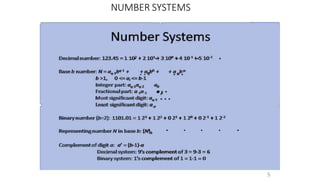
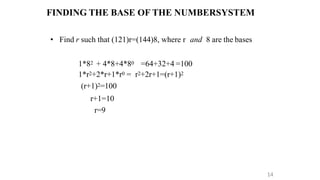
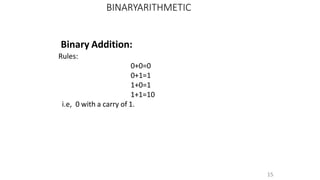
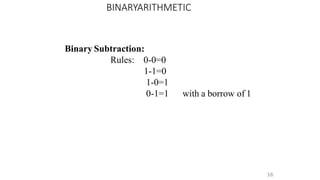
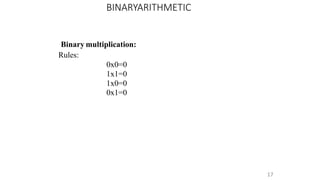
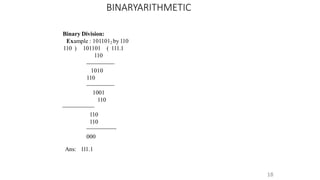
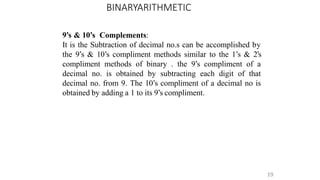
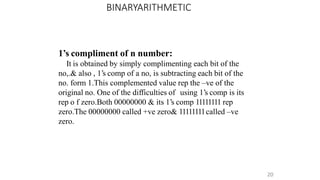
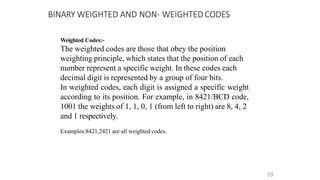
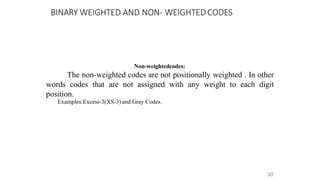
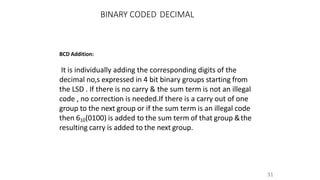
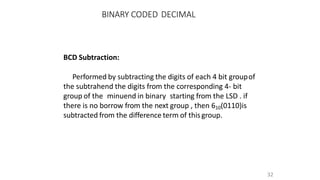
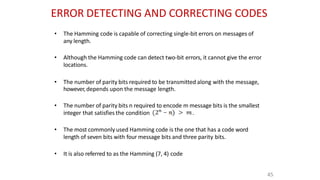
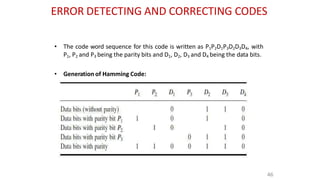
This document provides an overview of a computer organization course for first year BCA students. It covers topics like introduction to digital logic design, number systems, binary arithmetic operations, binary coded decimal, and non-weighted and weighted binary codes. The key concepts discussed include binary, octal, hexadecimal number conversions; addition, subtraction, multiplication and division in binary; 1's complement, 2's complement representations; and BCD and excess-3 coding schemes.