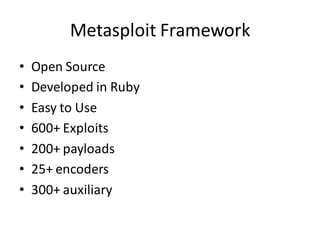
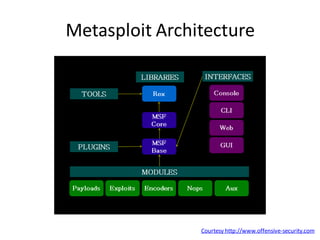
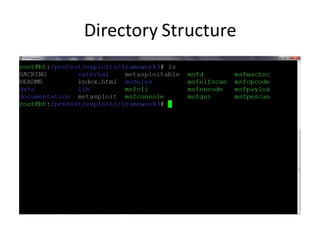
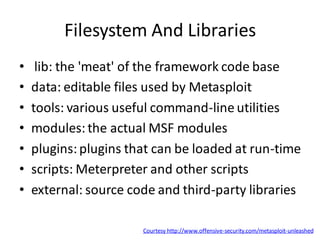
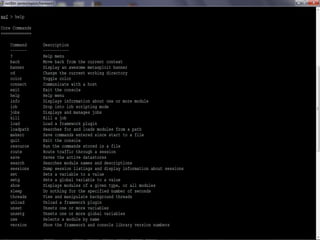
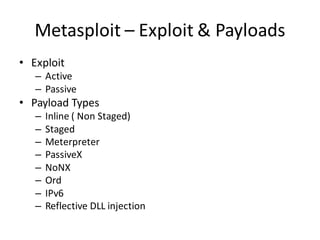
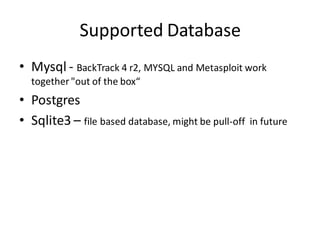
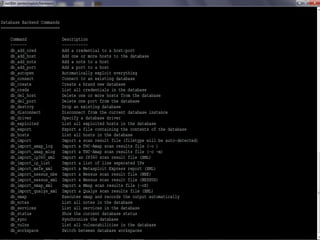
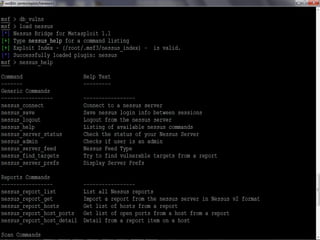
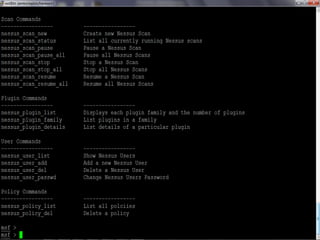
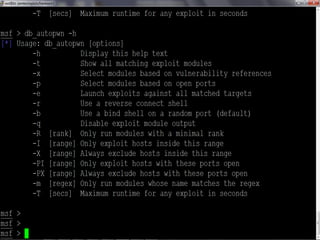
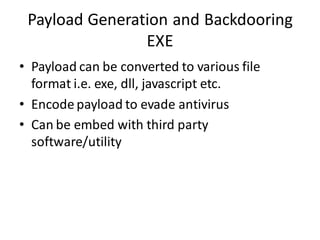
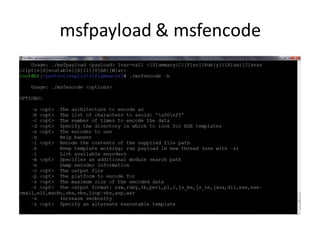
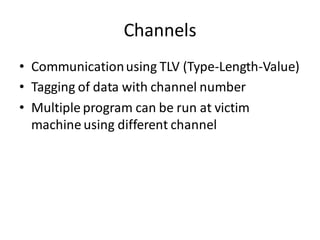
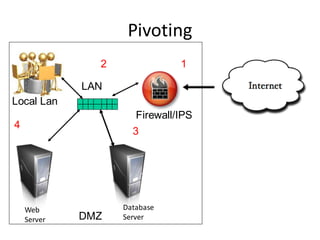
This document provides an overview of metasploitation and using the Metasploit framework. It discusses basics like vulnerabilities, exploits, payloads and encoders. It then covers using the msfconsole interface, exploit modules, auxiliary modules like scanners, databases integration, automation, client-side exploits, payload generation, backdooring files, Linux backdoors, Meterpreter, pivoting, and post-exploitation techniques. The document includes several screenshots and links resources for further information.