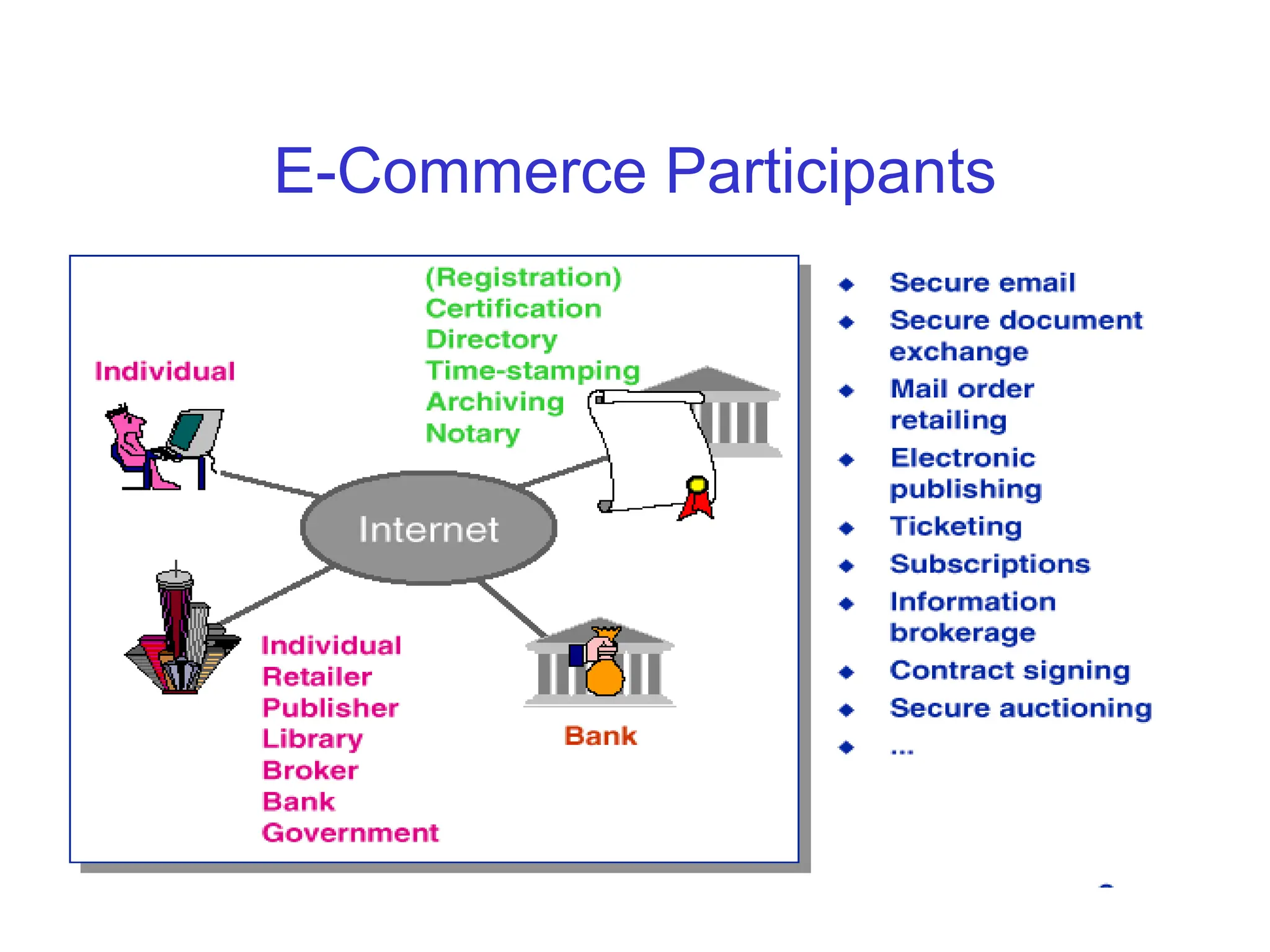
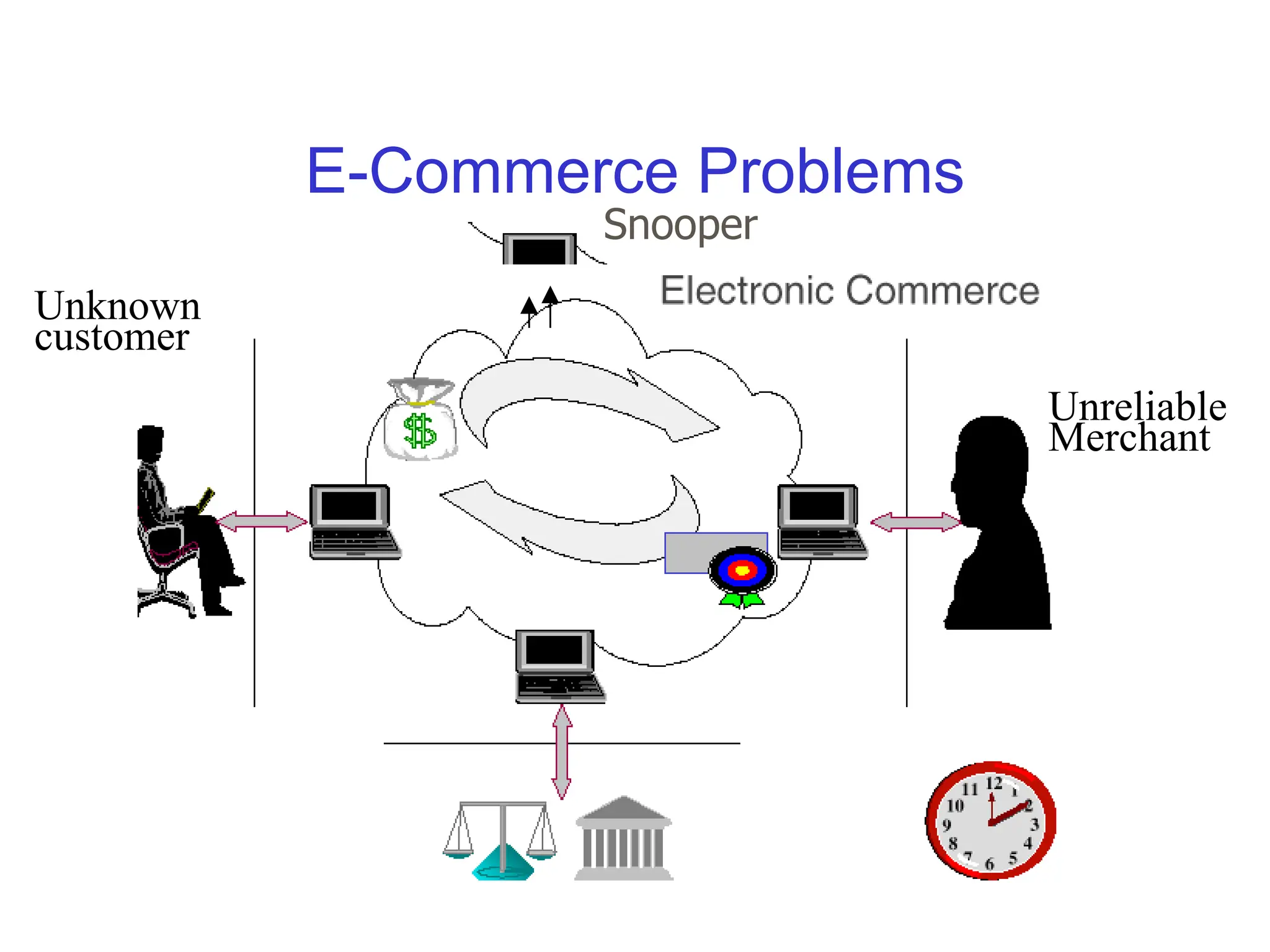
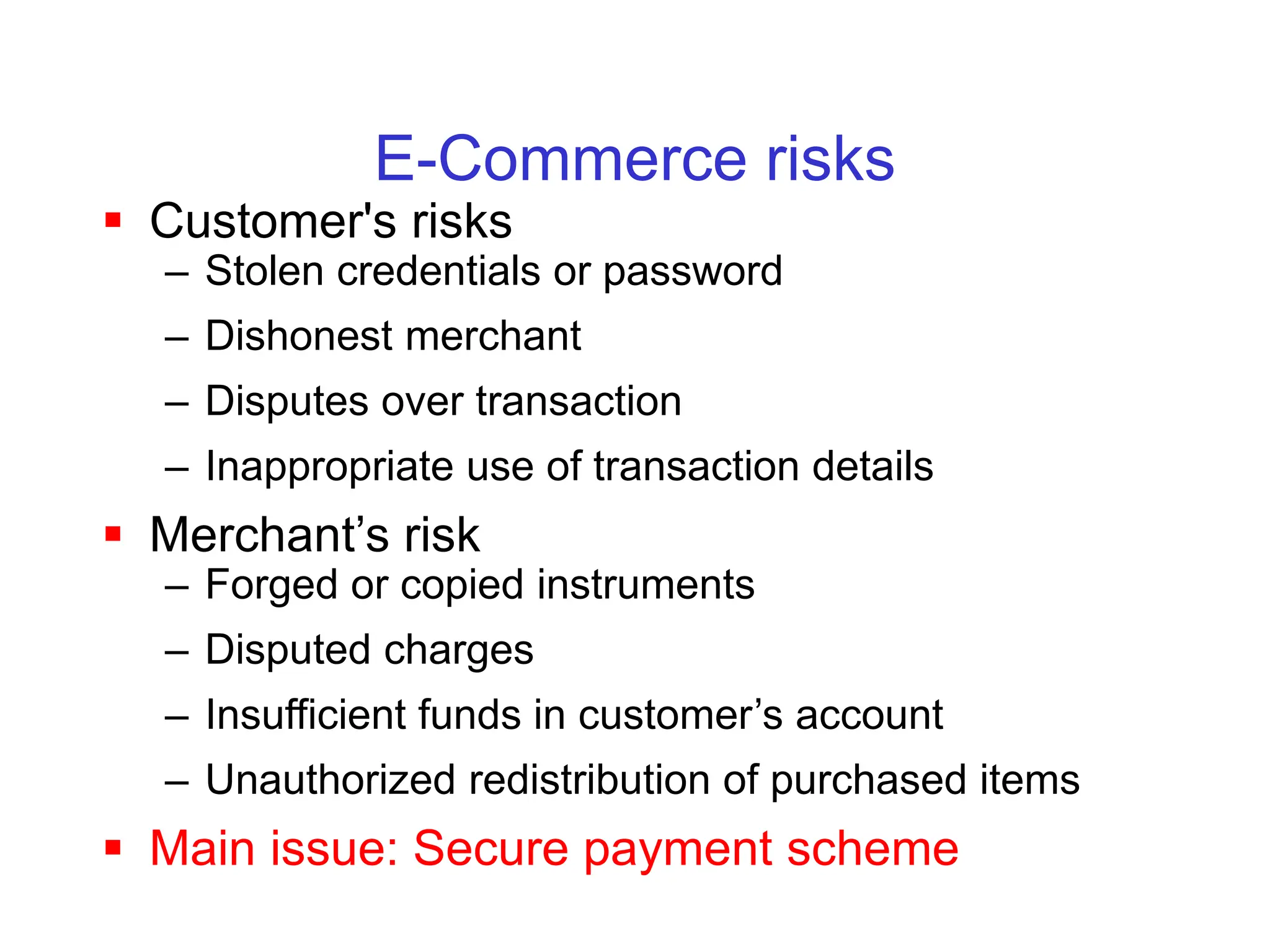
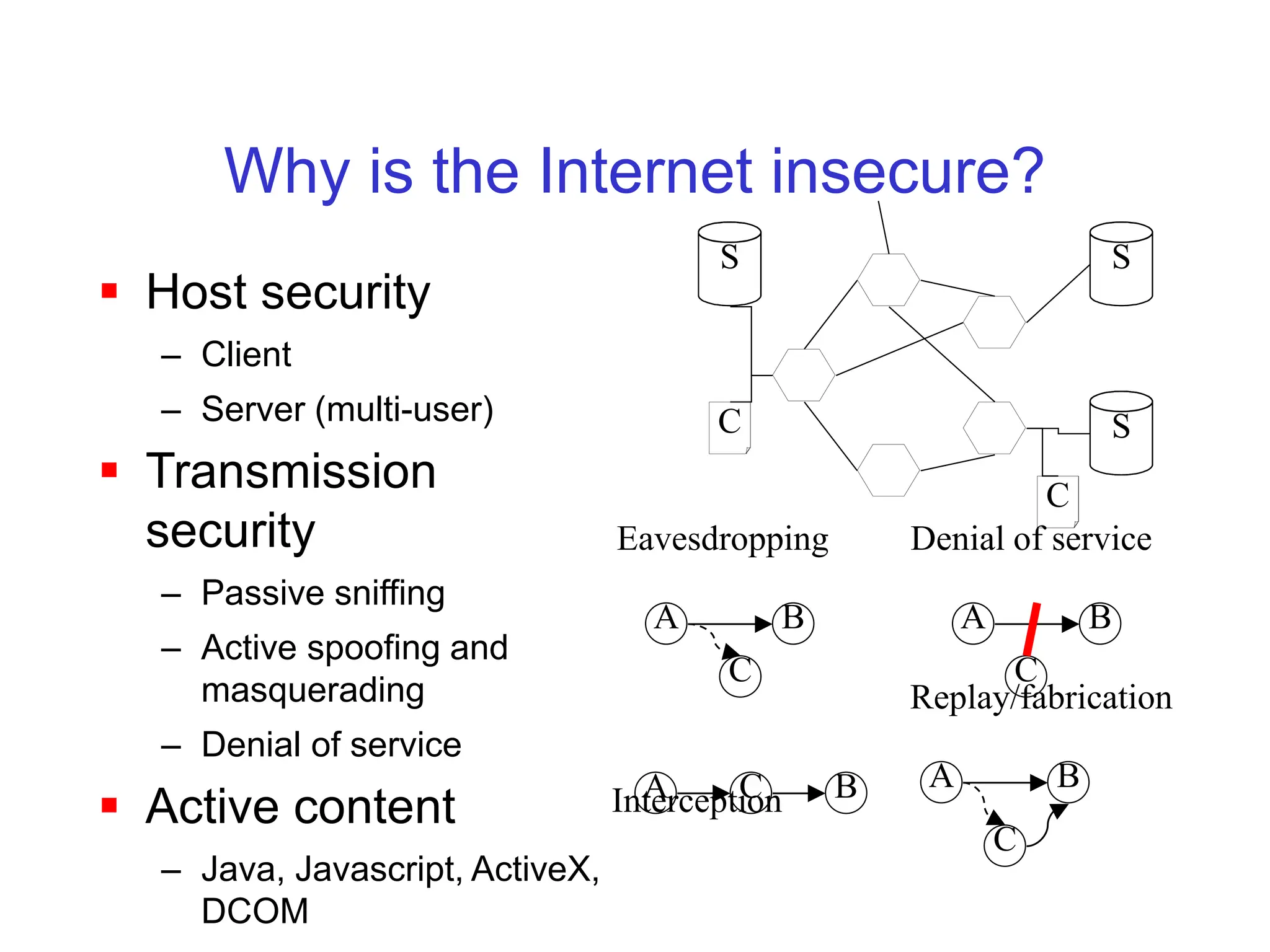
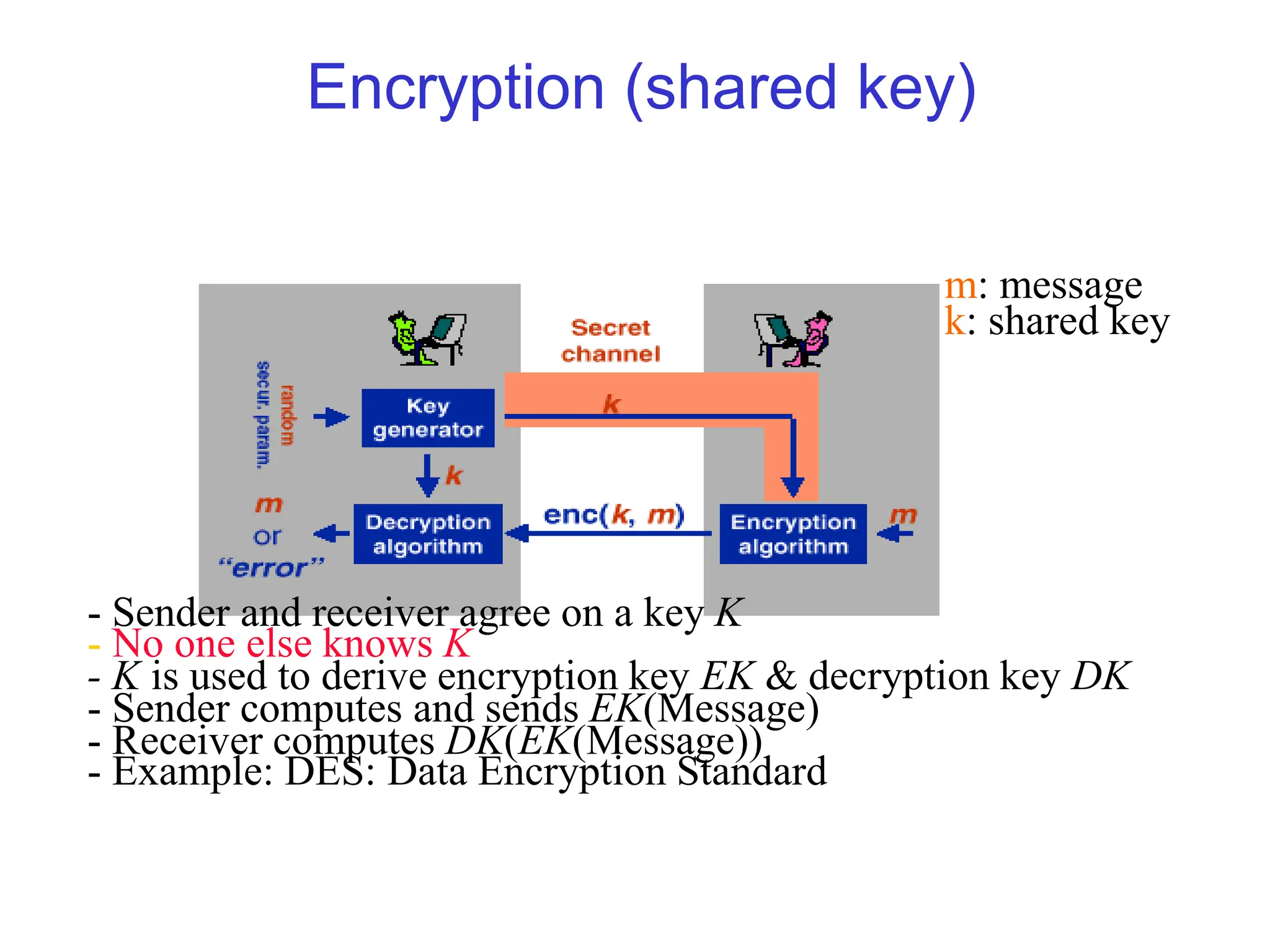
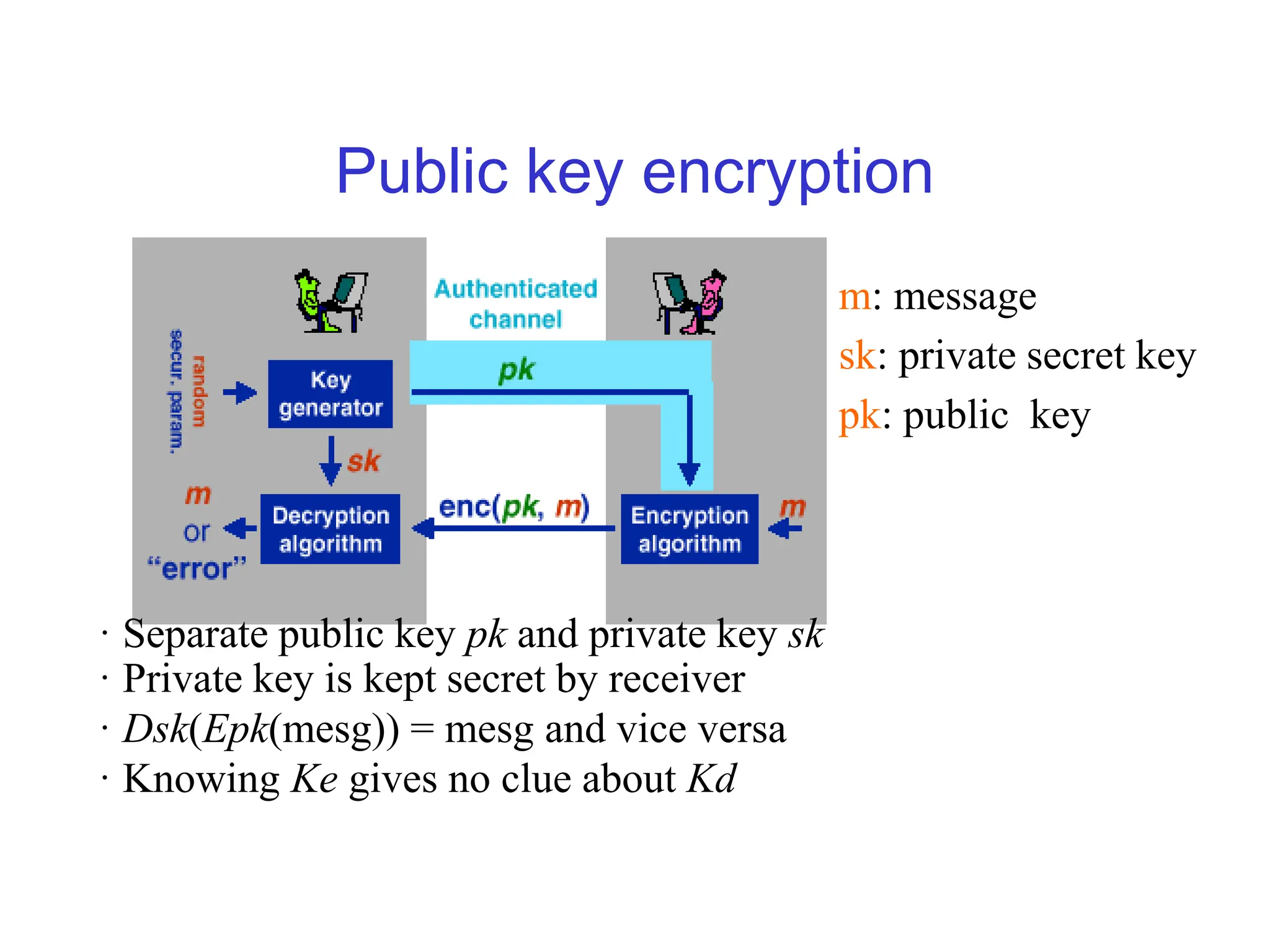
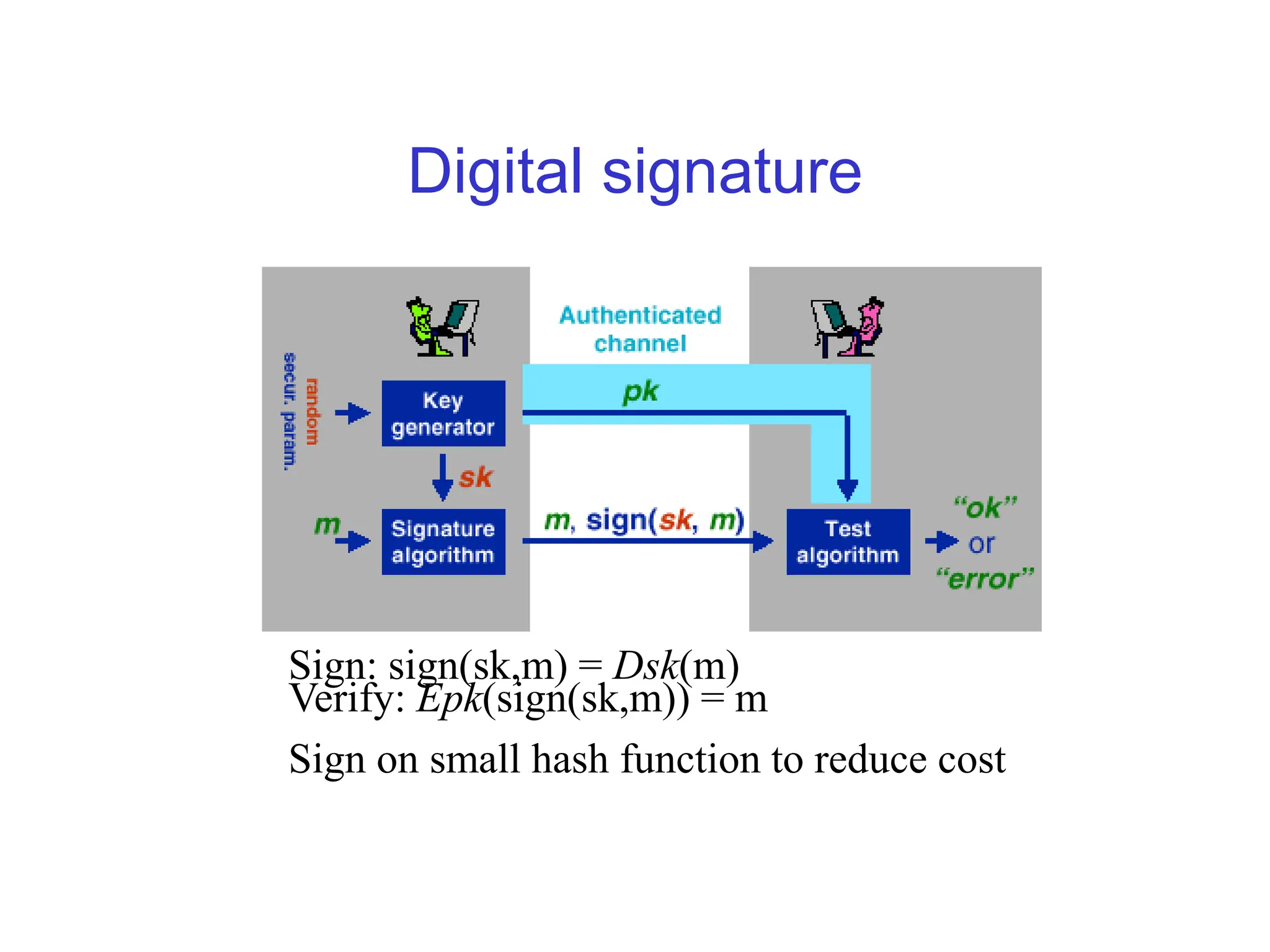
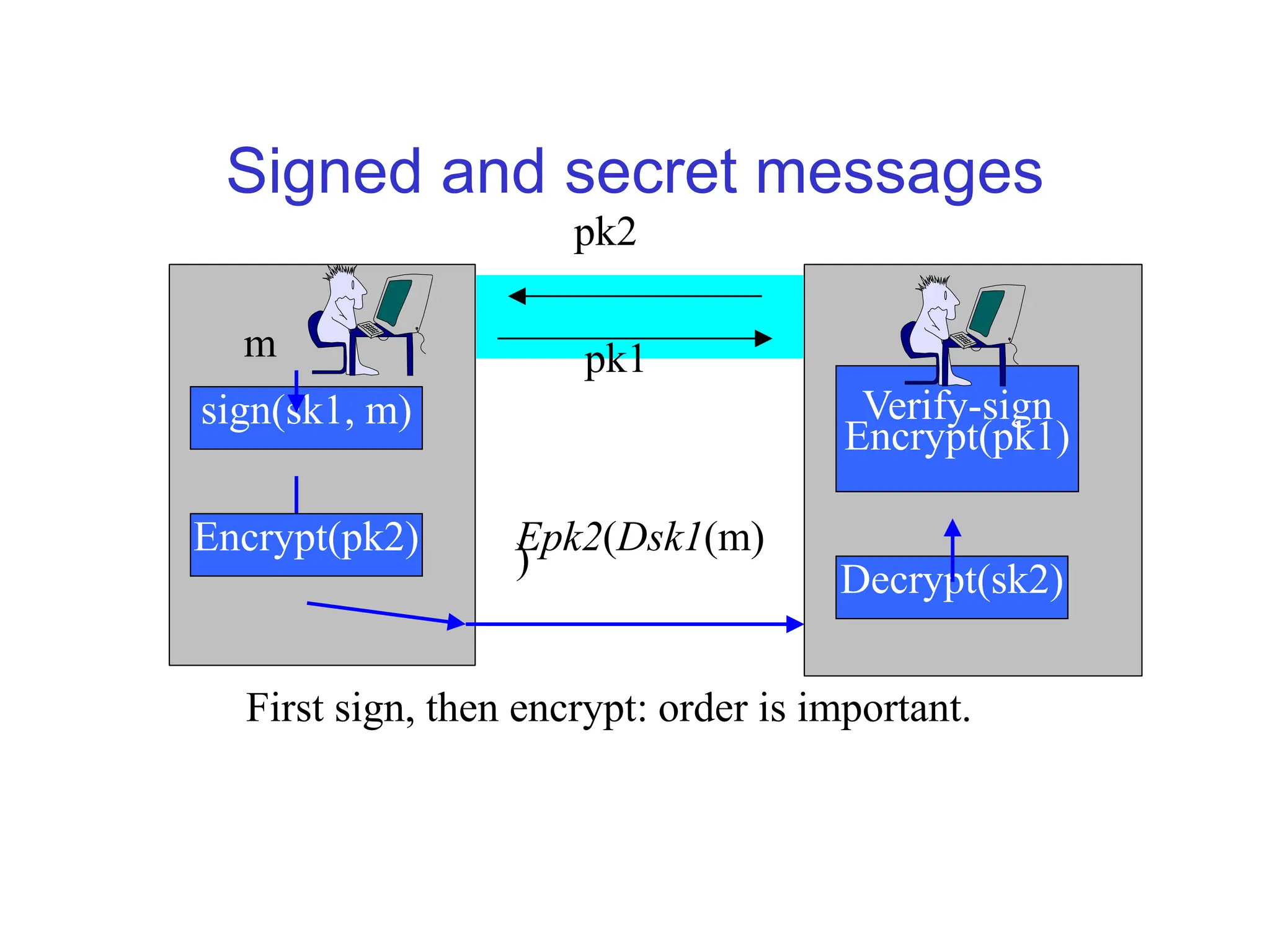
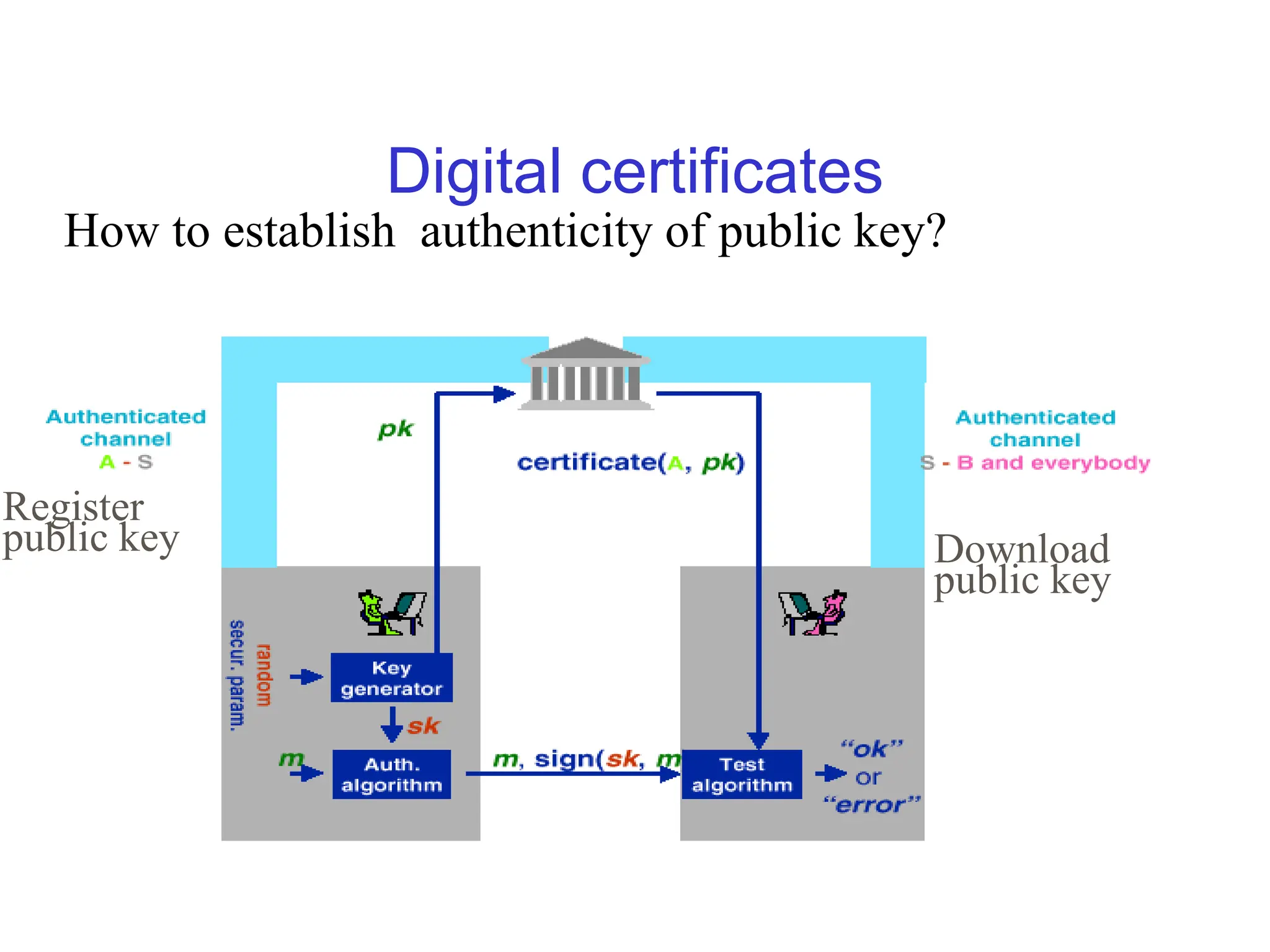
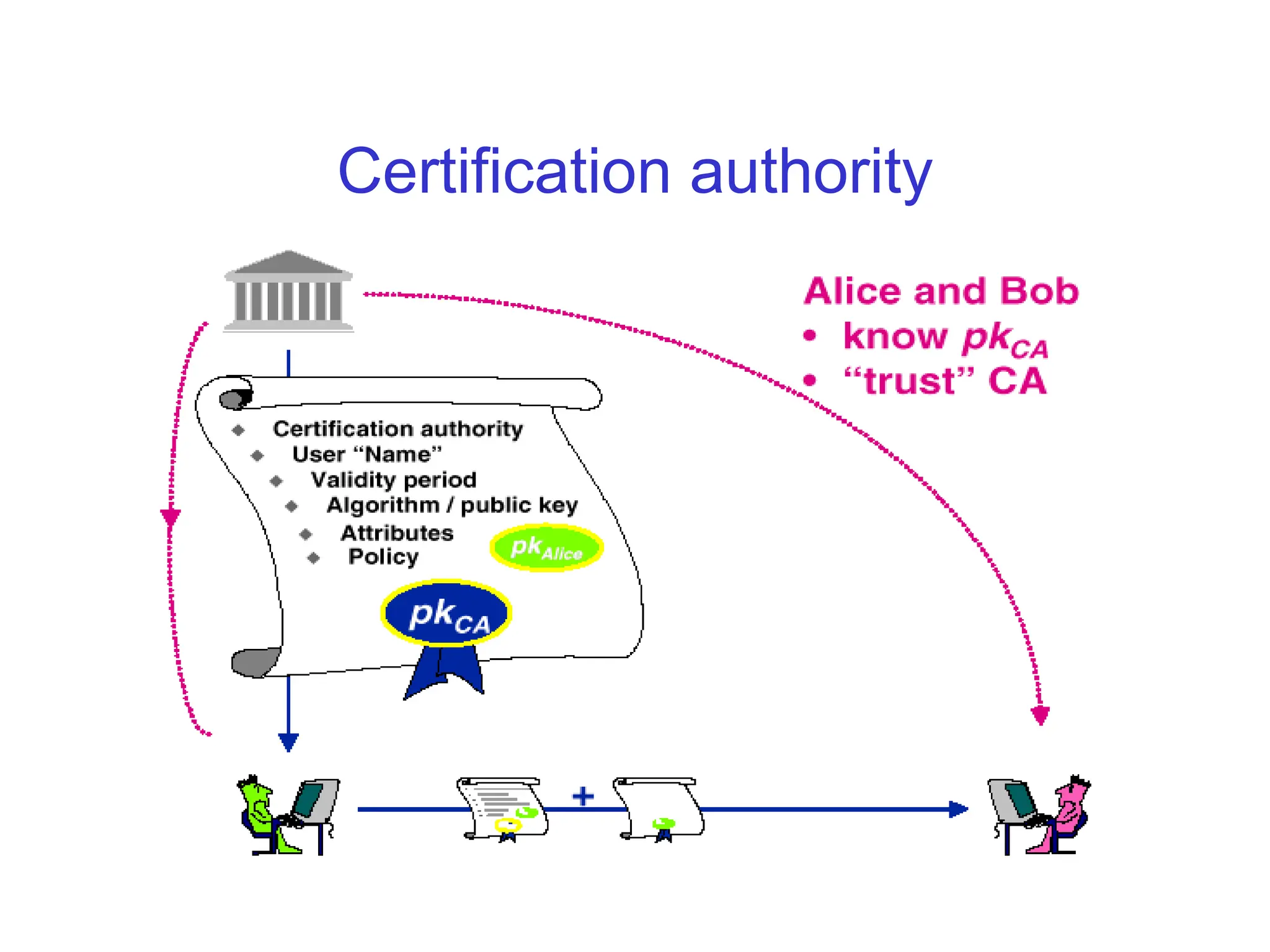
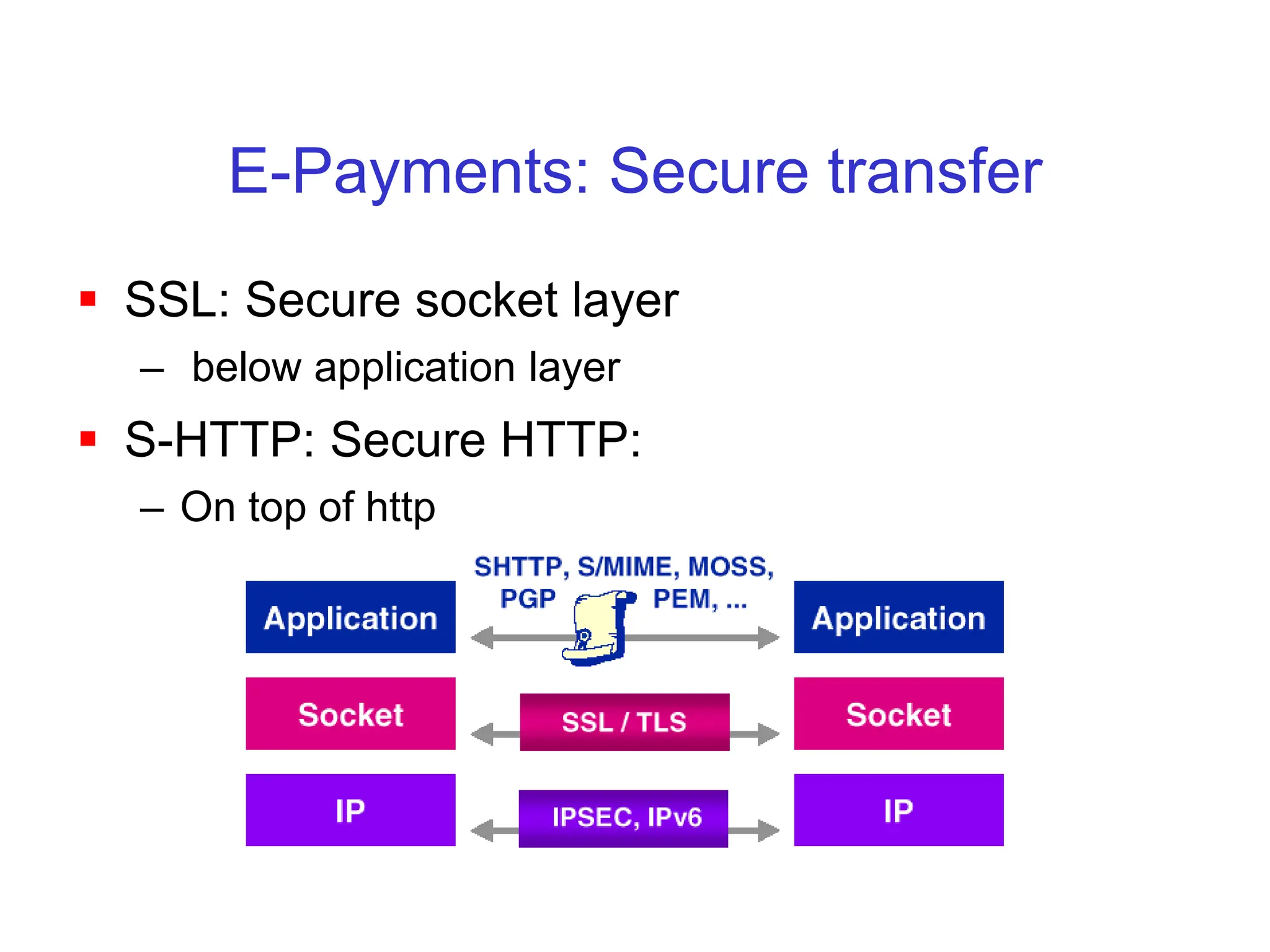
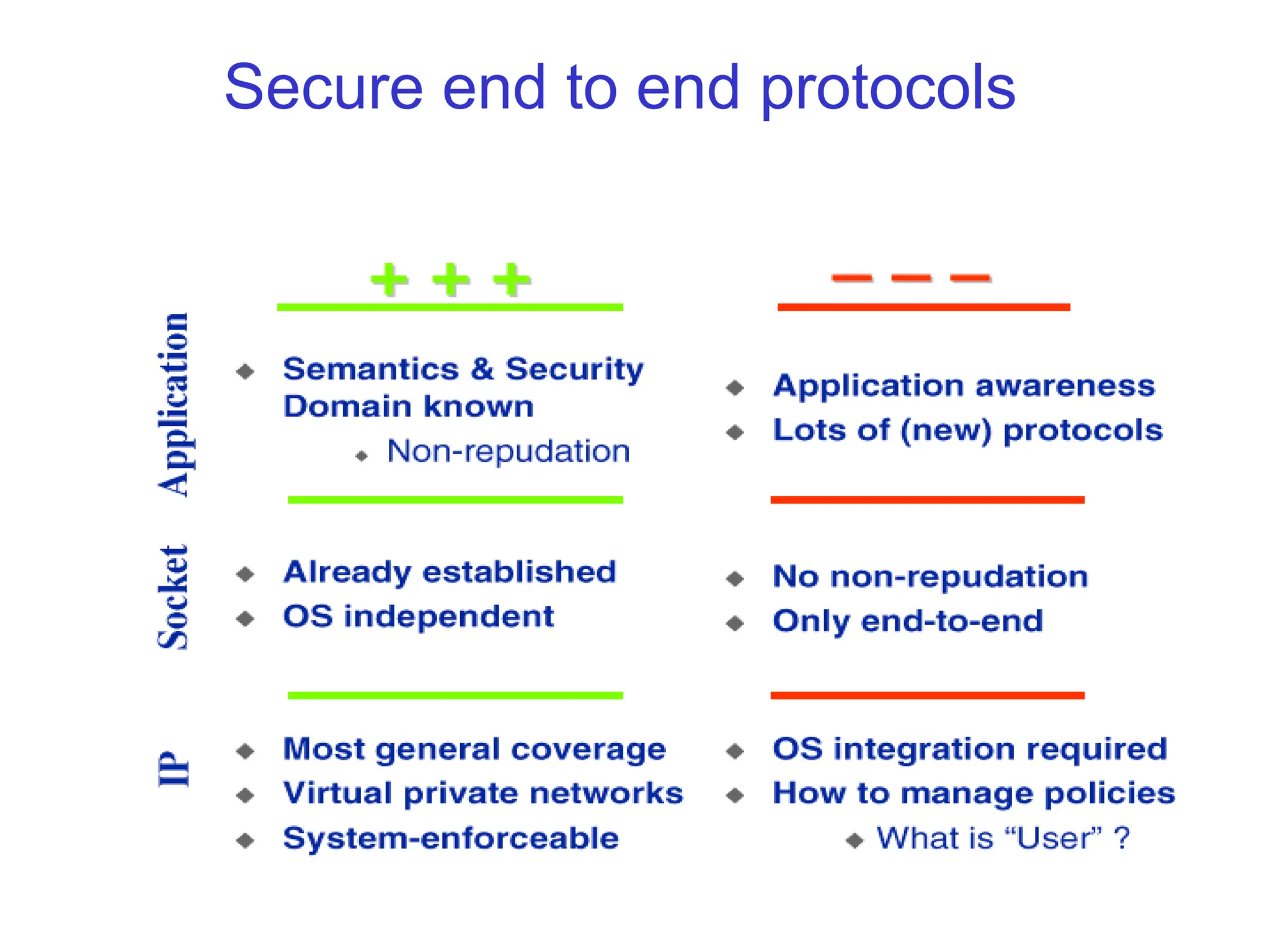
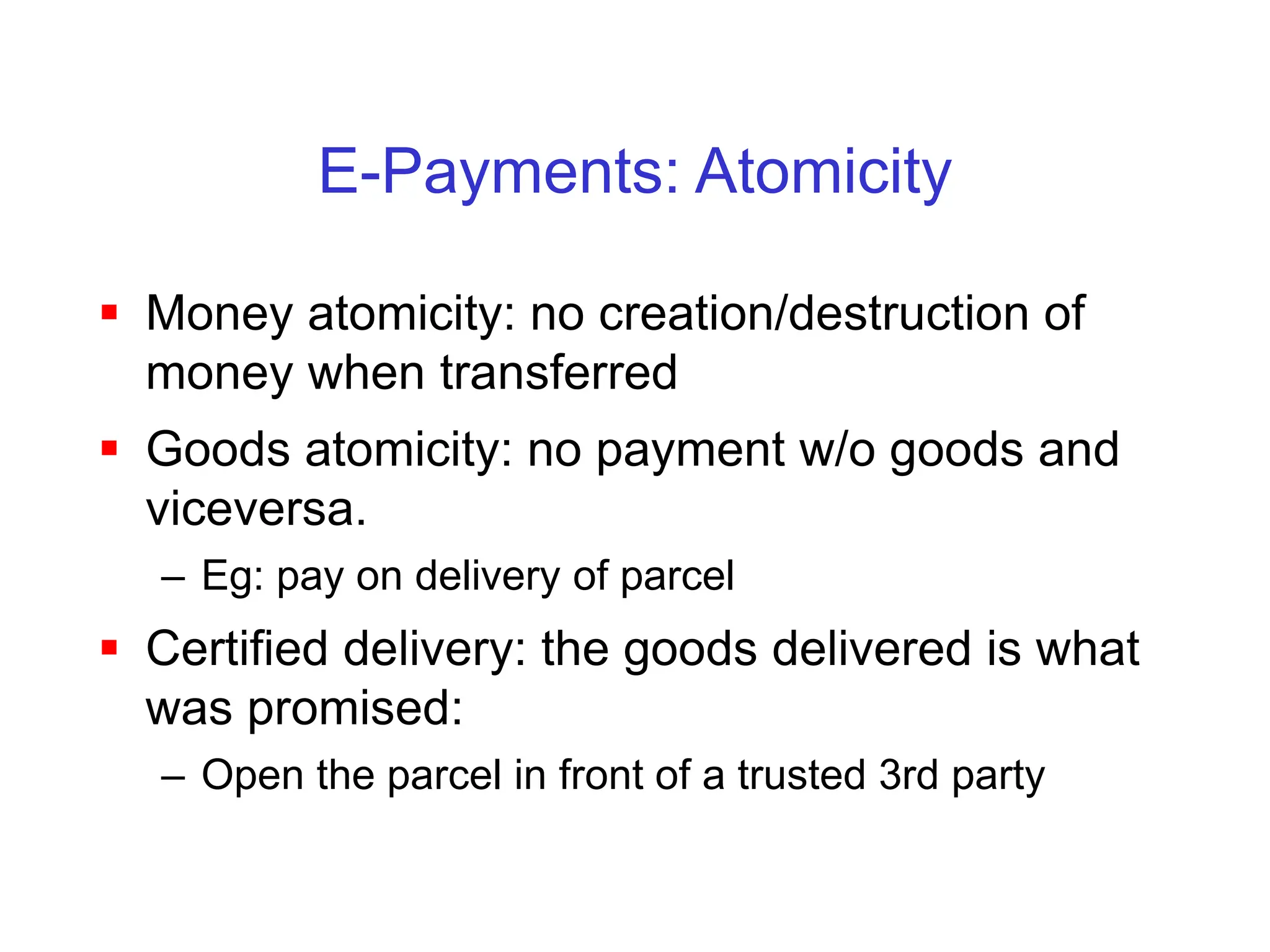
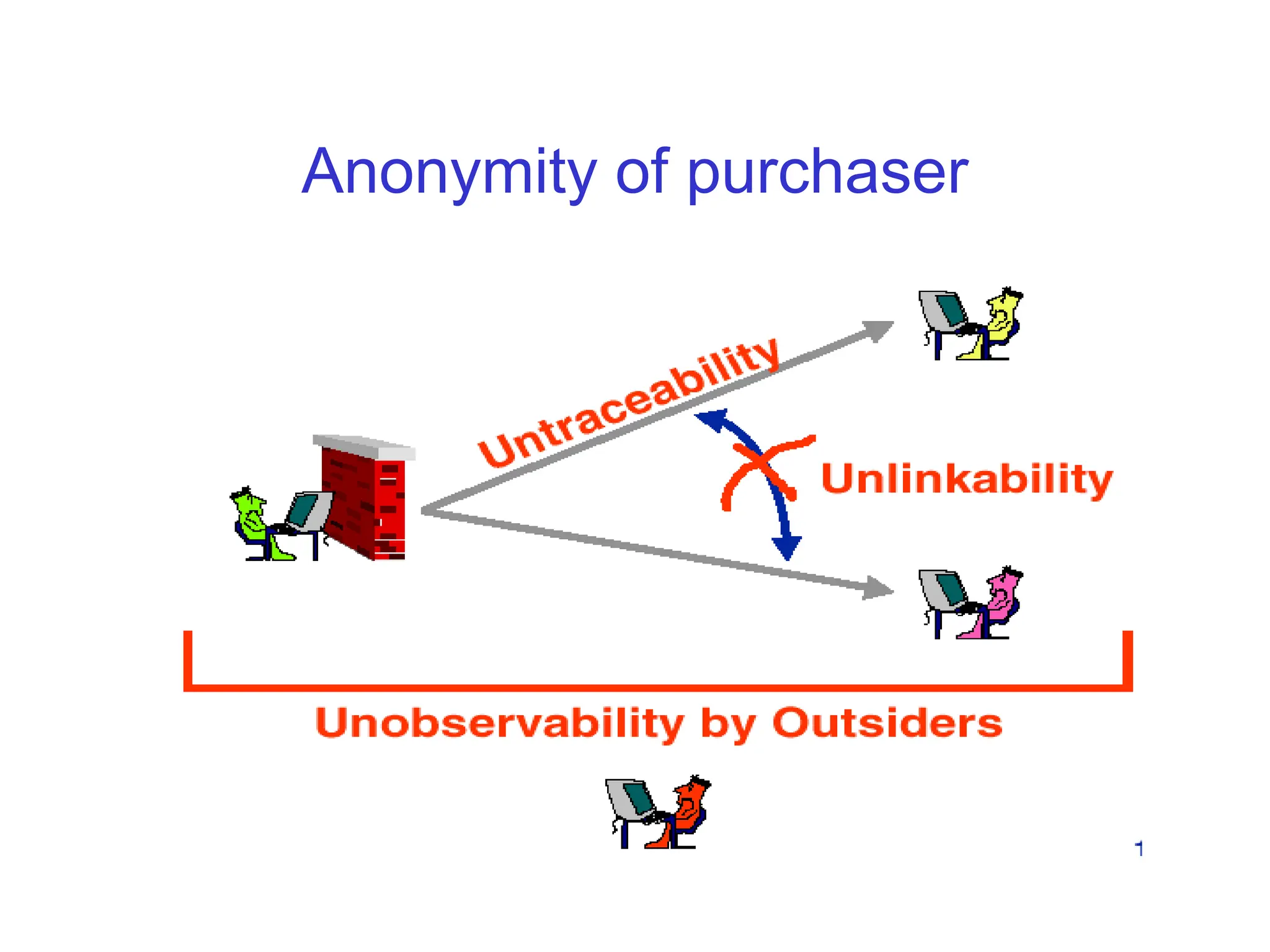
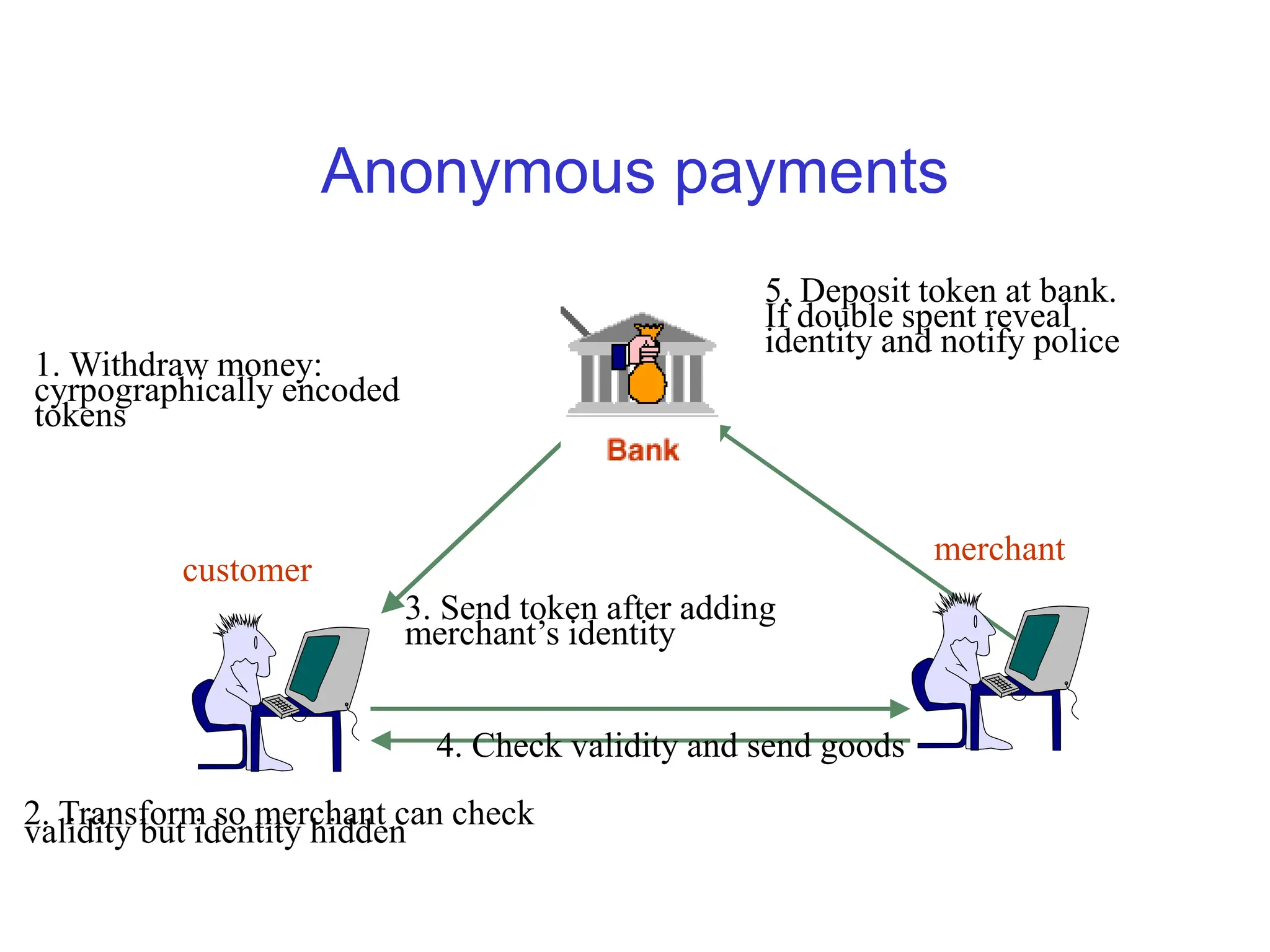
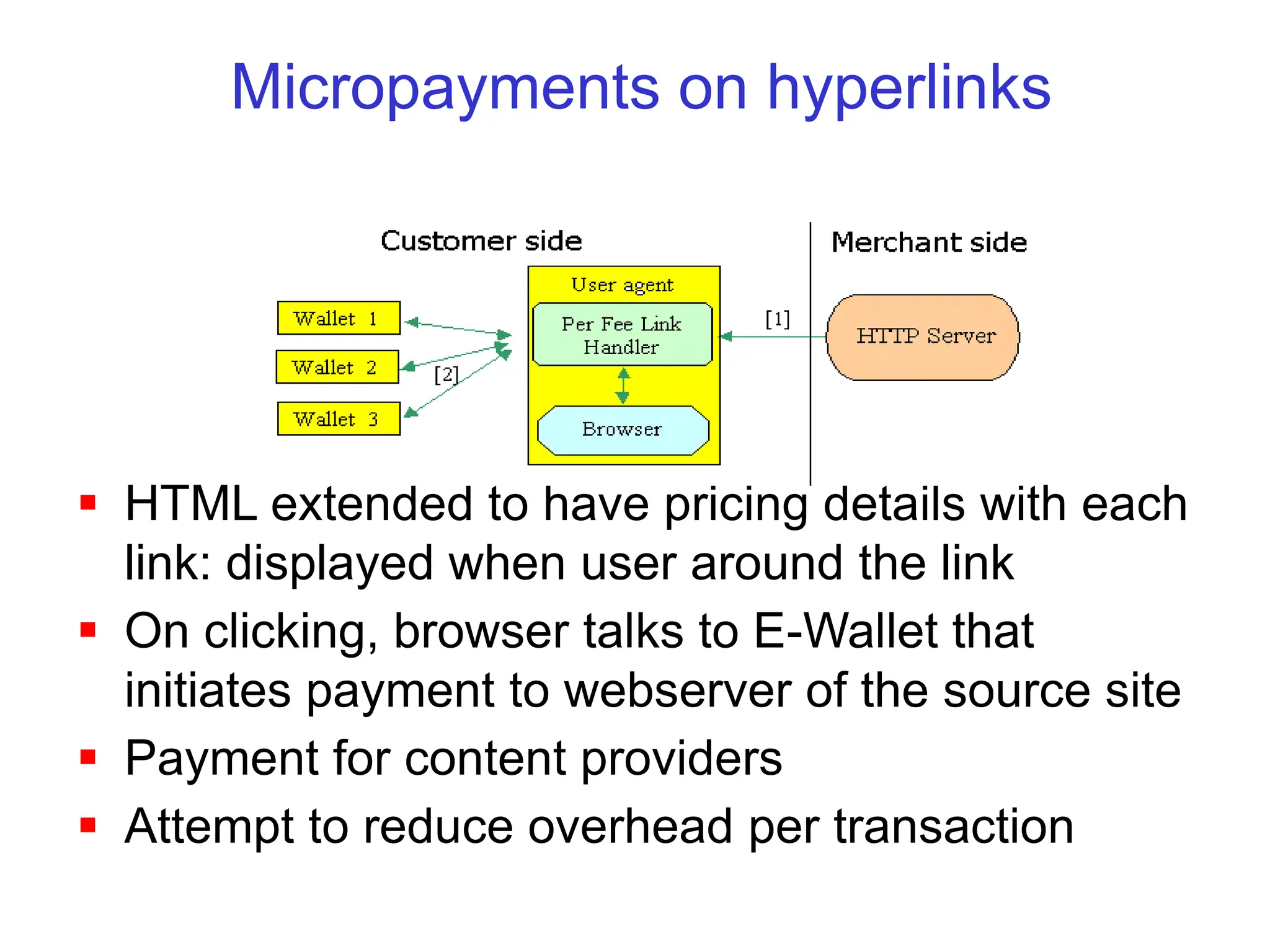
The document discusses secure web transactions and electronic payment systems. It provides an overview of cryptography and network security protocols that underlie e-commerce technologies. It then describes various electronic payment systems including credit card-based methods, electronic checks, anonymous payments, micropayments, and smart cards. For each payment system, it discusses how transactions are conducted securely and any issues around areas like anonymity, efficiency for microtransactions, and reliability.