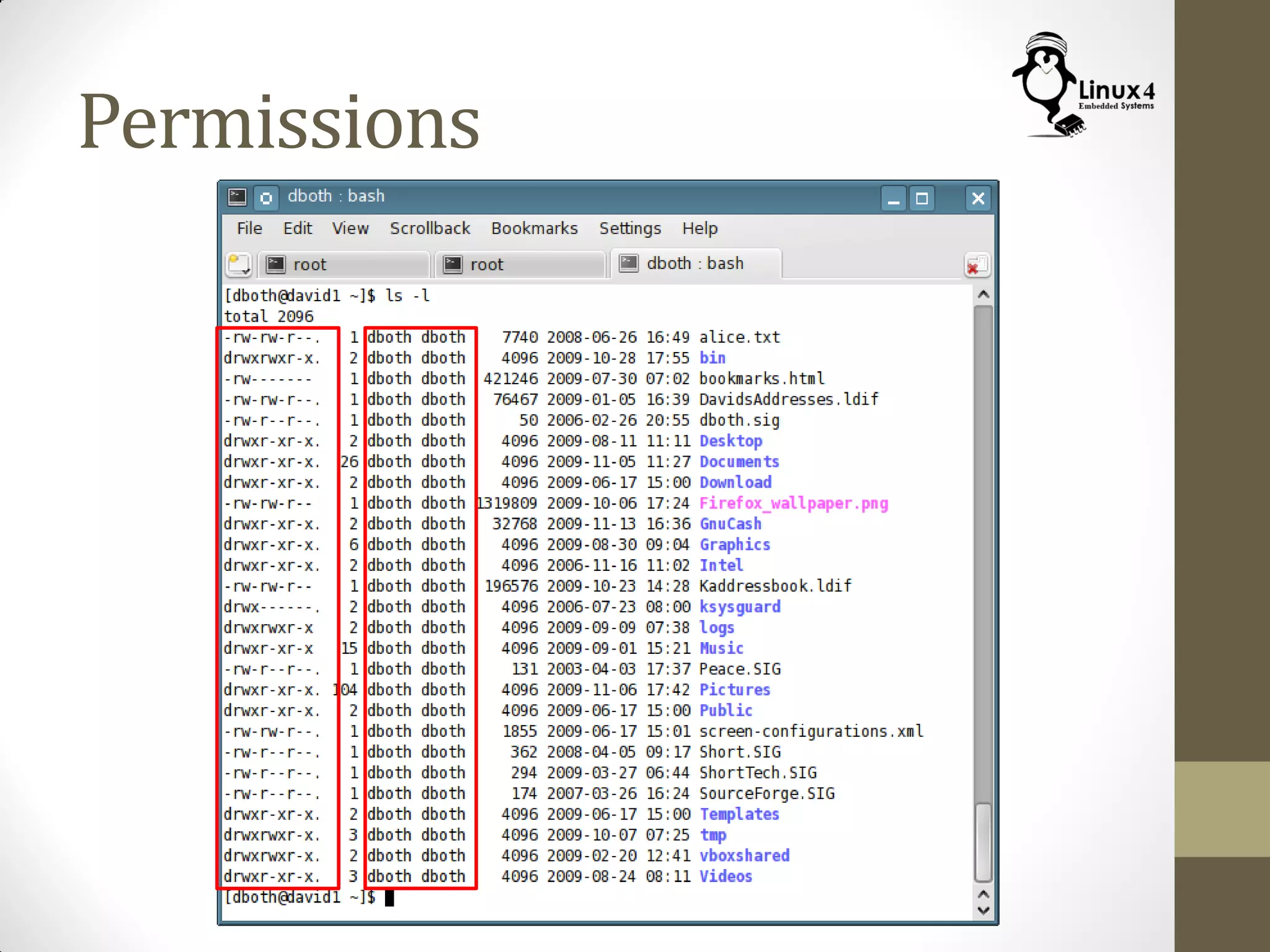
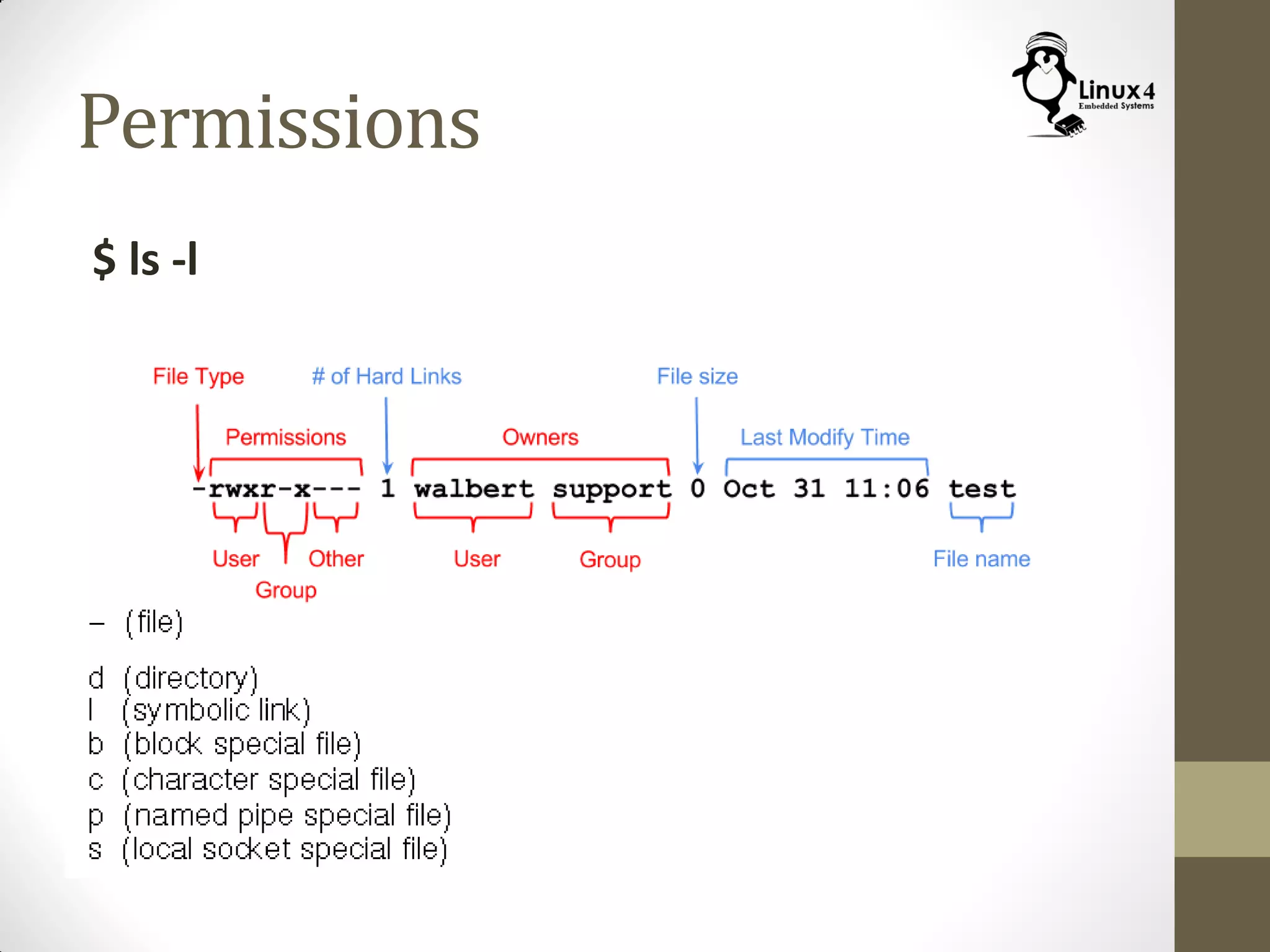
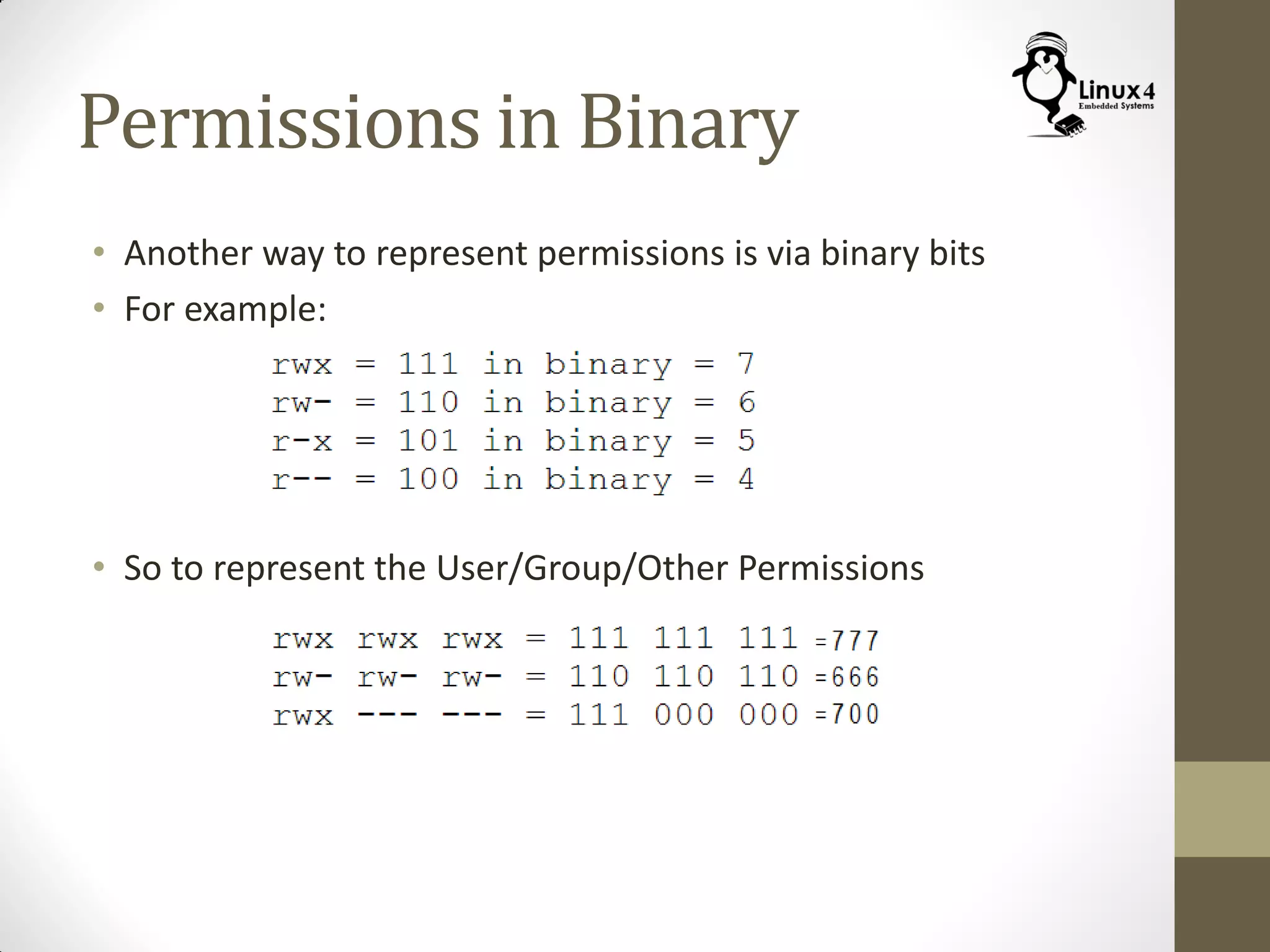
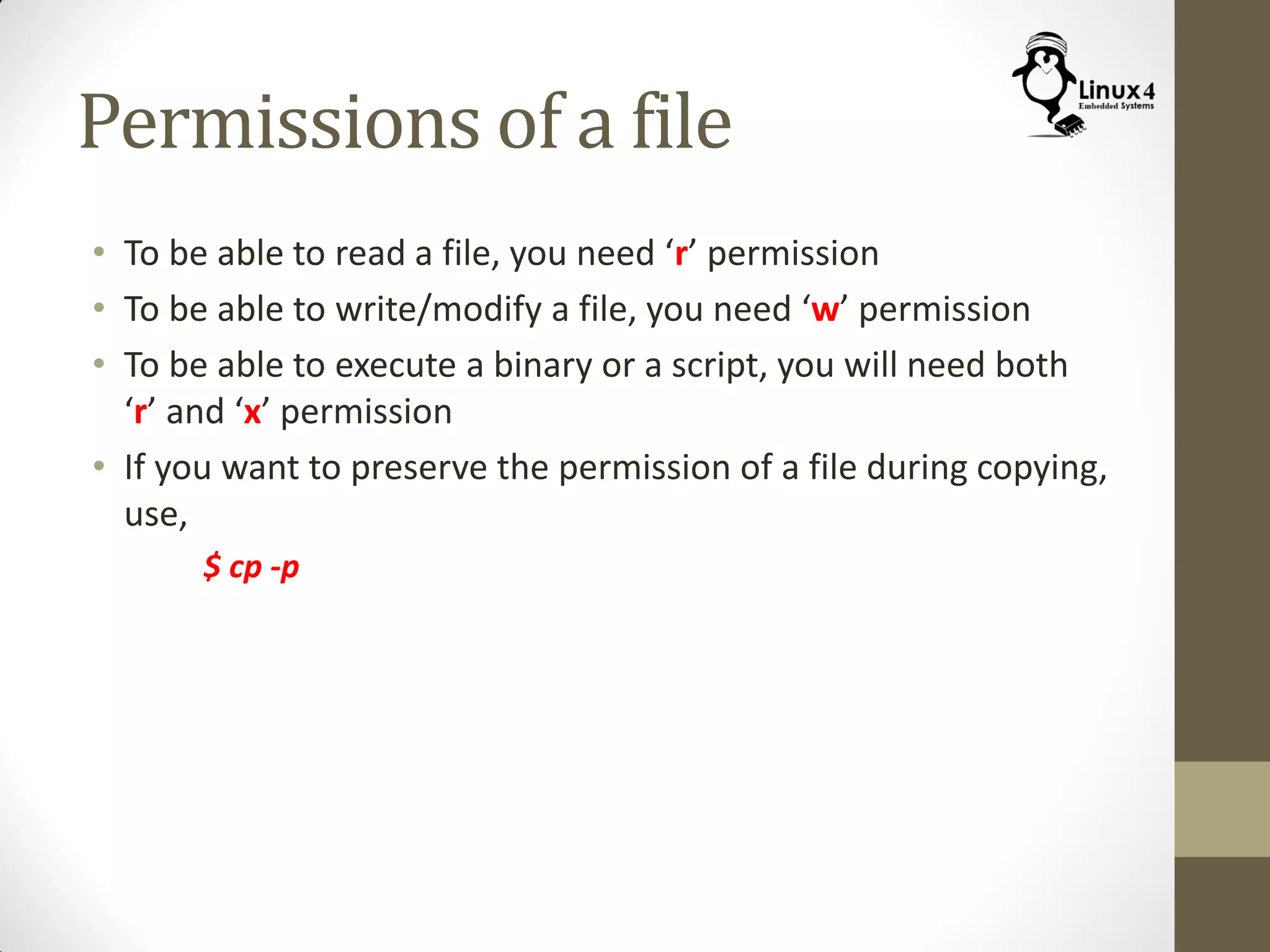
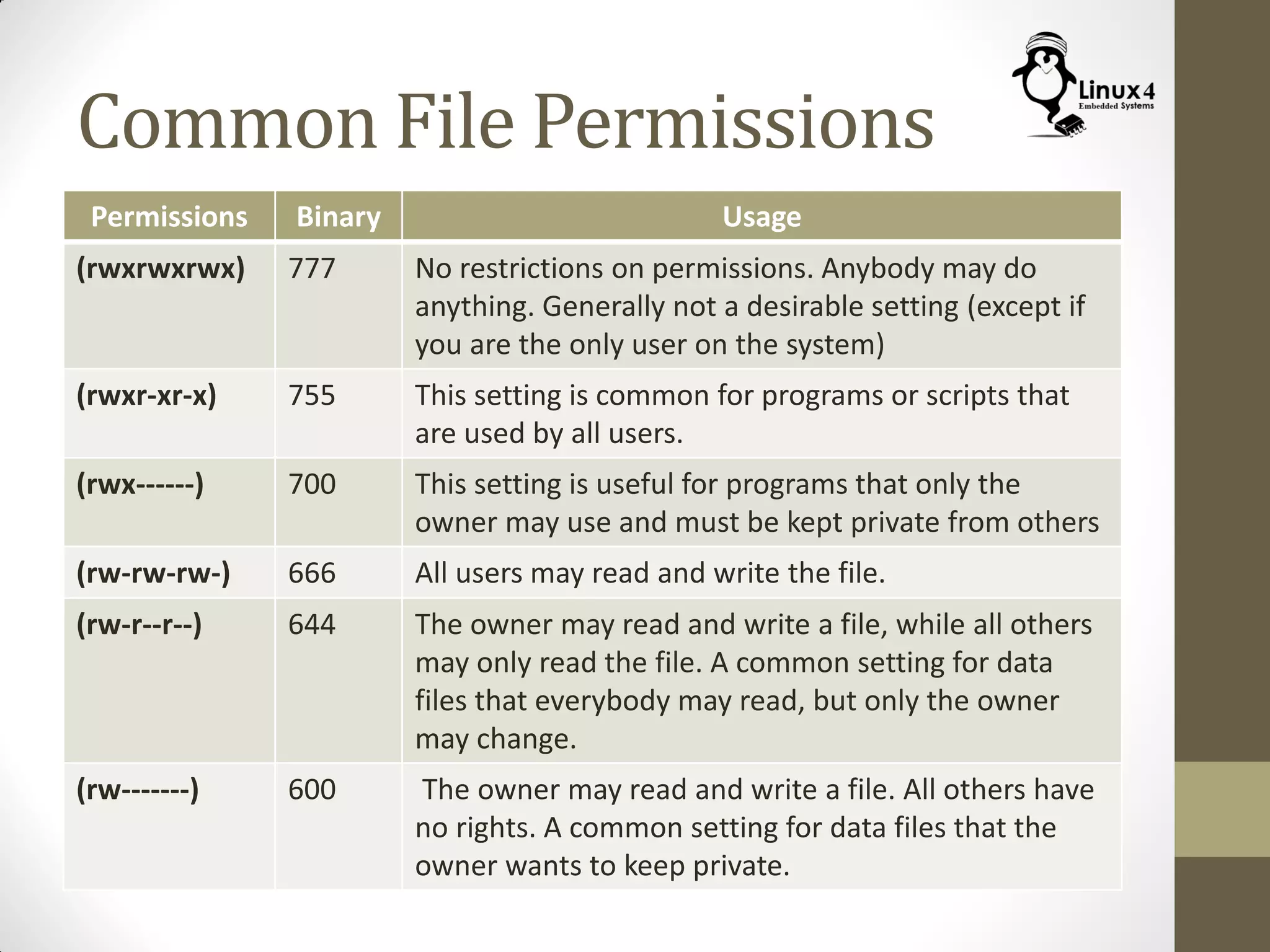
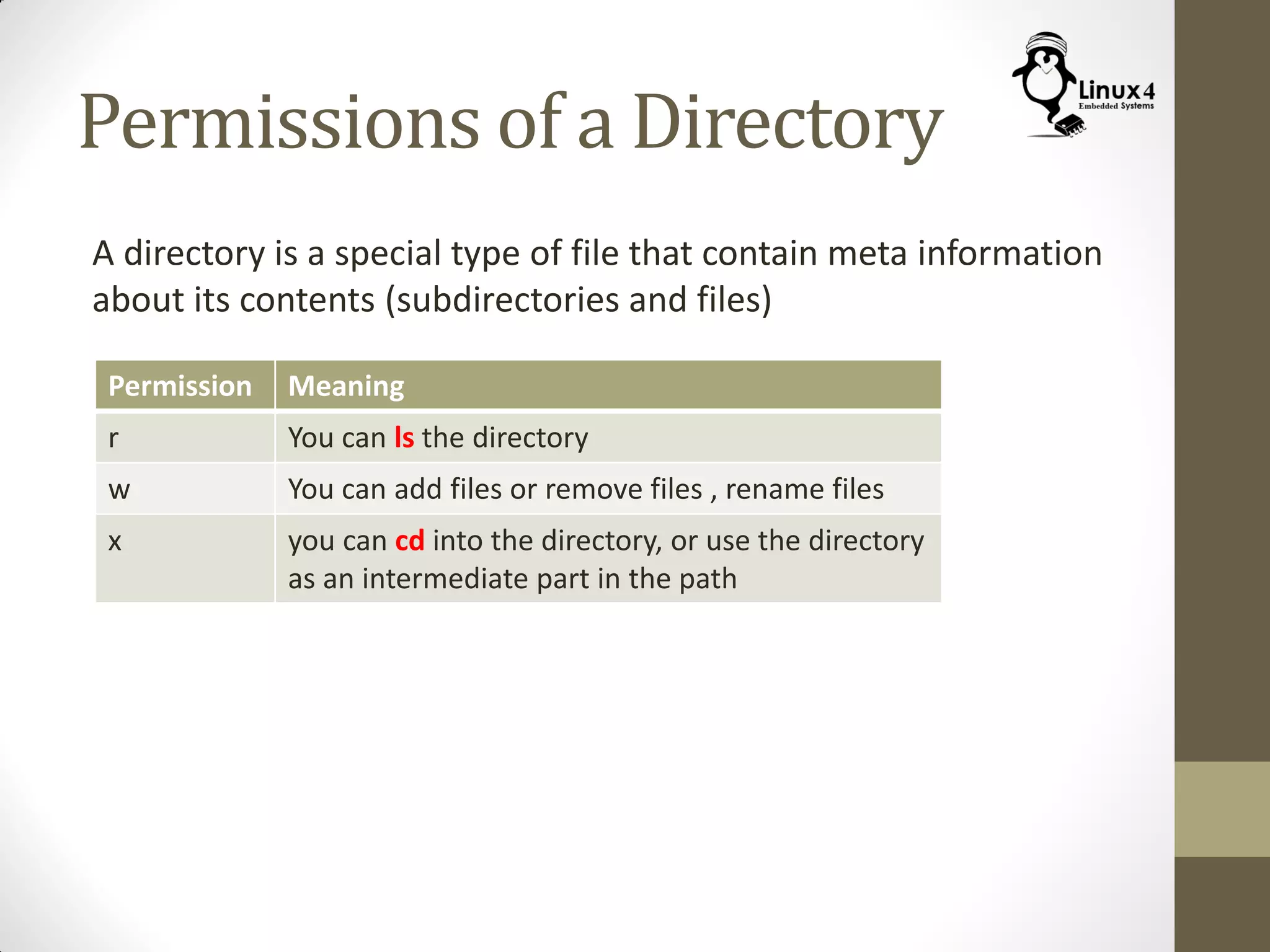
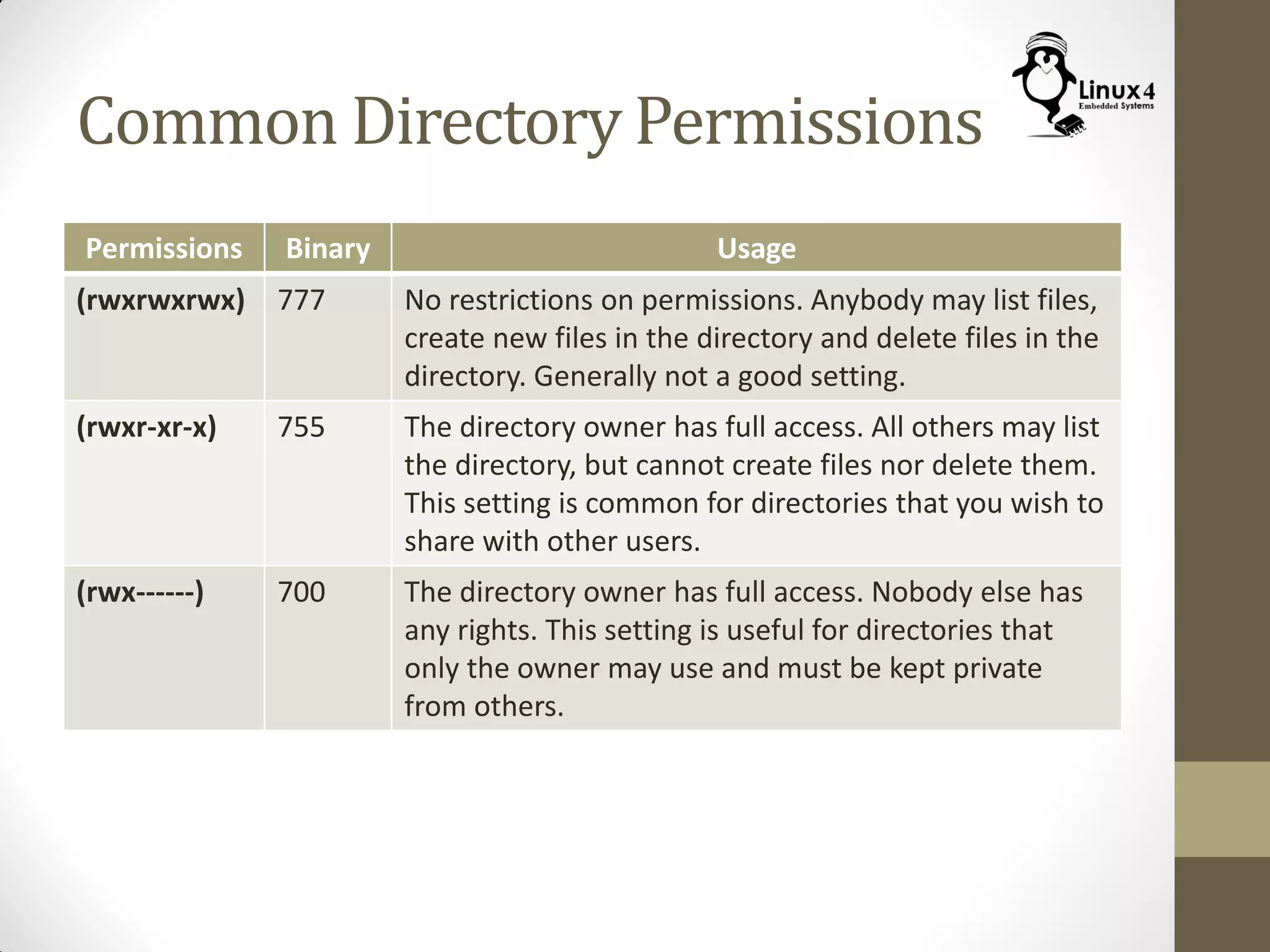
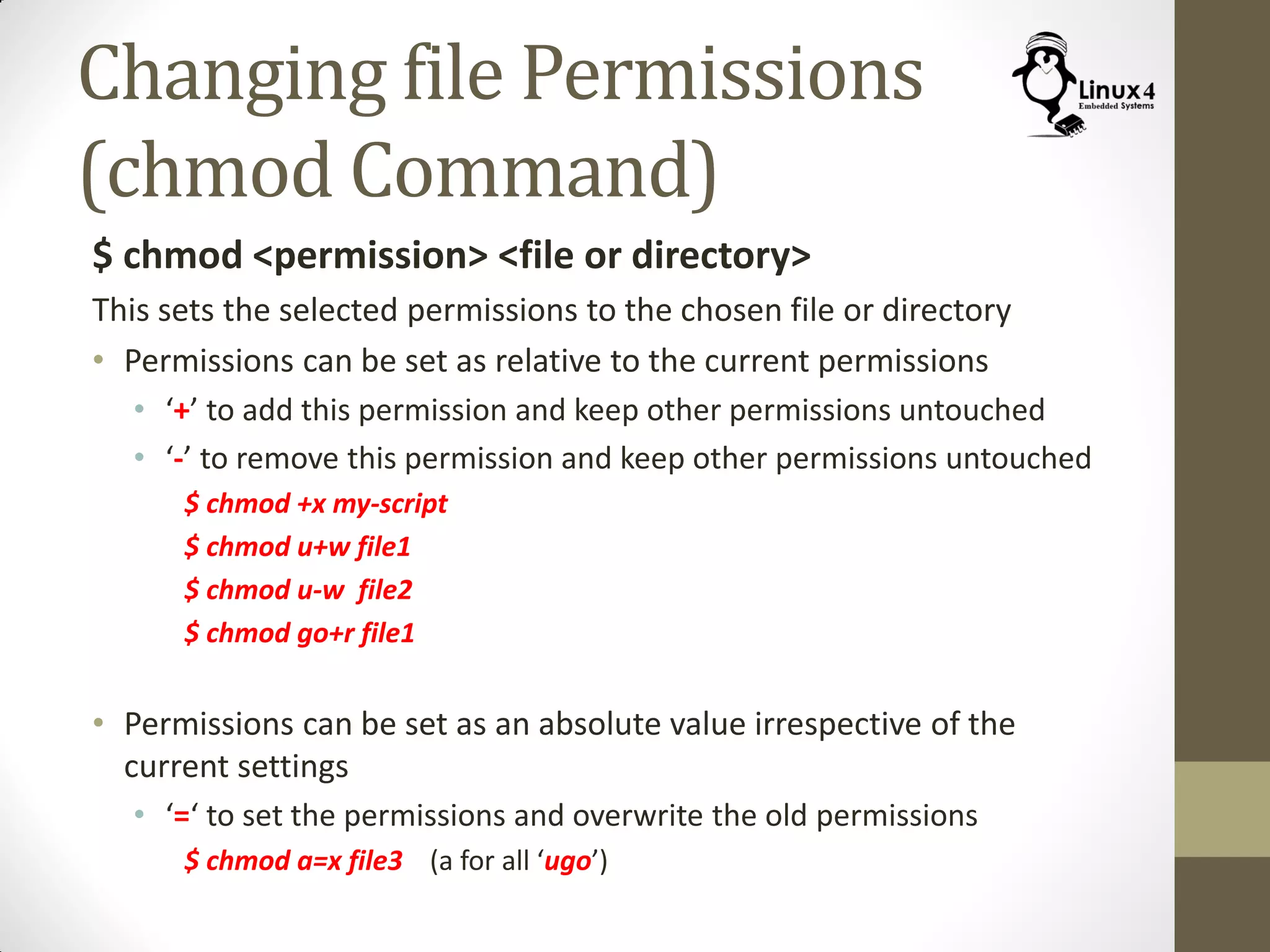
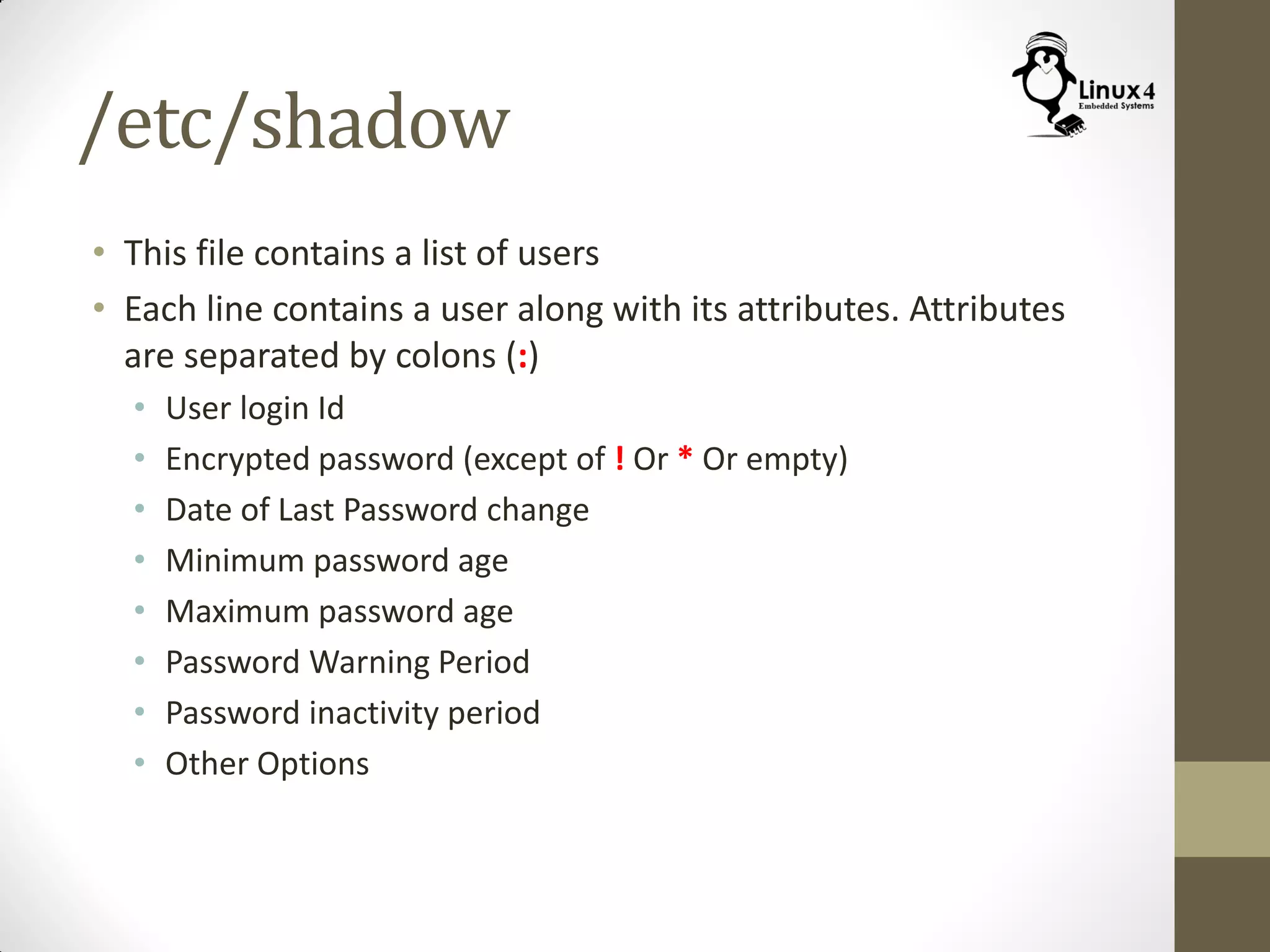
The document provides detailed information on Linux's multi-user system capabilities, highlighting user and permissions management. It explains Linux's structure for user identification, file ownership, and access rights, detailing commands for changing permissions, managing users and groups, and understanding special permission features. Additionally, it covers configuration files related to user and group data, and commands to add, delete, or switch users.