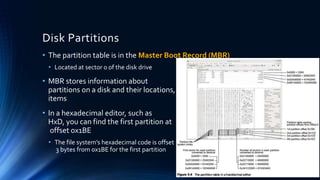
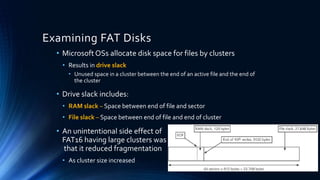
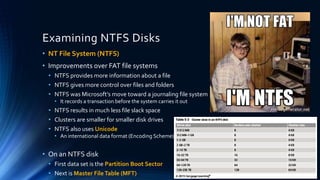
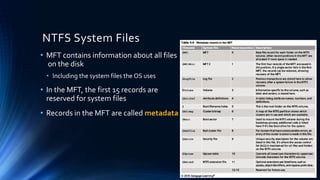
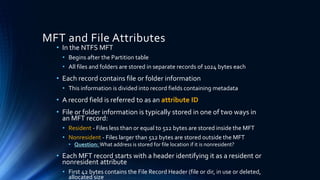
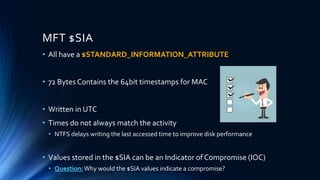
The document discusses Microsoft file structures. It explains that clusters contain sectors and store file data, with cluster size varying by file system. It describes the master boot record containing partition tables and the file allocation table (FAT) or master file table (NTFS) storing file metadata. Finally, it notes that deleted files have metadata changed in FAT/NTFS and may remain recoverable from slack space.