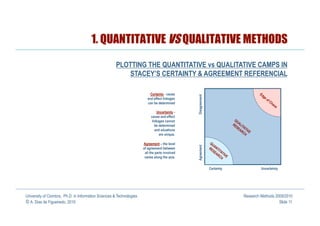
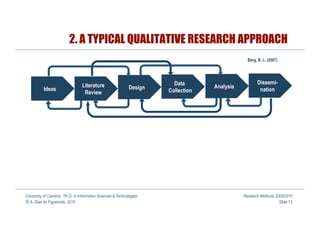
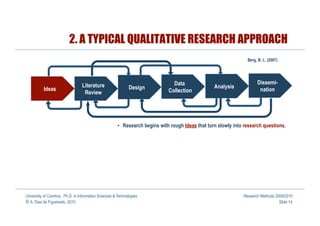
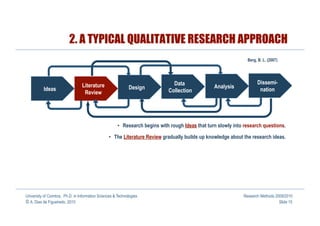
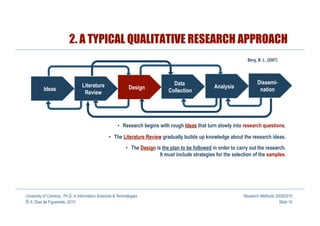
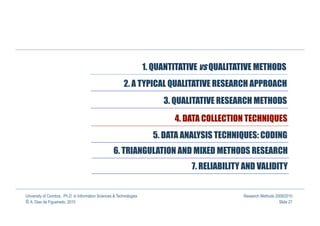
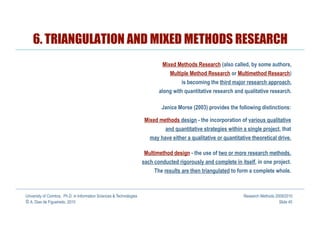
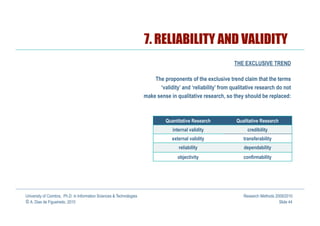
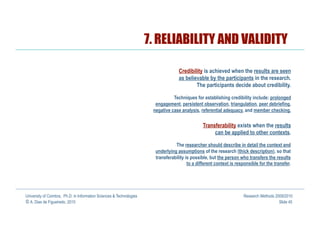
This document provides an introduction to qualitative research methods in information sciences and technologies. It discusses the differences between quantitative and qualitative methods, noting that while traditionally seen as incompatible, they are actually complementary. Qualitative methods are increasingly used in fields like information systems and human-computer interaction due to the complex social and human factors involved. The document outlines some key aspects of quantitative and qualitative research approaches.