This document presents the findings of a study that developed a machine learning model to predict whether a person has COVID-19 based on their symptoms. It describes building neural network and other models using a dataset of symptoms from COVID-19 patients. The models were tested using various validation techniques, with the neural network achieving over 99% accuracy. Future work proposed taking additional clinical data to improve accuracy and developing a real-time online system to demonstrate the prediction model.


![Coronavirus & Prevention
“Coronavirus Disease- 2019”, is a respiratory illness caused by the
severe acute respiratory syndrome coronavirus-2 (SARS-CoV-2).
● First reported to affect human life in Wuhan City, in the
Hubei province of China in December 2019
● Later, spread like wildfire throughout the rest of the world,
marking its presence in 235 countries & independent
territories with confirmed death of 9,67,164 [1]
● Immediate Countermeasures are highly need to curb this
catastrophic effects
Algorithms
That Can Be Used To Solve This Problem
● Similarity Based Algorithm
● Machine Learning Algorithm
● Deep Learning Algorithm
Introduction
4
Corona Prediction from Symptoms](https://image.slidesharecdn.com/coronapredictionfromsymptomsv1-210802184743/85/Corona-prediction-from-symptoms-v1-4-4-320.jpg)
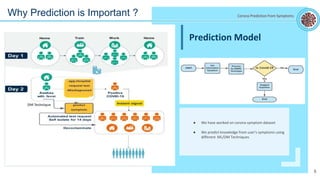
![State of the Art
State-of-the-art (SoTA) is a step to demonstrate the novelty of your
research results.
● Less work is being done on and predicting using text data.
● The major problem in the identification of COVID-19 is
detection and diagnosis.
● Different prediction models are built using machine learning
algorithms
Recent Studies on COVID Data
Data Types Algorithm Findings
Blood test report and
symptoms
CNN, LR Accuracy:
CNN (77%), LR (71%)
Based on age group [24] Random Forest Regressor
Random Forest Classifier
Accuracy: 96.6%
CT images [22] Neural Network Accuracy: 93.9%
Textual clinical data [23] Naïve Bayesian
Classification
Accuracy: 96.2%
Precision: 94%
Recall: 96%
7
Corona Prediction from Symptoms](https://image.slidesharecdn.com/coronapredictionfromsymptomsv1-210802184743/85/Corona-prediction-from-symptoms-v1-4-7-320.jpg)





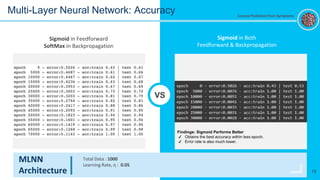
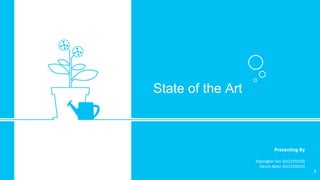
![21
MLNN
Architecture
Total Data : 30,000
Learning Rate, η : 0.0015 instead of 0.05
Activation Function : Sigmoid in Both Feedforward & Backpropagation
MLNN: Larger Dataset with Tuned Learning Rate
Accuracy Predicted Result
Input [0, 0, 0, 0, 0, 0, 0, 0, 0] | Predicted: [0.]
Input [1, 1, 1, 1, 1, 1, 1, 1, 1] | Predicted: [100.]
Input [1, 0, 1, 1, 0, 0, 1, 1, 1] | Predicted: [99.84]
Input [1, 1, 1, 1, 1, 0, 1, 1, 1] | Predicted: [100.]
Input [1, 1, 1, 0, 0, 0, 0, 0, 1] | Predicted: [0.57]
epoch 0 - error:0.5010 - acc:train 0.50 | test 0.50
epoch 5000 - error:0.0082 - acc:train 1.00 | test 1.00
epoch 10000 - error:0.0057 - acc:train 1.00 | test 1.00
epoch 15000 - error:0.0046 - acc:train 1.00 | test 1.00
epoch 20000 - error:0.0040 - acc:train 1.00 | test 1.00
epoch 25000 - error:0.0036 - acc:train 1.00 | test 1.00
epoch 30000 - error:0.0032 - acc:train 1.00 | test 1.00
Corona Prediction from Symptoms](https://image.slidesharecdn.com/coronapredictionfromsymptomsv1-210802184743/85/Corona-prediction-from-symptoms-v1-4-20-320.jpg)
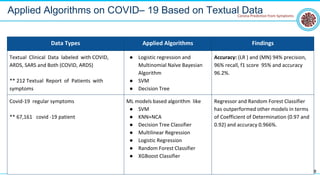
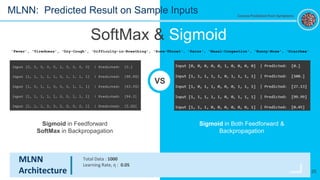
![Predicted result by
different algorithms.
Predicted Result
Input [0, 0, 0, 0, 0, 1, 0, 0, 0, 0] | Predicted: [0.]
Input [1, 1, 1, 1, 1, 0, 1, 1, 1, 1] | Predicted: [98.89]
Input [1, 0, 1, 1, 0, 0, 0, 1, 1, 1] | Predicted: [63.59]
Input [1, 1, 1, 1, 1, 0, 0, 1, 1, 1] | Predicted: [94.3]
Input [1, 1, 1, 0, 0, 0, 0, 0, 0, 1] | Predicted: [5.26]
Multi Layer Neural Network
Input [0, 0, 0, 0, 0, 1, 0, 0, 0, 0] | Predicted: [1]
Input [1, 1, 1, 1, 1, 0, 1, 1, 1, 1] | Predicted: [0]
Input [1, 0, 1, 1, 0, 0, 0, 1, 1, 1] | Predicted: [0]
Input [1, 1, 1, 1, 1, 0, 0, 1, 1, 1] | Predicted: [0]
Input [1, 1, 1, 0, 0, 0, 0, 0, 0, 1] | Predicted: [1]
Naïve Bayes Classifier (Multinomial)
Input [0, 0, 0, 0, 0, 1, 0, 0, 0, 0] | Predicted: [1.]
Input [1, 1, 1, 1, 1, 0, 1, 1, 1, 1] | Predicted: [0.]
Input [1, 0, 1, 1, 0, 0, 0, 1, 1, 1] | Predicted: [0.]
Input [1, 1, 1, 1, 1, 0, 0, 1, 1, 1] | Predicted: [0.]
Input [1, 1, 1, 0, 0, 0, 0, 0, 0, 1] | Predicted: [1.]
KNN (Regression)
Input [0, 0, 0, 0, 0, 1, 0, 0, 0, 0] | Predicted: [False]
Input [1, 1, 1, 1, 1, 0, 1, 1, 1, 1] | Predicted: [ True]
Input [1, 0, 1, 1, 0, 0, 0, 1, 1, 1] | Predicted: [ True]
Input [1, 1, 1, 1, 1, 0, 0, 1, 1, 1] | Predicted: [ True]
Input [1, 1, 1, 0, 0, 0, 0, 0, 0, 1] | Predicted: [False]
Linear Regression
22
'Fever', 'Tiredness', 'Dry-Cough', 'Difficulty-in-Breathing', 'Sore-Throat', 'Pains', 'Nasal-
Congestion', 'Runny-Nose', 'Diarrhea'
Predicted Results: Other Algorithms Corona Prediction from Symptoms](https://image.slidesharecdn.com/coronapredictionfromsymptomsv1-210802184743/85/Corona-prediction-from-symptoms-v1-4-21-320.jpg)
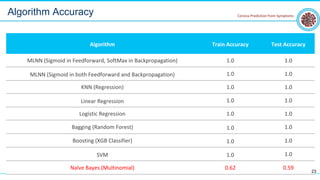
![2-Fold Cross Validation 5-Fold Cross Validation
Multi Layer Neural Network:
[0.9925, 0.995]
Naïve Bayesian Classifier
[0.6175, 0.63]
Multi Layer Neural Network:
[1.0, 0.99375, 0.98125, 0.99375, 1.0]
Naïve Bayesian Classifier
[0.5625, 0.6625, 0.64375, 0.66875, 0.5625]
Multi Layer Neural Network:
[1.0, 1.0, 1.0, 0.9875, 0.975, 0.9875, 1.0, 0.9875, 1.0, 1.0]
Naïve Bayesian Classifier
[0.6, 0.5, 0.6125, 0.6875, 0.625, 0.6625, 0.6875, 0.6375,
0.5875, 0.5375]
24
Validation: K-Fold Cross Validation
10-Fold Cross Validation
Corona Prediction from Symptoms](https://image.slidesharecdn.com/coronapredictionfromsymptomsv1-210802184743/85/Corona-prediction-from-symptoms-v1-4-23-320.jpg)
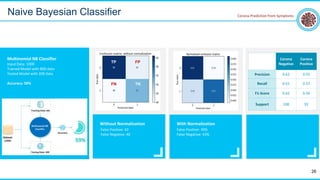
![2-Fold Cross Validation 5-Fold Cross Validation
[0.6175, 0.63]
Naïve Bayesian Classifier
[0.5625, 0.6625, 0.64375, 0.66875, 0.5625]
Validation: Jackknife Method
10-Fold Cross Validation
● Multi Layer Neural Network (MLNN)
● K-Nearest Neighbour (KNN)
● Support Vector Machine (SVM)
● Linear Regression (LR)
● Logistic Regression
● Random Forest (RM)
● XGB Classifier
Algorithms
25
Naive
Bayesian
Classifier
Corona Prediction from Symptoms
● Validation Applied for 1000
data
● All Algorithms except NB
provides same validation result](https://image.slidesharecdn.com/coronapredictionfromsymptomsv1-210802184743/85/Corona-prediction-from-symptoms-v1-4-24-320.jpg)


![[1] N. Chen et al., “Epidemiological and clinical characteristics of 99 cases of 2019 novel coronavirus pneumonia in Wuhan, China: a descriptive study,” Lancet, vol. 395, no. 10223, pp. 507–513, 2020, doi: 10.1016/S0140-
6736(20)30211-7.
[2] S. J. Fong, N. Dey, and J. Chaki, “Artificial Intelligence for Coronavirus Outbreak,” An Introd. to COVID-19, pp. 1–22, 2021, doi: 10.1007/978-981-15-5936-5.
[3] C. Menni et al., “Real-time tracking of self-reported symptoms to predict potential COVID-19,” Nat. Med., vol. 26, no. 7, pp. 1037–1040, 2020, doi: 10.1038/s41591-020-0916-2.
[4] Y. Lecun, Y. Bengio, and G. Hinton, “Deep learning,” Nature, vol. 521, no. 7553, pp. 436–444, 2015, doi: 10.1038/nature14539.
[5] V. Chamola, V. Hassija, V. Gupta, and M. Guizani, “A Comprehensive Review of the COVID-19 Pandemic and the Role of IoT, Drones, AI, Blockchain, and 5G in Managing its Impact,” IEEE Access, vol. 8, no. April, pp. 90225–
90265, 2020, doi: 10.1109/ACCESS.2020.2992341.
[6] X. Zhang, J. Kim, R. E. Patzer, S. R. Pitts, A. Patzer, and J. D. Schrager, “Prediction of emergency department hospital admission based on natural language processing and neural networks,” Methods Inf. Med., vol. 56, no. 5,
pp. 377–389, 2017, doi: 10.3414/ME17-01-0024.
[7] W. Naudé, “Artificial intelligence vs COVID-19: limitations, constraints and pitfalls,” AI Soc., vol. 35, no. 3, pp. 761–765, 2020, doi: 10.1007/s00146-020-00978-0.
[8] S. Lalmuanawma, J. Hussain, and L. Chhakchhuak, “Applications of machine learning and artificial intelligence for Covid-19 (SARS-CoV-2) pandemic: A review,” Chaos, Solitons and Fractals, vol. 139, 2020, doi:
10.1016/j.chaos.2020.110059.
[9] M. M. Ahamad et al., “A machine learning model to identify early stage symptoms of SARS-Cov-2 infected patients,” Expert Syst. Appl., vol. 160, p. 113661, 2020, doi: 10.1016/j.eswa.2020.113661.
[10] M. E. H. Chowdhury et al., “Can AI Help in Screening Viral and COVID-19 Pneumonia?,” IEEE Access, vol. 8, pp. 132665–132676, 2020, doi: 10.1109/ACCESS.2020.3010287.
[11] E. J. Chow et al., “Symptom Screening at Illness Onset of Health Care Personnel with SARS-CoV-2 Infection in King County, Washington,” JAMA - J. Am. Med. Assoc., vol. 323, no. 20, pp. 2087–2089, 2020, doi:
10.1001/jama.2020.6637.
[12] D. Wang et al., “Clinical Characteristics of 138 Hospitalized Patients with 2019 Novel Coronavirus-Infected Pneumonia in Wuhan, China,” JAMA - J. Am. Med. Assoc., vol. 323, no. 11, pp. 1061–1069, 2020, doi:
10.1001/jama.2020.1585.
[13] H. Swapnarekha, H. S. Behera, J. Nayak, and B. Naik, “Role of intelligent computing in COVID-19 prognosis: A state-of-the-art review,” Chaos, Solitons and Fractals, vol. 138, p. 109947, 2020, doi:
10.1016/j.chaos.2020.109947.
[14] D. A. Drew et al., “Rapid implementation of mobile technology for real-time epidemiology of COVID-19,” Science (80-. )., vol. 368, no. 6497, pp. 1362–1367, 2020, doi: 10.1126/science.abc0473.
[15] A. Bansal, R. P. Padappayil, C. Garg, A. Singal, M. Gupta, and A. Klein, “Utility of Artificial Intelligence Amidst the COVID 19 Pandemic: A Review,” J. Med. Syst., vol. 44, no. 9, pp. 19–24, 2020, doi: 10.1007/s10916-020-
01617-3.
[16] J. S. Obeid, M. Davis, M. Turner, S. M. Meystre, P. M. Heider, and L. A. Lenert, “An AI approach to COVID-19 infection risk assessment in virtual visits: a case report,” J. Am. Med. Informatics Assoc., vol. 0, no. May, pp. 1–5,
2020, doi: 10.1093/jamia/ocaa105.
[17] Q. V. Pham, D. C. Nguyen, T. Huynh-The, W. J. Hwang, and P. N. Pathirana, “Artificial Intelligence (AI) and Big Data for Coronavirus (COVID-19) Pandemic: A Survey on the State-of-the-Arts,” IEEE Access, vol. 8, no. Cdc, pp.
130820–130839, 2020, doi: 10.1109/ACCESS.2020.3009328.
[18] C. Huang et al., “Clinical features of patients infected with 2019 novel coronavirus in Wuhan, China,” Lancet, vol. 395, no. 10223, pp. 497–506, 2020, doi: 10.1016/S0140-6736(20)30183-5.
[19] H. Jelodar, Y. Wang, R. Orji, and H. Huang, “Deep Sentiment Classification and Topic Discovery on Novel Coronavirus or COVID-19 Online Discussions: NLP Using LSTM Recurrent Neural Network Approach,” IEEE J. Biomed.
Heal. Informatics, vol. 2194, no. c, pp. 1–1, 2020, doi: 10.1109/jbhi.2020.3001216.
[20] M. Jamshidi et al., “Artificial Intelligence and COVID-19: Deep Learning Approaches for Diagnosis and Treatment,” IEEE Access, vol. 8, no. December 2019, pp. 109581–109595, 2020, doi: 10.1109/ACCESS.2020.3001973.
[21] X. Jiang et al., “Towards an artificial intelligence framework for data-driven prediction of coronavirus clinical severity,” 2020.
[22] H. Kang et al., “Diagnosis of Coronavirus Disease 2019 (COVID-19) with Structured Latent Multi-View Representation Learning,” IEEE Trans. Med. Imaging, vol. 39, no. 8, pp. 2606–2614, 2020, doi:
10.1109/TMI.2020.2992546.
[23] A. M. U. D. Khanday, S. T. Rabani, Q. R. Khan, N. Rouf, and M. Mohi Ud Din, “Machine learning based approaches for detecting COVID-19 using clinical text data,” Int. J. Inf. Technol., vol. 12, no. 3, pp. 731–739, 2020, doi:
10.1007/s41870-020-00495-9.
[24] J. Wu et al., “Rapid and accurate identification of COVID-19 infection through machine learning based on clinical available blood test results,” 2020, doi: 10.1101/2020.04.02.20051136.
[25] “Coronavirus disease (COVID-19) Pandemic.” [Online]. Available:https://www.who.int/emergencies/diseases/novel-coronavirus-2019
32
References Corona Prediction from Symptoms](https://image.slidesharecdn.com/coronapredictionfromsymptomsv1-210802184743/85/Corona-prediction-from-symptoms-v1-4-31-320.jpg)
