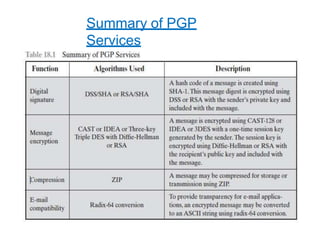
PGP (Pretty Good Privacy) is an open-source email encryption software that provides authentication, confidentiality, compression, and compatibility with email systems. It uses public-key encryption for authentication and symmetric-key encryption for confidentiality. PGP uses digital signatures for authentication by encrypting a hash of the message with the sender's private key. For confidentiality, it encrypts messages with a randomly generated symmetric session key, which is then encrypted with the recipient's public key.