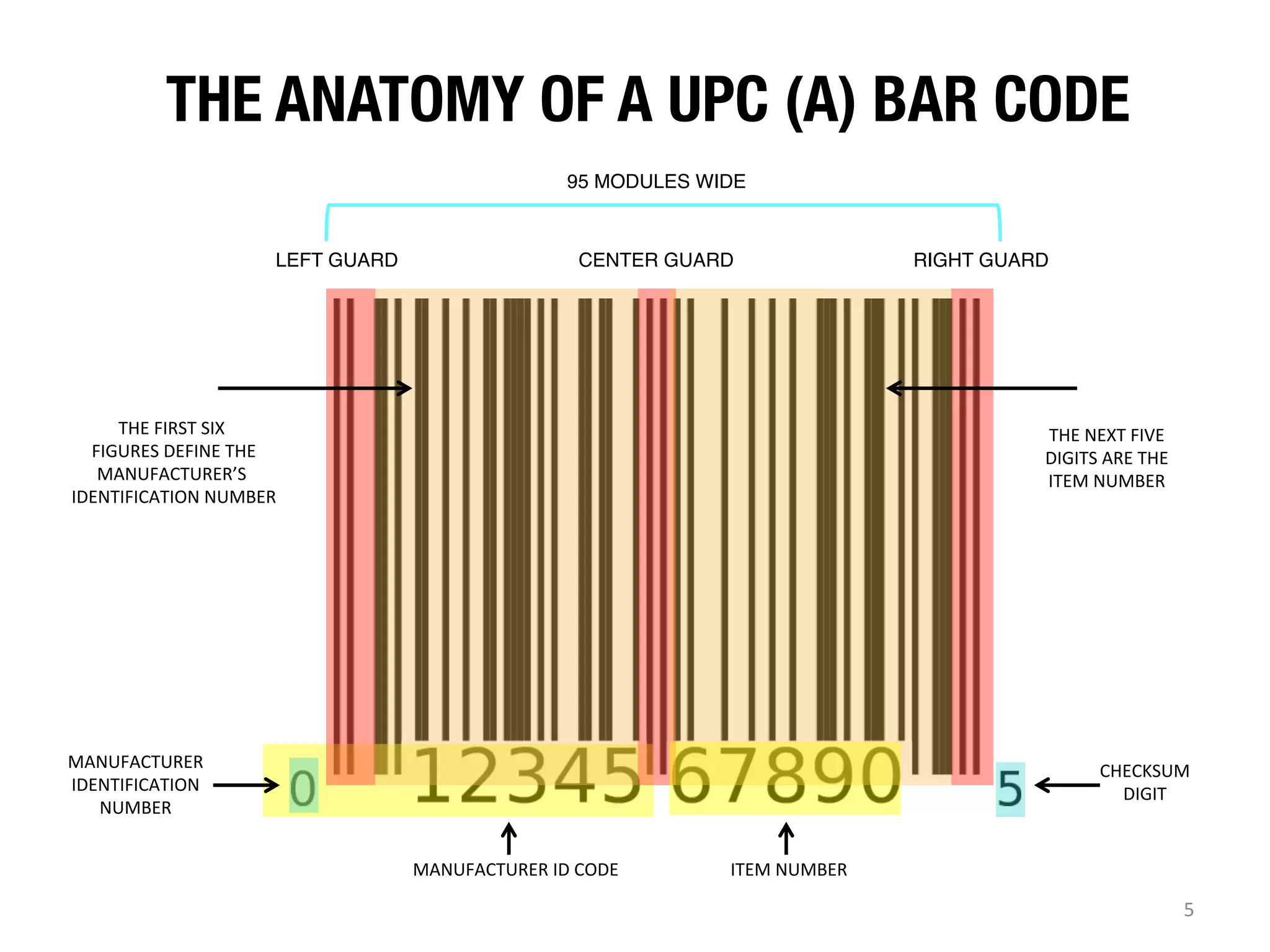
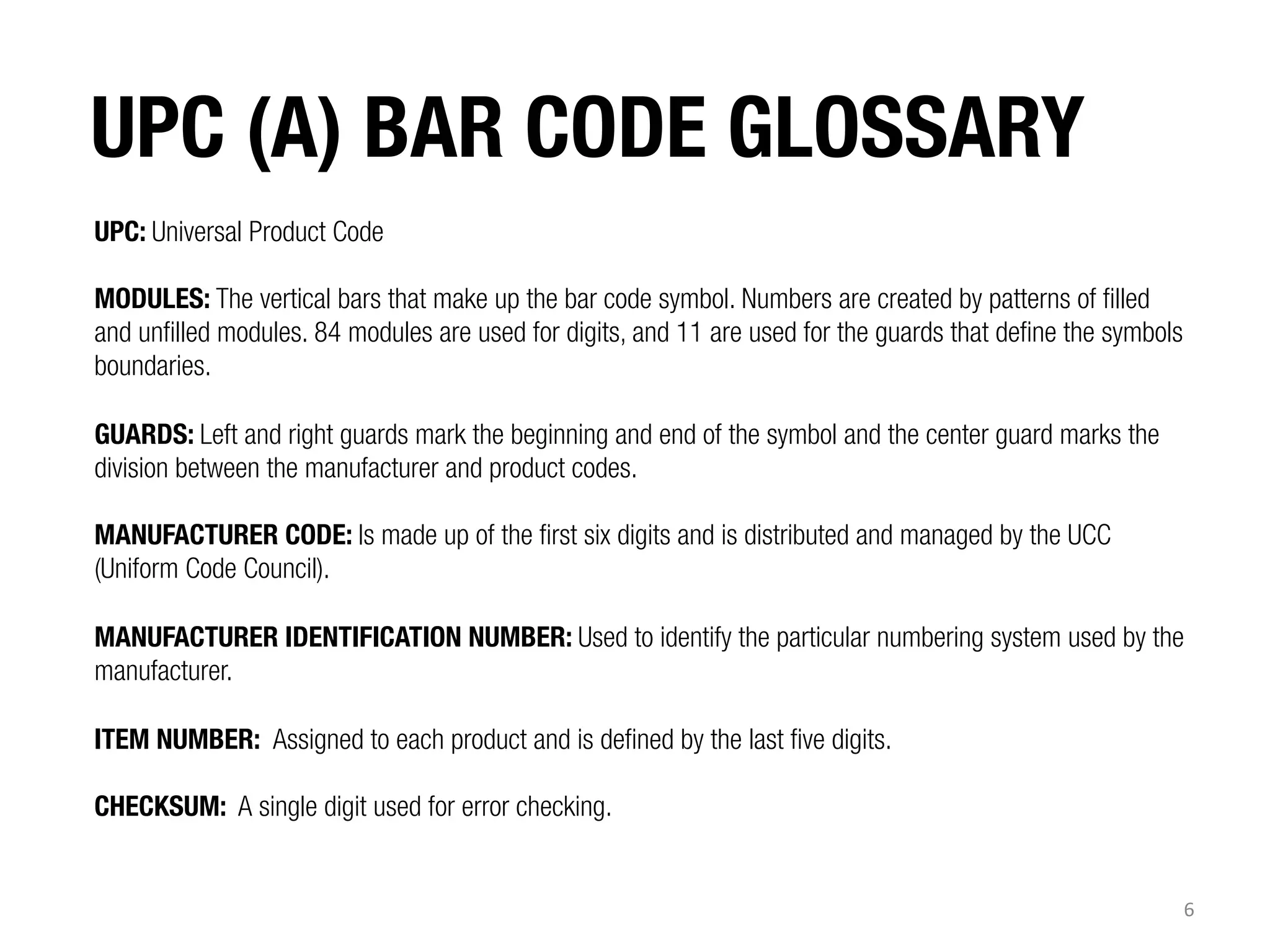
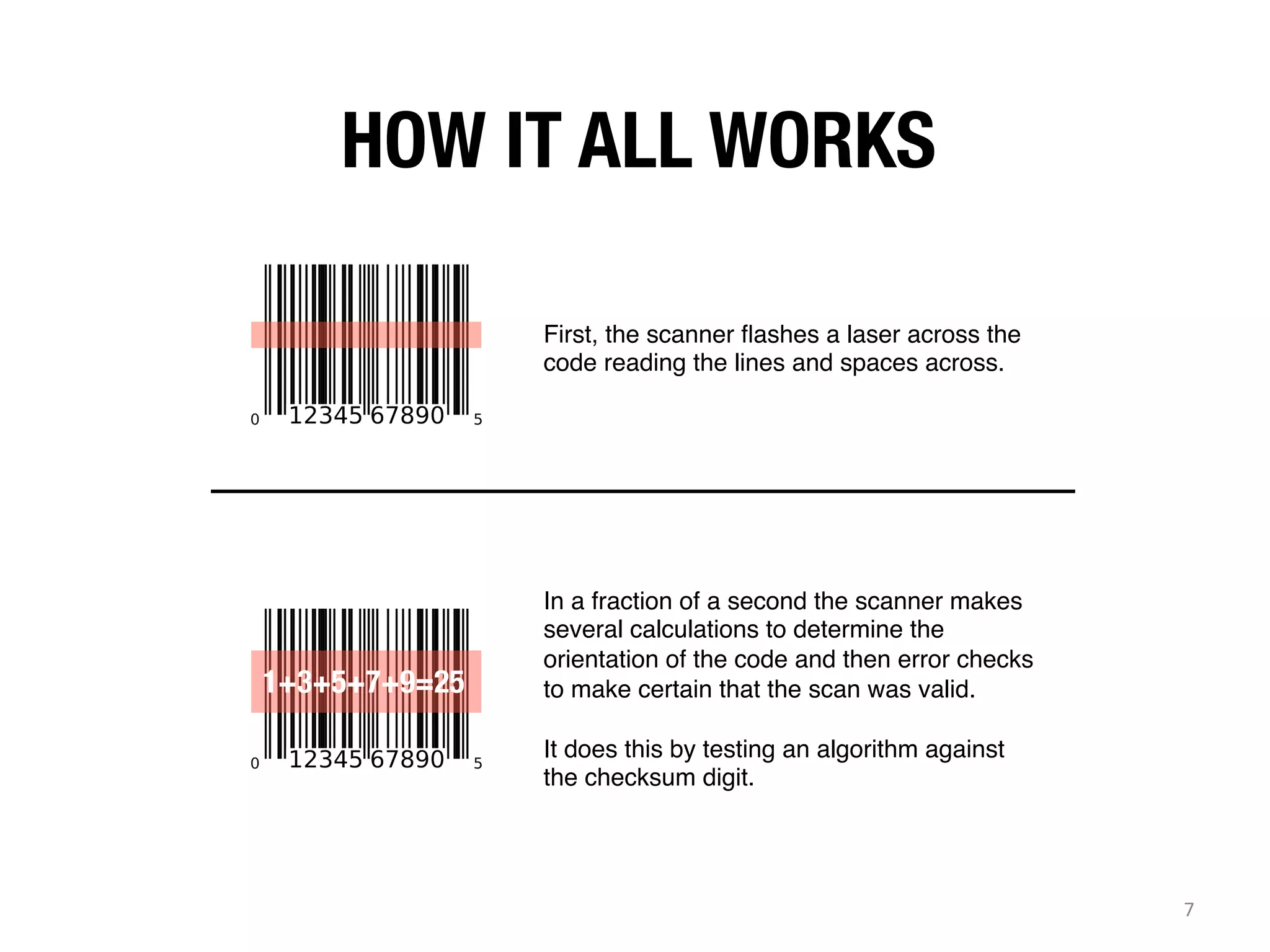
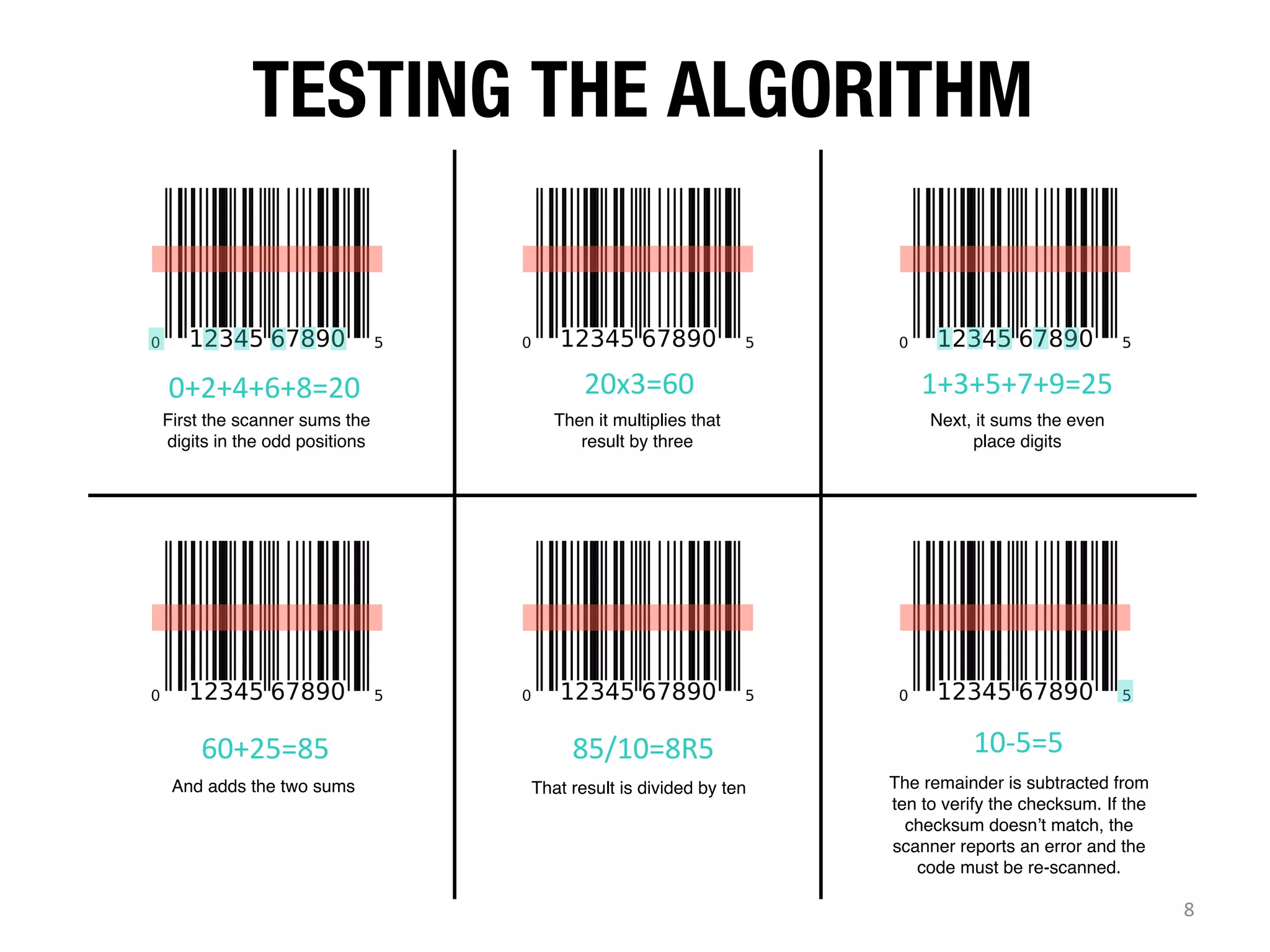
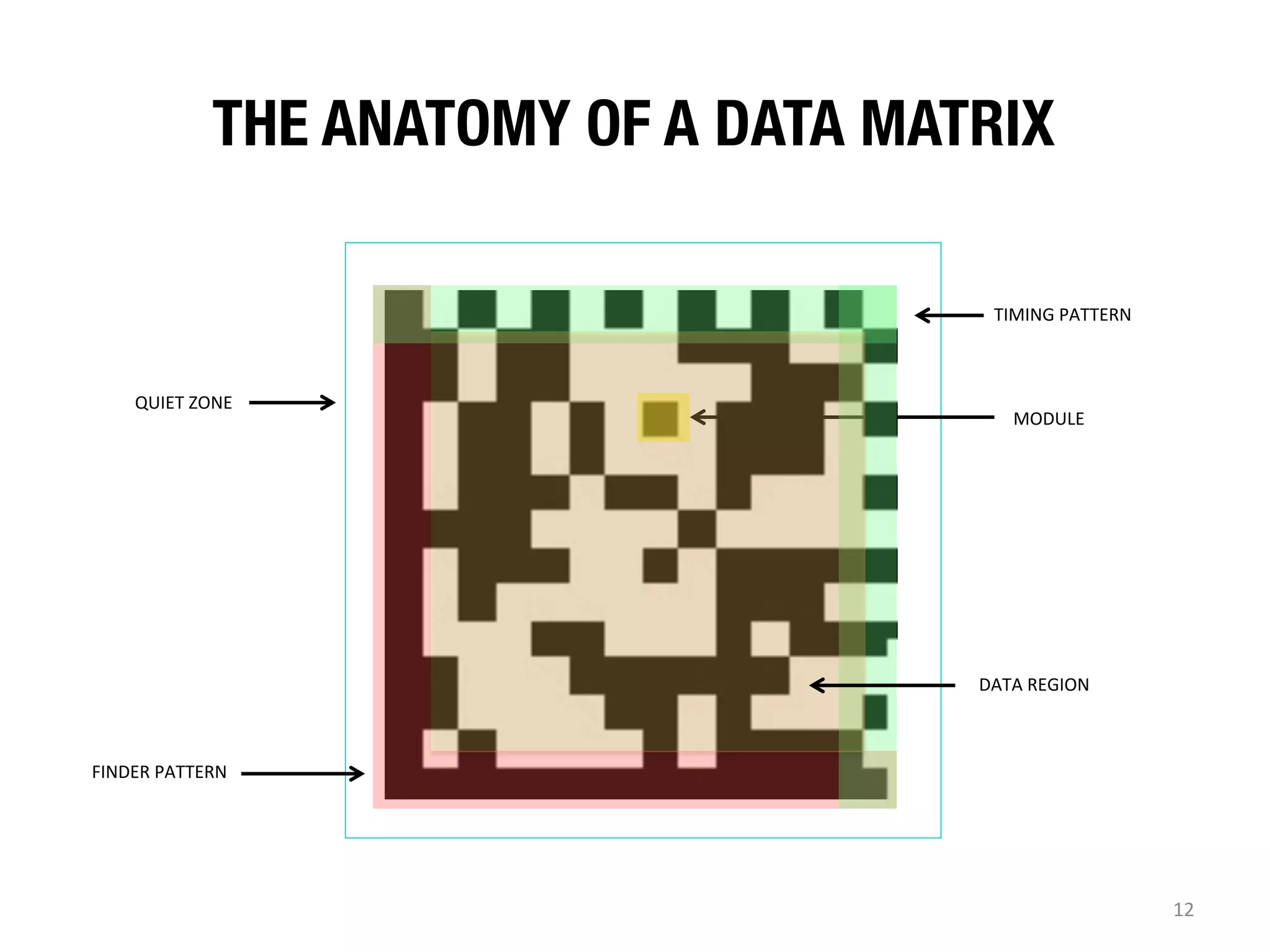
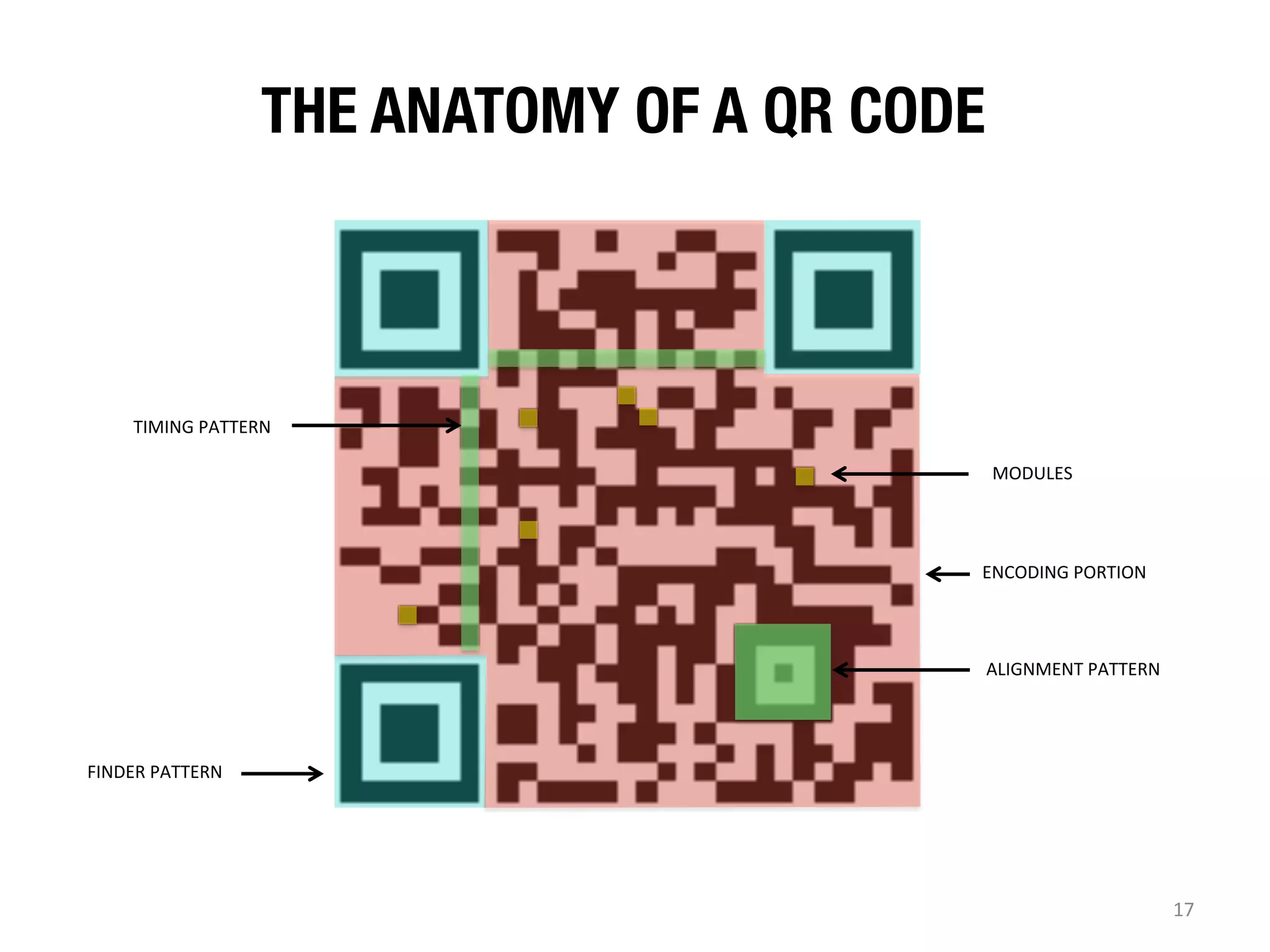
The document provides a comprehensive overview of barcode technology, focusing on various types including UPC, QR codes, and data matrix codes. It explains their anatomy, common uses, and the algorithms behind their functionality, emphasizing efficiency and error correction capabilities. Additionally, it touches on how these codes bridge physical and digital realms in businesses, particularly in sectors like healthcare and retail.