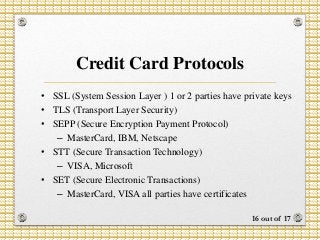
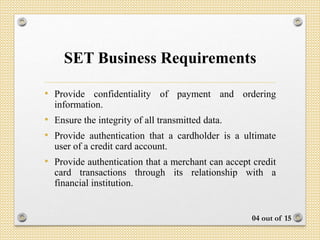
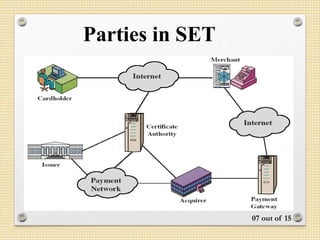
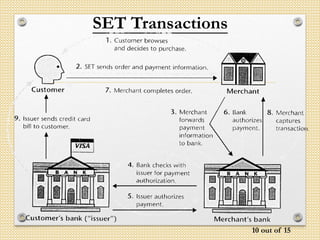
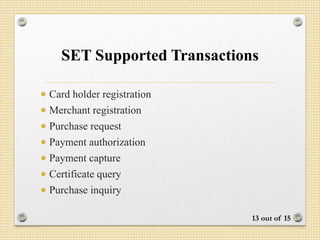
The document outlines the Secure Electronic Transaction (SET) protocol developed to ensure the security of credit card transactions over the internet, emphasizing confidentiality, integrity, and authentication. It describes the technical requirements, parties involved, dual signature operations, and various supporting technologies and transactions associated with SET. Additionally, the document mentions the importance of compliance with best security practices and interoperability among software providers.




![Dual Signature Operation
The operation for dual signature is as follows:
Take the hash (SHA-1) of the payment and order information.
These two hash values are concatenated [H(PI) || H(OI)] and
then the result is hashed.
Customer encrypts the final hash with a private key
creating the dual signature.
DS = EKRC [ H(H(PI) || H(OI)) ]
14 out of 17](https://image.slidesharecdn.com/set315131015-170411151311/85/Secure-Electronic-Transaction-14-320.jpg)