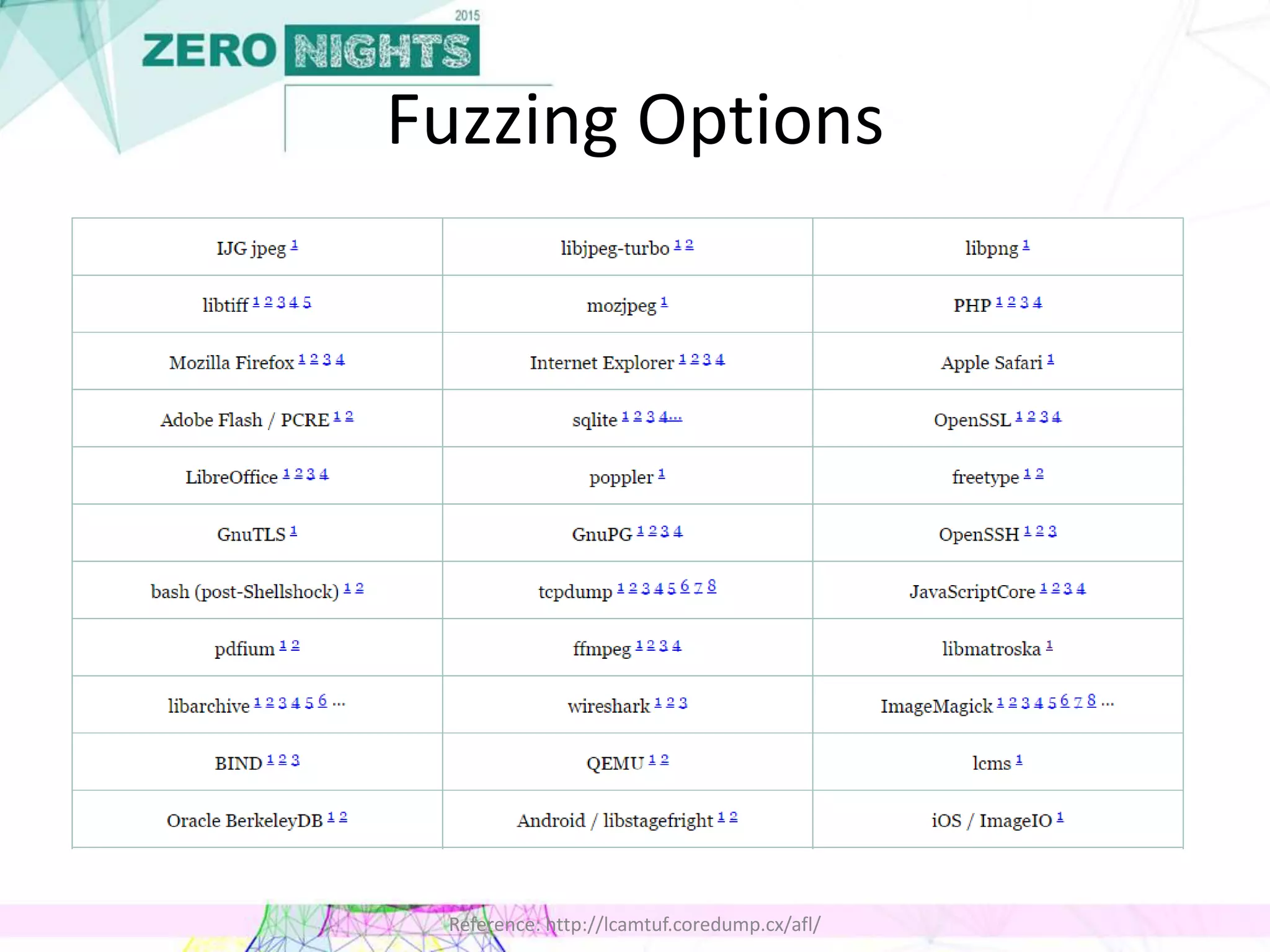
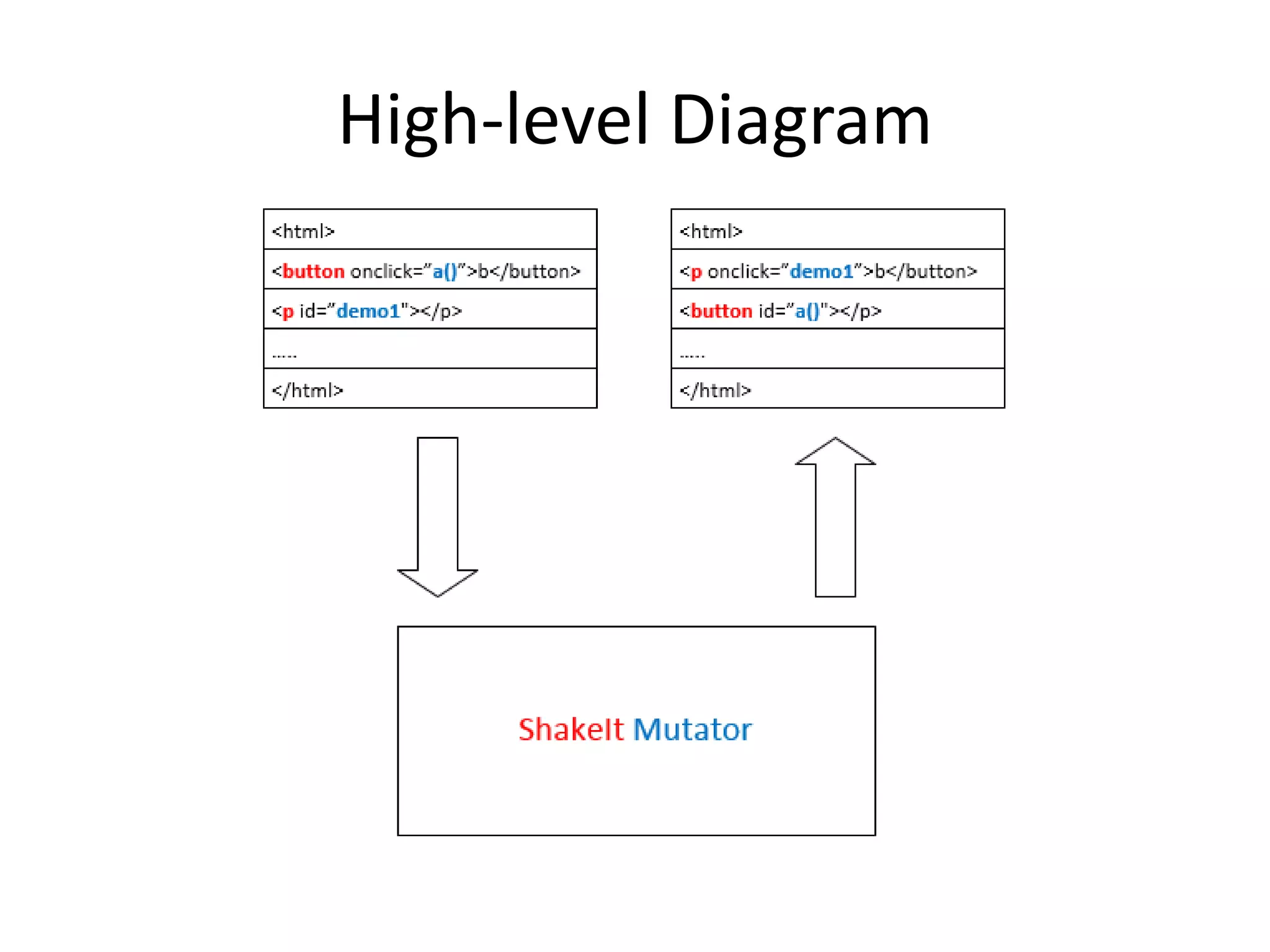
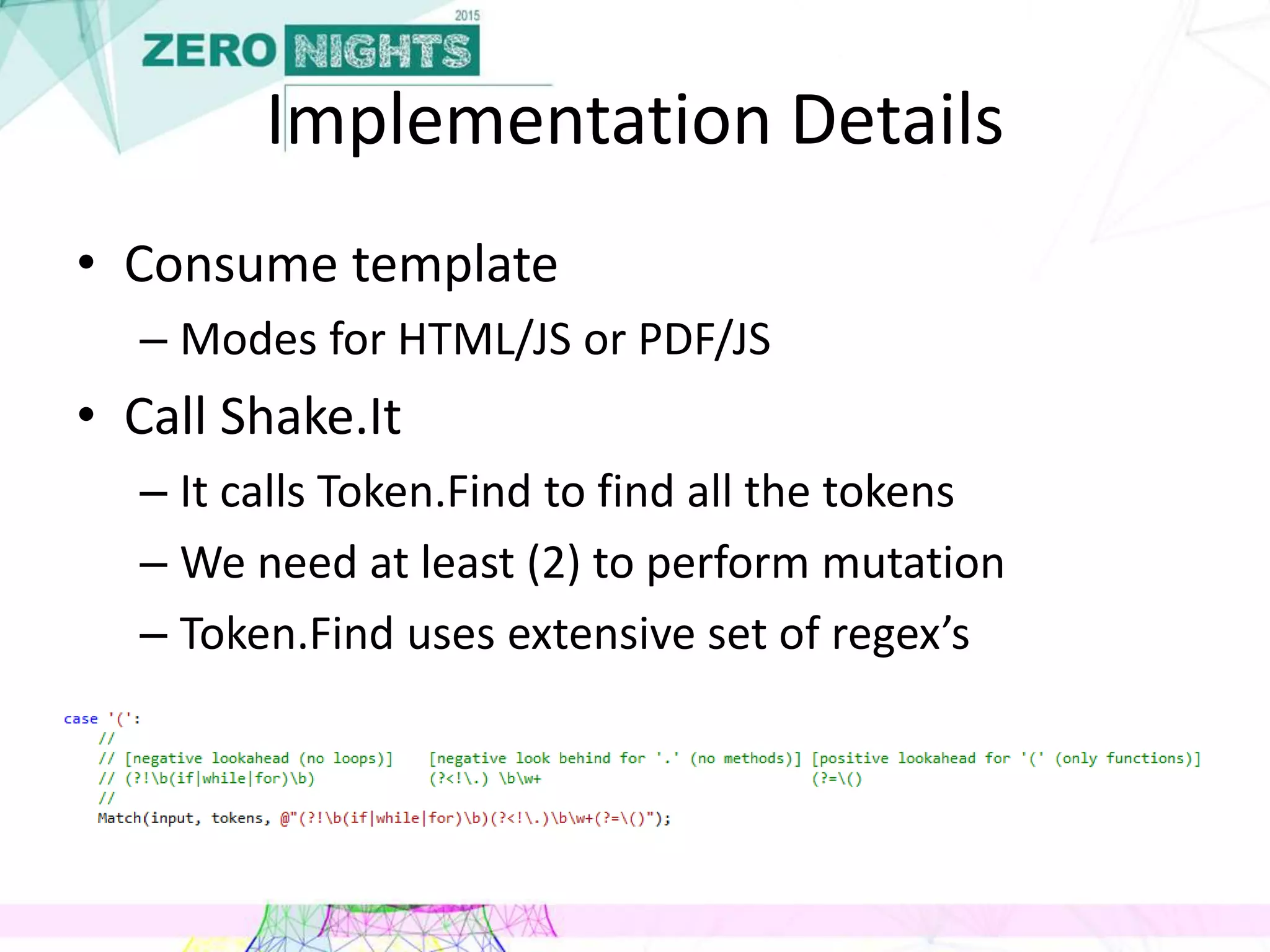
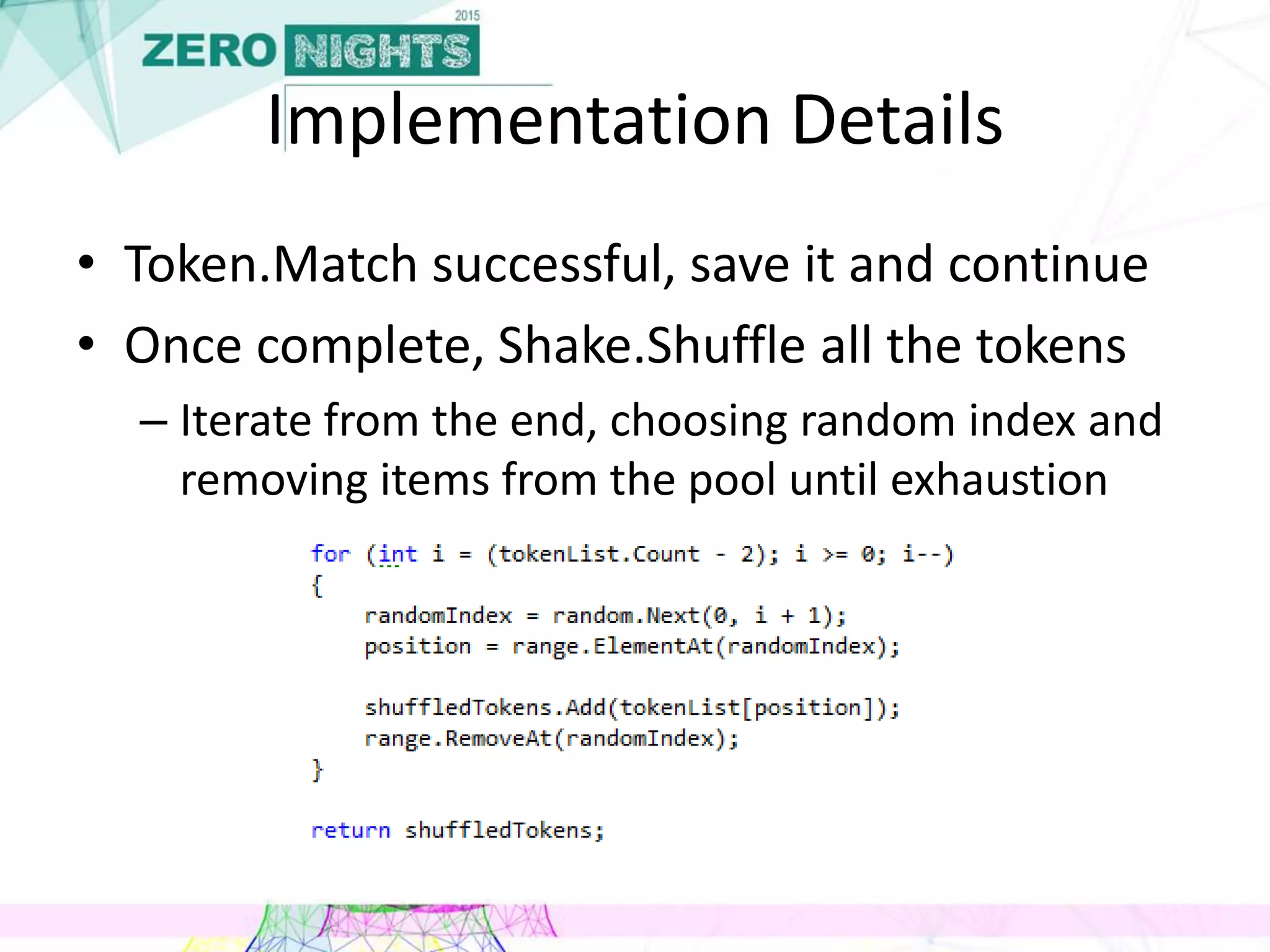
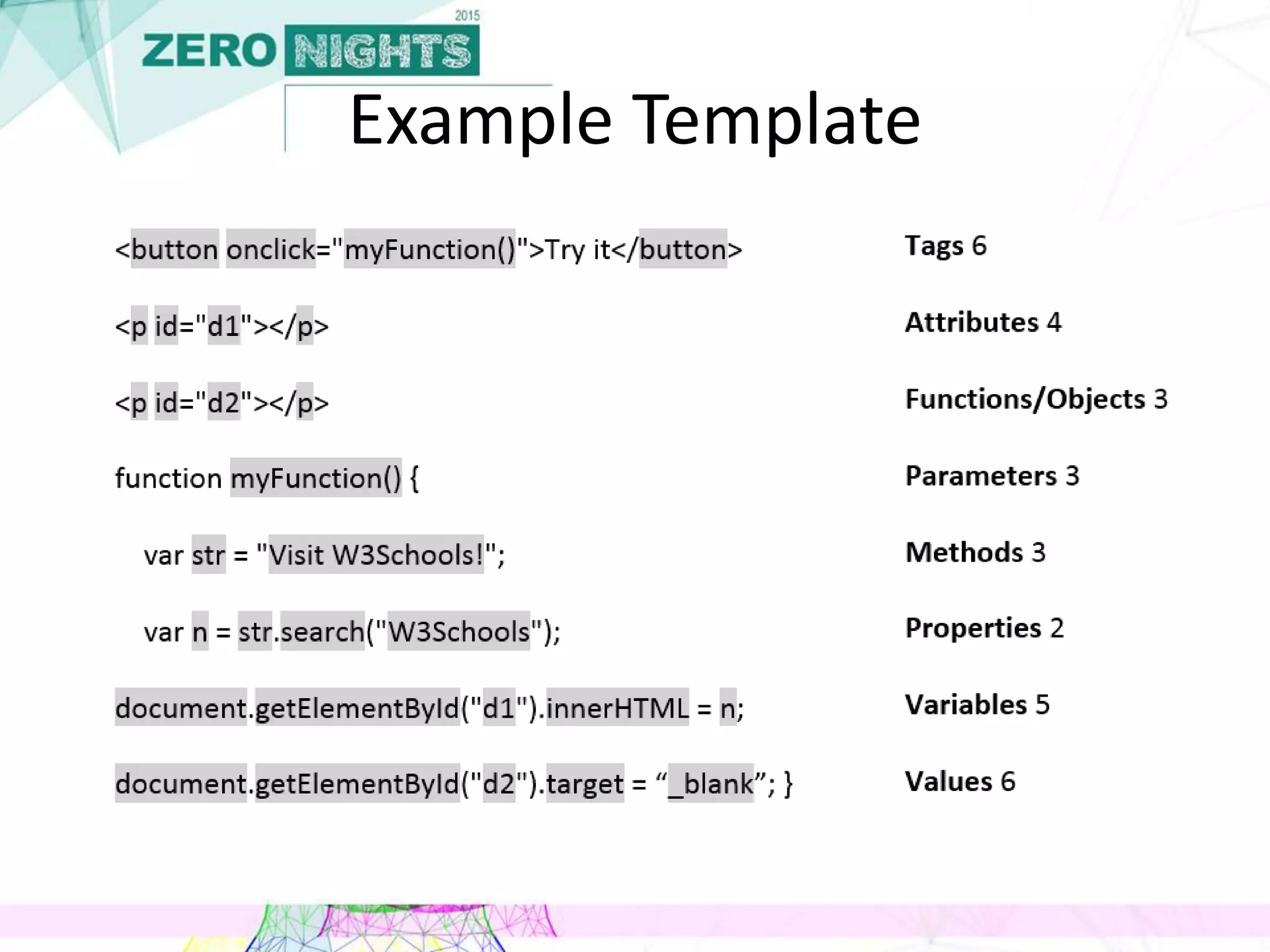
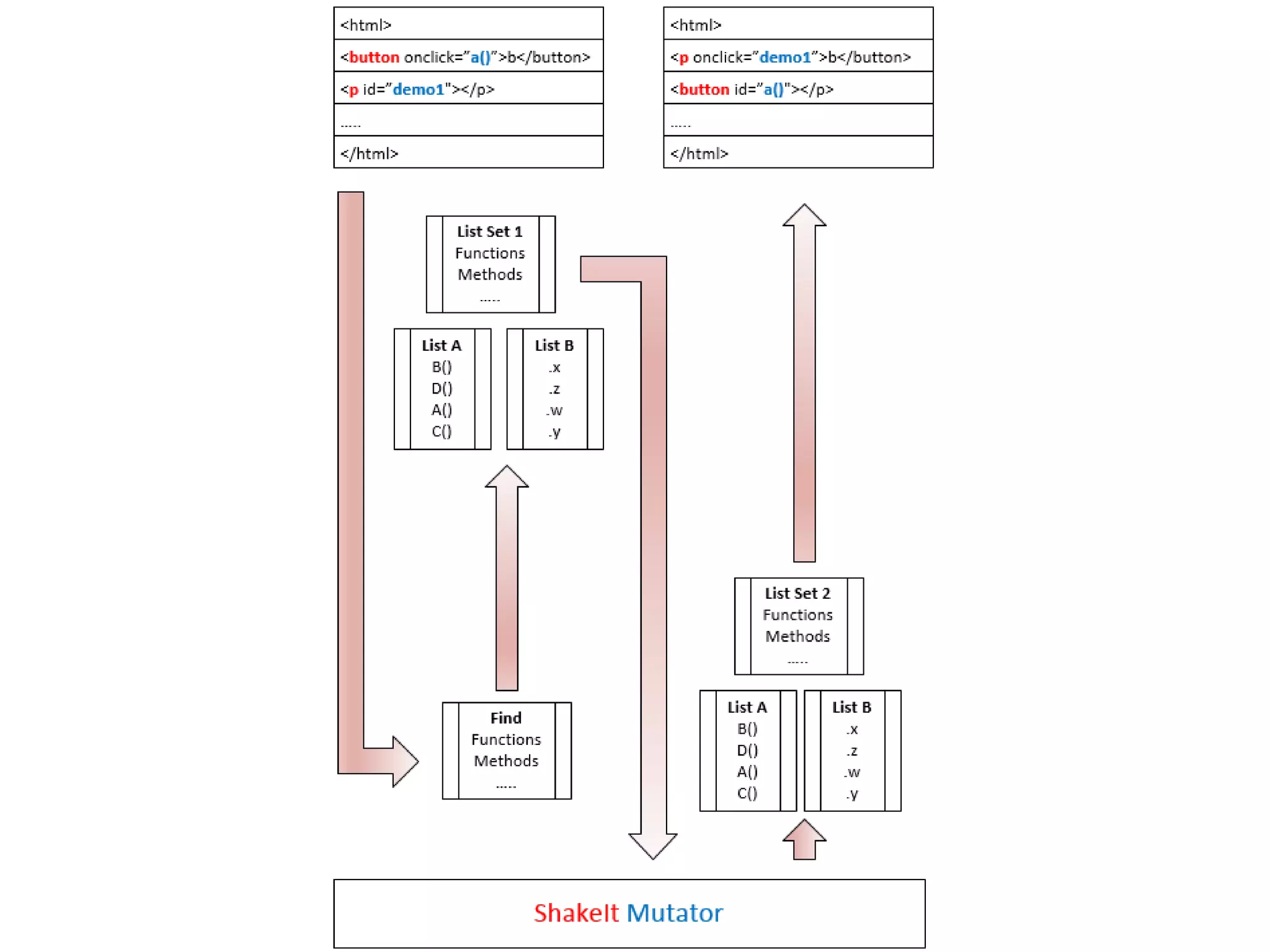
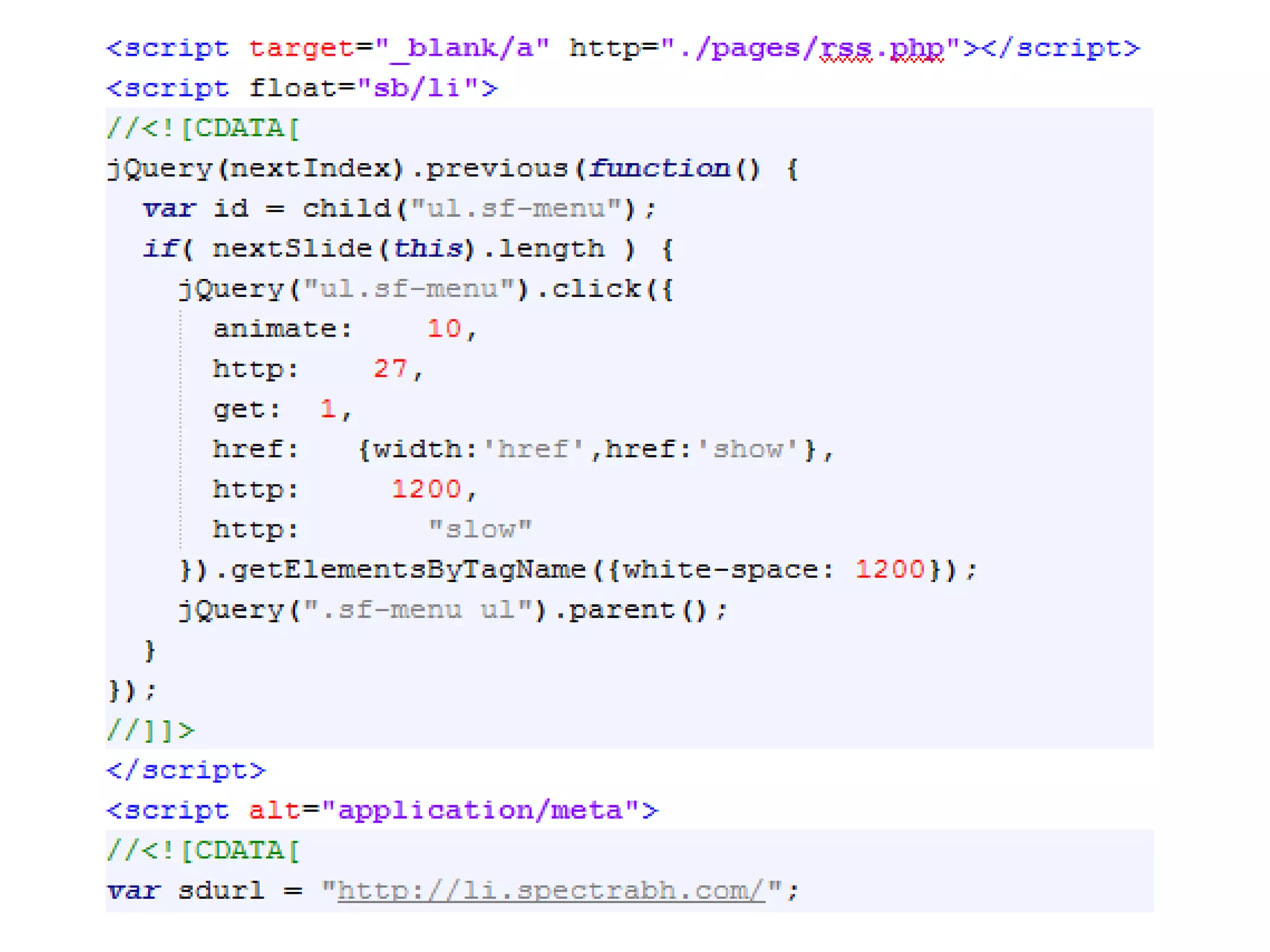
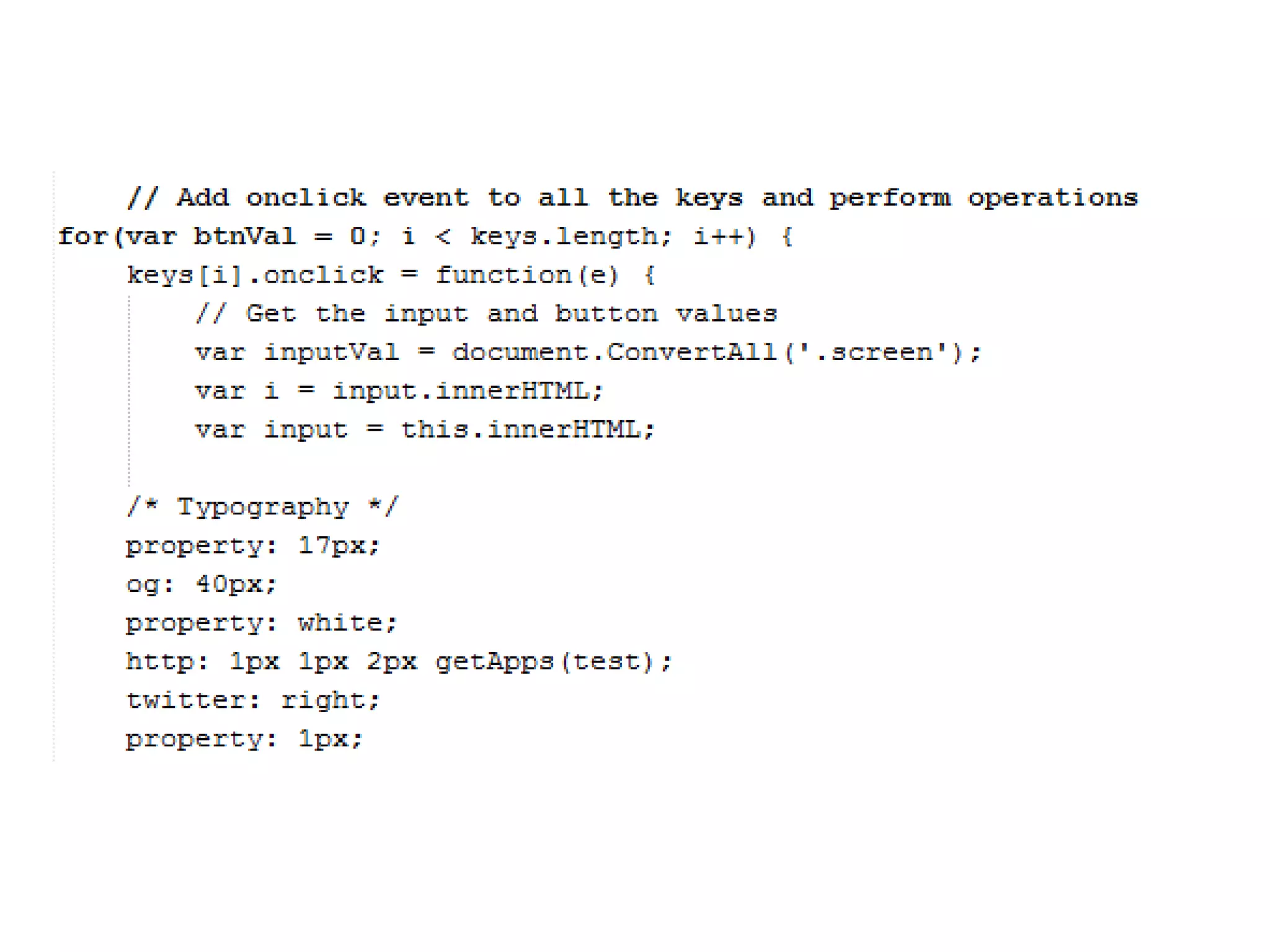
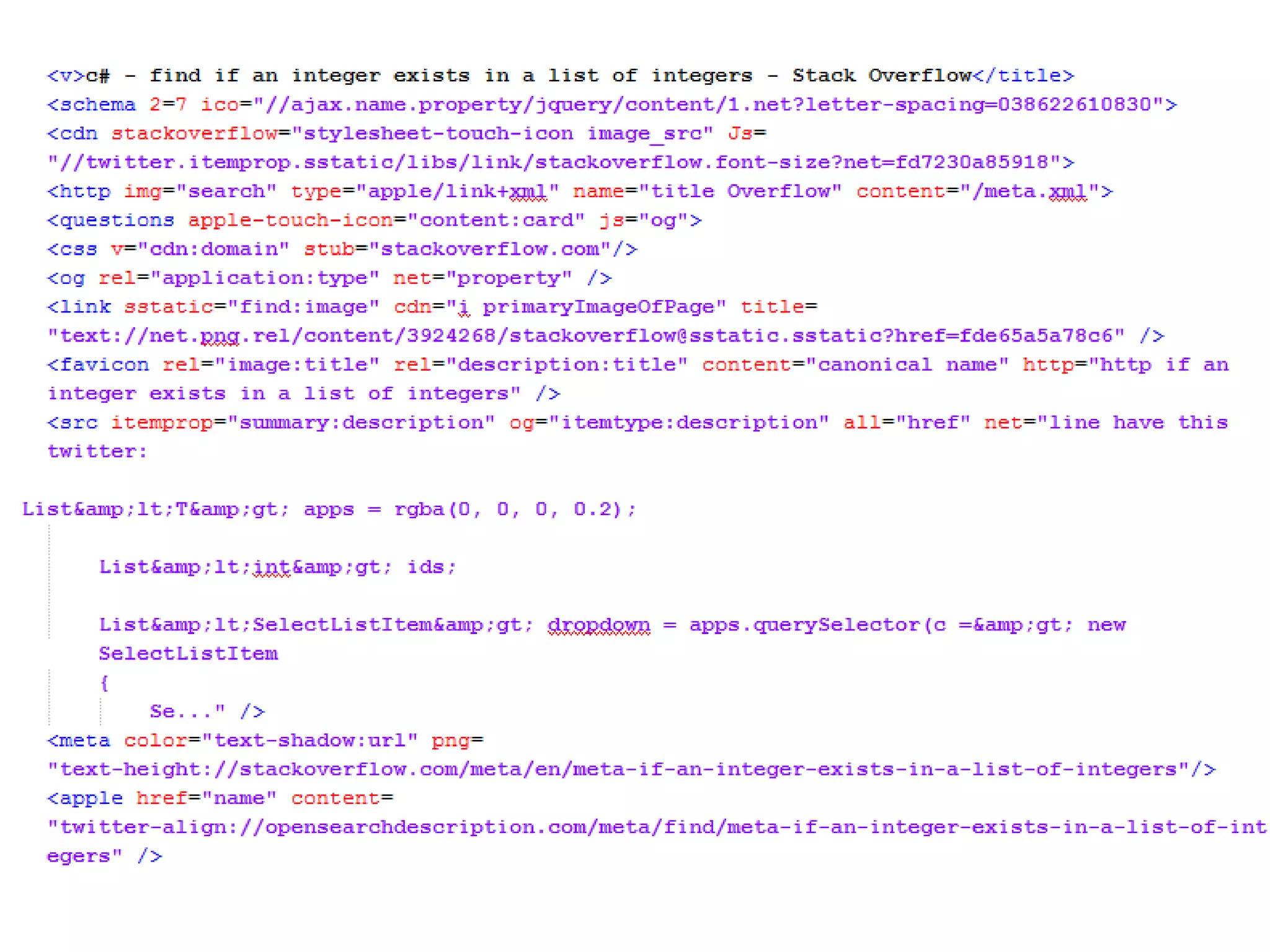
The document discusses an innovative approach to browser fuzzing using a tool called Shakeit, which focuses on mutating tokens rather than traditional fuzzing methods. It outlines the architecture, infrastructure, and current tools related to fuzzing, while detailing the process, challenges, and results from the research including various crashes in different browsers. The conclusion emphasizes the importance of strategy and infrastructure in fuzzing, as well as the ongoing presence of software vulnerabilities despite various mitigating measures.