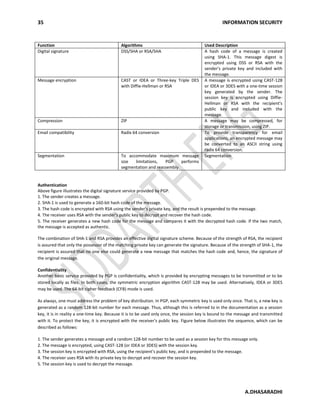
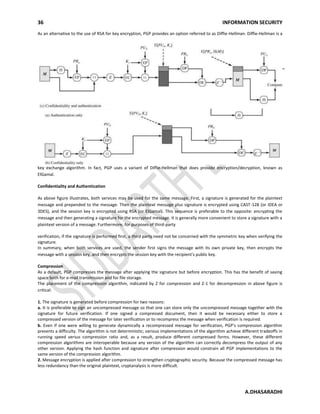
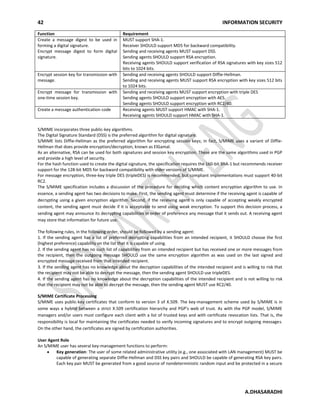
PGP (Pretty Good Privacy) is encryption software that allows users to securely exchange messages and files electronically. It was created by Phil Zimmermann and provides both confidentiality of messages through encryption and authentication of messages through digital signatures. PGP selects strong cryptographic algorithms, integrates them into an easy-to-use application, and makes the software freely available. It has grown popular due to its wide availability across different platforms, use of secure encryption algorithms, broad applicability, and development outside of government control. PGP provides services like encryption, digital signatures, compression, encoding messages for email compatibility, and segmentation of large messages.