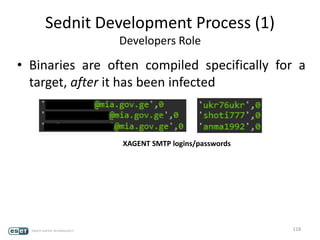
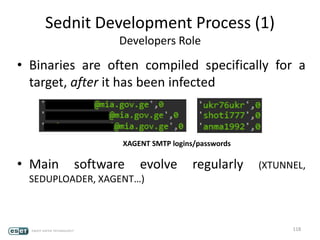
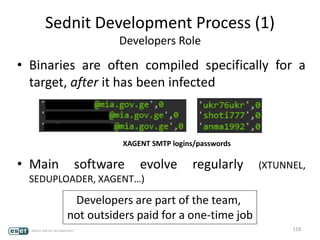
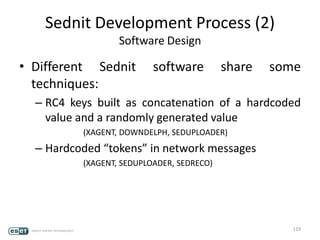
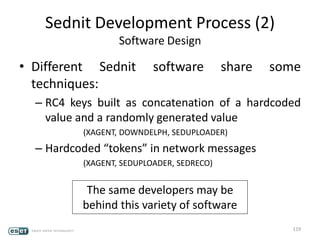
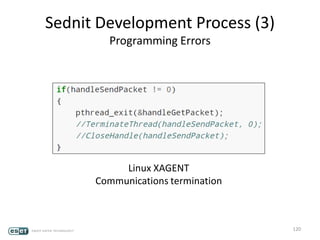
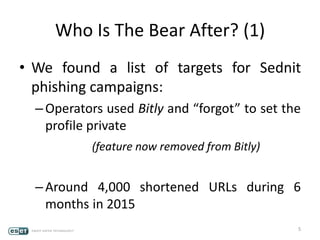
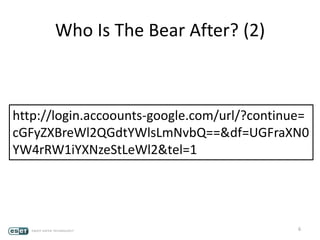
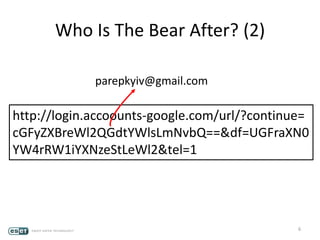
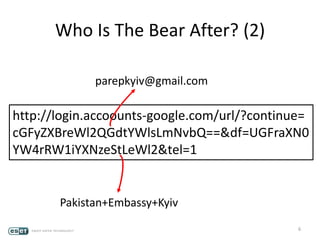
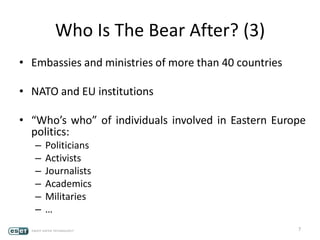
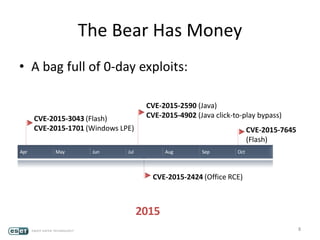
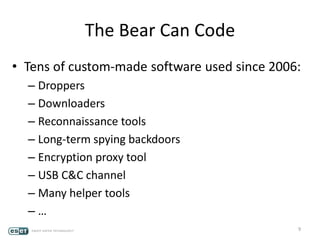
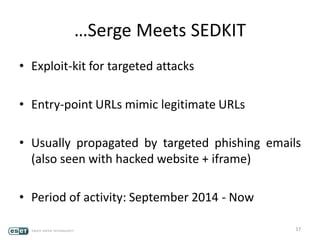
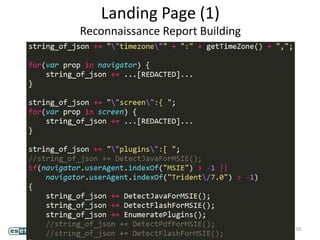
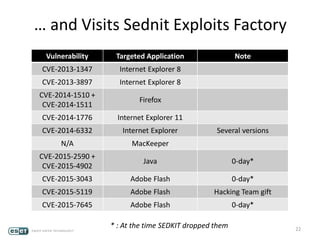
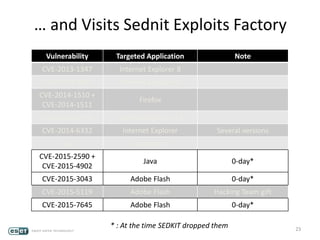
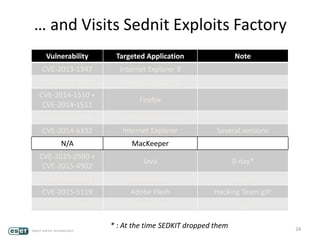
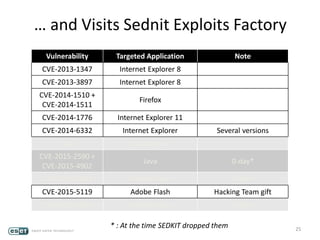
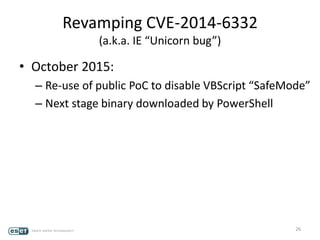
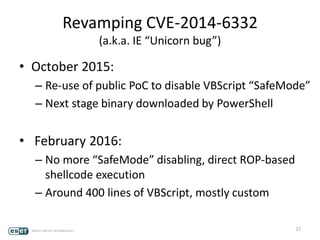
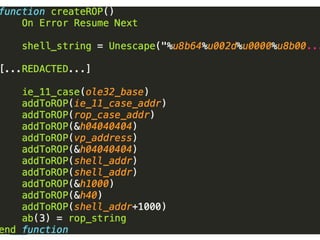
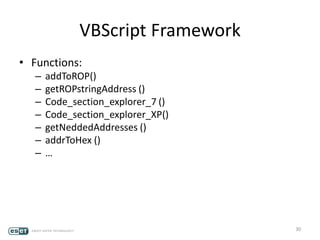
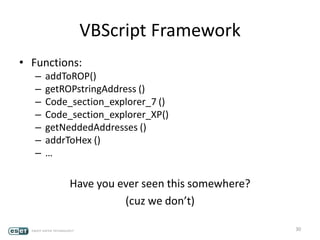
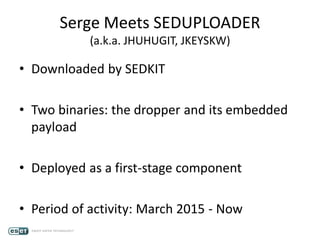
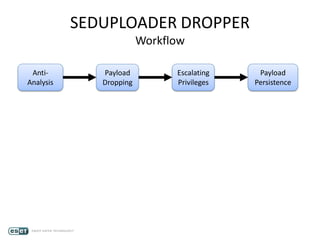
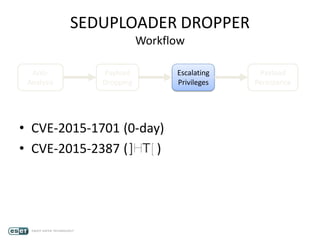
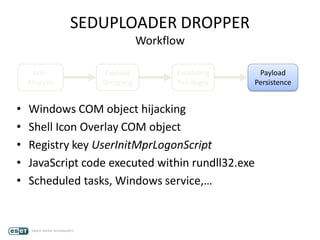
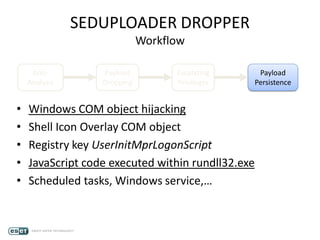
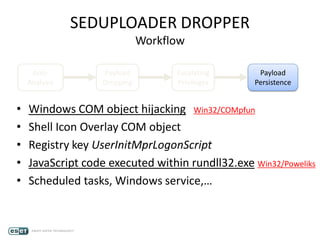
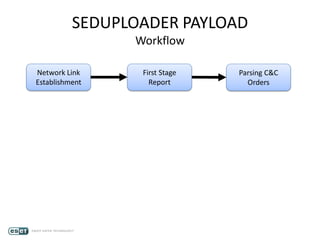
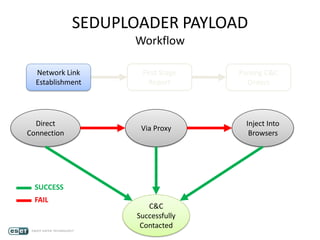
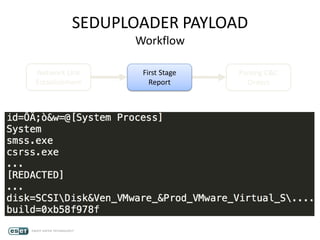
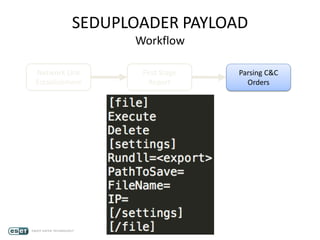
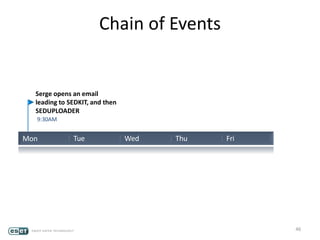
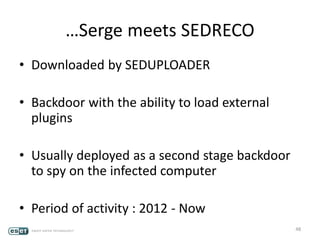
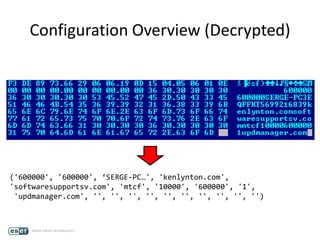
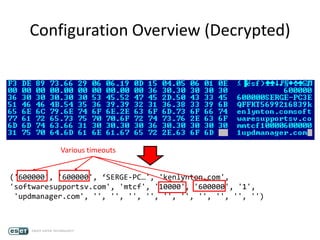
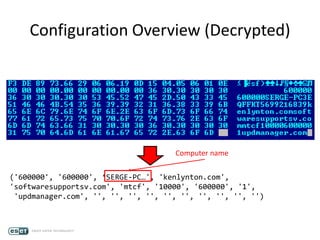
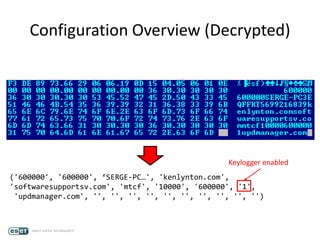
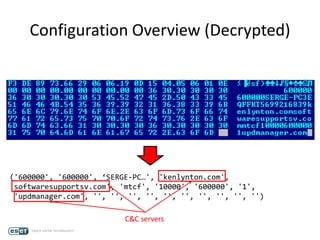
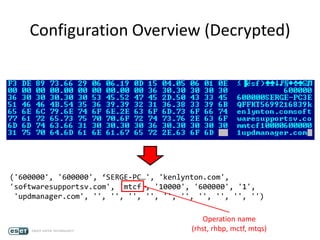
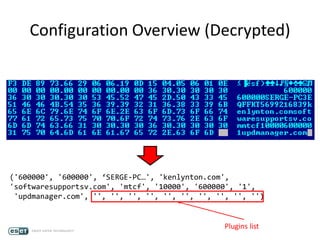
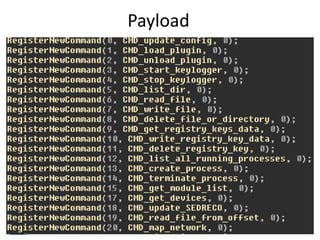
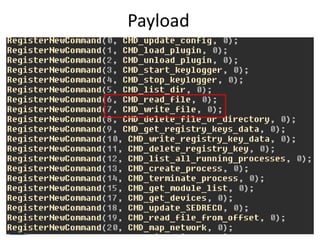
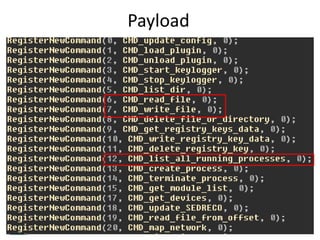
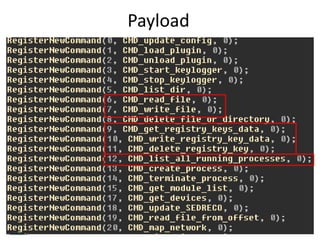
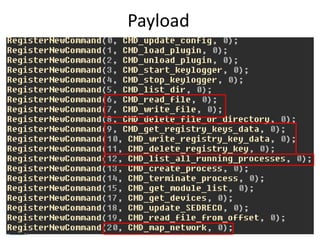
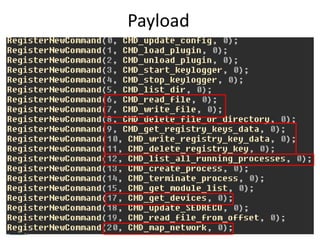
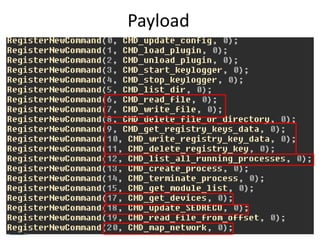
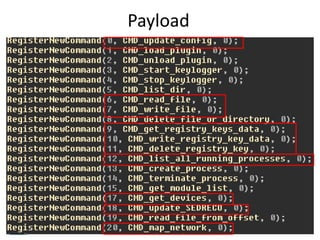
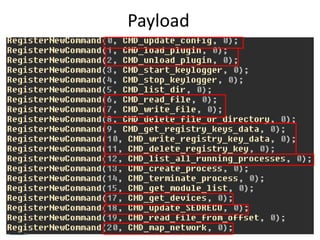
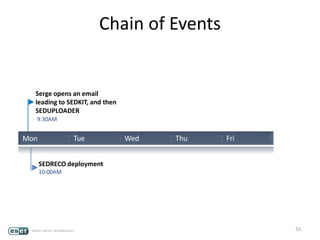
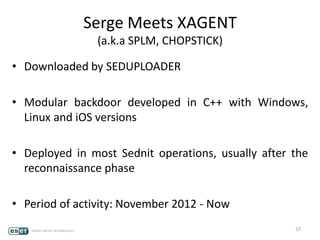
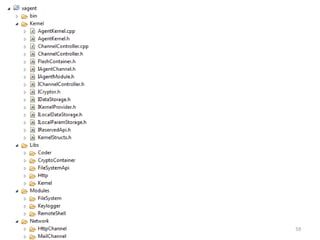
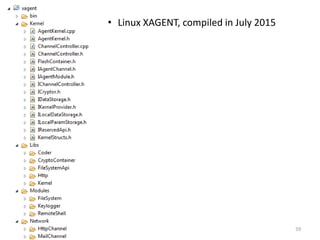
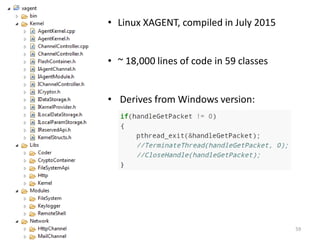
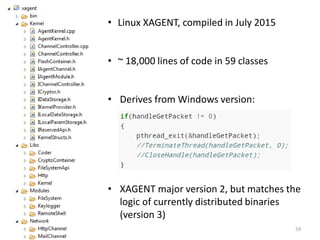
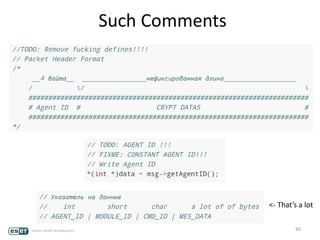
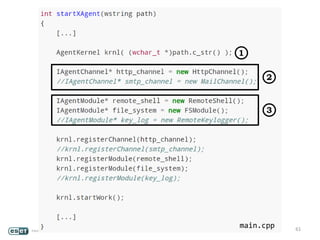
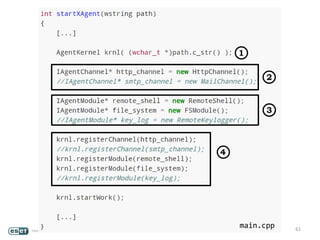
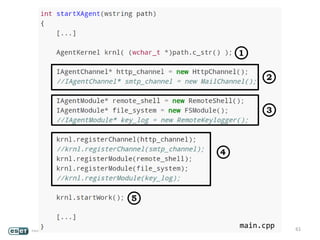
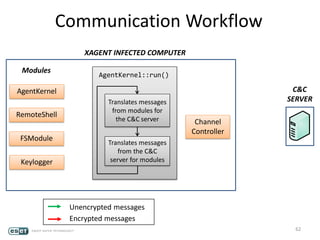
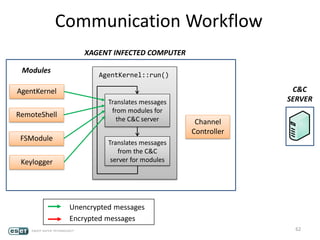
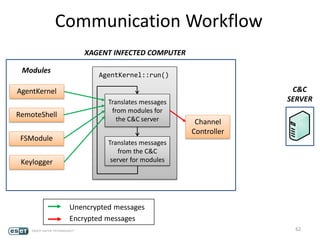
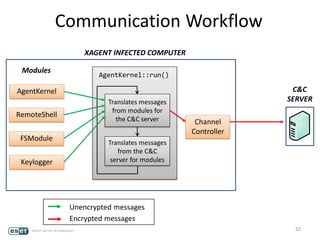
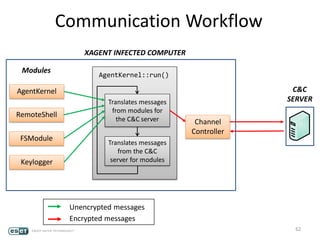
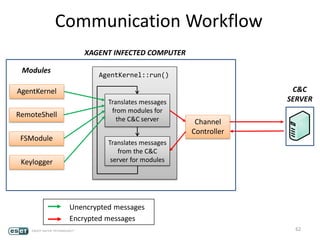
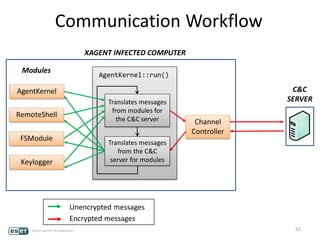
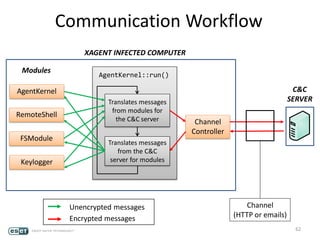
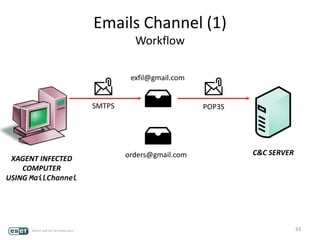
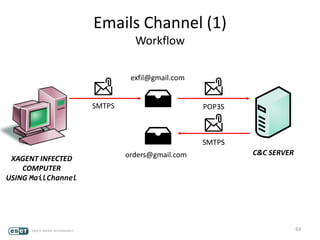
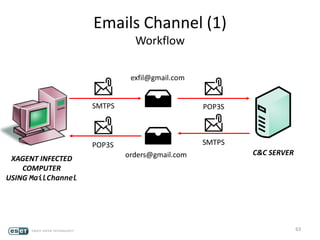
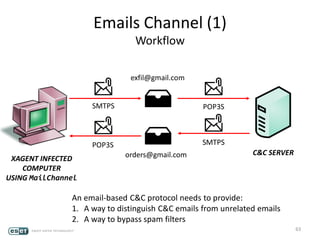
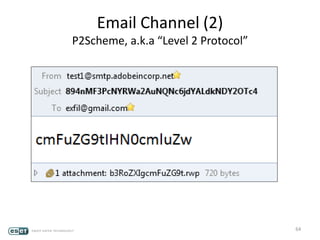
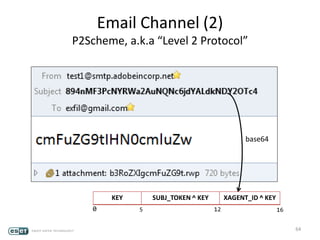
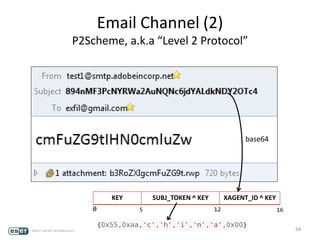
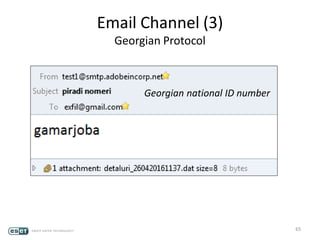
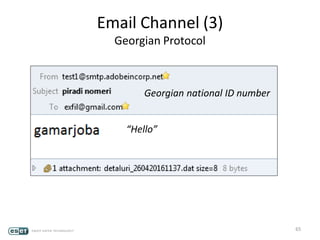
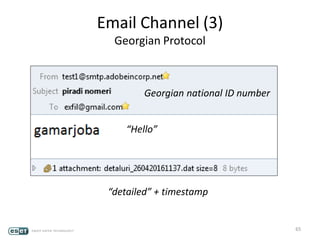
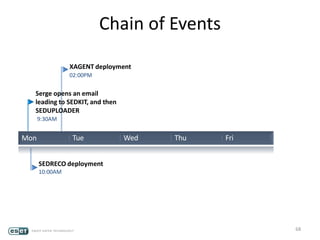
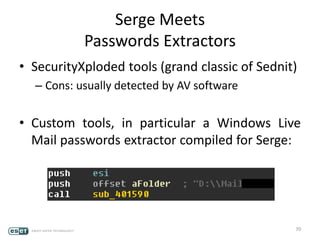
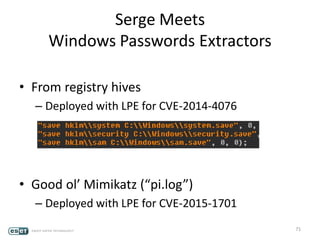
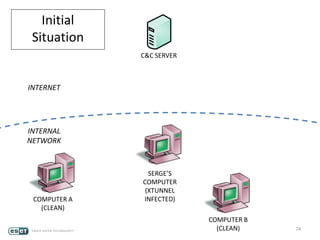
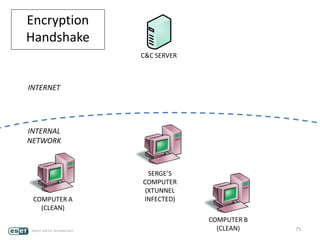
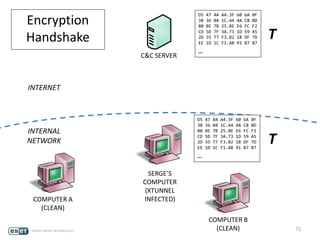
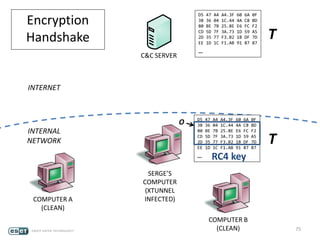
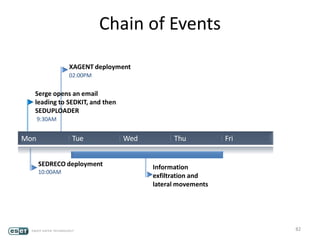
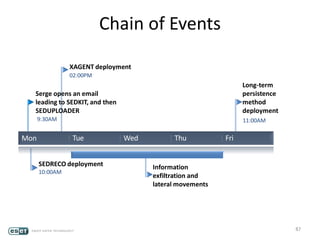
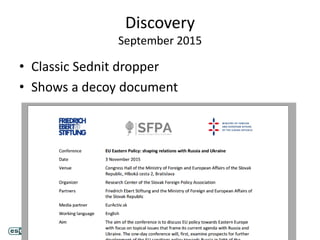
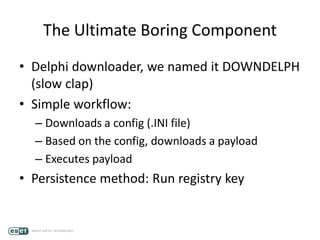
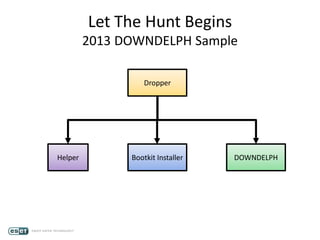
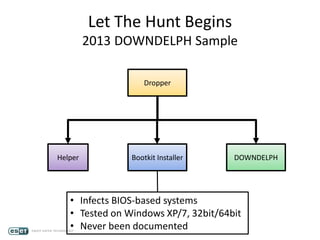
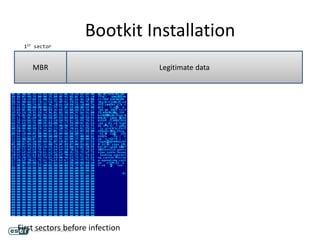
The document discusses the Sednit group, also known as APT28 or Fancy Bear, which has been conducting targeted cyber-espionage operations since 2006, focusing on geopolitics and key individuals in Eastern Europe. It provides a detailed analysis of the group's toolkit, including various exploits, custom software, and the methodologies used to carry out phishing attacks and infiltrate sensitive networks. A case study involving a fictional target named Serge illustrates how such attacks are executed and the tools used throughout the process.






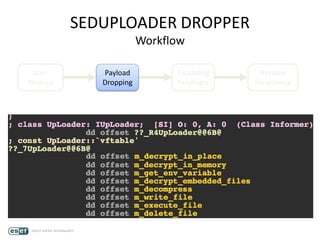
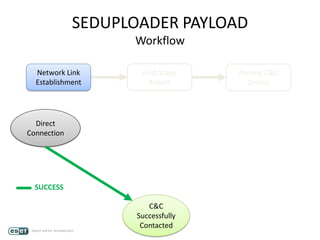
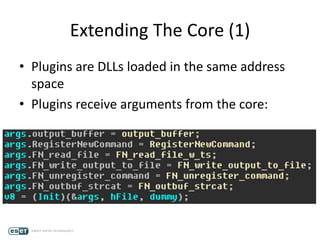
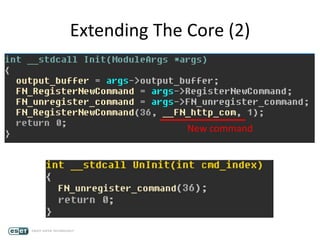





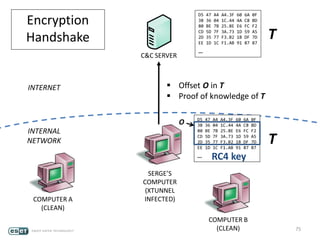
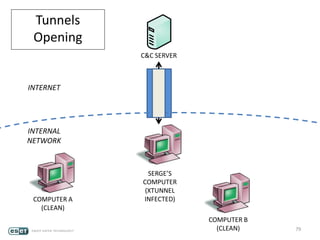

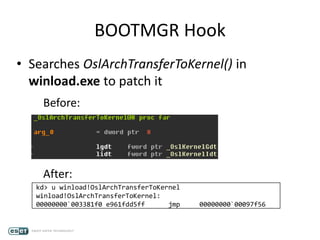
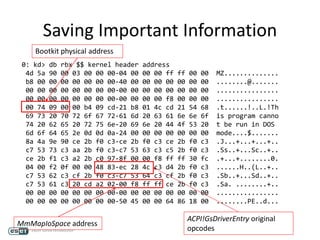
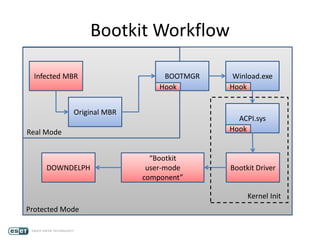
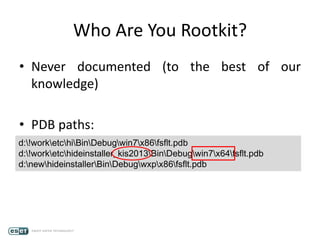
![Kernel Mode Rootkit (1)
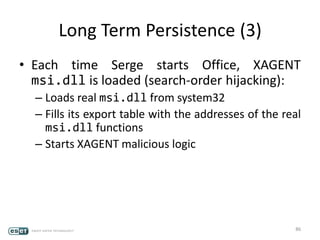
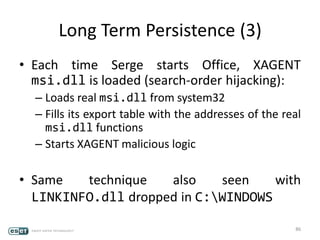
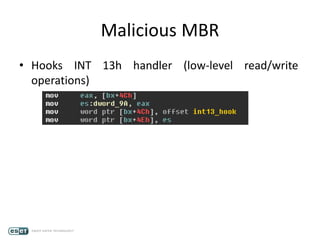
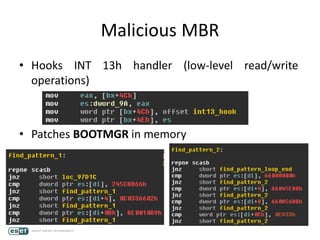
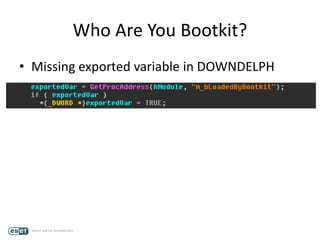
• Registered as a Windows service
• Injects DOWNDELPH into explorer.exe (APC)
• Hides files, folders and registry keys
• Relies on a set of rules:
HIDEDRV: >>>>>>>>Hide rules>>>>>>>> rules
HIDEDRV: File rules: Device[…]dnscli1.dll
HIDEDRV: File rules: Device[…]FsFlt.sys
HIDEDRV: Registry rules: REGISTRY[…]FsFlt
HIDEDRV: Registry rules: REGISTRY[…]FsFlt
HIDEDRV: Registry rules: REGISTRY[…]FsFlt
HIDEDRV: Inject dll: C:Windowssystem32mypathcomdnscli1.dll
HIDEDRV: Folder rules: DeviceHarddiskVolume1Windowssystem32mypathcom
HIDEDRV: <<<<<<<<XXXXX<<<<<<<< rules
HIDEDRV: <<<<<<<<Hide rules<<<<<<<< rules](https://image.slidesharecdn.com/visitingthebeardenrecon2016calvetcamposdupuy-160621122822/85/Visiting-the-Bear-Den-200-320.jpg)